Imagine being able to reach your tiny computer, a Raspberry Pi, from anywhere in the world, managing its tasks and pulling important data, all while feeling completely secure. This is the dream for many looking into remote IoT projects, and it's something quite achievable with the right setup. Getting your Raspberry Pi talking to the Amazon Web Services (AWS) cloud through a Virtual Private Cloud (VPC) and SSH gives you that powerful, private connection.
Many folks, you know, find it a bit tricky to get their small devices online in a way that feels truly safe. Public internet connections can be a little like leaving your front door open, which isn't ideal for important projects. That's where a private cloud setup, like a VPC, really shines. It creates a secluded corner of the internet just for your things, so to speak.
This article will walk you through setting up a secure channel for your Raspberry Pi. We'll explore how to use AWS VPC and SSH to connect, manage, and even download files to your Pi, so you can keep your remote IoT projects running smoothly. You'll, like, discover how to bring your small device into the big cloud world with confidence.
Table of Contents
- The Big Picture: Why Remote IoT with AWS and Raspberry Pi Matters
- Getting Ready: What You'll Need
- Building Your Secure Space: AWS VPC Configuration
- Preparing Your Pi for the Cloud Connection
- Making the Connection: SSH into Your Raspberry Pi
- Grabbing Files: Downloading from AWS to Your Raspberry Pi
- Keeping Things Safe: Security Pointers
- Common Questions Answered (FAQs)
- When Things Go Wrong: Simple Troubleshooting Tips
The Big Picture: Why Remote IoT with AWS and Raspberry Pi Matters
Having your Raspberry Pi connected to AWS through a VPC, with SSH for access, opens up a world of possibilities for your projects, you know. It means your little computer isn't just sitting there in your house; it's part of a bigger, more powerful system. This setup is really good for things like home automation, environmental monitoring, or even small-scale data collection in far-off places. Basically, it lets your Pi do its job and send information back securely.
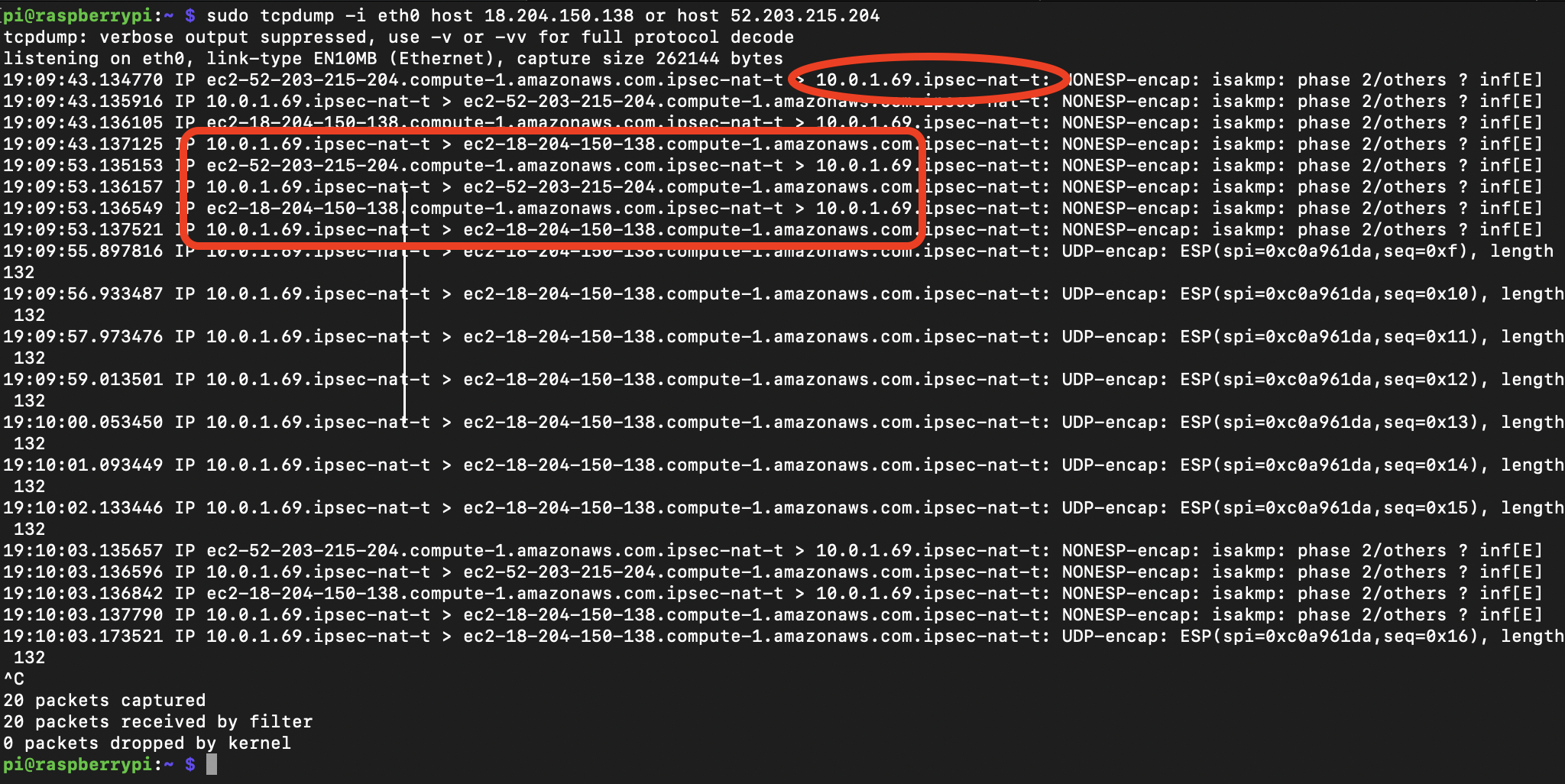
One of the biggest advantages, as a matter of fact, is the added security. A VPC creates a private network inside AWS, so your Raspberry Pi isn't directly exposed to the wide-open internet. SSH, or Secure Shell, then gives you an encrypted way to talk to your Pi, so your commands and data stay private. This combination means you can manage your device from anywhere, knowing your connection is pretty much locked down.
This approach also helps with scalability, which is important. If you start with one Raspberry Pi and later decide you need ten or twenty, this cloud-based method makes it much simpler to add more devices and manage them all from a central spot. You can, for example, push updates or pull data from many devices without a lot of extra fuss.
