Setting up your Raspberry Pi devices to talk with the cloud, especially from far away, really needs a solid, secure plan. You see, when you're dealing with things like sensors in remote places or smart gadgets spread across a building, just having them connect isn't enough. You need to know they are safe from unwanted access, and that their communications stay private. This kind of setup, actually, is a lot like how a really good encyclopedia works; it brings together lots of detailed information in one place, making complex topics understandable and accessible, much like we want to make secure remote access for your IoT projects clear and manageable.
The challenge, it seems, often lies in bridging the gap between small, powerful devices like a Raspberry Pi and the vast, robust infrastructure of a cloud service like Amazon Web Services (AWS). Many folks want to manage their Pis without being physically next to them, yet they worry about leaving security holes wide open. This is where a Virtual Private Cloud (VPC) on AWS, combined with secure shell (SSH) access, becomes a very practical answer. It’s about creating a safe, isolated space in the cloud where your devices can truly feel at home.
This guide will walk you through building a strong connection, showing you how to set up a `remoteiot vpc ssh raspberry pi aws example` that’s both functional and very secure. We will look at how to get your Raspberry Pi talking to AWS, making sure that only authorized people and systems can access it. So, you know, we're going to cover everything from setting up your AWS environment to configuring your tiny computer for this important task, giving you a clear path forward.
- Elizabeth Vargas Net Worth
- Spanish Word Search Printable Pdf
- Geoffrey Thorne Partner
- Sadee Horvat
- Billy Boyd Net Worth
Table of Contents
- Why Secure Remote IoT Access is a Big Deal
- The Main Pieces of Our Puzzle
- Getting Your AWS VPC Ready
- Preparing Your Raspberry Pi for the Cloud
- Making That Secure SSH Connection
- Bringing It All Together: Your Remote IoT System
- Smart Ways to Work and Fix Things
- Frequently Asked Questions
Why Secure Remote IoT Access is a Big Deal
Think about all the tiny computers out there, gathering information or doing tasks, often in places where you can't just walk up and plug in a keyboard. These devices, like your Raspberry Pi, are part of the Internet of Things (IoT), and they're becoming more and more common. As of early 2024, the number of connected IoT devices continues to grow significantly, pushing the need for better ways to manage them. For instance, being able to update software, check on sensor readings, or even reboot a device from your office, regardless of where the device is physically located, is really quite helpful. This kind of remote control saves a lot of time and effort, you know.
Without good security, though, letting these devices be accessible from afar can open up all sorts of problems. An unsecured connection is like leaving your front door wide open; anyone could just stroll in. This could mean data theft, device hijacking, or even using your tiny devices to launch attacks on other systems. So, making sure your `remoteiot vpc ssh raspberry pi aws example` is built with security at its very core isn't just a good idea; it's absolutely necessary. It's about protecting your data, your devices, and your peace of mind, basically.
Using an AWS Virtual Private Cloud (VPC) gives you a private section of the AWS cloud where you can put your resources, including your Raspberry Pi, if you set things up right. This private space acts as a kind of digital fortress, letting you control who and what can get in or out. Adding SSH for access means your connection is encrypted, making it very hard for anyone to snoop on your commands or data. This combination offers a strong way to manage your remote IoT devices, allowing for flexibility without giving up on safety, so it's a pretty neat solution.
The Main Pieces of Our Puzzle
To build this secure remote access system, we're going to use a few key components. Each piece plays an important part, and understanding what each one does helps us put them together effectively. It's kind of like assembling a piece of custom furniture, where each panel and fitting has a specific role; you choose the right thickness and finish for each part, ensuring the whole thing is strong and looks good. Here, we're picking the right digital "panels" for our secure connection.
Raspberry Pi: Your Edge Worker
The Raspberry Pi is a small, inexpensive computer that’s very popular for IoT projects. It's powerful enough to run various tasks, collect data, and even do some processing right where the action is – what we call the "edge." For our setup, this little device will be the target, the thing we want to reach and control remotely. It's really quite versatile, and you can do a lot with it, so it's a great choice for this kind of work.
AWS VPC: Your Private Cloud Home
An AWS VPC is like having your own isolated network within the larger AWS cloud. You get to define its IP address range, create subnets, and set up network gateways. This isolation is crucial for security, as it means your devices aren't just floating around on the public internet. Instead, they're tucked away in a private network that you control, which is a pretty big deal for keeping things safe.
SSH: Your Secure Doorway
SSH, or Secure Shell, is a network protocol that lets you access and control a computer over an unsecured network in a very secure way. It provides strong encryption, so when you're typing commands or transferring files, your information is protected. For our `remoteiot vpc ssh raspberry pi aws example`, SSH will be our encrypted tunnel, making sure our commands to the Raspberry Pi stay private and safe from prying eyes, which is, you know, very important.
