Keeping your internet-connected devices safe, especially those out in the world, feels like a big job. You know, with all the news about digital threats, it's easy to wonder how to truly protect your valuable equipment. This article talks about how to securely connect remote IoT devices using P2P SSH, which really helps keep unwanted visitors, like hackers, far away from your systems.
Think about the times you've seen messages pop up, like "This connection is untrusted," or maybe you've had trouble with files not saving right, as some people experience with things like crdownload files from browsers. These little issues can make you feel uneasy about digital safety, and that feeling, honestly, gets much bigger when we talk about devices that might be miles away. We want to avoid that sense of worry, so we look for solid ways to make sure everything stays private and works as it should, you know?
Today, we'll explore some ways to set up strong connections for your remote IoT gadgets. We're going to cover peer-to-peer (P2P) connections and how Secure Shell (SSH) can really make a difference in keeping things locked down. This is all about making sure your devices, whether they are sensors in a field or controls in a factory, stay under your command and out of reach from anyone who shouldn't be there. It's about taking charge of your digital space, as a matter of fact.
Table of Contents
- Understanding the IoT Security Challenge
- What is P2P and Why It Matters for IoT
- SSH: Your Digital Fortress for IoT
- Combining P2P and SSH for Ultimate IoT Protection
- Keeping Hackers at Bay: Best Practices
- Frequently Asked Questions About IoT Security
- Next Steps for Your IoT Security
Understanding the IoT Security Challenge
Remote IoT devices, you know, they bring so much good to our lives, from smart homes to massive industrial systems. But they also, frankly, bring some big security concerns right along with them. Imagine a device that's out in the wild, maybe collecting data, and it's not properly looked after. It could be like leaving a door wide open, you know, for anyone to just walk in. This is a real worry for many people, especially when personal or important information is involved.
Many of us have, as a matter of fact, seen how easily digital things can go wrong. Some folks have even found their web browsers acting strange, managed by an organization they don't belong to, or their devices showing warnings about being "at risk" because of missing updates. These are small reminders of how quickly things can become vulnerable. For IoT, the stakes are often much higher, with physical systems sometimes depending on these connections. So, keeping these devices safe, really, is a top priority for anyone using them, you know?
The problem is that many IoT devices are made for convenience, sometimes without enough thought put into their protection. They might use default settings, or have simple ways to get into them, which is not great for keeping things private. This makes them, well, a pretty tempting target for people who want to cause trouble, or frankly, just snoop around. So, figuring out how to connect these devices in a way that truly keeps them safe from such attempts is something we all need to understand, I mean, it's pretty important.
- Jon Skoog Net Worth
- Jimmy Uso First Wife
- Jasmine Crockett Husband Net Worth
- Sensualsunshine Leaked
- Is James May Gay
What is P2P and Why It Matters for IoT
P2P, or peer-to-peer, networking is a way for devices to talk directly to each other, without needing a big central server in the middle. Think of it like two friends talking on a walkie-talkie, rather than having to go through a phone company's huge system. This direct connection can be really helpful for remote IoT devices, especially when they are in places where a central server might be hard to reach or, you know, just too expensive to set up. It's a pretty neat idea, actually.
Traditional Client-Server vs. P2P
Usually, when you connect to something online, your device acts as a "client," and it talks to a "server." The server is like a big hub that handles all the requests and sends back the information. This works well for many things, but for IoT, especially in far-off places, it can have some problems. If the server goes down, or if the connection to it is weak, your devices might not be able to talk at all. P2P, on the other hand, just lets your devices find each other and communicate directly, which, you know, can be a lot more reliable in some situations.
With P2P, there isn't a single point of failure that can bring everything to a halt, which is pretty good, you know? It means your remote sensors or actuators can keep doing their job, even if the internet connection to a central cloud service gets a bit shaky. This kind of setup, honestly, offers a different kind of strength, one that comes from many independent connections working together. It’s a bit like having many paths to get somewhere instead of just one main road.
