Imagine having your tiny Raspberry Pi, perhaps running a smart home project or collecting environmental data, accessible and secure from anywhere on the planet. This dream, you know, is more attainable than you might think, especially when we bring in the powerful capabilities of Amazon Web Services (AWS). Connecting your remote IoT devices, like a Raspberry Pi, to the cloud securely and without breaking the bank, well, that's a bit of a challenge many folks face.
For quite some time, setting up reliable and safe remote access for these small computers felt a little like a secret club for seasoned IT pros. You might have worried about security holes, or perhaps the costs associated with cloud services seemed a bit too much for a hobby project. But what if there was a way to get robust security, consistent access, and even leverage the AWS Free Tier to keep things, more or less, completely affordable?
This article, you see, will walk you through how to achieve just that. We'll explore using AWS Virtual Private Cloud (VPC) for a private network, SSH for secure communication, and your trusty Raspberry Pi as the star of your remote IoT setup. By the end, you'll have a much clearer picture of how to manage your remote IoT projects with confidence, and, actually, with a surprisingly low financial commitment.
- Dick Van Dyke
- Arabian Prince
- Elodie Yung Net Worth
- Sydney Sweeney Blowjob
- Remoteiot Vpc Ssh Raspberry Pi Aws Download
Table of Contents
- Why Connect Your Raspberry Pi to AWS?
- The Power of Cloud for Tiny Computers
- Security and Scalability Made Easier
- Cost-Effectiveness with AWS Free Tier
- Understanding the Core Components
- Raspberry Pi: Your Edge Device
- AWS VPC: Your Private Cloud Sanctuary
- SSH: Your Secure Remote Gateway
- AWS Free Tier: Making it Accessible
- Setting Up Your Secure Remote IoT Environment
- Step 1: Preparing Your Raspberry Pi
- Step 2: Creating Your AWS VPC
- Step 3: Launching an EC2 Instance (Bastion Host)
- Step 4: Configuring Security Groups and Network ACLs
- Step 5: Establishing SSH Access to Your Raspberry Pi via EC2
- Step 6: Automating Connections and Enhancing Security
- Common Challenges and Smart Solutions
- Keeping Costs Truly Free
- Managing Connectivity Drops
- Advanced Security Practices
- Frequently Asked Questions (FAQs)
- Ready to Build Your Remote IoT?
Why Connect Your Raspberry Pi to AWS?
So, you've got your Raspberry Pi, doing its thing, maybe collecting data or controlling some lights. But what happens when you need to check on it from afar, or, you know, when you want to update its software without being physically present? That's where connecting it to a cloud platform like AWS really starts to shine, offering a whole new level of flexibility and control.
The Power of Cloud for Tiny Computers
Your Raspberry Pi, for all its charm, has limited processing power and storage. When you link it to AWS, it can offload heavy tasks, store vast amounts of data, and even run complex analytics that would be quite impossible on the device itself. This means your little computer can focus on its primary job, collecting information or executing commands, while the cloud handles the heavy lifting, which is pretty neat, actually.
This partnership, you know, effectively turns your Pi into a robust edge device, capable of interacting with a much larger system. It can send sensor readings to AWS IoT Core, trigger serverless functions with AWS Lambda, or, in a way, store its collected data in S3 buckets for later analysis. The possibilities, it's almost, become truly expansive, allowing for much more sophisticated projects than a standalone Pi could ever manage.
- Zak Brown Net Worth
- Short Goodbye Letter To Someone Who Hurt You
- Whipitdev Leak
- Who Regulates Access To Electrical Closets And Live Electrical Equipment
- Christina Milian Nude
Security and Scalability Made Easier
Directly exposing your Raspberry Pi to the internet for remote access can be a bit like leaving your front door wide open. It’s risky. AWS, however, provides a suite of security features, including Virtual Private Clouds (VPCs) and Security Groups, that let you create a protected environment for your devices. This means your Pi communicates within a controlled network, making it far less vulnerable to unwanted intrusions, which is, obviously, a big relief.
As your projects grow, or, you know, if you decide to add more Raspberry Pis, AWS scales with you. You don't have to worry about upgrading hardware or redesigning your network from scratch. You can simply add more resources within your AWS environment, and, basically, your existing setup can often accommodate the expansion without much fuss. This scalability is a huge advantage for anyone looking to grow their IoT footprint.