- Cardinals Roster Issues
- Was Chris Kyle A Fraud
- Thiccasianbaddie Onlyfans Leaked
- Ava Louise Onlyfans Leak
- Celina Smith Nude
Getting Ready: What You'll Need
Before we get too deep into the setup, it's good to have a few things in order. Gathering your tools and making sure everything is ready will make the whole process go a lot smoother, you know. Think of it like getting your ingredients ready before you start cooking a meal.
Your Raspberry Pi Setup
You'll need a working Raspberry Pi, of course, with its operating system installed. Most people use Raspberry Pi OS (formerly Raspbian), and that works just fine. Make sure your Pi is connected to the internet, at least for the initial setup and updates. A good quality power supply is also important, as a matter of fact, to keep your Pi running without unexpected shutdowns.
It's also a good idea to have a keyboard, mouse, and monitor connected to your Pi for the very first steps, just to make sure everything is booting up correctly. Once we get SSH working, you won't need these anymore, which is handy for remote use. Make sure you know your Pi's local IP address, too, as that will be helpful for the initial local connections.
An AWS Account
You'll need an active AWS account. If you don't have one, you can sign up for the AWS Free Tier, which gives you a good amount of free usage for many services, including the ones we'll be using. Just be mindful of the limits to avoid unexpected charges. Setting up billing alerts is a good practice, by the way, to keep track of your usage.
Make sure you have administrative access to your AWS account, or at least the necessary permissions to create VPCs, EC2 instances, and security groups. This is pretty much essential for making all the changes we'll need. You'll also want to choose an AWS region that's geographically close to you or your Raspberry Pi, as that can help with connection speeds.
Basic Command Line Skills
This project involves working with the command line on both your local computer (or a jump box) and your Raspberry Pi. You don't need to be a super expert, but knowing how to open a terminal, run commands, and understand basic file paths will be really helpful. Things like `ssh`, `scp`, and `sudo` will be our main tools, you know.
If you're new to the command line, there are plenty of resources online to help you get comfortable with the basics. Practice makes perfect, and pretty soon, these commands will feel like second nature. It's actually a very powerful way to interact with computers, especially for devices like the Raspberry Pi.
Building Your Secure Space: AWS VPC Configuration
The Virtual Private Cloud (VPC) is where we'll build our secure little network within AWS. Think of it as your own private piece of the AWS infrastructure, where you get to decide who comes in and out. This is where, essentially, your Raspberry Pi will feel safe and sound.
