Connecting your Internet of Things (IoT) devices remotely, especially for peer-to-peer (P2P) downloads on a Windows 10 system, really brings up some big questions about safety. You know, it's a bit like trying to get a package delivered to a friend's house across town; you want to be absolutely sure it gets there, and that nobody else can just open it up along the way. Many folks are finding their devices, you know, at risk because of outdated software or missing key security updates, and that’s a pretty common worry. We often see messages popping up, like, "This connection is untrusted," which is certainly a sign that something isn't quite right with how things are linking up.
It's actually pretty common to run into problems where a connection just isn't confirmed as secure, whether you're trying to access a website or even your email. This kind of issue, where you're asked to connect securely but the system can't quite confirm it, can be really frustrating. It makes you wonder, you know, how you can really trust what's happening. Just like dealing with an update that keeps trying to reinstall and fails, even though it seems like it was already put in place, the core issue is often about ensuring everything is working as it should, without unexpected hiccups or security gaps.
This guide is here to help you get your remote IoT P2P downloads on Windows 10 working in a way that feels truly safe. We'll look at how to set things up so your connections are trusted and your data stays private, which is, you know, super important these days. We'll cover ways to protect your information and make sure your devices are talking to each other without any unwanted eavesdroppers, because, as a matter of fact, nobody wants their sensitive information out in the open.
Table of Contents
- Understanding Remote IoT P2P and Its Importance
- The Real Security Challenges for IoT on Windows 10
- Setting Up a Secure P2P Connection on Windows 10
- Key Security Measures for IoT P2P Downloads
- Choosing the Right Tools and Protocols
- Troubleshooting Common Security Glitches
- Best Practices for Ongoing Security
- Frequently Asked Questions
- Final Thoughts on Securing Your IoT Connections
Understanding Remote IoT P2P and Its Importance
Remote IoT P2P, you know, basically means that your smart devices can talk directly to each other, or to your Windows 10 computer, without always needing a central server. This is pretty useful for things like, say, streaming video from a security camera to your laptop or sending sensor data straight to an application. It can make things quicker and, in some ways, more efficient, especially when you're dealing with lots of devices. This direct communication, however, also means you're pretty much taking on the responsibility for securing each connection yourself, which is a bit different from relying on a big company's secure servers.
The importance of this kind of connection really comes down to convenience and sometimes even necessity for certain applications. For example, if you're trying to download a large file from a remote IoT device, a P2P connection can be much faster than going through a cloud service. It's also, in a way, about maintaining control over your own data flow. But, as we've seen with issues like "This connection is untrusted," the convenience can quickly turn into a headache if the security isn't handled properly, so that's something to think about.
The Real Security Challenges for IoT on Windows 10
When you're dealing with IoT devices and P2P connections on Windows 10, there are, you know, quite a few things that can go wrong from a security standpoint. It's not just about getting the connection to work; it's about making sure that connection is, in fact, safe from prying eyes or unwanted access. Many people run into problems where their devices are, you know, flagged as being at risk because they're missing important security and quality updates, which is a pretty serious concern for anyone wanting to keep their setup protected.
Untrusted Connections and Update Woes
One of the most common issues people face is that dreaded "This connection is untrusted" message. Whether it's Firefox or another browser, when your system can't confirm a secure connection to a website or service, that's a big red flag. It's, you know, essentially the system telling you, "Hey, I can't vouch for this link." This can happen if certificates are expired, or if there's something fishy going on with the network itself. Furthermore, we've all experienced those frustrating moments where an update keeps trying to reinstall and fails, even though it looks like it was already installed. This kind of update problem leaves your system vulnerable, because, as a matter of fact, those updates often contain vital security fixes that keep bad actors out.
These update issues are not just annoying; they actually leave your Windows 10 device, and by extension your IoT connections, exposed. If your device is at risk because it's out of date, then any P2P connection you establish could, you know, potentially be compromised. It's pretty much a foundational step to ensure your operating system and all its components are fully patched. Without those crucial updates, you're essentially leaving a door wide open, which is, you know, something nobody wants for their smart devices or their personal computer.
The Need for Strong Access Controls
Another big challenge is making sure only the right people and systems can access your IoT devices. It's a bit like trying to lock down an office building, you know, so only authorized personnel can get in. We hear about people wanting to create transport rules to lock down their organization's O365 tenant to only allow mail from their third-party email threat protection platform's IPs. This same principle applies to your IoT setup. You need strict controls to prevent unauthorized downloads or access to your devices. This means, actually, thinking about who or what can initiate a P2P connection and what permissions they have.