Getting Your AWS VPC Ready
Setting up your AWS environment is the first big step. This involves creating a new VPC and configuring its network elements to support our Raspberry Pi. This is where we lay the groundwork for our secure connection, so it's worth taking your time to get it right. It's kind of like preparing the foundation for a building; a strong foundation means a strong structure, after all.
Building Your VPC
First, you'll want to go into the AWS Management Console and find the VPC service. You can choose to create a new VPC, giving it a name and a CIDR block (a range of IP addresses). For example, you might use `10.0.0.0/16`. This block defines the total address space for your private network. It's your private address book, in a way, for all the devices that will live inside this VPC, so that's pretty useful.
Setting Up Subnets and Gateways
Inside your VPC, you'll need at least two subnets: one public and one private. The public subnet will host a "bastion host" (a jump server), which we'll use to connect to our private devices. The private subnet is where your Raspberry Pi will eventually reside. You'll also need an Internet Gateway (IGW) attached to your VPC, and a NAT Gateway (Network Address Translation) in your public subnet. The NAT Gateway allows devices in your private subnet to access the internet for updates or external services without being directly exposed, which is, you know, a very clever trick for security.
Security Groups and Network ACLs
Security Groups act like virtual firewalls for your instances, controlling inbound and outbound traffic. You'll create specific security groups: one for your bastion host (allowing SSH from your IP address) and another for your Raspberry Pi (allowing SSH only from your bastion host's security group). Network Access Control Lists (NACLs) add another layer of security at the subnet level. These are stateless, meaning they don't remember previous connections, and they let you set very specific rules for traffic flow, which is, honestly, a lot of control.
Preparing Your Raspberry Pi for the Cloud
With your AWS network ready, it's time to get your Raspberry Pi prepared. This involves some initial setup and configuring it for secure SSH access. This part is about making sure your Pi is a good, well-behaved resident of your new private cloud space. It's not too hard, actually, but it does need a few steps.
Initial Pi Setup
First, make sure your Raspberry Pi is running the latest operating system, like Raspberry Pi OS. You can download the image and flash it onto an SD card. Once it boots up, you'll want to enable SSH. This is usually done through the `raspi-config` tool or by creating an empty file named `ssh` in the boot partition of the SD card. Make sure it's connected to a network initially so it can get updates. So, you know, just like any new computer, it needs a little bit of care to get going.
sudo apt update sudo apt upgrade -y sudo raspi-config # Enable SSH here if not already done Generating SSH Keys
Instead of passwords, we'll use SSH key pairs for better security. On your local machine (your computer), you'll generate an SSH key pair. The public key will be placed on your Raspberry Pi and on your AWS bastion host, while the private key stays securely on your local machine. This way, only someone with your private key can connect. You can generate these keys using `ssh-keygen`, which is a pretty standard tool, so that's good.
ssh-keygen -t rsa -b 4096 -C "your_email@example.com" Copy the public key (`~/.ssh/id_rsa.pub`) to your Raspberry Pi's `~/.ssh/authorized_keys` file. You can do this initially by direct connection or by temporarily exposing it if absolutely necessary, but quickly moving it into the private subnet. This is a very important step for security, so you really want to get it right.
