Connecting to your smart gadgets and remote devices, especially those Internet of Things (IoT) things, can feel like a bit of a puzzle sometimes. You want to make sure everything is running smoothly, right? Yet, there are often these nagging worries about whether your connections are truly safe, or if some update is going to mess things up, like your device getting stuck in a repair loop. Honestly, getting your devices to talk to you from far away, without opening up a whole lot of security holes, is a big deal for many people, especially when you are trying to keep things running well, you know, without too much fuss.
A lot of folks, just like you, are looking for ways to reach their remote devices without spending a fortune or compromising on safety. It's a common story, actually, seeing those "connection untrusted" messages pop up, or maybe struggling with updates that just won't install properly, even when they seem to be there already. That sort of thing can be really frustrating, particularly when you're trying to keep your home automation, industrial sensors, or even just a simple Raspberry Pi project ticking along nicely, more or less.
This guide is here to show you how to securely connect remote IoT devices using P2P SSH, and guess what? It can be done for free, which is pretty cool, really. We will talk about how this method helps you keep your devices safe from prying eyes, makes managing them much easier, and helps you avoid those annoying security warnings that make you think twice about what you are doing. So, let's look at how you can get your remote IoT setup working with peace of mind, basically.
Table of Contents
- Why Secure Remote Access for Your IoT Devices Matters
- What is P2P SSH and How Does It Work for IoT?
- Setting Up Your Free P2P SSH Connection for IoT
- Common Pitfalls and How to Avoid Them
- Frequently Asked Questions About Secure IoT Connections
- Moving Forward with Secure IoT Access
Why Secure Remote Access for Your IoT Devices Matters
Having your IoT devices out in the field, or even just across your house, is super convenient, but it also brings up some questions about how you get to them. You need to be able to check on them, send commands, or grab data, right? And doing all that without putting your network or your personal information at risk is, like, really important. As a matter of fact, many people are looking for solutions to securely connect remote IoT P2P SSH free, and for good reason.
Consider this: your devices might be gathering sensitive information, or they could be part of a system that controls something important. If someone unwanted gets access, the consequences could be pretty bad, actually. Think about those warnings you sometimes see, like "Your device is at risk because it's out of date and missing important security and quality updates." That's a clear sign that keeping things locked down and current is a big deal, you know?
Plus, when you're trying to manage a whole bunch of devices, maybe for a business or just a big personal project, having a reliable and secure way to connect saves a lot of headaches. It helps you keep everything running smoothly, prevent downtime, and react quickly if something goes wrong. That, in short, is why secure remote access isn't just a nice-to-have; it's practically a necessity for modern IoT setups, you know?
- Who Makes Project Source Toilets
- Is James May Gay
- Taylor Schabusiness Bodycam
- Yang Xi Zi Height
- Lina Bina Biography
The Challenges of Untrusted Connections
Have you ever seen a message pop up that says something like, "This connection is untrusted you have asked firefox to connect securely to www.yourwebsite.com, but we can't confirm that your connection is secure"? It's a bit unsettling, isn't it? That sort of warning means your browser, or whatever program you are using, can't verify the identity of the server it's trying to talk to. For IoT devices, this can be a real problem, actually.
An untrusted connection, quite simply, means there's a chance someone could be listening in on your communication, or even pretending to be your device. This is a big no-no when you are sending commands or receiving data from, say, a smart lock or a temperature sensor. You want absolute certainty that you are talking directly to your device, and that no one else is in the middle, basically.
Finding a way to make sure every connection is verified and encrypted is key to avoiding these warnings and keeping your IoT setup safe. It's about building a solid bridge between you and your device, one that only you and your device can cross, which is pretty much the goal when you want to securely connect remote IoT P2P SSH free, you know?
Keeping Your Devices Updated and Safe
It's a common frustration: you get a notification that "Your device is at risk because it's out of date and missing important security and quality updates." Then, you try to update, and sometimes it just fails, or it keeps trying to reinstall something that looks like it's already there. This kind of update trouble is a real headache, and it leaves your devices open to problems, too it's almost.