Benefits of P2P for Remote IoT
One big plus for P2P in IoT is that it can reduce the need for a lot of internet bandwidth. Since devices talk directly, they don't have to send all their data through a central server and then back again. This can save money on data plans, which is pretty nice. Also, it can make things happen faster, because there's less distance for the information to travel. It's a bit like, you know, cutting out the middleman.
Another benefit, and this is a big one, is that P2P can make your system more resilient. If one device or connection goes down, the others can often still communicate. This is a really important feature for critical IoT applications, where, frankly, you can't afford any downtime. It also, in some respects, gives you more control over your data, since it's not all passing through a third-party server. This is something many people are looking for these days, you know, more privacy and control.
SSH: Your Digital Fortress for IoT
SSH, which stands for Secure Shell, is basically a very strong way to get into a computer or device from somewhere else. It's like having a secret, super-tough tunnel that only you can use to send commands and get information. This is really important for IoT devices because they often need to be managed or updated when you're not physically next to them. Without something like SSH, trying to access them remotely could be, well, a bit like shouting your secrets across a crowded room, you know?
When you hear about people having issues with "untrusted connections," maybe like those warnings in Firefox or other browsers, it highlights how important it is to know that your connection is actually safe. SSH gives you that assurance. It makes sure that whatever you send or receive from your remote device is kept private and hasn't been changed by anyone else. This protection is, honestly, a must-have for any serious IoT setup, so, it's pretty essential.
How SSH Works Its Magic
SSH uses some really clever math to scramble, or encrypt, all the information that passes through it. This means that even if someone manages to intercept your communication, they won't be able to understand it. It's all just gibberish to them. Plus, SSH makes sure that the device you're talking to is actually the device you think it is, and not some impostor. This is a big deal, because, you know, you don't want to accidentally give commands to the wrong system.
The way it works is, basically, when you try to connect, your computer and the remote device do a sort of secret handshake. They agree on a way to encrypt everything, and they check each other's identities. Only when both sides are happy and have confirmed who they are, does the connection fully open. This whole process happens very quickly, and it provides a very high level of protection, making it, frankly, a go-to tool for anyone serious about digital safety, especially for remote access, you know?
SSH Key Authentication: A Stronger Lock
While SSH can use passwords, a much stronger way to prove who you are is with something called SSH keys. Think of it like having a special, very complex digital key and lock. You keep one part of the key (the private key) completely secret on your computer, and you put the other part (the public key) on your remote IoT device. When you try to connect, these two parts match up, and if they fit, you're in. There's no password to type, which, you know, means there's no password for someone else to guess or steal.
This method is, frankly, much more secure than using just a password, even a really good one. Passwords can be weak, or they can be found out through various means, but SSH keys are extremely hard to break. It's a bit like replacing a regular padlock with a bank vault door. This is a practice that many security experts strongly suggest, especially for devices that are important or out of your immediate sight. It's a definite step up in keeping things safe, you know, for your devices.
Combining P2P and SSH for Ultimate IoT Protection
When you put P2P and SSH together, you get a really powerful way to manage your remote IoT devices. P2P gives you that direct, flexible connection, letting your devices talk without a central hub. Then, SSH wraps that conversation in a very strong layer of protection, making sure no one can listen in or pretend to be one of your devices. It's like having a private, secure phone line straight to each of your gadgets, which, you know, is pretty cool.
This combination helps solve many of the worries people have about IoT security. You know, like when you're concerned about your device being "at risk" because it's not up to date, or when you feel like your browser is being managed by someone else. With P2P and SSH, you gain a lot more control and confidence that your remote systems are truly yours and that their communications are private. It's a way to take back that feeling of digital safety, honestly.
