Managing your IoT gadgets from afar can feel like a real puzzle, especially when you want to make sure everything stays secure. You might be thinking about how to check on a sensor in a far-off field or tweak settings on a smart device in another building, and you really need a dependable way to do it. This is where getting your IoT devices connected using SSH (Secure Shell) over the internet, all with the help of AWS (Amazon Web Services), becomes a true game-changer. It offers a very secure path to reach those devices, no matter where they are physically located, which is pretty amazing.
Leveraging AWS for remote IoT management through SSH, in a way, provides remarkable adaptability, room to grow, and strong safety measures. It's like having a direct, private line to each of your devices, making sure only authorized folks can get in. This setup helps you keep an eye on things, send updates, and fix problems without ever needing to be right there, which, you know, saves a lot of time and effort.
Connecting your SSH IoT devices over the internet using AWS is, actually, a rather powerful approach to look after distant equipment safely and effectively. This article will go into how you can use SSH to get to your IoT devices from just about anywhere, making good use of AWS as your cloud platform. We'll cover everything from getting things set up to keeping your connections safe and sound, so you feel confident doing it yourself.
- Bhad Bhabie Of Leaked
- Jameliz Benitez Onlyfans
- Kaia Kitsune Onlyfans Videos
- Logan Pepper Accident
- Sophie Rain Nude
Table of Contents
- Why Remote SSH for IoT on AWS?
- Getting Started: Prerequisites and Setup Choices
- The Core Components: AWS Services at Play
- Step-by-Step: Connecting Your IoT Device via SSH Over AWS
- Best Practices for Secure IoT SSH Access
- Frequently Asked Questions
Why Remote SSH for IoT on AWS?
When you're dealing with a bunch of IoT devices spread out over a wide area, getting to them for maintenance or troubleshooting can be a real headache. Maybe you have sensors in a smart city project, or perhaps a fleet of connected machines in different factories. Having a way to reach them all from your desk, securely, is pretty much essential these days, and that's where SSH over AWS really shines, you know.
The Security Edge
One of the biggest worries with IoT is keeping everything safe from unwanted access. SSH, or Secure Shell, is, like, built specifically for creating secure connections. When you combine this with AWS's already strong security features, you get a setup that’s very hard for unauthorized people to get into. This integration of SSH with AWS IoT services helps businesses improve their security position and makes device handling much simpler, which is a good thing.
Scalability and Reach
AWS's powerful infrastructure makes connecting IoT devices through SSH over the internet a very smooth operation. Whether you have ten devices or ten thousand, the system can handle it without much trouble. This means you can manage your devices from just about anywhere in the world, which is incredibly useful for global operations or devices located in hard-to-reach spots. It really gives you a lot of freedom, you see.
Streamlined Management
Being able to access your IoT devices remotely through SSH means you can do a lot of things without needing to send someone out to the device itself. You can push software updates, check system logs, or even restart a device, all from your computer. This kind of remote control saves a lot of resources and helps keep your IoT network running smoothly, which is very important for operational efficiency.
Getting Started: Prerequisites and Setup Choices
Before you can start connecting to your IoT devices using SSH over AWS, there are a few things you need to have ready. The specific steps for getting everything prepared can change a bit depending on whether you choose a quick way or a more detailed, manual approach for opening a connection and getting to your distant device. It's kind of like picking a fast route or a scenic one, both get you there, just differently.
