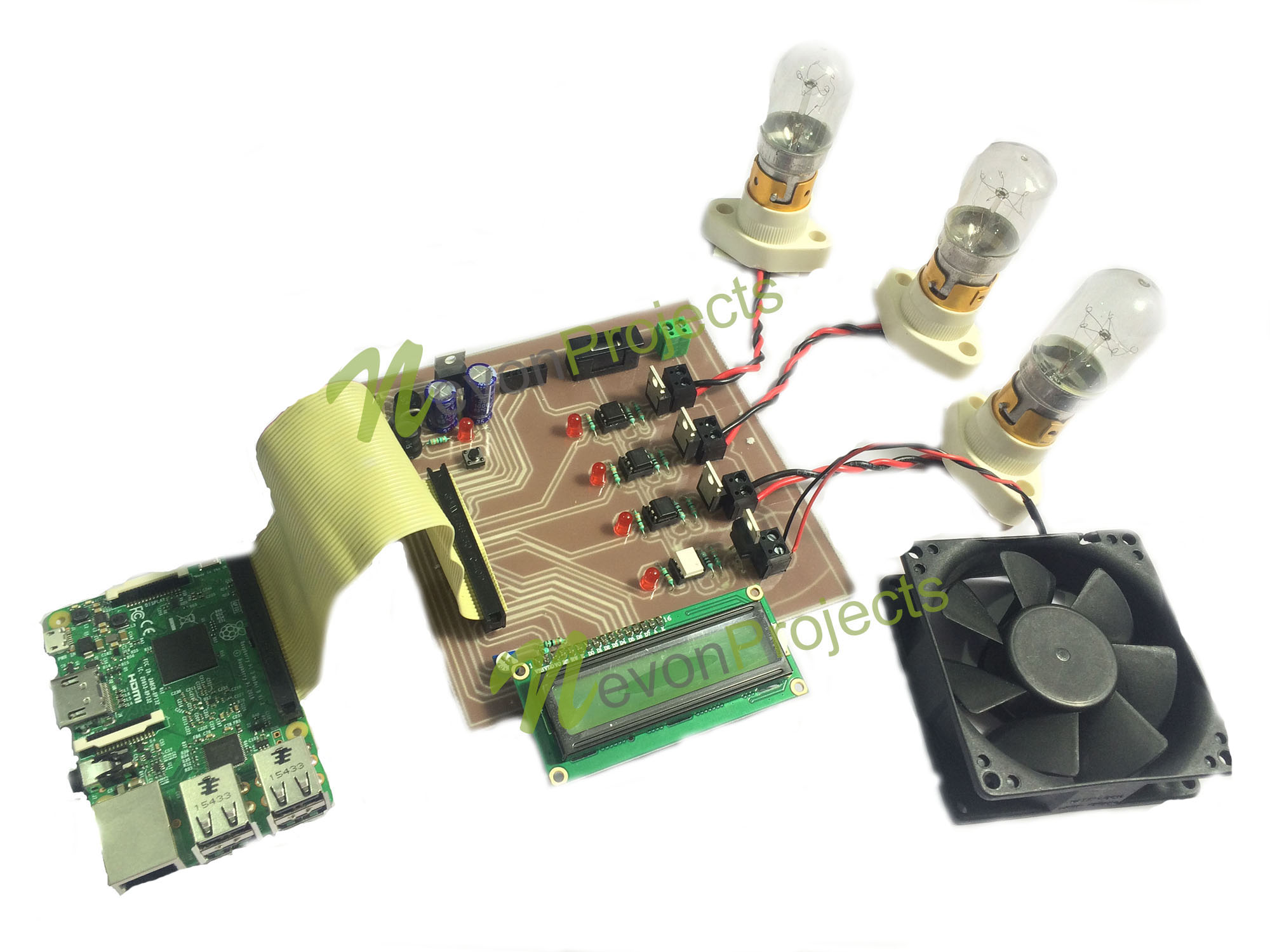
It's a familiar feeling, isn't it? That little knot of worry when you see a message like "This connection is untrusted" or perhaps "Your device is at risk because it's out of date." We all want our tech to just work, and more importantly, to work safely. For anyone dabbling with a Raspberry Pi as a far-off Internet of Things device, making sure it talks to its home base without trouble, and without letting unwanted guests listen in, is really important, you know?
Maybe you've had a moment where an update just won't stick, or you're just trying to keep your system safe from those digital snoops. That's why figuring out how to link up your tiny computer, your Raspberry Pi, to a virtual private cloud, or VPC, for IoT tasks is such a big deal. It's about building a strong, private pathway for your data, making sure everything stays just between you and your devices, which is pretty essential these days, I mean.
