Are you finding it tough to connect with your smart devices when you are away from home or the office? It's a common puzzle, especially when your internet connection has a firewall in the way, and you're trying to make a Mac server do the heavy lifting. Many people, you know, want to keep an eye on their IoT gadgets, maybe adjust a smart thermostat or check a security camera, but those digital walls often stop them. This piece will show you how to get your remote IoT setup working, making your Mac server a friendly go-between for your devices and the outside world.
It can feel a bit like trying to talk to someone through a closed door, right? Your Internet of Things, or IoT, devices are there, ready to take your commands, but the firewall on your network acts as a guard, keeping outside requests from reaching them. This is a good thing for safety, of course, but it does mean we need a clever way to bridge that gap. We will explore ways to put your Mac server into service for this specific purpose, making sure your smart home or office stays connected, no matter where you are.
So, if you have a Mac server and a bunch of smart things you want to manage from afar, you've come to the right place. We will walk through the steps needed to make this happen, giving you a clearer picture of how to use remoteiot behind firewall using mac server effectively. By the time we finish, you will have a good idea of how to make your Mac server a central point for all your remote IoT needs, keeping things safe and accessible, which is pretty neat, if you ask me.
- Abigail Spencer Nudes
- Sophie Rain Nude
- What Sign Is Teyana Taylor
- Sadee Horvat
- Jaylen Brown Net Worth 2025
Table of Contents
- The Challenge of Firewalls and IoT
- Your Mac Server: A Central Point
- Getting Your Mac Server Ready
- Making Your Connection Safe and Sound
- Connecting Up Your IoT Gadgets
- Sorting Out Common Problems
- Frequently Asked Questions
The Challenge of Firewalls and IoT
Firewalls, you know, are like digital bouncers for your home or office network. They stand at the entrance, checking everything that tries to come in or go out. Their main job is to keep unwanted things, like bad software or people with ill intentions, from getting to your computers and devices. This is very good for keeping your private information safe, so it's a valuable thing to have, actually.
However, this very protection can make it tricky for your IoT devices. These gadgets often need to talk to you or their own services on the internet, even when you're not physically there. A firewall, by its very nature, might block these connections because it sees them as incoming requests from unknown places. So, getting your smart lights or cameras to respond to your commands from miles away becomes a bit of a head-scratcher, which is something many people face.
We need a way to tell the firewall that certain incoming messages are okay, that they are meant for your IoT devices, and that they should be allowed through. This is where your Mac server can come into play, serving as a clever helper to make those connections happen. It's about making the firewall understand who belongs and who doesn't, more or less.
- Zak Brown Net Worth
- Brett Kelly Now
- Who Lives In Silverleaf Scottsdale
- Rob Minkoff Net Worth
- Liezel Lopez Husband
Your Mac Server: A Central Point
Think of your Mac server as a kind of command center for your smart things. It's always on, always connected to your local network, and it has the computing muscle to handle different tasks. This makes it an ideal machine to put into service for managing your IoT devices, especially when a firewall is involved. It can act as a bridge, or a relay, for those important messages.
Instead of trying to get every single IoT device to talk directly through the firewall, which can be a security headache and a lot of work, you can get them to communicate with your Mac server first. Then, your Mac server, being a more capable machine, can manage the connection to the outside world in a much more controlled and secure way. This approach, you know, simplifies things a great deal.
By employing your Mac server in this way, you make one point of contact for remote access, rather than many. This is generally much easier to keep safe and to adjust as needed. It helps you bring order to your network, making it simpler to use remoteiot behind firewall using mac server for all your smart home or office needs, which is a pretty smart move.
Getting Your Mac Server Ready
To make your Mac server work as this central point, there are a few initial setup steps you will need to take. These steps involve making sure your network is set up in a particular way and that your Mac is prepared to handle the incoming requests. It's about getting all your ducks in a row, so to speak, so everything runs smoothly.
Basic Network Setup
First off, you will want to give your Mac server a fixed address on your local network. This is called a static IP address. Why do this? Well, if your Mac's address keeps changing, it would be like trying to send mail to a house that moves every day. It makes it really hard for other devices, or for you from afar, to find it reliably, so that's a key thing.
You can usually set this up in your router's settings, or directly on your Mac itself within the Network preferences. Just pick an address that isn't already being used by another device and is outside the range your router usually hands out automatically. This way, your Mac always has the same spot on the network, which is quite important for consistent connections, you know.