Regular updates are like giving your devices their flu shots; they protect against new threats and fix known weaknesses. If you can't reliably update your remote IoT devices, they become, like, easy targets for people with bad intentions. A lot of the time, security flaws get found and patched, so if your device isn't getting those patches, it's just waiting for trouble, arguably.
A good remote access solution lets you push those updates easily, even when your devices are far away. It means you can keep everything current and protected, without having to physically go to each device. This is a huge part of keeping your entire IoT ecosystem healthy and secure, as a matter of fact, and it is a big reason why people look for ways to securely connect remote IoT P2P SSH free.
Gaining Control Over Your Gadgets
Imagine you have a bunch of devices, and you need to manage them, maybe setting up specific rules or checking their status. It's a bit like trying to password protect a file in SharePoint, but you don't want to protect the whole folder, just that one file, you know? You want granular control, not a broad brushstroke. For IoT, this means being able to access and manage individual devices without affecting others, basically.
Some people even have to set up really strict rules, like only allowing mail from specific IP addresses for their organization's email, to keep things locked down. That level of precision is what you want for your IoT devices, too. You need to be able to get in, make changes, troubleshoot, or just see what's happening, but only with the right permissions and from a trusted source, you know?
Remote access through a secure method like P2P SSH gives you that kind of precise control. It means you can fix issues, like a device stuck in an automatic repair loop, or retrieve important data, all from your desk. This level of management is really valuable, helping you keep your devices working exactly as they should, which is, like, what everyone wants, right? It's a big part of what makes securely connect remote IoT P2P SSH free so appealing.
What is P2P SSH and How Does It Work for IoT?
So, we've talked about why secure access is so important. Now, let's get into what P2P SSH actually is and why it's a great choice for your IoT devices. It might sound a little technical at first, but it's really about creating a direct, private conversation channel between your computer and your remote gadget, which is pretty neat, if you ask me. This approach helps you securely connect remote IoT P2P SSH free, and it is something many people are finding useful.
Think of it this way: instead of shouting across a crowded room (the internet) and hoping your message gets to the right person without anyone else hearing, P2P SSH sets up a private phone line. Only you and your device have the number, and everything you say is scrambled so no one else can understand it. That, in a nutshell, is the core idea, you know, for keeping things safe.
This method combines two powerful concepts: peer-to-peer networking and the Secure Shell protocol. Together, they offer a robust and often free way to manage your remote devices, which is, like, a big win for anyone with an IoT setup. It's about making sure your digital conversations are private and protected, basically.
Understanding Peer-to-Peer Connections
A peer-to-peer, or P2P, connection is a pretty straightforward idea, actually. Instead of having a central server that all devices talk through, like a post office, P2P means your device talks directly to another device. It's like two friends calling each other directly, rather than going through a switchboard operator, which is, like, more efficient in some ways.
For IoT, this is pretty cool because it can cut out the middleman. You don't always need a big, expensive cloud service to manage your connections. Your laptop, for instance, can talk directly to your Raspberry Pi or your smart sensor. This can make things faster, and sometimes, more reliable, especially if that central server is having a bad day, you know?
This direct link can also be more secure in some respects because there are fewer points where someone could try to intercept your data. When you want to securely connect remote IoT P2P SSH free, this directness is a big part of the appeal. It gives you a more private channel, which is something many people really value, as a matter of fact.