This article will walk you through the ways to set up a very safe connection for your distant Raspberry Pi within a VPC. We'll look at why security is so important, what a VPC actually does for your IoT projects, and how to put it all together. You'll get some practical ideas to keep your little Pi well-protected and running smoothly, so, let's get into it, shall we?
Table of Contents
- What's the Big Deal About Secure IoT?
- Understanding VPCs for Your Raspberry Pi
- Setting Up Your Secure Connection: A Step-by-Step Approach
- Monitoring and Maintaining Your Secure Setup
- Frequently Asked Questions
What's the Big Deal About Secure IoT?
Picture this: you've got a cool project running on a Raspberry Pi, maybe it's watching your plants or tracking your home's energy use, and it's sending data to the cloud. That data, you know, could be quite personal or important. Without proper safety measures, it's like leaving your front door wide open in a busy city, which, as a matter of fact, isn't a good idea for anything valuable, is it?
- How Many Kids Did Loretta Lynn Have
- Sophia Rain Leak
- Does Kevin Bacon Smoke Cigarettes
- Dj Qualls Illness
- Michael Desmond Lindenhurst
The Internet of Things, or IoT, has really changed how we interact with the physical world, linking up everyday items to the web. But with all this linking, there's also a bigger chance for things to go wrong if we're not careful. Keeping these connections safe is not just a nice-to-have; it's a must-do, especially when you're dealing with distant devices that might be out of your direct sight, so, that's something to think about.
Why Security Matters for Your Pi
Your Raspberry Pi, while small and mighty, is still a computer, and like any computer, it can be a target. If someone gets into your Pi, they could mess with your data, use your device for bad stuff without you knowing, or even get into other parts of your network. We've all seen those warnings about devices being "at risk" or "missing important security updates," and for a good reason, you know?
It's not just about protecting your specific project; it's about protecting your privacy and the overall health of your digital life. A compromised Pi could, for example, be used to send out spam or launch attacks on other systems, making you an unwilling participant in something harmful. Keeping it safe from the start just makes good sense, essentially.
Common Pitfalls of Insecure Connections
Many folks, when they first set up a far-off Pi, might just open up a port on their home router or use simple passwords. This is, to be honest, a bit like leaving a spare key under the doormat. It's an easy way for someone with bad intentions to get in. You might also run into issues where a connection is "untrusted," like when your browser gives you a warning about a website, which can be pretty annoying, right?
Other problems include using outdated software, which often has known weak spots that attackers can take advantage of. Or, perhaps, not setting up proper access controls, meaning anyone who finds your device can try to log in. These simple mistakes can lead to big headaches, and that's something we definitely want to avoid, you know?
Understanding VPCs for Your Raspberry Pi
So, you're wondering how to make those far-off Pi connections really safe? A Virtual Private Cloud, or VPC, is a pretty strong answer. Think of it as your own private, well-guarded corner within a bigger public cloud, like AWS or Google Cloud. It gives you a lot more control over who and what can talk to your devices, which is, frankly, a huge step up for security.
It's not just about having a safe place; it's about building a digital fortress around your IoT devices. This means you can decide exactly which parts of your network can see your Pi, and which can't. It's a way to keep your Raspberry Pi out of the general public's view, and that, you know, makes a big difference.
What is a Virtual Private Cloud
A VPC is, essentially, a logically isolated section of a cloud provider's network where you can launch resources in a virtual network that you define. You get to pick your own IP address ranges, set up subnets, and configure network gateways. It's like having your own dedicated server room, but it's all virtual, and you're sharing the physical hardware with others, but in a way that your stuff stays totally separate, which is pretty clever, really.
This isolation is key. It means your Raspberry Pi, when it's linked to this VPC, isn't just floating out on the open internet. Instead, it's inside your own private network bubble. This gives you a much better handle on traffic flow and who can reach your devices, and stuff, which is a major benefit.
Benefits for IoT Deployments
For IoT projects using a Raspberry Pi, a VPC offers several really good advantages. First, it gives you a safe space for your devices. You can put your Pi in a private subnet, meaning it doesn't have a public IP address and can't be directly reached from the internet. This significantly cuts down on unwanted access attempts, you know?
Second, you can set up very detailed rules about what kind of network traffic is allowed in and out of your VPC. This means you can restrict communication only to the specific services and ports your Pi needs, blocking everything else. This helps prevent those "untrusted connection" warnings and keeps things running smoothly. Third, it helps you manage your devices better, especially if you have many of them. You can group them, apply consistent security policies, and monitor their activity from one central place, which, honestly, simplifies things a lot.
Setting Up Your Secure Connection: A Step-by-Step Approach
Getting your far-off Raspberry Pi to securely connect to a VPC involves a few important steps. It's not just about flipping a switch; it's about building layers of safety. We'll start with the Pi itself, then move to the cloud side of things, and finally, look at how they can talk to each other in a really safe way, you know, so, let's get started.