What You'll Need
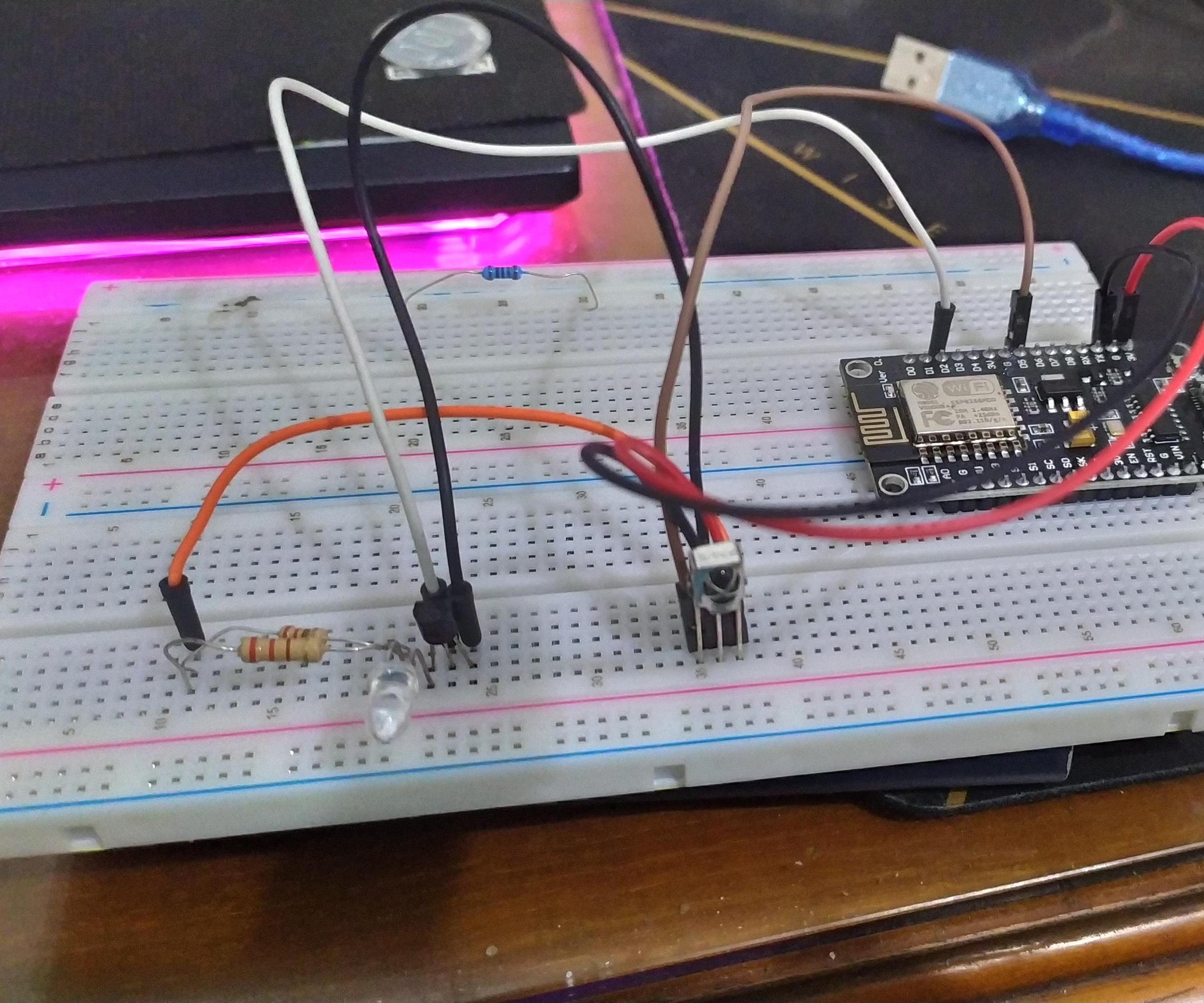
To begin, you'll need an active AWS account, of course, and some basic familiarity with the AWS console. Your IoT device itself needs to be capable of running SSH, which usually means it's a Linux-based system like a Raspberry Pi or an embedded Linux board. You'll also need an SSH client on your local computer, which is standard on most Linux and macOS systems, and easily available for Windows, too.
Quick vs. Manual Tunnel Setup
AWS offers a couple of ways to set up the secure tunnel needed for SSH access. There's a quick setup method, which is great for getting things going fast, and then there's a manual setup method that gives you more control over the specific configurations. The choice often depends on your comfort level with AWS services and the particular needs of your project, so you can pick what feels right.