Setting Up a Secure P2P SSH Connection
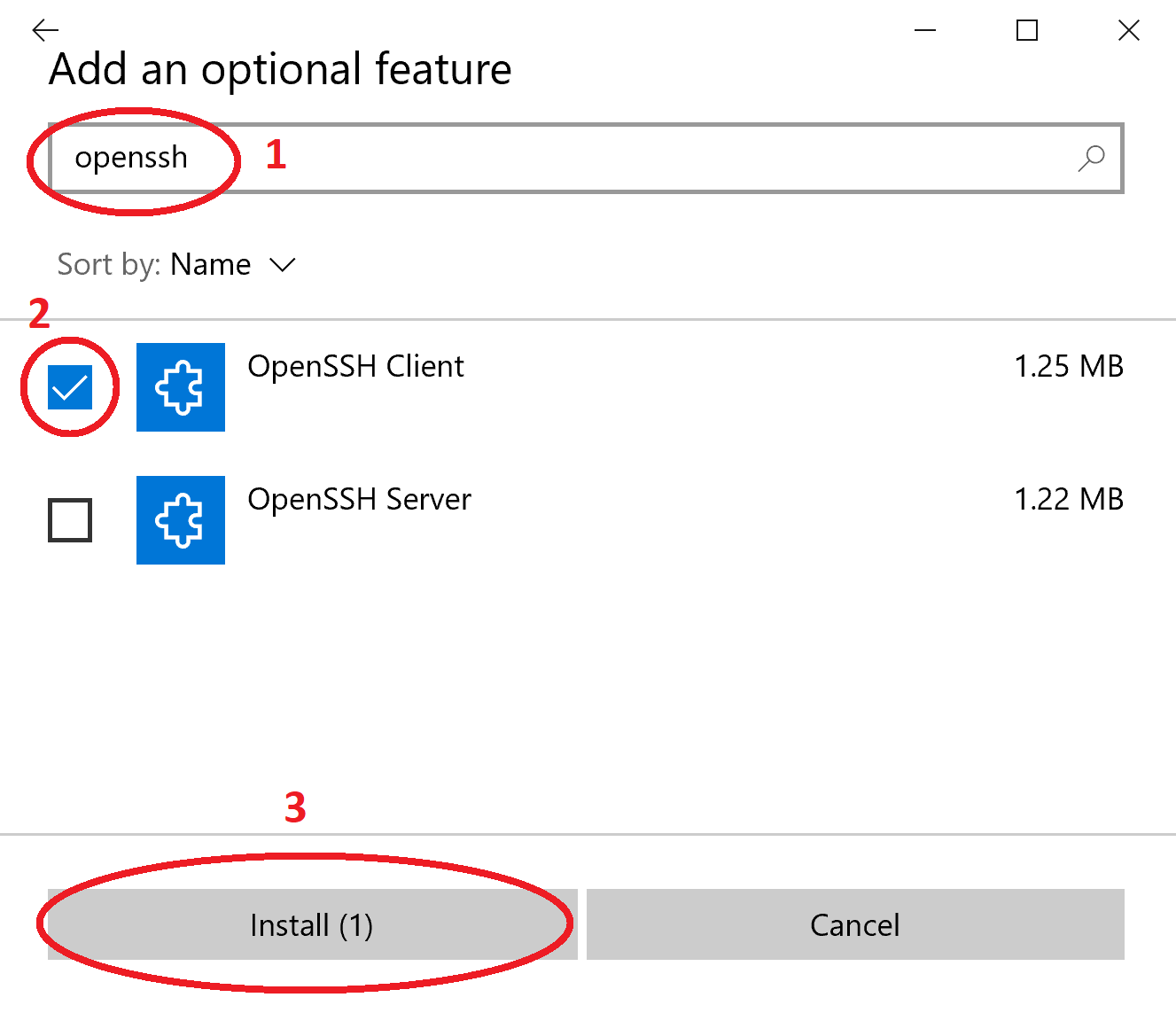
Getting this kind of setup going involves a few steps, but it's totally doable. First, you'll need to make sure your IoT devices are ready for SSH. This usually means installing an SSH server on them. Then, you'll generate those SSH keys we talked about earlier. You'll put the public key on each of your remote devices and keep the private key safe on your local computer. This is, arguably, the most important part of the whole process.
