Ensuring your remote IoT devices communicate safely with your AWS Virtual Private Cloud (VPC) is, you know, absolutely essential in today's interconnected world. Think about all the data these devices collect and transmit, whether it's sensor readings from a smart factory or telemetry from a remote weather station. Without strong security measures, this vital information, or really any aspect of your operations, could be at risk. It’s a bit like leaving your front door wide open in a busy neighborhood, so to speak.
Many organizations, like yours perhaps, are finding that the sheer number of internet-connected gadgets is just exploding, and with that comes a whole new set of worries. You might have experienced, for example, issues where systems keep trying to reinstall updates and fail, or where a device is flagged as "at risk" because it's simply out of date and missing important security fixes. These kinds of problems, as a matter of fact, are not just annoying; they really highlight the constant battle against vulnerabilities that could impact your entire setup.
This article will walk you through the key strategies and services AWS offers to help you securely connect remote IoT devices to your VPC. We'll explore how to build connections that are trusted, private, and resilient, which is actually pretty important. It's about giving you peace of mind, knowing that your device data, whether it's sensitive or not, is protected from unauthorized access and potential breaches, so.
Table of Contents
- Why Secure IoT Connectivity is So Important
- Understanding the Basics: AWS VPC and IoT Core
- Key AWS Services for Secure IoT-VPC Connections
- Architectural Patterns for Secure Remote IoT to VPC
- Best Practices for Implementing Secure IoT-VPC Connections
- Addressing Common Security Worries
- Frequently Asked Questions (FAQs)
- Taking the Next Step in IoT Security
Why Secure IoT Connectivity is So Important
The truth is, connecting remote IoT devices, you know, brings a lot of amazing possibilities, but it also opens up new avenues for potential security issues. Imagine a scenario where, like your web browser telling you "This connection is untrusted" when trying to reach a website, your IoT device tries to send data but can't confirm the recipient is legitimate. That's a real problem, actually. This kind of connection uncertainty can lead to data interception, manipulation, or even unauthorized control of your devices, which is pretty serious.
Consider the real-world impact. If, for instance, a critical sensor's data is tampered with, it could lead to faulty decisions in a manufacturing plant, or, you know, incorrect environmental readings that affect public safety. There are also situations where, as some have noted, legitimate email gets blocked, or systems get stuck in automatic repair loops after updates. These are all examples of how a lack of trust or a break in the expected secure flow can really mess things up, so.
Keeping your IoT devices and the data they produce safe isn't just a technical detail; it's fundamental to the trust your customers and stakeholders place in you. A breach, or even a perceived vulnerability, can damage reputations and lead to significant financial losses. It’s about building a foundation where every connection, every data point, and every device interaction is, in a way, verified and protected, which is rather important.
- Jay Pharoah Wife
- Remoteiot Web Ssh Example Android
- Can A Woman Forget A Man Who Broke Her Virginity
- Bettijo Hirsch
- Aroomikim Onlyfans Leaks
Understanding the Basics: AWS VPC and IoT Core
Before we get into the specifics of secure connections, it's helpful to quickly go over the main players: AWS VPC and AWS IoT Core. These two services, more or less, form the backbone of your secure IoT architecture on AWS, so.
AWS Virtual Private Cloud (VPC)
Your AWS VPC is, in essence, your own private, isolated section of the AWS cloud. It's where you launch your AWS resources, like EC2 instances, databases, and serverless functions, into a virtual network that you define. You have full control over your virtual networking environment, including IP address ranges, subnets, route tables, and network gateways. This isolation, actually, is a crucial first step in any secure setup, giving you a dedicated space, as it were.
Within your VPC, you can create multiple subnets, perhaps separating your public-facing web servers from your private application databases. Security groups and Network Access Control Lists (NACLs) act like virtual firewalls, allowing you to control traffic at the instance and subnet levels, respectively. This granular control means you can, in a way, dictate precisely what can enter or leave your private network, which is very useful.
AWS IoT Core
AWS IoT Core is a managed cloud service that lets connected devices easily and securely interact with cloud applications and other devices. It can support billions of devices and trillions of messages, and it processes and routes those messages to AWS endpoints and to other devices reliably. Think of it as the central hub for your IoT devices, the place where they all check in, so to speak.