Cost-Effectiveness with AWS Free Tier
One of the best parts about this whole setup, frankly, is the potential to keep costs incredibly low, sometimes even free, thanks to the AWS Free Tier. Many AWS services, including a certain amount of EC2 compute time, S3 storage, and IoT Core messages, come with a free usage tier for the first 12 months, or, in some cases, indefinitely. This means you can experiment, learn, and even run small production projects without incurring significant expenses.
Careful planning, you know, is key to staying within the free tier limits. We'll discuss how to pick the right services and monitor your usage so you can enjoy the benefits of AWS without unexpected bills. It’s a pretty amazing way to get started with powerful cloud tools, especially if you're on a budget or just exploring new ideas, which, you know, many of us are.
Understanding the Core Components
To really get this remote IoT setup working, it helps to understand the main pieces of the puzzle. Each component plays a vital role in creating a secure and efficient connection between your Raspberry Pi and the AWS cloud. So, let's break down what each one brings to the table, shall we?
Raspberry Pi: Your Edge Device
The Raspberry Pi, as you probably know, is a small, single-board computer that's perfect for IoT projects. It's affordable, versatile, and consumes very little power, making it ideal for deployment in remote locations or, you know, for always-on tasks. It acts as your "edge device," collecting data from sensors, controlling actuators, or, in a way, performing local processing before sending information to the cloud.
For our purposes, your Raspberry Pi will be the device that needs to be accessed remotely. It will be running an operating system, typically a flavor of Linux like Raspberry Pi OS, and will have an SSH server enabled so we can connect to it securely. Keeping it updated and, you know, with minimal unnecessary software running, is a good practice for both security and performance.
AWS VPC: Your Private Cloud Sanctuary
A Virtual Private Cloud (VPC) in AWS is, basically, your own isolated section of the AWS cloud. Think of it as your private network within AWS, where you have complete control over your IP address ranges, subnets, route tables, and network gateways. This isolation is crucial for security, as it means your devices and resources aren't directly exposed to the public internet unless you explicitly allow it.
Using a VPC, you can create a secure tunnel for your Raspberry Pi to communicate with AWS services. This ensures that all traffic between your Pi and your cloud resources stays within this private, protected environment, which, you know, significantly reduces the risk of eavesdropping or unauthorized access. It’s like building a high-walled, guarded compound for your digital assets, so to speak.
SSH: Your Secure Remote Gateway
SSH, or Secure Shell, is a network protocol that lets you establish a secure, encrypted connection between two computers over an unsecured network. It's the standard way to access remote Linux servers, and, you know, it's perfect for managing your Raspberry Pi from afar. When you SSH into your Pi, all the data exchanged, including your commands and the Pi's responses, is encrypted, keeping it safe from prying eyes.
We'll use SSH in a specific way here: through a "bastion host" or "jump box" within your AWS VPC. This means you'll first SSH into a small, secure EC2 instance in your VPC, and then, from that instance, you'll SSH into your Raspberry Pi. This two-step process adds an extra layer of security, as your Pi is never directly accessible from the open internet, which is, frankly, a very good thing.
AWS Free Tier: Making it Accessible
The AWS Free Tier, as I mentioned, is a fantastic program that allows you to use many AWS services up to a certain limit without charge. For our remote IoT setup, this is particularly useful. You can often get a small EC2 instance (which will serve as our bastion host), some S3 storage, and a good amount of AWS IoT Core messaging for free for the first 12 months, or, in some cases, even longer.
It's really important, you know, to keep an eye on your usage to make sure you stay within these limits. AWS provides tools to monitor your consumption, and, you know, setting up budget alerts is a very smart move. This way, you can leverage the immense power of AWS for your Raspberry Pi projects without worrying about unexpected costs, which is, quite honestly, a huge benefit for hobbyists and learners.
Setting Up Your Secure Remote IoT Environment
Alright, let's get down to the practical steps. Setting up this secure remote access for your Raspberry Pi on AWS involves a few key stages. We'll start with your Pi, then move into the AWS console to build your private network, and finally, connect the two. Just follow along, and, you know, we'll get there together.
Step 1: Preparing Your Raspberry Pi
First things first, your Raspberry Pi needs to be ready. You'll want to make sure it's running the latest version of Raspberry Pi OS. You can download the image from the official Raspberry Pi website and flash it to an SD card. Once it's booted up and connected to your local network, you'll need to enable SSH.