The Core Components: AWS Services at Play
To make this whole remote SSH IoT connection work, you'll be using several key AWS services together. Each service plays a really important part in creating a secure, reliable path between your computer and your IoT device. It's like a team working together, you know.
AWS IoT Core
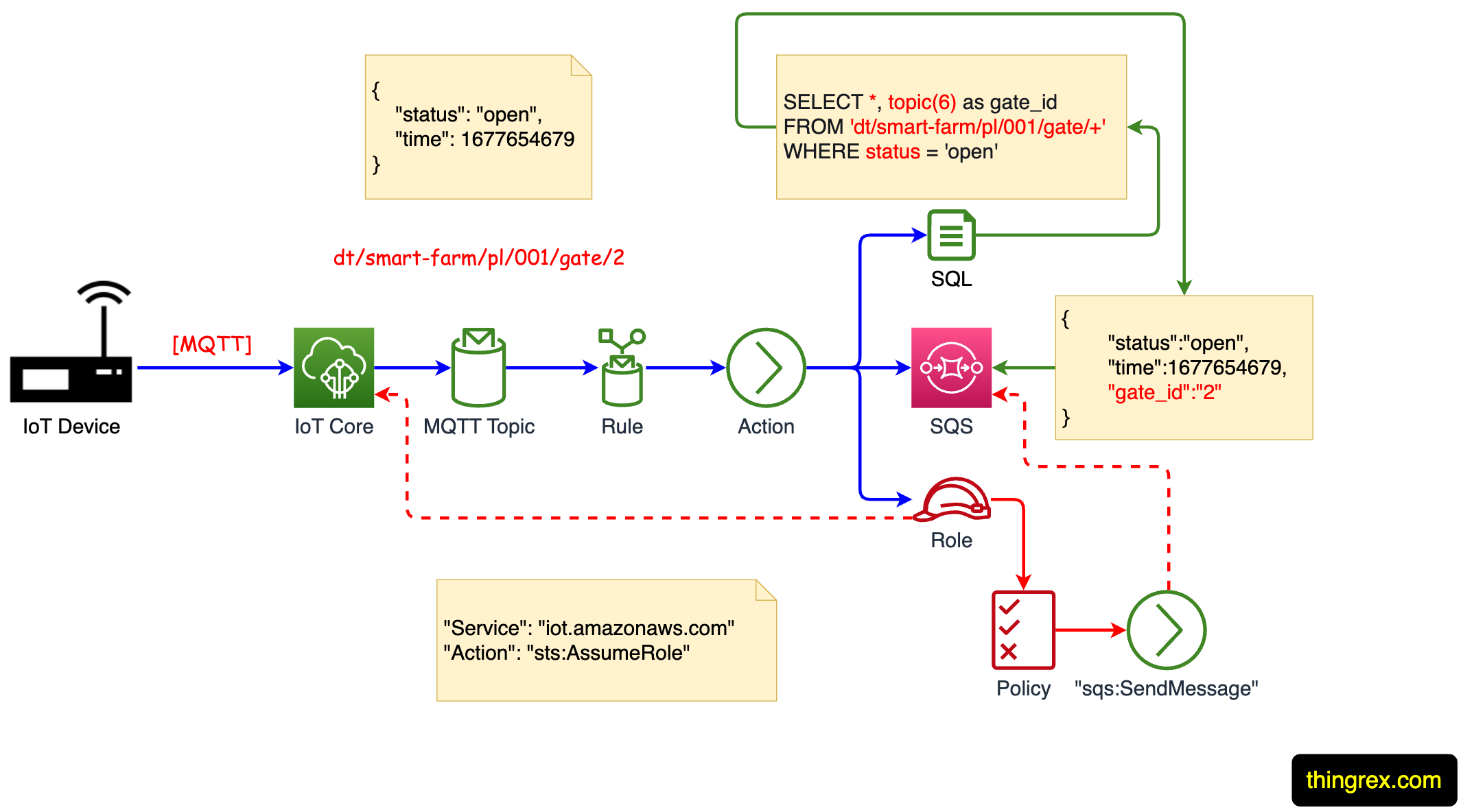
AWS IoT Core is, essentially, the central hub for all your IoT devices. It allows billions of IoT devices to connect to AWS services without needing to manage servers. It helps your devices talk to the cloud, send data, and receive commands. This service is crucial for registering your devices and managing their identities, which is a big part of keeping things organized and safe.