Sometimes, people even struggle with basic security, like trying to password protect a file in SharePoint and finding the option isn't there anymore. This shows how important it is to have clear, functional ways to secure individual components, not just the whole folder or system. For remote IoT P2P, this translates to making sure each device, and each connection, has its own robust access controls, because, you know, a single weak link can compromise the entire chain.
Setting Up a Secure P2P Connection on Windows 10
Getting your remote IoT P2P connections to work securely on Windows 10 involves a few important steps. It's not just about plugging things in; you actually have to, you know, configure your system and devices with security in mind from the very start. Think of it like building a house; you want a strong foundation before you even think about the roof. This approach helps prevent a lot of the common issues, like untrusted connections, that people often run into.
Foundational Steps for Device Preparation
First off, make sure your Windows 10 operating system is completely up to date. We've talked about how frustrating it is when an update keeps trying to reinstall and fails, but getting those updates to stick is, you know, absolutely critical. They fix known vulnerabilities that could be exploited. Similarly, ensure your IoT devices themselves have the latest firmware. Many device manufacturers release updates that patch security holes, so checking for these regularly is a must. It's pretty much the first line of defense, actually.
Next, change all default passwords on your IoT devices. This is, like, a super basic but often overlooked step. Many devices come with generic passwords that are, you know, widely known and easily guessed. Using strong, unique passwords for each device and for your Windows 10 user accounts is, arguably, one of the simplest yet most effective ways to boost your security. You know, a strong password is a bit like a sturdy lock on your front door.
Configuring Windows Firewall for IoT Traffic
Your Windows Firewall is a pretty powerful tool for controlling what goes in and out of your computer. For secure IoT P2P connections, you'll want to, you know, set up specific rules that only allow the necessary traffic. This means identifying the ports your IoT devices use for P2P communication and creating inbound and outbound rules for them. It's kind of like telling a bouncer exactly who is allowed into your club.
You should, in fact, be very specific with these rules. Instead of opening up a wide range of ports, just open the ones that are absolutely needed for your IoT devices to communicate. Also, consider restricting access to specific IP addresses if your IoT devices have static IPs, or if you're connecting from a known remote location. This approach helps prevent unauthorized devices or users from trying to, you know, connect to your system, which is pretty much what we want to avoid when we see those "connection is untrusted" warnings.
Key Security Measures for IoT P2P Downloads
Beyond the basic setup, there are some really important security measures you should always have in place for your IoT P2P downloads. These aren't just good ideas; they're, you know, pretty much essential for keeping your data safe and your connections private. It's about building layers of protection, so if one layer fails, there are others to back it up, which is, you know, a smart way to approach security.
Encryption and Data Protection
Encryption is, arguably, one of the most powerful tools you have for securing your P2P IoT downloads. When data is encrypted, it's scrambled in such a way that only someone with the correct key can, you know, unscramble and read it. This is super important because if an untrusted connection somehow intercepts your data, they won't be able to make sense of it. Look for IoT devices and P2P software that support strong encryption protocols like TLS/SSL. This ensures that the information flowing between your devices and Windows 10 is, in fact, protected from eavesdropping, which is a pretty big deal.
For any files you're downloading or transferring, especially sensitive ones, consider encrypting them before they even leave the source device. While some P2P software might offer encryption for the transfer itself, adding an extra layer of file-level encryption gives you, you know, even more peace of mind. This is a bit like putting your valuables in a locked box inside another locked box. It just adds that much more protection, you know, against any potential breaches.
Strong Authentication and Access Management
Just like you wouldn't want anyone to just walk into your house, you don't want unauthorized access to your IoT devices or your Windows 10 system. Implementing strong authentication methods is, you know, absolutely key. This goes beyond just strong passwords; think about using two-factor authentication (2FA) wherever possible. This means that even if someone guesses your password, they still need a second piece of information, like a code from your phone, to get in. It's a pretty effective way to keep things locked down.
Also, regularly review who has access to your IoT devices and what permissions they have. If you have, say, an old account that's no longer needed, disable it. This is similar to how organizations create transport rules to lock down their O365 tenant to only allow mail from specific, trusted IPs; you want to make sure only known and authorized entities can connect. Restricting access to the bare minimum needed for functionality is, you know, a really good practice for overall security.