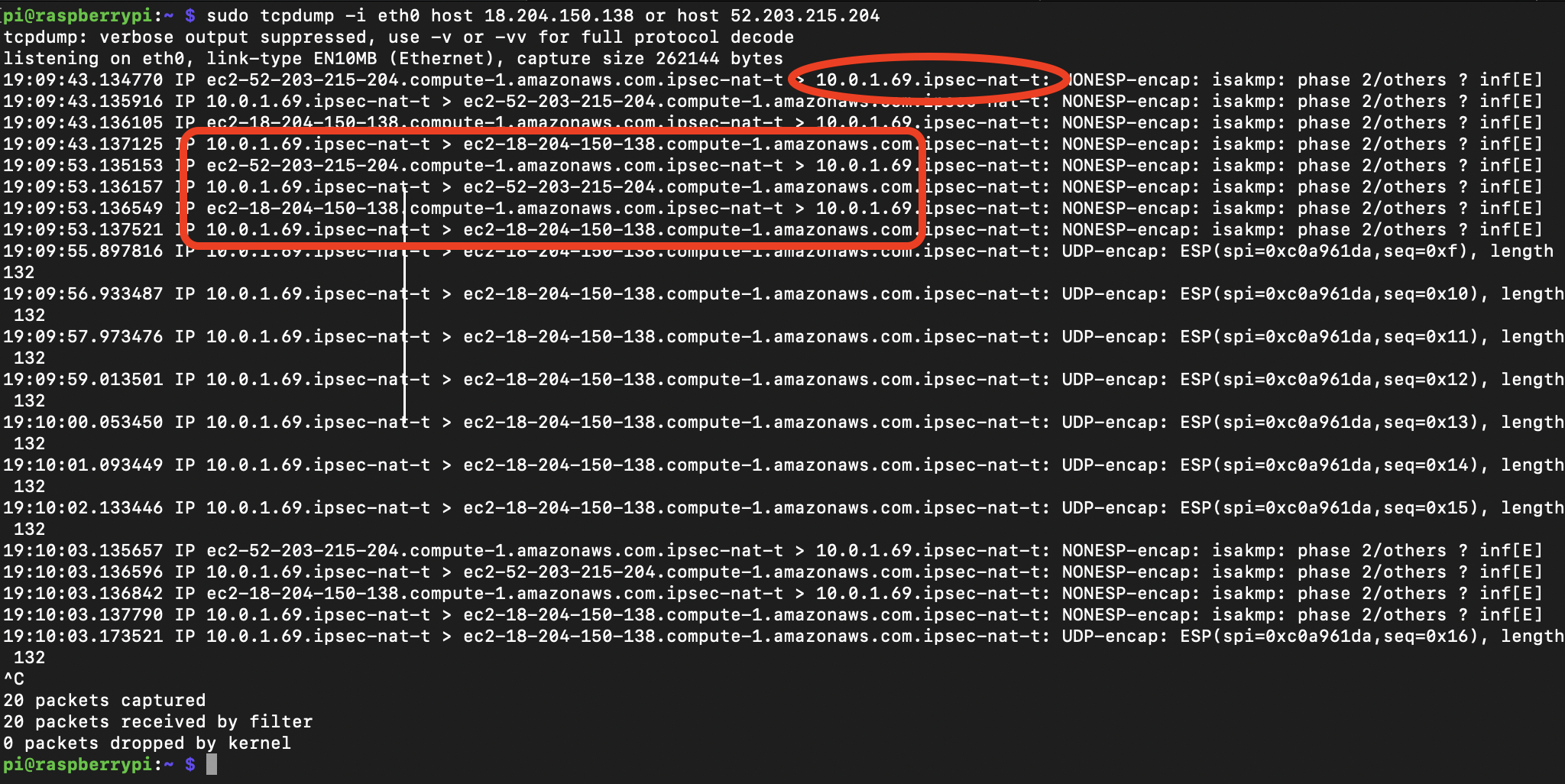
Making That Secure SSH Connection
Now, we're ready to put the pieces together and establish the secure connection. Since your Raspberry Pi will be in a private subnet, you can't directly SSH into it from the internet. This is where our bastion host comes in. It acts as a secure intermediary, a kind of controlled checkpoint, which is, you know, pretty smart.
Creating an EC2 Bastion Host
Launch a small EC2 instance (like a t2.micro) in your public subnet. This will be your bastion host. When you launch it, make sure to associate it with the public security group you created earlier, allowing SSH access from your home IP address. Also, ensure you use the same SSH key pair that you generated earlier for this EC2 instance. This bastion host will be the only public-facing machine in your setup that can talk to your private Raspberry Pi, so it's a very key part of the whole system.
Once the EC2 instance is running, you can SSH into it from your local machine using your private key:
ssh -i /path/to/your/private_key.pem ec2-user@YOUR_BASTION_PUBLIC_IP Connecting Through the Bastion
With your bastion host up and running, and your Raspberry Pi in the private subnet (configured with the public part of your SSH key), you can now SSH into your Pi. You'll do this by "hopping" through the bastion host. This is often done using SSH Agent Forwarding or by configuring your `~/.ssh/config` file. For instance, you could add something like this to your config file on your local machine:
Host bastion HostName YOUR_BASTION_PUBLIC_IP User ec2-user IdentityFile /path/to/your/private_key.pem Host raspberrypi HostName YOUR_RASPBERRY_PI_PRIVATE_IP User pi ProxyJump bastion IdentityFile /path/to/your/private_key.pem Then, you can simply type `ssh raspberrypi` from your local terminal, and it will automatically use the bastion host to reach your Pi. This setup, you know, makes it very convenient and secure, which is just what we want for a `remoteiot vpc ssh raspberry pi aws example`.