You can do this by opening a terminal on your Pi and typing: sudo raspi-config. Then, navigate to "Interface Options" -> "SSH" and enable it. It's also a good idea, you know, to change the default password for the 'pi' user or, even better, set up SSH key-based authentication for stronger security. Make sure your Pi has a static IP address on your local network, or, you know, at least a reserved DHCP lease, so its IP doesn't change unexpectedly.
Step 2: Creating Your AWS VPC
Now, let's head over to the AWS Management Console. Search for "VPC" and open the service. We'll create a new VPC. You can use the "VPC Wizard" for a quick start, choosing the "VPC with a Single Public Subnet" option. This will set up a VPC, an Internet Gateway, a route table, and a public subnet.
When you configure it, choose a CIDR block for your VPC (e.g., 10.0.0.0/16). This defines the IP address range for your private network. Give your VPC and subnet descriptive names, like "RemoteIoT-VPC" and "RemoteIoT-PublicSubnet". This initial setup, you know, gives us the basic network structure we need for our bastion host.
Step 3: Launching an EC2 Instance (Bastion Host)
Next, we'll launch a small EC2 instance that will act as our bastion host, the secure gateway to your Raspberry Pi. Go to the EC2 service in the AWS console and click "Launch Instance".
Choose an Amazon Machine Image (AMI) that's free tier eligible, like "Amazon Linux 2 AMI" or "Ubuntu Server 20.04 LTS (HVM)". For the instance type, select a "t2.micro" or "t3.micro" if available, as these are typically covered by the free tier. Make sure to select your newly created "RemoteIoT-VPC" and "RemoteIoT-PublicSubnet" for this instance.
During the setup, create a new key pair (e.g., "remote-iot-key") and download the .pem file. This key is crucial for SSHing into your EC2 instance. Configure a security group that allows SSH access (port 22) only from your specific public IP address. This is a very important security measure, you know, to restrict who can even attempt to connect to your bastion host. Give the instance a descriptive name, like "RemoteIoT-BastionHost", and launch it. It's, you know, a pretty straightforward process if you take your time.
Step 4: Configuring Security Groups and Network ACLs
Security is, basically, paramount here. We need to ensure that only authorized traffic can flow. For your EC2 bastion host's security group, as mentioned, allow inbound SSH (port 22) from your specific public IP. For outbound rules, allow all traffic (or, you know, specifically allow SSH to your Raspberry Pi's local IP if you want to be super strict).
Now, this is where it gets a little more advanced. To connect to your Raspberry Pi, it needs to be accessible from the bastion host. If your Raspberry Pi is on your home network, you'll need a way for the bastion host (which is in AWS) to reach it. This typically involves setting up a VPN or, you know, using a service like AWS IoT Core for device shadows, but for direct SSH, you'd usually have the Pi connect *out* to the bastion host, or use a tool like ngrok to expose it. However, for a truly secure VPC setup where the Pi is *inside* the VPC, you'd need a more complex setup like a Site-to-Site VPN or Direct Connect, which isn't free tier. So, for the "free" and "remoteiot vpc ssh raspberry pi aws free" context, we're assuming the Pi is *behind* your home router and the bastion host is the jump point. The Pi will either initiate a connection to the bastion, or you'll use a local network setup where the bastion can reach it via a local gateway (which is beyond free tier). The most practical free approach is for the Pi to *initiate* the SSH connection to the bastion, or use reverse SSH.
Let's refine this for the "free" and "remoteiot vpc ssh raspberry pi aws free" context. The Pi will be behind your home router. The bastion host is in AWS. For the bastion to SSH *into* the Pi, the Pi needs a public IP, or a VPN tunnel back to AWS, which isn't free. The most common "free" approach is for the Pi to establish a reverse SSH tunnel *to* the bastion host. This way, the Pi initiates the connection, punching through your home router's firewall, and then the bastion can connect back to the Pi through that tunnel.
So, for the bastion's security group, allow SSH (port 22) from your home IP. For the Pi, ensure its local firewall (ufw) allows SSH (port 22) from your bastion host's private IP address *if* it were directly in the VPC, but since it's not, we'll focus on the reverse SSH approach. Network ACLs (NACLs) can also be configured at the subnet level for an extra layer of stateless filtering, but for this basic setup, security groups are usually sufficient, you know.