Also, make sure your Mac server is always on and connected to your network, preferably with a cable rather than Wi-Fi if possible. A wired connection is usually more stable and faster, which is always a good thing for a server. This gives it a solid foundation to make something serve your purpose of remote IoT access, you see.
Opening Doors with Port Forwarding
Now, let's talk about port forwarding. This is the part where you tell your router, the main device that connects your home to the internet, to send specific types of incoming internet traffic to your Mac server. It's like telling the post office that any mail addressed to "IoT Control" should always go to your Mac's specific room in the house, so to speak.
You will need to get into your router's administration page, usually by typing its IP address into a web browser. Look for a section often called "Port Forwarding," "Virtual Servers," or "NAT Settings." Here, you will create rules that point certain external port numbers to your Mac server's internal static IP address and a specific internal port number. For example, if you use a VPN on your Mac, you might forward the VPN's port to your Mac's internal address, which is quite common.
It's important to only open the ports you absolutely need and to know what those ports are for. Opening too many ports, or the wrong ones, can create security risks. So, be a bit careful here, and only forward ports that are really necessary for your Mac server to receive connections for your remote IoT setup, which is a big part of keeping things safe. Learn more about network security on our site.
Keeping Track of Your IP: Dynamic DNS
Most home internet connections have what's called a dynamic IP address. This means the internet address your home uses to talk to the rest of the world can change from time to time. If you are trying to connect to your Mac server from outside your home, and its external IP address changes, you won't be able to find it, which is kind of a problem.
This is where Dynamic DNS, or DDNS, comes in handy. DDNS services give you a fixed web address, like `myiotmac.ddns.net`, that always points to your home's current external IP address, even if it changes. You sign up for a service, install a small program on your Mac, or configure your router, and it automatically updates the DDNS service whenever your IP address shifts. This way, you can always employ that fixed web address to reach your Mac server, which is really helpful.
There are several free and paid DDNS providers out there, so you can pick one that works for you. Setting this up is a good step toward making sure you can always connect to your Mac server, no matter when your internet service provider decides to change your external IP address. It truly makes remote access much more reliable, you know.
Making Your Connection Safe and Sound
Opening up connections through your firewall needs to be done with care, as it can create potential ways for unwanted visitors to get in. So, making your connection safe is a very important part of this whole process. We want to be able to use remoteiot behind firewall using mac server without any worries, which means adding layers of protection.
The Power of a VPN
One of the best ways to connect to your Mac server and your IoT devices securely is by using a Virtual Private Network, or VPN. A VPN creates a secure, encrypted tunnel between your remote device (like your phone or laptop) and your Mac server. It's like having a private, secret road directly to your home network, making it much harder for anyone to snoop on your traffic.
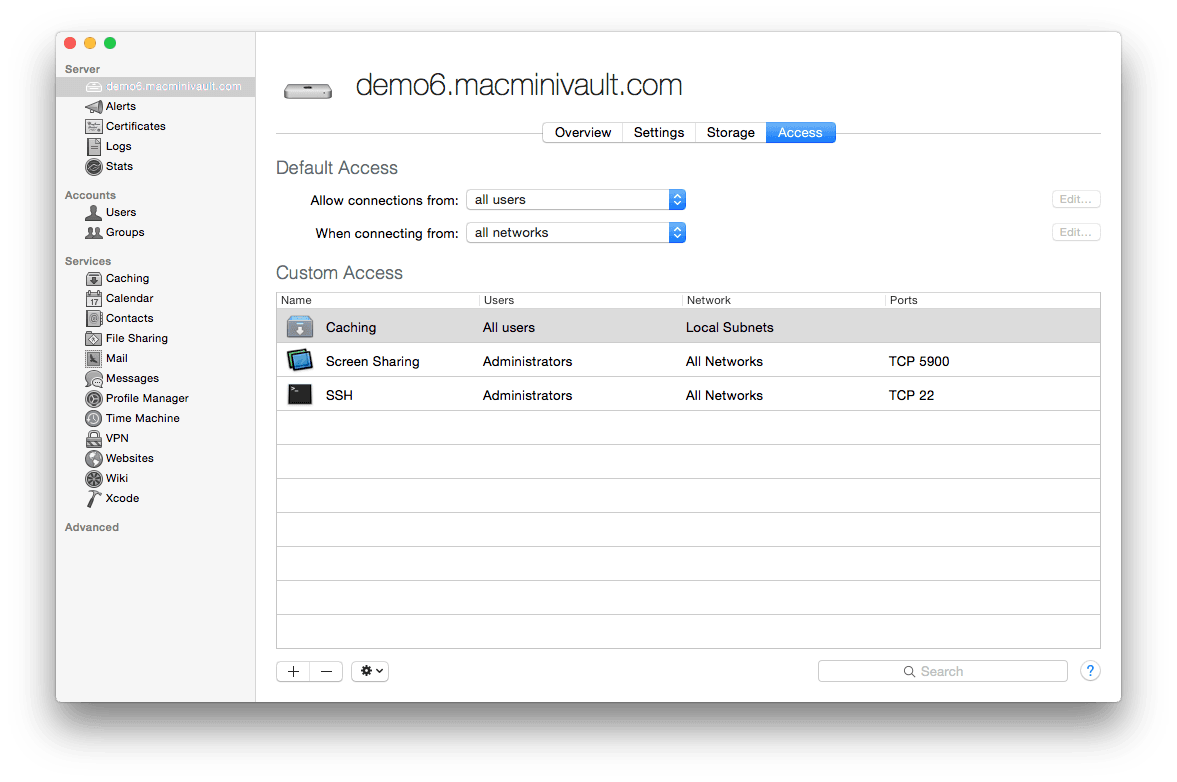
You can set up a VPN server directly on your Mac. macOS has built-in capabilities for this, or you can use third-party software. Once your Mac is acting as a VPN server, you would configure your router to forward the VPN's specific port to your Mac. Then, when you're away, you simply connect your phone or laptop to your home VPN. Once connected, your device acts as if it's physically on your home network, giving you direct access to your IoT devices as if you were sitting right there, which is pretty cool.