Setting Up Your VPC and Subnets
First, go to the AWS Management Console and search for "VPC." You'll want to create a new VPC. Give it a name that makes sense to you, like "MyPiVPC." For the IPv4 CIDR block, you might choose something like `10.0.0.0/16`. This range gives you a lot of IP addresses to work with, which is handy.
Within your VPC, you'll need at least two subnets: one public and one private. The public subnet will host our "jump box" (an EC2 instance we'll use to connect to the Pi), and the private subnet is where your Raspberry Pi will live. For example, your public subnet might use `10.0.1.0/24` and your private subnet `10.0.2.0/24`. Make sure each subnet is in a different Availability Zone for better resilience, you know.
Creating an Internet Gateway
An Internet Gateway (IGW) allows resources in your public subnet to connect to the internet. Your jump box will need this to let you SSH into it from your local machine. Create an IGW and then attach it to your newly created VPC. This is a pretty straightforward step, actually, but a very important one for external access.
Without an Internet Gateway, nothing in your VPC could talk to the outside world, which would make our jump box pretty useless for connecting from your home computer. It's basically the bridge between your private cloud and the public internet, so to speak.
Route Tables for Traffic Control
Route tables tell your network traffic where to go. You'll need to adjust the route tables for both your public and private subnets. For your public subnet's route table, you'll add a route that sends all internet-bound traffic (0.0.0.0/0) to your Internet Gateway. This ensures your jump box can reach the internet.
For your private subnet's route table, you generally won't have a direct route to the Internet Gateway. Instead, traffic might go through a NAT Gateway (if your Pi needs to initiate outbound connections to the internet) or just stay within the VPC. For our SSH connection, the traffic will mostly stay within the VPC, which is good for security, you know. Learn more about VPC routing on our site.
Security Groups: Your Digital Bouncers
Security groups act like firewalls for your instances. You'll create two main security groups: one for your jump box and one for your Raspberry Pi. The jump box security group should allow inbound SSH traffic (port 22) from your specific public IP address (or a known range if you're comfortable with that). This is the only way you'll get into the jump box.
For your Raspberry Pi's security group, you'll allow inbound SSH traffic (port 22) *only* from the security group of your jump box. This means only your jump box can initiate an SSH connection to your Pi, creating a very tight and secure pathway. It's a bit like having a special pass to get into a club, where only certain people with the right pass can even get to the door, you know.
Preparing Your Pi for the Cloud Connection
Now that your secure AWS network is taking shape, it's time to get your Raspberry Pi ready to join in. A little bit of setup on the Pi itself will make all the difference, as a matter of fact, for a smooth connection.
OS Updates and SSH Enablement
First things first, make sure your Raspberry Pi's operating system is completely up to date. Open a terminal on your Pi and run these commands:
sudo apt update sudo apt upgrade -yThis ensures you have all the latest security patches and software. Next, you need to enable SSH on your Raspberry Pi. You can do this through the `raspi-config` tool by typing `sudo raspi-config`, going to "Interface Options," and enabling SSH. Alternatively, you can create an empty file named `ssh` in the boot partition of your SD card before you even start the Pi, and it will enable SSH automatically, you know.
Generating SSH Keys
Using SSH keys is much more secure than relying on passwords. You'll generate an SSH key pair on your local machine (the computer you're using right now) and another pair on your Raspberry Pi. The public key from your local machine will go onto your jump box, and the public key from your jump box will go onto your Raspberry Pi.
On your local machine, open a terminal and type `ssh-keygen -t rsa -b 4096`. Follow the prompts, and it's a good idea to set a strong passphrase for your private key. Do the same on your Raspberry Pi: `ssh-keygen -t rsa -b 4096`. This creates two sets of keys, which is pretty important for our secure chain.
You'll then need to copy the public key (`id_rsa.pub`) from your local machine to your EC2 jump box's `~/.ssh/authorized_keys` file. Similarly, copy the public key from your EC2 jump box to your Raspberry Pi's `~/.ssh/authorized_keys` file. This basically tells each machine, "Hey, this other machine has permission to connect," you know.
Making the Connection: SSH into Your Raspberry Pi
With your AWS network set up and your Raspberry Pi ready, it's time to bring them together. We'll use a "jump box" to create a secure path, which is a rather common practice for reaching devices in private networks.