IoT Core supports common communication protocols like MQTT, HTTPS, and LoRaWAN, making it quite flexible for different types of devices. It also provides device authentication and authorization, ensuring that only trusted devices can connect and publish data. This is where, for example, your device's identity is verified, preventing issues similar to an "untrusted connection" message you might get on a browser, which is pretty important.
Key AWS Services for Secure IoT-VPC Connections
To really nail down secure connections, we often combine AWS IoT Core with other networking and security services. These services, you know, work together to create a layered defense, making it much harder for unauthorized access to happen, actually.
AWS IoT Core Device Gateway
The Device Gateway, more or less, handles all device connections. It supports secure communication using TLS and mutual authentication, where both the device and AWS IoT Core verify each other's identities. This is a bit like a digital handshake, ensuring both parties are who they say they are. Without this, you could face issues where connections are simply untrusted, as some users have reported with web browsers, which is something we definitely want to avoid.
AWS IoT Core Device Shadows and Registry
The Device Registry helps you manage your devices, giving each one a unique identity. Device Shadows, on the other hand, provide a persistent, virtual representation of each device, storing its last reported state and desired future state. This means your applications can interact with the device's shadow even if the device is offline. This helps maintain a consistent view of your device fleet, which is very helpful for management, so.
AWS IoT Greengrass
AWS IoT Greengrass extends AWS cloud capabilities to edge devices, allowing them to perform local compute, messaging, data caching, sync, and ML inference. This means your devices can react locally to events, reducing latency and allowing them to operate even with intermittent connectivity. It's a way to bring some of the cloud's intelligence closer to where the action is, so to speak, which can enhance both performance and security by processing sensitive data closer to its source, actually.
AWS PrivateLink
AWS PrivateLink is a network technology that lets you connect your VPC to AWS services privately, without exposing your traffic to the public internet. When you use PrivateLink, traffic between your VPC and the AWS service (like IoT Core) stays entirely within the AWS network. This is a huge win for security, as it significantly reduces the attack surface. It’s like creating a dedicated, secure tunnel for your data, which is pretty neat.