This process might seem like a bit much at first, but each step adds to the overall strength of your setup. It's like building a strong house; you need a good foundation and sturdy walls. For your Pi, that means getting its basic security right before connecting it to the bigger cloud world, which is, pretty logical, right?
Initial Raspberry Pi Hardening
Before your Pi even thinks about connecting to a VPC, you should make it as tough as possible on its own. This is about closing off the easy ways in that many people often forget. Think of it as putting on its armor before sending it into battle, which, honestly, is just good common sense.
These initial steps are quick but make a huge difference in protecting your device from the get-go. It's a bit like making sure your home's locks are good before you even think about an alarm system, you know?
Changing Default Credentials
The very first thing to do is change the default username and password on your Raspberry Pi. Many Pi images come with standard login details (like 'pi' and 'raspberry'). If you leave these as they are, it's an open invitation for anyone to get in, as a matter of fact. Seriously, change them to something long and complex right away. This is a basic but absolutely essential step for any new device, you know?
Using a strong, unique password for your Pi is one of the easiest ways to keep it safe. It prevents simple, automated attacks that try common passwords. You might also want to set up SSH key-based authentication instead of passwords for even better security, which, honestly, is a great idea.
Keeping Software Updated
Remember those frustrating messages about "Your device is at risk because it's out of date and missing important security and quality updates"? That's exactly why keeping your Pi's software current is so important. Software updates often include fixes for security holes that bad actors could use to get into your system, you know?
Regularly run `sudo apt update` and `sudo apt upgrade` on your Raspberry Pi. You can even set this up to happen automatically, so you don't forget. This helps make sure your Pi always has the latest protection against known threats, which, essentially, keeps it much safer. It's a simple habit that really pays off, you know?
VPC Configuration Essentials
Now, let's look at the cloud side of things. Setting up your VPC correctly is key to creating that private, secure space for your Pi. This involves drawing the boundaries and setting the rules for your virtual network, which, frankly, gives you a lot of control.
These settings are where you define who can talk to your Pi and how. It's like designing the layout of your secure building and deciding where the doors and windows go, which is, pretty much, what you want for security.
Subnets and Security Groups
Within your VPC, you'll want to create subnets. A private subnet is a good place for your Pi, as it means the Pi won't have a public IP address and can't be reached directly from the internet. This is a major layer of protection. Then, you use security groups, which act like virtual firewalls for your individual devices, you know?
Security groups let you specify exactly which types of traffic are allowed in and out of your Pi. For example, you might only allow SSH access from a specific IP address range (like your home network or a jump box) and block everything else. This is a very powerful tool for limiting exposure, and stuff, which is really helpful.
Network Access Control Lists
Network Access Control Lists, or NACLs, are another layer of security, acting like firewalls for your subnets. While security groups are stateful (meaning if you allow outbound traffic, the return inbound traffic is automatically allowed), NACLs are stateless, meaning you have to explicitly allow both inbound and outbound rules, you know?
This gives you a finer grain of control at the subnet level. You can use NACLs to block specific IP addresses or ports at a broader level before traffic even reaches your security groups. It's an extra line of defense that, honestly, adds a lot of peace of mind.
VPN or SSH Tunneling: Your Secure Gateway
Even with your Pi in a private subnet, you still need a way to reach it safely from outside the VPC. This is where VPNs (Virtual Private Networks) or SSH (Secure Shell) tunneling come into play. These create a protected channel for your communication, so your data travels without being seen by others, which is pretty neat, right?
Choosing between a VPN and SSH tunneling depends a bit on your needs and how much traffic you expect. Both are good options for establishing a safe link to your far-off Pi, which, essentially, is what we're aiming for.
OpenVPN on Raspberry Pi
Setting up OpenVPN on your Raspberry Pi allows it to connect to a VPN server within your VPC. This creates a secure, encrypted tunnel between your Pi and your VPC, making it appear as if your Pi is physically inside your private cloud network. All traffic between your Pi and the VPC then travels through this encrypted tunnel, which is, honestly, a very strong way to protect your data.
This approach is great for continuous, secure access and for routing all your Pi's network traffic through the VPC. There are many guides available for setting up an OpenVPN client on a Raspberry Pi, and it's a very common and trusted method for secure remote access, you know?
SSH Tunneling Best Practices
SSH tunneling is another way to create a secure connection, often used for specific tasks rather than routing all traffic. You can use SSH to forward ports, allowing you to access services on your Pi that are otherwise blocked by security groups, all through an encrypted SSH connection, you know?