Launching an EC2 Instance (Jump Box)
Go back to the AWS Management Console and launch a new EC2 instance. This will be your jump box. Choose a small, inexpensive instance type, like a `t2.micro`, as it doesn't need a lot of computing power. Make sure to launch it into your *public* subnet within the VPC you created.
When you configure the instance, associate it with the security group you made for the jump box, which allows SSH from your home IP. Also, when prompted to create or select a key pair, use the public key you generated on your *local machine*. This will let you SSH into the jump box from your home computer, which is, like, the first step in our connection chain.
Once the EC2 instance is running, grab its public IP address. You'll use this to connect to it from your local machine. It's basically the front door to your private AWS network, you know.
Connecting to Your Pi via the Jump Box
Now for the fun part! From your local machine, you'll first SSH into your EC2 jump box. Use the command:
ssh -i /path/to/your/local/private_key.pem ec2-user@YOUR_EC2_PUBLIC_IPReplace `/path/to/your/local/private_key.pem` with the actual path to your private key file, and `YOUR_EC2_PUBLIC_IP` with the public IP of your EC2 instance. Once you're logged into the jump box, you'll then SSH from there to your Raspberry Pi. For this to work, you need to have copied your Raspberry Pi's public key to the jump box's `authorized_keys` file, as mentioned earlier.
The command from the jump box to your Pi will look something like this:
ssh -i /path/to/your/jump_box/private_key.pem pi@YOUR_RASPBERRY_PI_PRIVATE_IPThe `YOUR_RASPBERRY_PI_PRIVATE_IP` is the IP address your Raspberry Pi has within your AWS private subnet. You might need to set up a static IP for your Pi or use its assigned private IP. If you've set up SSH agent forwarding, you can simplify this a bit, too, which is handy. You've now, essentially, created a secure tunnel right to your Pi!
Grabbing Files: Downloading from AWS to Your Raspberry Pi
Once you have that secure SSH connection, moving files between your AWS environment and your Raspberry Pi becomes pretty straightforward. This is where the "download" part of our keyword really comes into play, you know.
Using SCP or SFTP for Transfers
SCP (Secure Copy Protocol) and SFTP (SSH File Transfer Protocol) are your best friends for moving files over an SSH connection. You can use these from your local machine, tunneling through your jump box, or directly from the jump box if the files are there.
To copy a file from your jump box to your Raspberry Pi, while you are already SSH'd into the jump box, you might use:
scp /path/to/file_on_jump_box pi@YOUR_RASPBERRY_PI_PRIVATE_IP:/path/to/destination_on_piIf you want to copy a file from your local machine directly to your Pi, tunneling through the jump box, it gets a little more complex but is still very doable with SSH's proxy jump feature. This allows you to specify an intermediate host. It's like telling your package to go through a specific post office before reaching its final destination, you know. This is a very common way to transfer things.
AWS CLI on Your Pi (Optional, but Handy)
For more advanced interactions, like downloading files directly from AWS S3 buckets to your Raspberry Pi, you can install the AWS Command Line Interface (CLI) on your Pi. This lets your Pi talk directly to many AWS services. First, SSH into your Raspberry Pi.
Then, you'll install the AWS CLI. The process typically involves downloading an installer script and running it. For example:
curl "https://awscli.amazonaws.com/awscli-exe-linux-arm.zip" -o "awscliv2.zip" sudo apt install unzip unzip awscliv2.zip sudo ./aws/installAfter installation, you'll need to configure it with AWS access keys and secret keys. It's very important to create an IAM user with minimal permissions just for your Pi, rather than using your root account credentials. This way, your Pi only has access to what it absolutely needs, which is a good security practice. Then you can use commands like `aws s3 cp s3://your-bucket-name/your-file.txt /home/pi/downloads/` to pull files down, you know. You can find more details on AWS VPC documentation.
Keeping Things Safe: Security Pointers
Security is, arguably, the most important part of any remote setup. A few simple practices can go a long way in keeping your Raspberry Pi and your AWS environment safe from unwanted visitors. It's like putting good locks on your doors and windows.
Always use SSH keys instead of passwords for all your connections. Passwords can be guessed, but SSH keys are much harder to crack. Make sure your private keys are stored securely on your local machine and protected by a strong passphrase. Never share your private keys with anyone, you know.