AWS Site-to-Site VPN
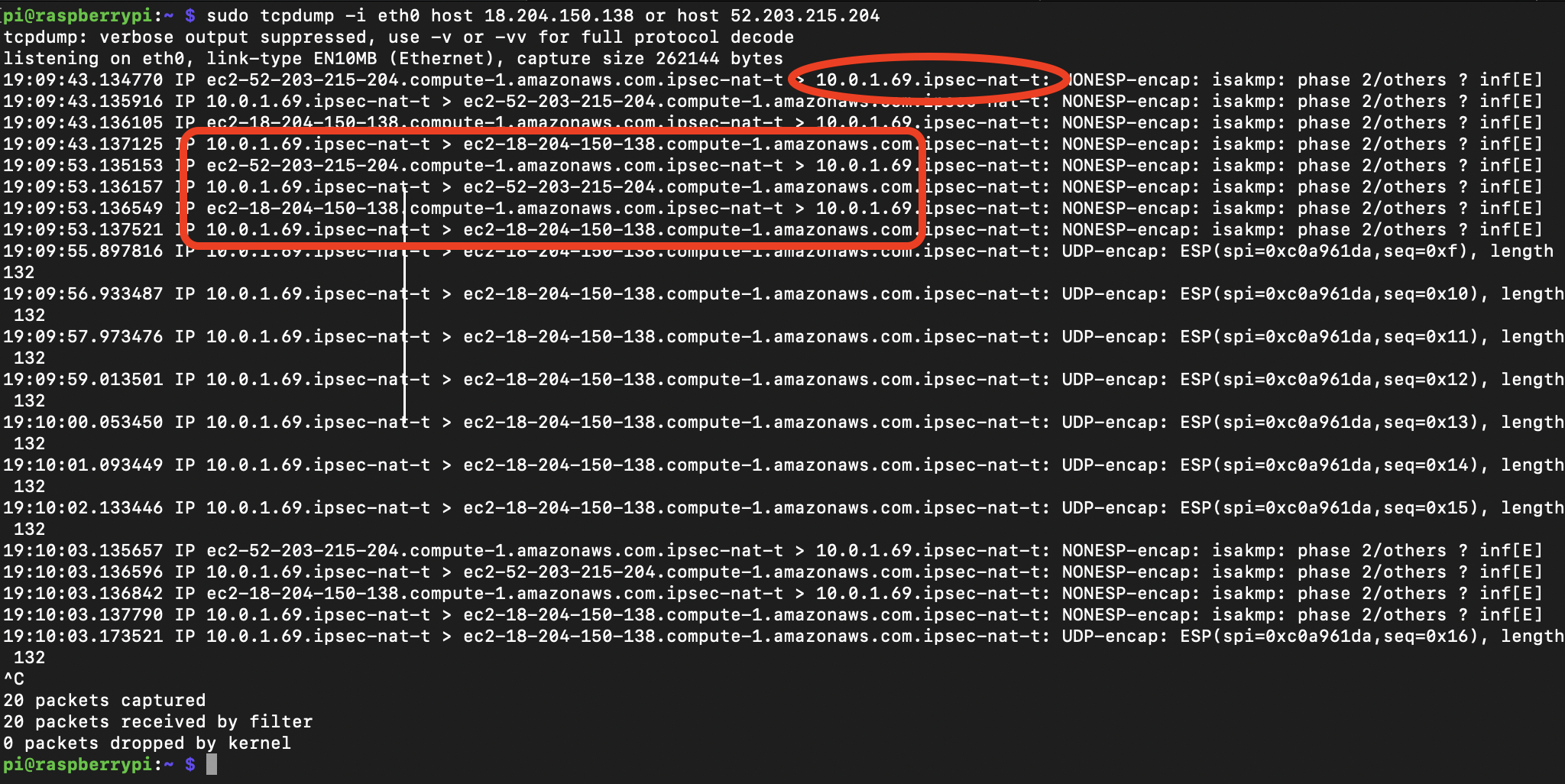
For connecting on-premises networks or remote locations with a few IoT gateways to your AWS VPC, a Site-to-Site VPN is a common choice. It establishes an encrypted tunnel over the public internet between your network and your VPC. While it uses the internet, the encryption makes the data secure. This can be a cost-effective solution for, say, smaller deployments or when you need to connect a specific remote site, you know.
AWS Direct Connect
AWS Direct Connect provides a dedicated, private network connection from your premises to AWS. Unlike a VPN, it doesn't use the public internet, offering consistent network performance and lower latency. This is often preferred for large-scale IoT deployments where high bandwidth, low latency, and maximum security are critical. It’s a bit like having your own private highway directly to the cloud, which is very efficient, actually.
AWS Transit Gateway
As your network grows and you have multiple VPCs, perhaps for different business units or environments, managing connections can get complicated. AWS Transit Gateway acts as a central hub that connects your VPCs, on-premises networks, and even other AWS accounts. This simplifies your network architecture and, you know, helps maintain consistent routing and security policies across your entire AWS footprint, which is pretty useful.
Architectural Patterns for Secure Remote IoT to VPC
There are several common ways to architect these secure connections, depending on your specific needs, device capabilities, and scale. Each pattern has its own strengths, so choosing the right one is important, actually.
Pattern 1: IoT Core with PrivateLink to VPC
This is a highly recommended pattern for devices that can connect directly to AWS IoT Core over the internet. The devices send data to IoT Core, and then IoT Core uses AWS PrivateLink to securely and privately forward that data to your applications running within your VPC. The traffic never touches the public internet between IoT Core and your VPC. This setup, you know, gives you excellent security and simplifies device connectivity, as the devices only need to know how to reach IoT Core.
Basically, devices connect to IoT Core using MQTT or HTTPS with TLS, authenticating with X.509 certificates or AWS IAM credentials. IoT Core then publishes messages to an endpoint within your VPC via a PrivateLink interface endpoint. Your applications in the VPC can then subscribe to these messages. This approach helps avoid those "untrusted connection" messages, as the entire path within AWS is, in a way, verified and private, so.