Bringing It All Together: Your Remote IoT System
So, you have your AWS VPC acting as a secure, private network. Your Raspberry Pi lives within a private subnet inside this VPC, shielded from the direct internet. A bastion host in a public subnet serves as your controlled entry point. And SSH, with key-based authentication, provides the encrypted tunnel for all your communications. This entire structure gives you a robust and secure way to manage your remote IoT devices, which is, honestly, a pretty powerful arrangement.
This approach means that even if someone were to try and scan for open ports on the internet, they wouldn't find your Raspberry Pi directly. They would only see the bastion host, which itself is locked down to only allow SSH from your specific IP address. It's a multi-layered defense, a bit like having several locked doors before you get to the treasure, so it's very effective. This makes your `remoteiot vpc ssh raspberry pi aws example` much safer for any kind of data or operations you're running.
You can expand on this foundation by integrating with AWS IoT Core for device management, telemetry, and more advanced IoT functionalities. The secure network you've built here is a perfect base for those services. This setup offers a strong starting point for any serious remote IoT project, giving you confidence in your system's integrity, which is, you know, a very good feeling to have.
Smart Ways to Work and Fix Things
When you're dealing with remote systems, it's always good to have some smart practices in mind. Always keep your software updated, both on your Raspberry Pi and on your bastion host. Regular updates often include security patches that fix newly discovered vulnerabilities. Also, use strong, unique SSH keys, and never share your private keys with anyone. It's kind of like keeping your house keys safe; you wouldn't just hand them out, would you? So, you know, be careful with them.
Monitor your AWS environment for unusual activity. AWS CloudWatch and CloudTrail can help you keep an eye on what's happening in your VPC and with your EC2 instances. Set up alerts for things like unauthorized SSH attempts or changes to your security groups. This proactive monitoring helps you catch problems early, which is, honestly, very helpful. It ensures your `remoteiot vpc ssh raspberry pi aws example` stays secure over time.
For troubleshooting, start by checking network connectivity. Can your bastion host reach the internet? Can it ping your Raspberry Pi's private IP address? Are your security group rules correct? Sometimes, a simple typo in an IP address or a forgotten rule can cause a lot of headaches. Just remember to check each step methodically, and you'll usually find the problem, so that's a good approach to take. Learn more about network troubleshooting on our site, and for deeper insights into AWS services, you might want to visit the official AWS VPC page.
Frequently Asked Questions
Here are some common questions people often ask about this kind of setup:
How do I SSH into a Raspberry Pi from AWS?
You generally SSH into a Raspberry Pi from AWS by using a bastion host (a jump server) that lives in a public subnet of your AWS VPC. Your local machine connects to the bastion host first, and then from the bastion, you connect to your Raspberry Pi, which is typically in a private subnet. This method uses SSH key-based authentication for both connections, making it very secure. So, it's a two-step process, basically.
What is the best way to secure IoT devices in AWS?
The best way to secure IoT devices in AWS often involves a multi-layered approach. This includes placing devices in private subnets within a VPC, using security groups and network ACLs to control traffic, implementing strong authentication like SSH keys or X.509 certificates, and encrypting all communications. Integrating with AWS IoT Core for device identity and policy management also adds significant security. It's about building a strong defense, you know, from every angle.
Can I connect my Raspberry Pi to AWS VPC?
Yes, you can absolutely connect your Raspberry Pi to an AWS VPC. This is done by configuring your Raspberry Pi to be part of the private subnet within your VPC. You'll need to ensure it has network access to the VPC (often through a VPN or a direct connect if it's physically remote, or simply by being on the same network as a VPC endpoint for local setups) and that its security group allows necessary inbound traffic, typically from a bastion host for SSH access. It’s a very common and effective way to manage these devices, so it's definitely doable.


Detail Author:
- Name : Pablo Huels
- Username : dasia.jones
- Email : fhilpert@kohler.biz
- Birthdate : 1977-07-09
- Address : 16402 Lera Prairie Michellefurt, MA 41591-7088
- Phone : 586.906.3340
- Company : Gutkowski-Murray
- Job : Municipal Fire Fighting Supervisor
- Bio : Adipisci quis fugiat in nihil. Deleniti voluptatem sed quibusdam nulla facilis. Tenetur dolor assumenda autem consectetur.
Socials
instagram:
- url : https://instagram.com/addie_xx
- username : addie_xx
- bio : Cupiditate voluptatum accusamus laboriosam. Sit occaecati eveniet repudiandae nemo.
- followers : 2683
- following : 1375
tiktok:
- url : https://tiktok.com/@addierodriguez
- username : addierodriguez
- bio : Autem iure dolorem animi provident odit aut in facere.
- followers : 6782
- following : 866