Using a VPN is generally seen as the most secure method because all your traffic is encrypted, and you are not leaving any open ports directly exposed to the internet for your IoT devices. This is a much better way to make something serve your purpose of remote access while keeping things private and secure, which is something we all want, I mean.
SSH Tunnels: A Secret Path
Another clever way to create a secure connection is through an SSH tunnel. SSH, or Secure Shell, is a protocol often used to connect to remote computers securely. You can employ it to create a secure "tunnel" for your IoT traffic. It's a bit like creating a hidden, protected pathway for your data to travel through, right to your Mac server.
To use an SSH tunnel, you would first need to enable SSH access on your Mac server. Then, from your remote device, you would establish an SSH connection to your Mac server, forwarding a specific local port on your remote device to a specific port on your Mac server, or even directly to an IoT device on your network through your Mac. This method is a bit more technical to set up, but it offers a very strong level of security for specific connections.
SSH tunnels are great for accessing specific services or devices without needing a full VPN connection. It gives you a way to put your Mac server into service as a secure intermediary for particular tasks. Just remember to use strong passwords for your SSH access, as that is truly important for keeping things safe, you know.
Good Habits for Security
Beyond setting up VPNs or SSH tunnels, there are some general good practices that will help keep your entire setup secure. First, always use strong, unique passwords for your Mac server, your router, and all your IoT devices. A mix of letters, numbers, and symbols, and a good length, is key. Seriously, don't use "password123," please.
Keep all your software updated. This includes macOS, your router's firmware, and the software on your IoT devices. Updates often include important security fixes that close potential weaknesses. It's like patching holes in a fence; you want to make sure no gaps are left open. So, regularly checking for updates is a very good idea, I mean.
Finally, regularly check your router's logs and your Mac's firewall settings. Make sure no unexpected connections are being made and that only the ports you intend to open are actually open. Being a bit vigilant helps you make something serve your purpose without inviting trouble, which is something we all want, you know.
Connecting Up Your IoT Gadgets
Once your Mac server is all set up and secure, the next step is to get your IoT devices talking to it. This part will vary quite a bit depending on the type of IoT devices you have. Some devices are designed to communicate with a central hub, while others might offer their own app or web interface. We need to make these devices recognize your Mac server as their gateway to the outside world, or as their local control point, you see.
For many IoT devices, especially those that use local network communication, you might configure them to send their data to your Mac server's internal IP address. Your Mac can then run software that collects this data and presents it to you remotely, or it can forward your commands to the devices. This is a common way to employ your Mac as a smart home hub, you know.
If your IoT devices have their own cloud services, you might not need to do much on the device side itself, beyond making sure they are connected to your local network. The remote access would then happen through your Mac server, which acts as the secure entry point to your network. Your Mac then allows you to reach those cloud services or directly access the devices as if you were home, which is quite useful, you know. To make things even better, you can explore advanced home automation ideas on this site.