Always use strong SSH keys instead of passwords. Disable password authentication for SSH on your Pi. Limit SSH access to only specific IP addresses or subnets. This keeps your SSH connection very tight and reduces the chances of someone trying to guess their way in, which, honestly, is just good practice.
Identity and Access Management (IAM)
Managing who can do what within your cloud environment is just as important as network security. Identity and Access Management (IAM) tools, offered by cloud providers, let you control permissions for users and services. This means you can give your Pi, or the services that interact with it, only the exact permissions they need to do their job, and nothing more, which is called the principle of least privilege, you know?
For instance, if your Pi needs to upload data to a specific storage bucket, you create an IAM role that grants only that permission. This prevents a compromised Pi from being used to access other parts of your cloud account, which, essentially, is a critical safeguard. It's about making sure everyone has just the right keys, and no extras.
Monitoring and Maintaining Your Secure Setup
Setting up your secure connection is a great first step, but security is an ongoing effort, not a one-time task. You need to keep an eye on things and make sure everything stays up-to-date. It's like having a security system for your home; you still need to check it and make sure it's working properly, you know?
Staying on top of your system's health and security helps prevent problems before they become big issues. This means regularly checking logs and making sure your software is current, which, honestly, just keeps things running smoothly.
Regular Audits and Logs
Your Raspberry Pi and your VPC generate logs that record activity. Regularly checking these logs can help you spot unusual behavior or attempted breaches. For example, if you see many failed login attempts to your Pi, that could be a sign of trouble. Cloud providers also offer logging services that track activity within your VPC, which is, pretty useful, really.
Setting up alerts for specific types of activity, like unauthorized access attempts or changes to security configurations, can give you an early warning. This proactive approach helps you react quickly to potential threats, which, essentially, is what good security is all about.
Automated Updates and Patches
We've talked about the importance of keeping software updated, and it's worth mentioning again. Manual updates can be easy to forget, leading to your device being "out of date and missing important security and quality updates." Setting up automated updates for your Raspberry Pi's operating system and applications is a smart move, you know?
Many Linux systems allow you to configure unattended upgrades. While you should still occasionally check that updates are applying correctly (especially if you've had issues with updates failing to reinstall), automation helps ensure your Pi is always running with the latest security fixes. This helps prevent those "untrusted connection" warnings by keeping your system robust, and stuff.
Frequently Asked Questions
What's the best way to secure my Raspberry Pi for remote access?
The best way involves a few steps: change default passwords right away, use SSH key-based authentication, keep your Pi's software updated, and connect it through a VPN or SSH tunnel to a private network like a VPC. This layered approach really helps keep things safe, you know?
How can I make sure my IoT data is private when using a Raspberry Pi?
To ensure your IoT data stays private, use encrypted communication channels like TLS/SSL for any data sent from your Pi to the cloud. Put your Pi in a private subnet within a VPC, use strong access controls, and encrypt any sensitive data stored on the Pi itself. This way, your information is protected at every step, which, honestly, is pretty important.
Why should I use a VPC instead of just a VPN for my remote Raspberry Pi?
A VPC gives you a dedicated, isolated network space in the cloud where you can place your Pi, offering more control over network traffic and security rules than just a VPN alone. A VPN creates a secure tunnel, but a VPC provides the entire secure environment. Using both together, with the VPN connecting your Pi *into* the VPC, gives you the strongest setup for securely connect remote iot vpc raspberry pi, which, essentially, is a great combination.
Learning how to securely connect remote iot vpc raspberry pi is a big step in protecting your projects. For more on keeping your devices safe, you might want to learn more about network security best practices.
- Ben Stein Net Worth
- Norafawn Leaks
- Was Miranda Actually Pregnant In Satc
- Warren Haynes Net Worth
- Who Earns More Neurologist Or Neurosurgeon

Detail Author:
- Name : Barry Davis
- Username : hickle.judson
- Email : broderick67@muller.biz
- Birthdate : 1983-07-07
- Address : 766 Isabell Mountain Apt. 918 West Jasperstad, MI 83788
- Phone : 906-693-3898
- Company : Romaguera-Muller
- Job : Singer
- Bio : Necessitatibus et numquam est in. Dolores ducimus est iure.
Socials
linkedin:
- url : https://linkedin.com/in/ross7336
- username : ross7336
- bio : Ut error praesentium et aut.
- followers : 5739
- following : 1673
twitter:
- url : https://twitter.com/ross.hackett
- username : ross.hackett
- bio : Aspernatur eum sequi sit. Repellendus non saepe repudiandae nobis. Doloribus dolorem optio et quos culpa odit aut.
- followers : 1390
- following : 309
instagram:
- url : https://instagram.com/ross_id
- username : ross_id
- bio : Fugiat quasi tenetur et. Sed non ut earum sed voluptates.
- followers : 6624
- following : 1420