Keep your Raspberry Pi's operating system and all its software updated regularly. Software updates often include security patches that fix known weaknesses. Limit the services running on your Pi to only what's absolutely necessary. Every open port or running service is a potential entry point for someone trying to get in.
On the AWS side, be very specific with your security group rules. Only open ports that are truly needed, and restrict access to specific IP addresses or other security groups whenever possible. For example, allowing SSH from `0.0.0.0/0` (anywhere on the internet) is generally a bad idea for your jump box. Always use the least privilege principle for IAM roles and users, too, which means giving them only the permissions they need to do their job, and nothing more. This is, basically, a cornerstone of cloud security.
Common Questions Answered (FAQs)
Many people have similar questions when setting up something like this. Here are some common ones that might be on your mind, you know.
How do I securely access my Raspberry Pi from anywhere using AWS?
You access your Raspberry Pi securely by setting up an AWS Virtual Private Cloud (VPC) with private subnets for your Pi. Then, you use an EC2 instance as a "jump box" in a public subnet. You SSH into the jump box from your local machine, and from there, you SSH into your Raspberry Pi. All connections should use SSH keys for strong encryption, and security groups should strictly control who can connect to what. This creates a secure tunnel, so to speak, from your computer right to your Pi.
What's the best way to transfer files from AWS to a Raspberry Pi over a private connection?
The best way to transfer files is by using SCP (Secure Copy Protocol) or SFTP (SSH File Transfer Protocol) over your established SSH connection. You can initiate these transfers from your local machine, tunneling through your jump box to your Raspberry Pi. For direct downloads from AWS services like S3, installing the AWS CLI on your Raspberry Pi allows you to pull files directly, assuming your Pi has the correct IAM role or access keys configured. This is, very, efficient for moving data.
Can I use a VPC to manage multiple Raspberry Pis for IoT projects?
Absolutely, you can! A VPC is an excellent way to manage multiple Raspberry Pis. You would place each Raspberry Pi in the private subnet of your VPC. You could then use your single jump box to SSH into each of them, or even set up a fleet management system using AWS IoT Core, which integrates well with VPCs. This approach makes it much easier to scale your IoT project and keep all your devices under a unified, secure network umbrella, which is, actually, a huge benefit.
When Things Go Wrong: Simple Troubleshooting Tips
Even with the best planning, sometimes things don't quite work as expected. Don't worry, that's a pretty normal part of working with technology, you know. Here are some simple things to check if you run into trouble.
If you can't SSH into your EC2 jump box from your local machine, first check your security group rules for the jump box. Is port 22 open? Is your public IP address allowed? Also, make sure you're using the correct private key file and that its permissions are set correctly (e.g., `chmod 400 your_key
- Cicely Yasin Bernhard
- Susan Powter Documentary
- Dem Root Word
- Yahoo Serious Net Worth
- Czech Swap Wife


Detail Author:
- Name : Prof. Caitlyn Lindgren IV
- Username : dietrich.brown
- Email : rylan.runte@yahoo.com
- Birthdate : 1998-05-07
- Address : 8574 Ruthie Islands Noemyburgh, GA 31502
- Phone : 743-286-9233
- Company : Lehner, Little and Skiles
- Job : Tree Trimmer
- Bio : Qui aut blanditiis a qui unde consectetur excepturi. A tempora delectus eum qui. Cumque vitae in illum ex quisquam adipisci doloremque.
Socials
tiktok:
- url : https://tiktok.com/@mariane_hudson
- username : mariane_hudson
- bio : Dolor ut commodi minima. Aspernatur et vel laborum libero fugit.
- followers : 2455
- following : 87
facebook:
- url : https://facebook.com/hudsonm
- username : hudsonm
- bio : Inventore assumenda perferendis ab sit non est in.
- followers : 2120
- following : 2075
linkedin:
- url : https://linkedin.com/in/mhudson
- username : mhudson
- bio : Porro perferendis quis dicta minima et atque et.
- followers : 5639
- following : 2556
twitter:
- url : https://twitter.com/mariane_official
- username : mariane_official
- bio : Deserunt omnis consectetur veniam ab quos sint. Debitis repellat molestiae qui delectus qui temporibus totam. Et nulla nostrum quae recusandae assumenda qui.
- followers : 1347
- following : 829
instagram:
- url : https://instagram.com/mhudson
- username : mhudson
- bio : Quae aut in et explicabo quis. Sit iusto id magnam optio sequi quis.
- followers : 3692
- following : 2457