For the P2P part, you might use a tool or service that helps devices find each other directly, even if they're behind different internet routers. There are some clever ways to do this, often called "hole punching" or using specific P2P frameworks. Once the P2P connection is established, you then use SSH over that connection. It sounds a bit involved, but many guides and tools exist to help you through it. It’s a bit like building a custom bridge, you know, to get to your devices safely.
Real-World Scenarios for Secure IoT Access
Imagine you have a bunch of sensors monitoring soil moisture in a large agricultural field. They're far from any central office, and running wires for a regular network would be too much work. With P2P SSH, each sensor could, in some respects, talk directly to your main monitoring station, sending its data securely. You could also, you know, log into a specific sensor via SSH to check its status or update its software, all without leaving your desk.
Another example could be a smart factory with various machines needing remote maintenance. Instead of opening up the entire factory network to the internet, which would be a huge risk, each machine could establish a P2P SSH connection when needed. This way, a technician could securely access just the one machine that needs attention, and only for the time required. It's a much more controlled and, frankly, safer way to work, reducing the chances of any unwanted access, you know, from outside.
Keeping Hackers at Bay: Best Practices
Even with P2P and SSH, there are still things you need to do to keep your IoT setup truly safe. Think of it like having a strong lock on your door, but still needing to remember to close the door and maybe check the windows. These practices are, honestly, just good common sense for anything connected to a network, but they are extra important for remote IoT devices that might be out of sight. They help you maintain that feeling of control, you know, over your own systems.
Remember those times when you might have gotten warnings about your device being "at risk" because it's out of date? That's a perfect example of why these practices matter. A strong connection is only as good as the system it's connecting to. So, keeping everything in good shape, really, is a continuous effort. Learn more about IoT security on our site, and link to this page here for more detailed guides.
Regular Updates and Maintenance
This is probably one of the simplest, yet most overlooked, steps. Device makers often release updates that fix security holes or make things work better. If you don't install these updates, your devices could be left open to known problems that hackers already know how to exploit. It's a bit like, you know, leaving a known weakness in your defenses. So, make it a habit to check for and apply updates regularly, for all your IoT gadgets, as a matter of fact.
Just like you wouldn't want your personal computer to be running old, insecure software, your IoT devices need the same care. This also includes keeping the operating system and any software on the device up to date. Sometimes, people forget about these "headless" devices, but they need just as much attention, if not more, because they often operate without much direct human interaction. So, staying on top of updates is, frankly, a crucial part of keeping everything running smoothly and safely.
Strong Passwords and Key Management
Even if you're using SSH keys, there might still be places where passwords are needed, perhaps for local access or for other services. Always use long, complex passwords that are unique for each device. Never use default passwords! Those are, frankly, the first things any would-be intruder tries. And for your SSH keys, treat your private key like gold. Keep it on a secure computer, maybe even with an extra password on the key itself. Losing it would be, you know, a big problem.
Proper management of these keys is, arguably, just as important as creating them. Make sure you know where your keys are stored, and who has access to them. If an employee leaves, for example, you should revoke their access keys. This kind of careful handling helps prevent unauthorized entry, which, honestly, is a cornerstone of good digital protection. It's about being diligent with your digital credentials, you know, at all times.
Network Segmentation and Firewalls
Think of your network as a house. You wouldn't leave all the rooms connected with no doors, right? Network segmentation means dividing your network into smaller, isolated parts. So, your IoT devices could be in one segment, your office computers in another. If someone manages to get into one segment, they can't easily jump to another. Firewalls then act like security guards, controlling what traffic can go in and out of each segment. This adds, frankly, a very strong layer of defense.
This practice is especially useful for IoT, where a compromised device in one part of your system shouldn't be able to affect everything else. It limits the damage an intruder can do, which is pretty important. Configuring firewalls to only allow necessary connections, like your SSH connections, and block everything else, makes it much harder for unwanted traffic to get through. It’s a very practical step for anyone looking to seriously boost their network protection, you know, for their devices.