It's a good idea to test each device after you make changes. Try connecting to your VPN or SSH tunnel from a different network, like a coffee shop's Wi-Fi, and then try to control your IoT devices. This helps you confirm that everything is working as it should and that your remote access is solid. This is a pretty important step to make sure your setup is truly working for you.
Sorting Out Common Problems
Even with the best planning, you might run into a few bumps along the road when you try to use remoteiot behind firewall using mac server. That's totally normal. Knowing what to look for can save you a lot of time and frustration, so let's go over some common issues and how to deal with them, which is quite helpful, you know.
One common problem is that your remote connection just won't go through. This often points back to the firewall or port forwarding settings. Double-check your router's port forwarding rules. Are the external and internal port numbers correct? Is the internal IP address pointing to your Mac server's static IP address? A small typo can stop everything, so check it carefully, I mean.
Another issue might be related to your dynamic IP address. If you're using a DDNS service, make sure the DDNS client on your Mac or router is actually running and updating correctly. Sometimes, the service might not update quickly enough, or there could be a glitch. You can check your current external IP address by visiting a site like WhatIsMyIPAddress.com and comparing it to what your DDNS service thinks it is, which is a good way to check.
If your IoT devices are not responding, even when you are successfully connected to your Mac server remotely, the problem might be with the devices themselves or how they are configured to talk to your Mac. Make sure they are powered on, connected to your local network, and that any software on your Mac designed to interact with them is running. Sometimes, a simple restart of the device or the Mac software can make things work again, you know.
Finally, remember that security software on your Mac, like its built-in firewall, can also block connections. Make sure that any necessary applications on your Mac that are part of your IoT setup are allowed to receive incoming connections. You can usually adjust these settings in your Mac's System Settings under "Network" and "Firewall." Taking a close look at these settings can often solve many connection puzzles, which is quite useful.
Frequently Asked Questions
Here are some common questions people often ask about getting their IoT devices to work remotely with a Mac server behind a firewall.
How can I tell if my firewall is blocking my IoT devices?
You can often check your router's firewall logs, which might show blocked connection attempts. Also, if you can access your IoT devices when you are on your home network but not when you are away, that's a pretty clear sign the firewall is doing its job a bit too well. You might try temporarily disabling your router's firewall (just for a moment, for testing, then turn it back on!) to see if that makes a difference, which can help you figure things out, you know.
Is it really safe to open ports on my router for remote access?
Opening ports always carries some level of risk, as it creates a direct path into your network. However, by using methods like a VPN or SSH tunnels, you are adding strong layers of security to those open ports. The key is to only open the ports you need, keep your systems updated, and use very strong passwords. So, with careful steps, it can be quite safe, you know.
What if my internet service provider (ISP) blocks port forwarding?
Some internet providers might use what's called "CGNAT" (Carrier-Grade Network Address Translation), which can make traditional port forwarding difficult or impossible. If you suspect this is the case, you might need to explore alternative solutions, such as using a cloud-based relay service or a VPN service that offers a dedicated IP address. You can also contact your ISP to ask about their policies on port forwarding, which is a good first step, you know.
- Sexy Videocom
- Securely Connect Remoteiot P2p Ssh Download Free
- Richard Marx Age
- Corinna Kopf Only Fans Leaked
- Jameliz Smith Onlyfans


Detail Author:
- Name : Davonte Bartoletti
- Username : antonette.kulas
- Email : beer.oceane@ratke.org
- Birthdate : 1979-05-30
- Address : 75530 Desiree Harbor Apt. 417 North Jackelinefurt, NJ 94158-8254
- Phone : 314-946-9106
- Company : Morar-Batz
- Job : Electronic Equipment Assembler
- Bio : Sit et nobis facilis eos maiores. Illo qui qui ut nemo vel et amet. In qui voluptatibus non mollitia architecto velit tempore. Molestiae qui culpa necessitatibus nihil dolor laboriosam.
Socials
linkedin:
- url : https://linkedin.com/in/bauchb
- username : bauchb
- bio : Sit ut error totam accusamus veritatis.
- followers : 3098
- following : 1040
facebook:
- url : https://facebook.com/bradford.bauch
- username : bradford.bauch
- bio : Vel aut veritatis recusandae odio distinctio eos.
- followers : 6365
- following : 76