Step 5: Establishing SSH Access to Your Raspberry Pi via EC2 (Reverse SSH Tunnel)
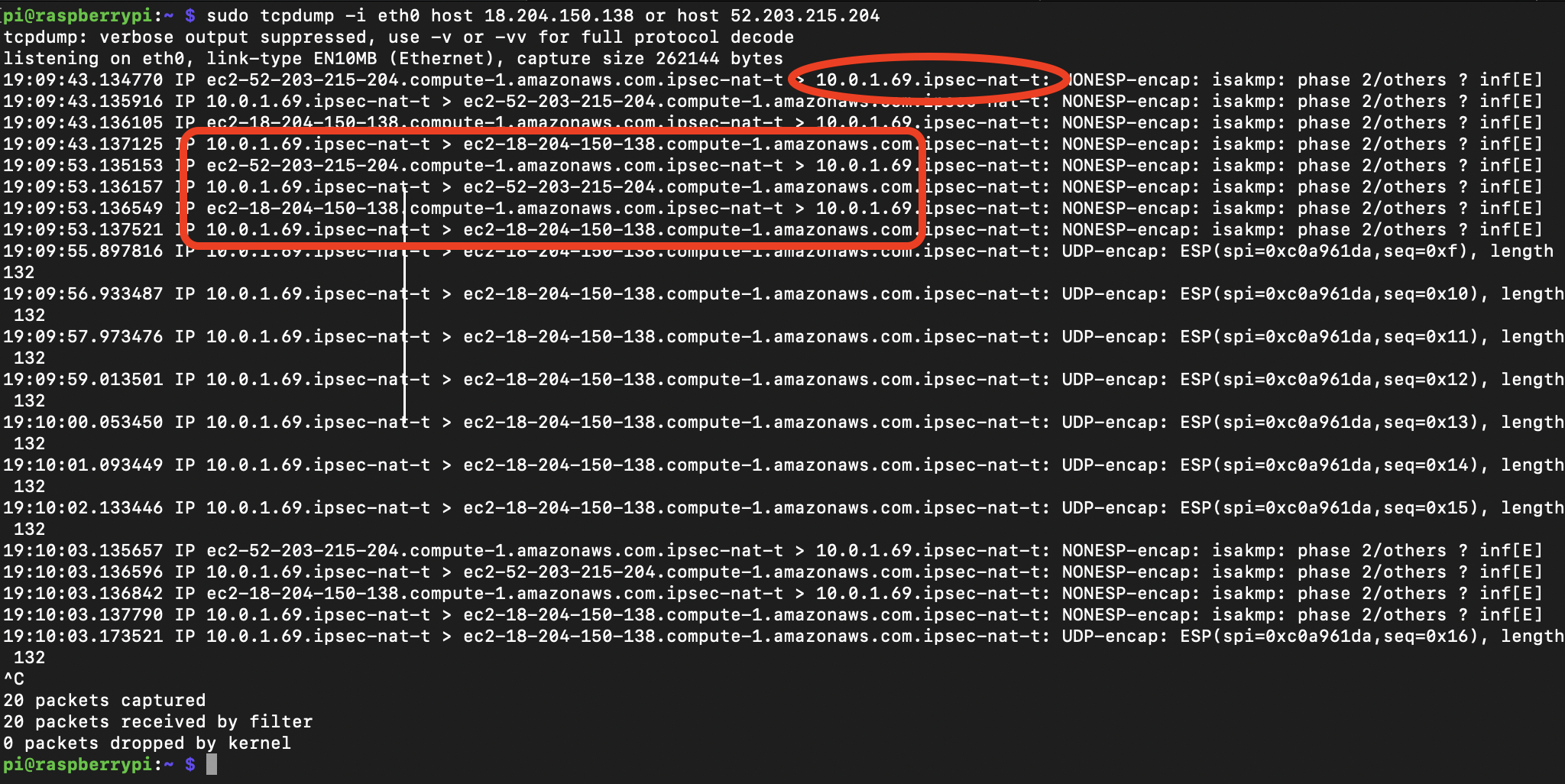
This is the clever part, really. Your Raspberry Pi will initiate an SSH connection to your EC2 bastion host, creating a reverse tunnel. This means the bastion host can then connect back to your Pi through that tunnel, even though your Pi is behind your home router.