Pattern 2: IoT Greengrass with VPN or Direct Connect
For devices that need local processing, or when you have a local gateway that aggregates data from many devices before sending it to the cloud, AWS IoT Greengrass is a great fit. The Greengrass core device, which might be a local server or a powerful edge device, connects to your AWS VPC using either a Site-to-Site VPN or AWS Direct Connect. The individual IoT devices then connect to the Greengrass core locally.
This pattern, you know, provides a secure bridge between your local network and your VPC. It's particularly useful for environments where devices might have limited internet access or require very low latency for local operations. The Greengrass core can perform filtering, aggregation, and even machine learning inference locally before sending only the necessary data securely to your VPC. This reduces the amount of data sent over the network, which is very efficient, actually.
Pattern 3: Direct Device Connection via VPN or Direct Connect
In some specific cases, especially for larger, more capable IoT devices or industrial equipment that are part of an on-premises network, you might want them to connect directly to your AWS VPC without going through IoT Core. This would typically involve setting up a Site-to-Site VPN or AWS Direct Connect between your on-premises network and your AWS VPC.
The devices on your local network would then use this secure tunnel to communicate directly with applications or services running in your VPC. This pattern is less common for very small, resource-constrained IoT devices but can be quite effective for industrial control systems or large gateways that need to exchange substantial amounts of data directly with cloud resources. It's a bit like extending your data center into the cloud, which is pretty powerful.
Best Practices for Implementing Secure IoT-VPC Connections
Regardless of the architectural pattern you choose, some fundamental security practices are, you know, absolutely crucial. These aren't just good ideas; they're essential for avoiding the kinds of security headaches some users face, like untrusted connections or devices being out of date and at risk, so.
Strong Device Identity and Authentication
Every single IoT device should have a unique identity and use strong authentication methods. AWS IoT Core, for example, heavily relies on X.509 certificates for mutual authentication. This means both the device and IoT Core verify each other. Provisioning these certificates securely and rotating them regularly is very important. Think of it like having a strong, unique password for every device, not just one for the entire folder, which is actually a common mistake.
Implementing a robust certificate management system is key. You need to be able to revoke certificates quickly if a device is compromised or retired. This helps prevent unauthorized devices from connecting, which is a bit like keeping unauthorized individuals out of your private network, you know.
Data Encryption in Transit and At Rest
All data transmitted between your IoT devices and AWS, and within AWS itself, should be encrypted. TLS (Transport Layer Security) is the standard for data in transit, and AWS IoT Core enforces this. For data at rest, such as data stored in S3 buckets or databases within your VPC, use encryption keys managed by AWS Key Management Service (KMS). Encryption, as a matter of fact, is your primary defense against data interception, so.
This means that even if an attacker manages to intercept your data, they won't be able to read it without the decryption key. It's an extra layer of protection, similar to how you might want to password protect a file, not just the entire folder, as some users have tried to do, which is very sensible.
Network Segmentation and Least Privilege
Within your VPC, use network segmentation to isolate your IoT-related resources. Place different components (e.g., IoT data processing, analytics, device management) into separate subnets with strict security group and NACL rules. Apply the principle of least privilege to all IAM roles and policies. This means granting only the minimum permissions necessary for a device or application to perform its function. This reduces the blast radius if a component is compromised, which is pretty important.
For example, an IoT device should only have permission to publish to specific MQTT topics and not, say, access your entire database. This granular control, you know, helps prevent an issue in one area from spreading to others, which is very helpful for overall security.
Continuous Monitoring and Auditing
Actively monitor your IoT environment for suspicious activity. Use AWS CloudWatch for logging and metrics, AWS CloudTrail for API call auditing, and AWS IoT Device Defender for auditing device configurations and detecting anomalies. Set up alerts for unusual behavior, like a device trying to connect from an unexpected location or publishing to unauthorized topics. This is how you catch problems early, which is absolutely critical, actually.
Regularly reviewing logs and audit trails can help you identify potential security gaps or active threats. It's a bit like having a security guard constantly watching for anything out of the ordinary, ensuring that your systems are, you know, running more securely, so.
Secure Firmware and Software Updates
Keeping your devices updated is, as a matter of fact, extremely important. As some users have experienced with operating system updates, failing to apply security and quality updates can leave your device at risk. For IoT devices, this means having a secure over-the-air (OTA) update mechanism. Ensure that firmware updates are signed and verified before installation to prevent malicious code from being introduced.