SSH: Your Secure Remote Shell
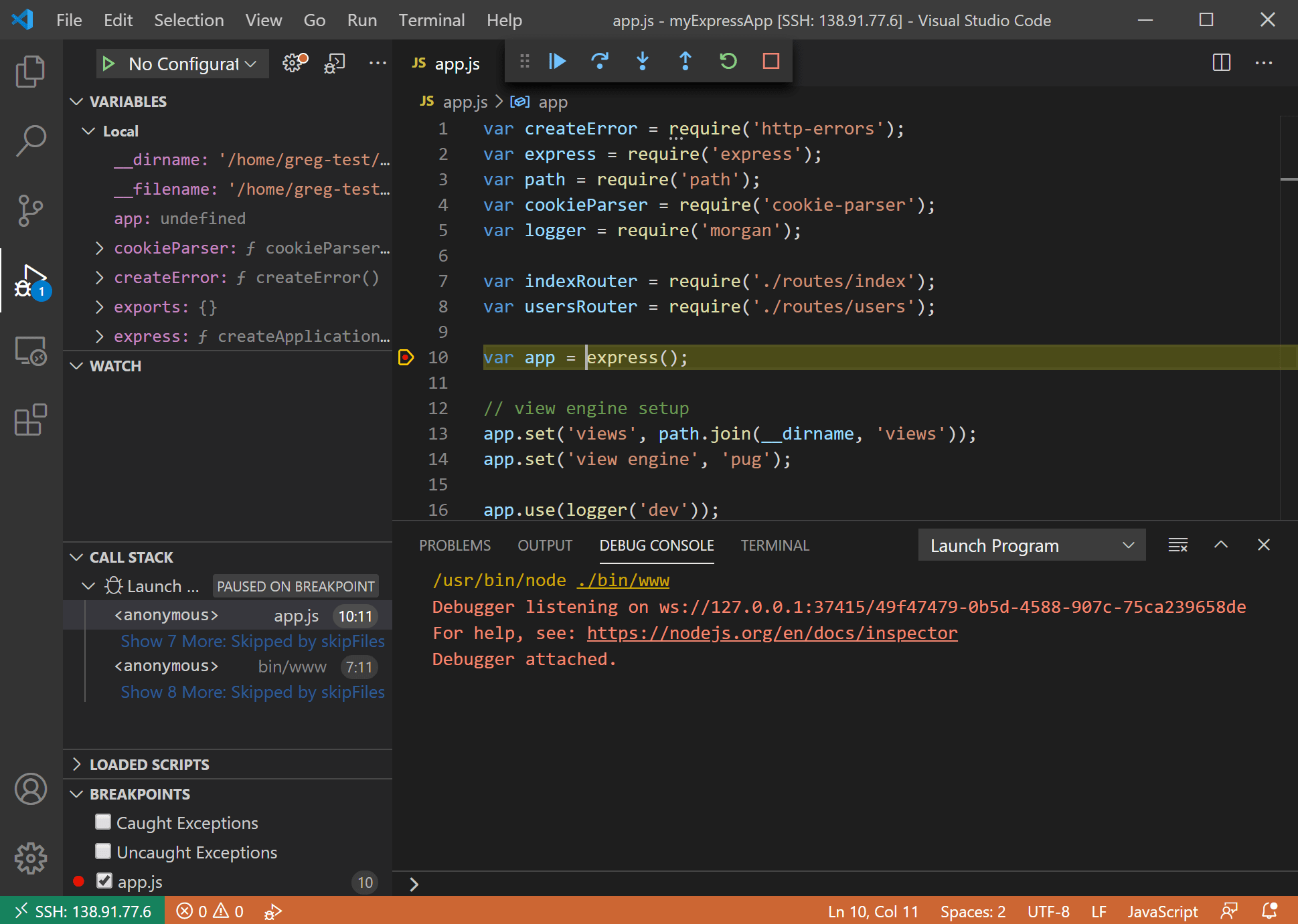
SSH stands for Secure Shell, and it's a way to get a text-based command window on a remote computer, but with strong encryption. Think of it as a super-secure walkie-talkie that lets you type commands to your device from anywhere. It's what people use to manage servers, and it works just as well for little IoT devices, too it's almost.
When you use SSH, all the information going back and forth, like your login details and the commands you send, is scrambled. This means if someone were to somehow intercept the data, they wouldn't be able to read it. It's like sending a secret message in code; only someone with the right key can decode it, you know?
SSH also uses something called public-key cryptography for authentication, which is a bit like having a really fancy lock and key system. Instead of just a password, you use a pair of keys – one public, one private – to prove who you are. This is a much stronger way to verify identity and prevent unauthorized access, which is, like, absolutely crucial when you want to securely connect remote IoT P2P SSH free, honestly.