On your Raspberry Pi, you'll run a command like this:
ssh -N -R 2222:localhost:22 -i /path/to/your/aws-key.pem ec2-user@YOUR_BASTION_PUBLIC_IP-N: Not execute a remote command (just forward ports).-R 2222:localhost:22: Forward port 22 (SSH) on your Pi to port 2222 on the bastion host.-i /path/to/your/aws-key.pem: Use your AWS SSH key for authentication.ec2-user@YOUR_BASTION_PUBLIC_IP: Connect to your bastion host.
Once this tunnel is active, from your local machine, you first SSH into your bastion host:
ssh -i /path/to/your/aws-key.pem ec2-user@YOUR_BASTION_PUBLIC_IPThen, from *within* the bastion host, you SSH into your Raspberry Pi using the forwarded port:
ssh -p 2222 pi@localhostAnd, just like that, you're securely connected to your Raspberry Pi, all through your AWS VPC and bastion host! This method, you know, is pretty robust for getting around NAT and firewalls at home.
Step 6: Automating Connections and Enhancing Security
Running that reverse SSH command manually on your Pi isn't ideal. You can automate it by adding it to your Pi's /etc/rc.local file (before exit 0) or, better yet, creating a systemd service that automatically starts and restarts the tunnel if it drops. This ensures your Pi is always trying to maintain its connection to the bastion host.
For even better security, consider disabling password authentication on your Raspberry Pi's SSH server and relying solely on SSH keys. Also, keep your AWS key pairs extremely secure and never share them. Regularly update your Raspberry Pi's software (sudo apt update && sudo apt upgrade) and your bastion host's packages. You can, you know, also set up monitoring on AWS to alert you to any unusual activity on your EC2 instance.
Common Challenges and Smart Solutions
Even with the best planning, you might run into a few bumps along the way. But don't worry, there are usually straightforward solutions. Let's look at some common issues and how to tackle them, because, you know, everyone hits a snag sometimes.
Keeping Costs Truly Free
The AWS Free Tier is amazing, but it does have limits. The biggest trap, you know, is often forgetting about data transfer costs or exceeding the free tier for EC2 instance hours. To keep things genuinely free, or at least very cheap:
- **Choose `t2.micro` or `t3.micro` instances:** These are typically free tier eligible for 750 hours per month. One instance running continuously for a month uses about 720 hours, so you're good with one.
- **Monitor Data Transfer:** Inbound data transfer to AWS is usually free, but outbound data transfer can incur charges. Keep your Raspberry Pi's data uploads small and infrequent if possible.
- **Set Up Billing Alerts:** This is, arguably, the most important step. In the AWS Billing console, configure alerts to notify you if your estimated monthly charges exceed a small amount (e.g., $1 or $5). This way, you'll get a heads-up before any significant charges accumulate, which, you know, is a huge peace of mind.
- **Clean Up Unused Resources:** If you're experimenting, remember to terminate EC2 instances, delete VPCs, and remove S3 buckets you no longer need. Unused resources can still accrue costs.
Managing Connectivity Drops
Your Raspberry Pi might lose its internet connection, or, you know, the reverse SSH tunnel could drop for various reasons. This can be frustrating when you need remote access. Here are some solutions:
- **Automate Tunnel Restart:** As mentioned, use a systemd service on your Raspberry Pi to ensure the reverse SSH tunnel automatically restarts if it fails. This is pretty much essential for reliable access.
- **Persistent SSH Sessions:** Use tools like `tmux` or `screen` on your bastion host. If your local SSH connection to the bastion drops, your `tmux` session (and the SSH connection from bastion to Pi) can remain active, allowing you to reattach later.
- **Health Checks:** Consider implementing a simple script on your Raspberry Pi that periodically pings an external service or sends a "heartbeat" message to an AWS IoT Core topic. If the heartbeat stops, you know your Pi is offline, which, you know, helps with troubleshooting.
- **Stable Internet:** Ensure your Raspberry Pi has a reliable internet connection at its physical location. A good Wi-Fi signal or, even better, a wired Ethernet connection can make a big difference, obviously.
Advanced Security Practices
While our setup is already quite secure, there are always ways to make it even more robust:
- **MFA for AWS Console:** Always enable Multi-Factor Authentication (MFA) for your AWS root account and any IAM users. This is, basically, non-negotiable for cloud security.
- **Least Privilege:** Configure IAM roles and policies on AWS to grant only the minimum necessary permissions to your EC2 instance. It's a good habit to only give what's needed, you know.
- **SSH Key Passphrases:** Protect your SSH private keys with strong passphrases. This adds another layer of security in case your key file is compromised.