Keeping Software Up-to-Date
We've touched on this, but it really can't be stressed enough: keeping all your software updated is, you know, non-negotiable. That feeling of your device being at risk because it's out of date and missing important security updates is, in fact, a very real threat. This includes your Windows 10 operating system, any P2P client software you're using, and the firmware on all your IoT devices. Developers constantly release patches to fix newly discovered vulnerabilities, and if you're not applying them, you're leaving yourself exposed.
Set up automatic updates whenever you can, or at least schedule regular checks. While dealing with an update that keeps trying to reinstall and fails can be frustrating, finding a way to resolve those issues is, you know, paramount. Sometimes, it might mean doing a manual install or troubleshooting a specific problem, but the effort is always worth it for the added security. It’s pretty much the ongoing maintenance that keeps your digital doors and windows firmly shut.
Choosing the Right Tools and Protocols
Selecting the correct tools and communication methods is, you know, pretty important for building a secure remote IoT P2P setup on Windows 10. Not all software or protocols are created equal when it comes to security, so making informed choices can really make a difference. It's a bit like picking the right tools for a job; you want the ones that are, in fact, designed for safety and reliability.
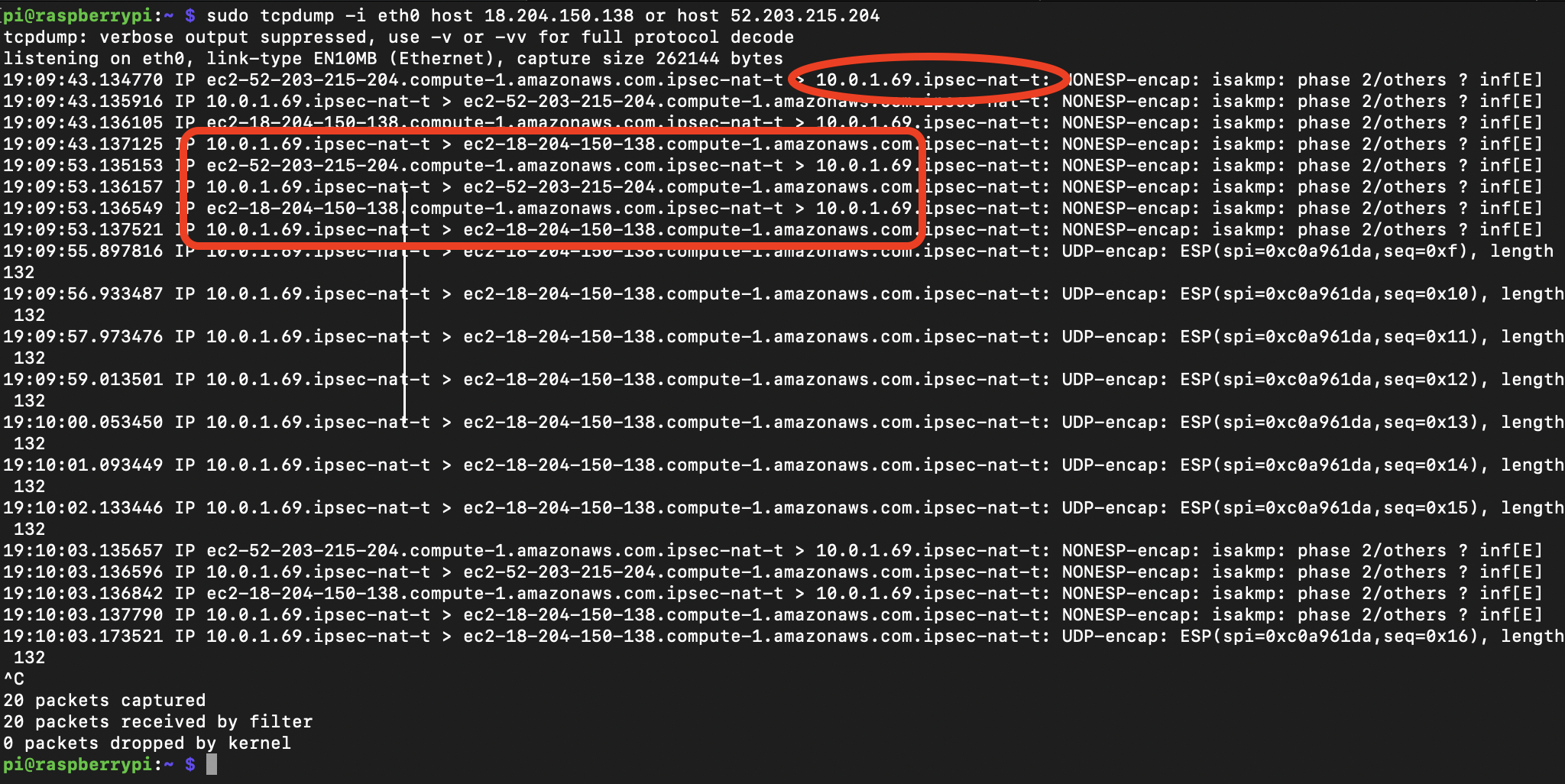
Virtual Private Networks (VPNs)
Using a Virtual Private Network (VPN) can, you know, add a really significant layer of security to your remote IoT P2P connections. A VPN creates an encrypted tunnel for all your internet traffic, essentially hiding your online activity from your internet service provider and potential eavesdroppers. If you're connecting to your IoT devices from outside your home network, a VPN ensures that your connection is, you know, private and secure, even if the underlying network is untrusted.
You can set up a VPN client on your Windows 10 machine, or even configure a VPN server on your home router if it supports it, which is pretty handy. This means all traffic going to and from your IoT devices, through your home network, is protected. It helps address those "connection is untrusted" warnings by making sure the data itself is, in fact, wrapped in a secure layer before it even hits the open internet, which is a good thing to consider.
Secure File Transfer Protocols
When it comes to downloading files from your IoT devices, make sure you're using secure file transfer protocols. While P2P can be direct, the actual transfer of data should be, you know, protected. Protocols like SFTP (SSH File Transfer Protocol) or FTPS (FTP Secure) offer encryption for file transfers, unlike older, unencrypted methods like standard FTP. These secure protocols help ensure that the files you're downloading from your remote IoT devices aren't intercepted or tampered with during transit. It's pretty much a standard for moving sensitive information.