AWS IoT Device Management, for instance, provides tools for managing and deploying updates to your fleet. This helps you avoid situations where devices are "out of date and missing important security and quality updates," which is a very common vulnerability, you know. Regular updates are a key part of maintaining the integrity of your entire IoT ecosystem, so.
Addressing Common Security Worries
Many of the security concerns people have, whether it's about a web browser connection being untrusted or an operating system update failing, really come down to trust and verification. When you're trying to securely connect remote IoT devices to your AWS VPC, you're essentially building a system where trust is paramount. You want to avoid those messages saying "This connection is untrusted" or "we can't confirm that your connection is secure" at all costs.
By implementing the services and best practices discussed, you create a verified pathway for your IoT data. You establish clear identities for devices, encrypt all communications, and limit what each device can do. This proactive approach helps prevent issues like legitimate data being blocked or unauthorized access, which is something many people worry about, you know, in various digital interactions, actually. It's about setting up your system so that, in a way, it inherently trusts what it should and rejects what it shouldn't.
Frequently Asked Questions (FAQs)
How do I prevent "untrusted connection" messages with my IoT devices?
To prevent untrusted connection messages, you need to ensure your IoT devices use proper authentication, typically X.509 certificates, and communicate over TLS with trusted endpoints like AWS IoT Core. This verifies the identity of both the device and the cloud service, which is pretty important. Using services like AWS PrivateLink also ensures that the traffic between IoT Core and your VPC stays within the trusted AWS network, so.
What if my IoT device is out of date and missing security updates?
If your IoT device is out of date, it's at risk, much like an outdated computer. You should implement a secure over-the-air (OTA) update mechanism, perhaps using AWS IoT Device Management. This allows you to remotely and securely push firmware and software updates to your devices, ensuring they always have the latest security patches and are, in a way, running more securely, actually.
Can I protect individual IoT data streams or device configurations, similar to password protecting a single file?
Yes, you can protect individual data streams and device configurations with fine-grained control. AWS IoT Core policies allow you to define exactly which MQTT topics a device can publish or subscribe to, and what actions it can perform on its device shadow. This is more effective than just protecting an entire folder, as it gives you very specific control over each data point and device interaction, which is very useful, you know.
Taking the Next Step in IoT Security
Building a truly secure IoT ecosystem on AWS means thinking about security from the ground up. It’s about more than just setting up connections; it’s about creating a framework where every interaction is, you know, verified and protected. By leveraging AWS IoT Core, VPC, PrivateLink, and other services, you can establish robust, private connections for your remote devices. You can learn more about AWS IoT security best practices on our site, and also explore more about AWS IoT Core directly.
Remember, the digital landscape is always changing, so staying informed and regularly reviewing your security posture is, as a matter of fact, extremely important. It’s a continuous process, but with the right tools and strategies, you can confidently connect your remote IoT devices, knowing your data and operations are well-protected. So, take these steps to secure your connections today.
- Jessica Lyman Saratoga Springs
- Best Remoteiot Firewall Examples
- Sophie Rain Onlyfans Naked
- Mckinley Richardson Leaked
- Barry Keoghan Drama


Detail Author:
- Name : Leora Berge
- Username : moises.dare
- Email : carole.vonrueden@yahoo.com
- Birthdate : 1983-06-10
- Address : 155 Madisen Curve Lake Elyssa, MI 40235
- Phone : +17272385369
- Company : Zulauf Group
- Job : Maintenance Supervisor
- Bio : Et non nobis impedit quam quae. At eveniet error rerum iure quia eaque atque. Vitae consequatur magnam illum ut rerum. Dolorem tempore et et dignissimos natus atque et.
Socials
facebook:
- url : https://facebook.com/jazmynlebsack
- username : jazmynlebsack
- bio : Sit quidem magni magni dolorum suscipit. Enim saepe occaecati nemo eum quam.
- followers : 4956
- following : 1719
instagram:
- url : https://instagram.com/jazmyn4759
- username : jazmyn4759
- bio : Consequatur non vero veniam. Assumenda vero magni et quaerat nemo est.
- followers : 3053
- following : 2338