- **Regular Audits:** Periodically review your AWS security groups, NACLs, and IAM policies to ensure they still meet your security requirements. Things change, and, you know, so should your security posture.
- **VPN Client on Pi:** For an even more secure and direct connection (though potentially not free tier), you could run a VPN client on your Raspberry Pi that connects to a VPN server within your AWS VPC. This would place your Pi directly into your private cloud network, which is, you know, a very strong security model.
Frequently Asked Questions (FAQs)
People often ask a few common questions when they're thinking about this kind of setup. Here are some of the popular ones:
Is the AWS Free Tier truly enough for a remote Raspberry Pi IoT project?
Yes, for many hobbyist or small-scale projects, the AWS Free Tier is, you know, absolutely sufficient. It provides enough EC2 compute time for a bastion host, a generous amount of data transfer, and even free usage for services like AWS IoT Core. The key, honestly, is careful resource management and monitoring your usage to stay within the limits. For instance, if you're sending very large files constantly, you might exceed the free data transfer, but for typical sensor data or occasional remote access, it's usually fine.
How secure is using SSH over a VPC for Raspberry Pi access?
Using SSH over a VPC, especially with a bastion host and reverse SSH tunnel, is, frankly, a very secure method. SSH itself encrypts all communication, protecting your data from eavesdropping. The VPC provides network isolation, and the bastion host acts as a controlled entry point, so your Raspberry Pi isn't directly exposed to the public internet. This multi-layered approach, you know, significantly reduces the attack surface compared to direct public exposure.
Can I connect multiple Raspberry Pis using this same AWS VPC and bastion host setup?
Absolutely! You can, you know, connect multiple Raspberry Pis using the same bastion host and VPC. Each Pi would establish its own reverse SSH tunnel to the bastion, but you'd need to assign a different remote port for each Pi on the bastion host (e.g., Pi 1 uses port 2222, Pi 2 uses port 2223, and so on). This allows you to differentiate and connect to each Pi individually through the same secure gateway, which is, you know, pretty convenient for managing a fleet of devices.
Ready to Build Your Remote IoT?
Connecting your Raspberry Pi to AWS using a VPC and SSH, especially leveraging the free tier, is, you know, a remarkably powerful way to manage your remote IoT projects. It offers a fantastic blend of security, flexibility, and affordability, allowing you to keep an eye on your devices and deploy updates from anywhere in the world. This setup gives you a solid foundation for all sorts of creative endeavors, from smart home automation to environmental monitoring, and, honestly, much more.
- Who Is Jennifer Kish Goggins
- Brett Seacat 2025
- Mickey Rooney Net Worth At Death
- Does Katie Pavlich Have Children
- Anthony Weiner Net Worth


Detail Author:
- Name : Prof. Adella Oberbrunner DVM
- Username : sonya.kuhic
- Email : ewalsh@schaden.org
- Birthdate : 1996-04-08
- Address : 3416 Sanford Hill Lake Eldora, IL 15310
- Phone : +1-484-769-6848
- Company : Hane, Ondricka and Ebert
- Job : Septic Tank Servicer
- Bio : Occaecati est saepe alias. Qui nobis repudiandae voluptatibus et mollitia in. Rerum consequatur ea laboriosam qui. In occaecati nihil aut architecto.
Socials
linkedin:
- url : https://linkedin.com/in/remington7832
- username : remington7832
- bio : Dolorem voluptatem nulla aut repudiandae.
- followers : 4093
- following : 2310
tiktok:
- url : https://tiktok.com/@remingtonconroy
- username : remingtonconroy
- bio : Et voluptates et et fugit omnis harum.
- followers : 1536
- following : 360
instagram:
- url : https://instagram.com/conroy2016
- username : conroy2016
- bio : Sit sequi est sed et recusandae dolores non. Non accusantium quis non pariatur asperiores at.
- followers : 6437
- following : 1235
twitter:
- url : https://twitter.com/conroyr
- username : conroyr
- bio : Fugiat ut omnis eum doloribus et officiis repellendus. Incidunt ea nemo debitis. Nobis ad temporibus illum eveniet. Ad est officiis quas quas autem aliquid et.
- followers : 5665
- following : 1551
facebook:
- url : https://facebook.com/remington_real
- username : remington_real
- bio : Nostrum corporis a dolorem soluta esse omnis.
- followers : 1171
- following : 2433