Some P2P solutions might have their own built-in secure transfer methods, so it's always a good idea to check their documentation. If you're building your own IoT solution, incorporating these secure protocols from the start is, you know, absolutely vital. This helps prevent issues where there's a problem connecting securely to a website or device, because the protocol itself is designed with security in mind, which is, in fact, a very important detail.
Troubleshooting Common Security Glitches
Even with the best planning, you might still run into some security glitches. It's, you know, pretty common to hit snags, especially when you're dealing with complex setups involving multiple devices and networks. The key is knowing how to, you know, figure out what's going wrong and how to fix it, so you can get back on track with your secure connections.
If you're getting "This connection is untrusted" messages, first check the date and time on your Windows 10 computer and your IoT devices. Incorrect system clocks can, actually, cause certificate validation errors. Also, try clearing your browser's cache and cookies if the issue is web-related. Sometimes, simply restarting your router, modem, and devices can resolve temporary network glitches. We've all been there, you know, where a simple restart works wonders.
When an update keeps trying to reinstall and fails, or if your device is at risk because it's out of date, you might need to take a more direct approach. This could involve manually downloading the update from Microsoft's catalog, running the Windows Update troubleshooter, or even, you know, temporarily disabling your antivirus to see if it's interfering. Sometimes, an automatic repair loop can happen after installing updates, which is pretty much a sign that something went wrong during the update process. In those cases, system restore points or a clean install might be necessary, though that's a bit more drastic.
If you're having a problem connecting securely to a website or your IoT device, check your firewall settings. Make sure you haven't accidentally blocked the necessary ports or applications. Also, test your network connection generally to rule out broader internet issues. Sometimes, the problem might be on the IoT device itself, so checking its logs or status can provide, you know, valuable clues. It's all about methodically ruling out possibilities, which is, in fact, a pretty good way to troubleshoot.
Best Practices for Ongoing Security
Maintaining a secure remote IoT P2P setup on Windows 10 isn't a one-time task; it's, you know, an ongoing commitment. The digital world is always changing, so your security practices need to adapt as well. Think of it like maintaining your car; you don't just fill it with gas once and expect it to run forever without any issues. Regular checks and adjustments are, actually, pretty important.