Monitoring and Logging
Knowing what's happening on your network and with your devices is, honestly, a huge part of keeping them safe. Set up your devices to record, or "log," important events, like login attempts, failed connections, or unusual activity. Then, regularly review these logs. It's like having a security camera system that records everything that happens. If someone tries to get in, or if something goes wrong, you'll have a record of it. This helps you catch problems early, which is pretty good.
There are tools available that can automatically monitor your network and alert you to anything suspicious. This is, arguably, much better than manually checking logs all the time. Being proactive about watching your systems can make a big difference in preventing a small issue from becoming a big problem. It’s about having eyes on your digital perimeter, you know, at all times, to ensure everything is as it should be.
Frequently Asked Questions About IoT Security
People often have questions about how to keep their connected devices safe. Here are a few common ones, with some straightforward answers, you know, to help clear things up.
What are the biggest risks for remote IoT devices?
Honestly, the biggest risks for remote IoT devices often come from not keeping them updated, using weak passwords, or having open network ports that shouldn't be open. Think of it like leaving a window unlocked or, you know, having a very easy-to-guess code for your alarm system. These things make it much simpler for someone to gain unauthorized access. Also, sometimes the devices themselves have problems in their basic design that can be exploited, which is pretty bad.
How can I tell if my IoT device has been compromised?
You might notice strange behavior from your device, like it's turning on or off by itself, sending data when it shouldn't, or making unusual network connections. Sometimes, you might see a sudden increase in its data usage, or it might just stop working correctly. Checking the device's activity logs, if it has them, can also show unauthorized login attempts or unusual commands. It's about looking for anything out of the ordinary, you know, something that just doesn't feel right.
Is P2P SSH really more secure than other methods?
When set up correctly, P2P SSH offers a very strong level of protection for remote IoT connections. It combines the directness of peer-to-peer communication with the robust encryption and authentication of SSH. This often makes it more secure than methods that rely on less protected protocols or that route all traffic through potentially vulnerable central servers. It's a bit like, you know, building a custom, armored path just for your important messages, which is pretty good.
Next Steps for Your IoT Security
Taking steps to secure your remote IoT devices with P2P SSH is a smart move, especially in today's digital world, you know. It gives you a strong foundation for keeping your systems safe from unwanted intrusions. Remember, keeping things secure isn't a one-time job; it's an ongoing process that needs your attention, honestly, all the time. Stay informed, keep your systems updated, and use these powerful tools to maintain control.
For more detailed information on specific tools or configurations, you might want to check out resources like the National Institute of Standards and Technology (NIST) guidelines on IoT security, which offer a lot of good advice. You can find some of their publications on their official website, NIST Cyber Security Framework. This will help you, you know, stay ahead of the game and keep your devices protected for the long haul.
- Yemada Onlyfans Leaks
- Christian And Maria Arranged 2025
- Dr Drew Net Worth
- Jason Kennedy Public Figure Latest
- Is Harry Richardson Married

Detail Author:
- Name : Lera Mertz DDS
- Username : schultz.daisy
- Email : emurazik@collins.com
- Birthdate : 1997-07-15
- Address : 4692 Wilbert Vista Jaydonton, KS 45460
- Phone : 424.335.1124
- Company : Ferry, King and Bergnaum
- Job : Advertising Manager OR Promotions Manager
- Bio : Aut natus et alias dolor repudiandae suscipit. Illo soluta ab aut consequatur maiores. Molestias quis qui magni vel saepe cum distinctio.
Socials
linkedin:
- url : https://linkedin.com/in/ahmedbaumbach
- username : ahmedbaumbach
- bio : Minima vel minus cumque ut magni.
- followers : 2779
- following : 1142
tiktok:
- url : https://tiktok.com/@ahmed4879
- username : ahmed4879
- bio : Voluptate minima et incidunt corrupti distinctio dolorem.
- followers : 3062
- following : 1204
twitter:
- url : https://twitter.com/baumbach2023
- username : baumbach2023
- bio : Sit et ipsam quidem incidunt ea et. Non voluptatem eos odio et. Similique nostrum quis consequatur.
- followers : 5922
- following : 2714