The P2P SSH Advantage for IoT
Combining P2P with SSH gives you some pretty neat benefits for your IoT setup. First off, it means you can often bypass some of the trickier network configurations, like firewalls or NAT (Network Address Translation), that can make connecting to remote devices a real pain. It's like finding a secret tunnel around a big wall, you know?
Because it's peer-to-peer, you can often avoid relying on third-party services that might cost money or introduce their own security risks. This is a big part of the "free" aspect of securely connect remote IoT P2P SSH free. You are, in a way, taking more control over your own connections, which is a good feeling for many people, basically.
The security of SSH, combined with the directness of P2P, means you get a robust, private, and efficient way to manage your IoT devices. You can be confident that your commands are reaching the right device and that the data coming back is safe. This setup is really powerful for anyone looking to maintain a secure and reliable remote IoT environment, you know, without too much fuss.
Setting Up Your Free P2P SSH Connection for IoT
Alright, so you're probably thinking, "This sounds good, but how do I actually do it?" Setting up your free P2P SSH connection for IoT devices does involve a few steps, but it's totally doable, even if you're not a networking expert. We'll go through the general idea here, and you'll see it's more about understanding the concepts than, like, needing to be a wizard. Many people are successfully able to securely connect remote IoT P2P SSH free, and you can too, honestly.
The main goal is to create a secure tunnel between your local computer and your remote IoT device. This tunnel will use SSH for its security, and the P2P aspect means we're looking for direct ways for them to find each other, even if they're on different networks. It's a bit like setting up a secret handshake and a private meeting spot, you know?
We'll talk about the tools you'll need, how to make those super-secure keys, and the general steps to get that connection going. Remember, the exact commands might vary a little depending on your specific IoT device, like a Raspberry Pi versus something else, but the principles are pretty much the same across the board, in a way.
Essential Tools and Preparations
Before you start, you'll need a few things. First, you'll need your IoT device itself, obviously, and it should be running some form of Linux, like Raspberry Pi OS or a similar system, because SSH is usually built right in. You'll also need a computer to connect *from*, which can be your laptop or desktop, and it should also have an SSH client. Most Linux and macOS systems have it by default, and Windows 10/11 has it built-in too, which is handy, you know?
You'll also need a way for your remote device to, like, "call home" or tell a rendezvous server where it is. This is often done using a small piece of software on your IoT device that helps it establish the P2P part of the connection. There are free services and open-source tools that can help with this, so you don't always need to build your own, which is good, as a matter of fact.
Finally, you'll need a stable internet connection for both your local computer and your IoT device. While P2P tries to be direct, it still needs the internet to initially find each other. Having these basics ready makes the whole process much smoother when you're trying to securely connect remote IoT P2P SSH free, basically.
Generating SSH Keys for Security
Instead of relying on just a password, which can sometimes be guessed or cracked, SSH uses key pairs for much stronger security. You'll generate a pair of keys on your local computer: a public key and a private key. The public key, like your house number, can be shared, but the private key, like your house key, must be kept secret and safe, absolutely.
To create these keys, you'll typically use a command like `ssh-keygen` in your terminal. It will ask you where to save the keys and if you want a passphrase for your private key. Using a passphrase is a really good idea, actually, as it adds another layer of protection, just in case someone gets hold of your private key, you know?
Once you have your key pair, you'll copy the public key to your IoT device. This tells your device, "Hey, if someone tries to connect with the matching private key, let them in." This method is far more secure than just using a password, which is a big part of why you can securely connect remote IoT P2P SSH free with confidence, honestly.
Establishing the P2P Tunnel (Conceptually)
The trickiest part for many people when they want to securely connect remote IoT P2P SSH free is getting the two devices to find each other when they're behind different routers or firewalls. This is where the P2P aspect comes in. It often involves a technique called "hole punching" or using a relay server, at least initially. It's a bit like two people trying to meet up, but they're both in separate, locked rooms, you know?
With "hole punching," both your local computer and your IoT device try to make an outgoing connection to a third, public server. Because they're both initiating connections, their routers temporarily "punch holes" in their firewalls to allow the outgoing traffic. The public server then tells them each other's public IP addresses and ports, and they can then try to connect directly through those temporary holes, which is pretty clever, actually.