Regularly audit your network for any unauthorized devices or suspicious activity. Keep an eye on your firewall logs and your IoT device activity. Implement a strong backup strategy for any critical data on your IoT devices or your Windows 10 system. If, you know, something does go wrong, having a recent backup can be a lifesaver. This is a bit like having insurance; you hope you never need it, but you're glad it's there.
Educate yourself and anyone else using your IoT devices about basic security practices. Strong passwords, recognizing phishing attempts, and being cautious about what you download are, you know, pretty fundamental. Remember the issues with untrusted connections? Understanding why those happen can help you avoid them. Learn more about IoT security fundamentals on our site, and also check out this page for advanced P2P encryption techniques to deepen your knowledge. Staying informed is, in fact, one of the best ways to stay secure.
Consider segmenting your network. This means creating a separate network for your IoT devices, distinct from your main home network. If one IoT device is compromised, it won't, you know, immediately put your entire home network at risk. This is a bit like having different rooms in your house; if one catches fire, it doesn't necessarily burn down the whole place. It's a pretty advanced but effective security measure for those with many devices.
Frequently Asked Questions
How can I make sure my IoT P2P connection is safe on Windows 10?
To keep your IoT P2P connections safe on Windows 10, you should, you know, use strong, unique passwords for all devices, enable encryption for data transfers, and keep your Windows 10 system and all IoT device firmware completely up to date. Also, configuring your Windows Firewall to only allow necessary traffic is, in fact, a really good step. Consider using a VPN for remote access to add an extra layer of security, which is pretty much a standard recommendation.
What are the risks of using P2P for IoT on Windows 10?
The risks of using P2P for IoT on Windows 10 include, you know, unauthorized access to your devices, data breaches if connections aren't encrypted, and the potential for malware if you're downloading files from untrusted sources. If your device is at risk because it's out of date, those vulnerabilities can be exploited. Untrusted connections can also expose your data, which is, you know, a pretty big concern for anyone. So, you know, taking precautions is super important.
Are there any tools to help secure remote IoT connections?
Yes, there are, you know, several tools that can help secure your remote IoT connections. VPNs (Virtual Private Networks) are excellent for encrypting your traffic. Firewall software, like the built-in Windows Firewall, helps control network access. For secure file transfers, look for P2P software that supports protocols like SFTP or FTPS. Additionally, password managers can help you create and store strong, unique passwords for all your devices, which is, in fact, a very useful tool for overall security. You can find more information about these tools on sites like PrivacyTools.io, which is a good external resource.
Final Thoughts on Securing Your IoT Connections
Getting your remote IoT P2P downloads working securely on Windows 10 really comes down to a few key things: staying updated, using strong authentication, and encrypting your data. It's about being proactive, you know, rather than waiting for a problem like an untrusted connection to pop up. By following these steps, you can feel much more confident that your devices are communicating safely and your information is protected. It's pretty much about taking control of your digital safety, and that's a good feeling to have.
- David Goggins And Jennifer Kish
- Unlocktme Bypass
- Where Is Ovidio Guzman Now
- Cancer Vs Scorpio Who Is Stronger
- Sonny Landham Net Worth

Detail Author:
- Name : Prof. Lafayette Leannon
- Username : tyrique64
- Email : gloria.mertz@hotmail.com
- Birthdate : 1987-03-17
- Address : 785 Cristian Extension New Craigview, AK 76645
- Phone : (629) 606-0116
- Company : Lindgren Inc
- Job : Public Relations Specialist
- Bio : Laudantium delectus deserunt dolorem excepturi nihil ut. Culpa velit qui aut ducimus. Dolorem voluptates quis et error et quia ut. Quo delectus quos sit fugiat.
Socials
linkedin:
- url : https://linkedin.com/in/cwyman
- username : cwyman
- bio : Aut magnam quisquam amet porro.
- followers : 3508
- following : 2381
tiktok:
- url : https://tiktok.com/@crystal.wyman
- username : crystal.wyman
- bio : Veniam consequatur maiores quaerat natus sunt quos. Eaque sed voluptas et ab.
- followers : 2468
- following : 24
facebook:
- url : https://facebook.com/crystal_wyman
- username : crystal_wyman
- bio : Qui cum est ex minima repudiandae recusandae.
- followers : 3471
- following : 805