AWS IoT Secure Tunneling
This is, arguably, the star of the show for our purposes. AWS IoT Secure Tunneling creates a secure, bidirectional communication channel between your source device (your local computer) and your destination device (your IoT device), even if your IoT device is behind a firewall or NAT. This tutorial shows how to open a tunnel, which is pretty neat. It means you don't need to open inbound ports on your IoT device's network, which is a huge security benefit.
EC2 Instances (as a Jump Host)
Sometimes, for added security or specific network setups, you might use an Amazon EC2 instance as a "jump host." This means you first SSH into the EC2 instance, and then from there, you SSH into your IoT device through the secure tunnel. Combining AWS IoT Core, EC2 instances, and SSH protocols helps you create a very smooth and secure connection to your IoT devices, you see. It's an extra layer of protection.
Virtual Private Cloud (VPC) Considerations
For more complex setups, especially in corporate environments, integrating your IoT solution with an AWS Virtual Private Cloud (VPC) can be really helpful. With the integration of AWS IoT, VPC, and SSH, users can securely get to and manage their IoT devices from just about anywhere in the world. This allows you to create a private, isolated network within AWS where you can launch resources and control access, adding another layer of network security, which is quite important.
Step-by-Step: Connecting Your IoT Device via SSH Over AWS
Now, let's get into the practical side of things. This guide is going to take you through everything you need to know about setting up remote access to your IoT devices using SSH over the web. We'll explore how to configure SSH access for IoT devices using AWS while keeping the highest security standards in mind, which is a good approach.
Preparing Your IoT Device
First, your IoT device needs to be ready. This typically means ensuring SSH is enabled on the device and that you have a user account with appropriate permissions. You'll also need to install the AWS IoT Device SDK or a similar client that can interact with AWS IoT Core and secure tunneling. Make sure your device has internet access and can communicate with AWS endpoints, too.
Creating an AWS IoT Secure Tunnel
This is where the magic really happens. You'll go to the AWS IoT console, find your device (often called a "thing"), and create a secure tunnel. When you create a tunnel from the thing details page of the AWS IoT console, you can also specify some settings for it. This process generates two client access tokens: one for the source (your local machine) and one for the destination (your IoT device). These tokens are, like, super important for establishing the connection.
For an example tutorial, see open a tunnel and start SSH session to remote device. This will give you a clear walkthrough.
Connecting from Your Local Machine
Once the tunnel is created, you'll use the source client access token on your local computer. You'll typically use the AWS IoT Secure Tunneling client (often a small executable or script) to initiate the connection. This client uses the token to establish its side of the secure tunnel, creating a local port that will forward traffic to your IoT device. It's a pretty clever system, actually.
Using the AWS IoT Console Terminal (or External Client)
After creating the tunnel, you have a couple of options for actually running your SSH session. You can SSH directly within the browser using the AWS IoT console's built-in terminal, which is very convenient for quick checks. Alternatively, you can open a terminal outside the AWS IoT console on your local machine and connect to the local port established by the tunneling client. This tutorial shows how to use the terminal outside the console to get to the remote device, which many developers prefer for more extensive work. You have successfully connected to your device over the internet using a secure encrypted SSH connection, which is a great feeling.
Best Practices for Secure IoT SSH Access
While AWS IoT Secure Tunneling makes connections safe, it's still very important to follow some best practices to keep your entire setup as secure as possible. Think of it as putting extra locks on a very strong door, just to be extra careful.