If direct hole punching doesn't work, sometimes a relay server is used. This server acts as an intermediary, forwarding traffic between your computer and your IoT device. While it's not strictly P2P in the purest sense, it still allows for a secure SSH connection without needing complex port forwarding on your home router. There are free tools and services that help manage this process, making it much simpler, in a way.
Practical Steps and Considerations
To actually set this up, you'll typically install a P2P SSH client or agent on your IoT device. Projects like ZeroTier, Tailscale, or even some custom scripts can help create that direct, secure network link. These tools often create a virtual network where all your devices, no matter where they are physically, appear to be on the same local network, which is super convenient, you know?
Once that virtual network is up and running, and your IoT device is part of it, you can then use your standard SSH client on your local computer to connect. You'd just use the virtual IP address assigned to your IoT device by the P2P network. It's like your device gets a new, special address that works anywhere, basically.
Remember to configure your IoT device's SSH server properly. Make sure it's set to only allow key-based authentication and disable password logins. This really tightens up security. Also, regularly check for updates for both your IoT device's operating system and any P2P software you're using. Staying current helps keep everything safe and running smoothly, which is, like, a big part of securely connect remote IoT P2P SSH free, honestly.
Common Pitfalls and How to Avoid Them
Even with the best intentions, things can sometimes go a little sideways when you're dealing with remote connections and IoT devices. It's not uncommon to hit a snag or two, like those "connection untrusted" messages we talked about earlier, or maybe a device that just won't update properly. Knowing about these common issues ahead of time can really help you avoid a lot of frustration, you know, when you are trying to securely connect remote IoT P2P SSH free.
One of the biggest worries for many people is just keeping everything working and safe. You want to make sure your devices are protected, your data is private, and that you can always get to them when you need to. So, let's talk about some of these typical problems and some straightforward ways to deal with them, basically.
From dealing with stubborn updates to making sure your data is truly private, there are practical steps you can take. These tips can help you keep your IoT setup running smoothly and securely, which is, like, the whole point, right? It's about making your remote access experience as hassle-free as possible, actually.
Dealing with Update Woes
We've all been there: an update tries to reinstall repeatedly and fails, or it looks like it was already installed, and you're just trying to stop it from reinstalling again. Or maybe your computer gets stuck in an automatic repair loop after an update. These kinds of update problems are, like, really annoying and can leave your remote IoT devices vulnerable, too it's almost.
To avoid this, first, always make sure your device has enough storage space for updates. Sometimes, a lack of space is
- Tyne Daly Net Worth
- Did Will Smith Die Today
- Ryan Merriman Destino Final 1
- Janet Leigh Net Worth
- Tracy Caliendo Nyc Husband

Detail Author:
- Name : Dr. Joseph Johnston
- Username : glowe
- Email : dante.keeling@franecki.org
- Birthdate : 2004-11-24
- Address : 82644 Barbara Hills West Reubenland, NY 65607-4141
- Phone : +1-458-815-2195
- Company : Feest-Ortiz
- Job : Audiologist
- Bio : Distinctio non debitis ut tempore quisquam. Facere omnis facere soluta dolores vero nostrum. Qui incidunt ullam praesentium perferendis. Ad sit ut est labore.
Socials
tiktok:
- url : https://tiktok.com/@hallie795
- username : hallie795
- bio : Beatae quam saepe labore natus.
- followers : 2696
- following : 1076
linkedin:
- url : https://linkedin.com/in/hallie.marquardt
- username : hallie.marquardt
- bio : Dignissimos odit dolorum voluptate quae ab.
- followers : 353
- following : 479
instagram:
- url : https://instagram.com/marquardt2005
- username : marquardt2005
- bio : Eum consectetur quis quae ea sint ipsum. Officia unde et facere iste. Et commodi harum explicabo.
- followers : 178
- following : 2445
facebook:
- url : https://facebook.com/hallie_marquardt
- username : hallie_marquardt
- bio : Repellat et accusamus impedit et sit eos et.
- followers : 406
- following : 2540