Identity and Access Management (IAM)
Always use AWS Identity and Access Management (IAM) to control who can create and manage secure tunnels. Give specific users or roles only the permissions they absolutely need, and nothing more. This means creating policies that limit access to tunnel creation and management, which is a fundamental security step.
Least Privilege Principle
Apply the principle of least privilege to your IoT devices themselves. The user account on your IoT device that you SSH into should only have the necessary permissions to perform its intended tasks. Avoid using the root user for daily operations, for example, which is a common security recommendation.
Monitoring and Logging
Keep a close eye on your tunnel activity. Use AWS CloudWatch logs to monitor tunnel creation, connection attempts, and disconnections. This helps you spot any unusual activity that might suggest a security issue. Regular checks of these logs are, arguably, a very important part of your security routine.
Regular Security Audits
Periodically review your security configurations, including IAM policies, device permissions, and SSH keys. New vulnerabilities can emerge, so staying updated and performing regular audits helps ensure your system remains secure over time. It's a bit like checking your car regularly, you know, to make sure everything is still running well.
Frequently Asked Questions
People often ask a few common things about using SSH with IoT devices over AWS. Here are some answers to those questions.
Is SSH over AWS IoT Secure Tunneling really safe?
Yes, it's actually very safe. AWS IoT Secure Tunneling uses strong encryption for all data passing through the tunnel. It also helps because your IoT device doesn't need to have any inbound ports open on its network, which removes a common way for attackers to get in. So, you know, it's a pretty robust solution.
Can I use this method with any IoT device?
You can use this method with any IoT device that supports SSH and can run a small client application to connect to the AWS Secure Tunneling service. Most Linux-based IoT devices, like Raspberry Pis or industrial controllers running Linux, are a good fit. Devices that don't have an operating system capable of running an SSH server or the tunneling client won't work with this specific approach, though.
What if my IoT device loses its internet connection?
If your IoT device loses its internet connection, the secure tunnel will, of course, be disconnected. You won't be able to SSH into it until the device re-establishes its internet connection and can reconnect to AWS IoT Core. It's important to have a reliable network connection for your IoT devices if you plan on managing them remotely, which makes a lot of sense.
This blog has shown you how AWS IoT Secure Tunnel can create a safe path to your IoT device, letting you perform remote operations using SSH. We've gone over everything from the basics of SSH and IoT to some more advanced setups using AWS services. By the end of this, you’ll have the know-how and confidence to get this working for your own devices. Learn more about IoT security on our site, and for more technical specifics, you can link to this page about AWS IoT Secure Tunneling deep dive.
- Eric Weinstein Net Worth
- Jerry Garcia Net Worth At Death
- Nicole Aniston Bts
- Ashley Loo Erome
- Bettijo Hirsch

Detail Author:
- Name : Mrs. Laura Klocko
- Username : rocky53
- Email : lucie.monahan@stoltenberg.com
- Birthdate : 2002-03-14
- Address : 610 Carter Loop Port Richie, KS 37049
- Phone : 205.294.7700
- Company : Willms Inc
- Job : Compensation and Benefits Manager
- Bio : Officiis et repellat ut nihil similique quia. Maiores sed quia dolores esse cupiditate laborum quia. Optio neque cum numquam ad facilis. Eum quibusdam et laboriosam recusandae.
Socials
twitter:
- url : https://twitter.com/gulgowskij
- username : gulgowskij
- bio : Ipsum numquam quaerat sit placeat repudiandae. Soluta quaerat ipsum quam amet et id soluta. Delectus corporis et ipsum est iure.
- followers : 3660
- following : 2746
instagram:
- url : https://instagram.com/jeanne.gulgowski
- username : jeanne.gulgowski
- bio : Atque id et culpa deleniti aut. Sunt ut aut non eos. Dolor in ut dolores.
- followers : 2657
- following : 2617