Connecting your smart devices from afar, especially when they are tucked away behind your home router, can feel a bit like trying to talk to someone through a thick wall. You want to use your internet-connected gadgets, like smart cameras or sensors, even when you're not at home, but often, the usual ways of setting things up involve fiddling with router settings, maybe even getting into MAC addresses or port forwarding. For many, that just sounds like too much trouble, or perhaps your router does not even allow those kinds of changes. This article will show you how to get those remote IoT connections working smoothly, without needing to dive deep into complex network adjustments you might not have access to or understand, which is a common concern for people these days.
So, you’ve got these cool IoT devices, perhaps a smart thermostat, some security cameras, or even automated lights, and you really want to put them into service from anywhere. The thought of controlling your home's temperature before you arrive, or just checking in on things with a camera, is very appealing. The problem, though, often comes down to how your home network is set up, particularly with your router acting as a kind of gatekeeper, which it typically does.
This guide is for anyone who has ever wondered, "how to use remote iot behind router mac without" the usual headaches. We will look at some clever ways to make your devices talk to you no matter where you are, bypassing those tricky router configurations, because, you know, not everyone is a network wizard, and that is perfectly fine. We aim to help you employ your gadgets to their fullest potential, making your smart home truly smart, even when you're miles away.
Table of Contents
- Understanding the Challenge of Remote IoT Access
- Cloud-Based IoT Platforms: Your Simplest Solution
- Using VPN Services for a Secure Connection
- Reverse Proxies and Tunneling: More Advanced, Yet Effective
- IoT Gateways and Hubs: A Centralized Approach
- Security Considerations for Remote IoT
- Frequently Asked Questions About Remote IoT Access
- Getting Your IoT Devices Connected From Anywhere
Understanding the Challenge of Remote IoT Access
When you try to use your IoT device from outside your home network, you are trying to reach something that is, in a way, hidden. Your router, which is a pretty important piece of equipment, gives all your devices a private address within your home. It then presents one public address to the wider internet, kind of like a single front door for your entire house, so, in some respects, this is why direct connections are tricky.
The internet, you see, does not really know how to find your specific smart bulb among all the other things behind that one public address. This is where things like port forwarding come in, which basically tells the router, "Hey, if someone asks for this specific thing, send them to that specific device." But we are looking for ways to avoid that, because, as I was saying, it can be a bit complicated or just not an option for everyone.
Many people find that their internet service provider (ISP) does not give them a static IP address, meaning their public address changes sometimes. This makes it even harder to reliably find your devices from afar, as you might expect. Also, trying to directly use a device's MAC address, which is its unique hardware identifier, outside your local network is simply not how the internet works, so that is not a practical way to employ your devices remotely.
Cloud-Based IoT Platforms: Your Simplest Solution
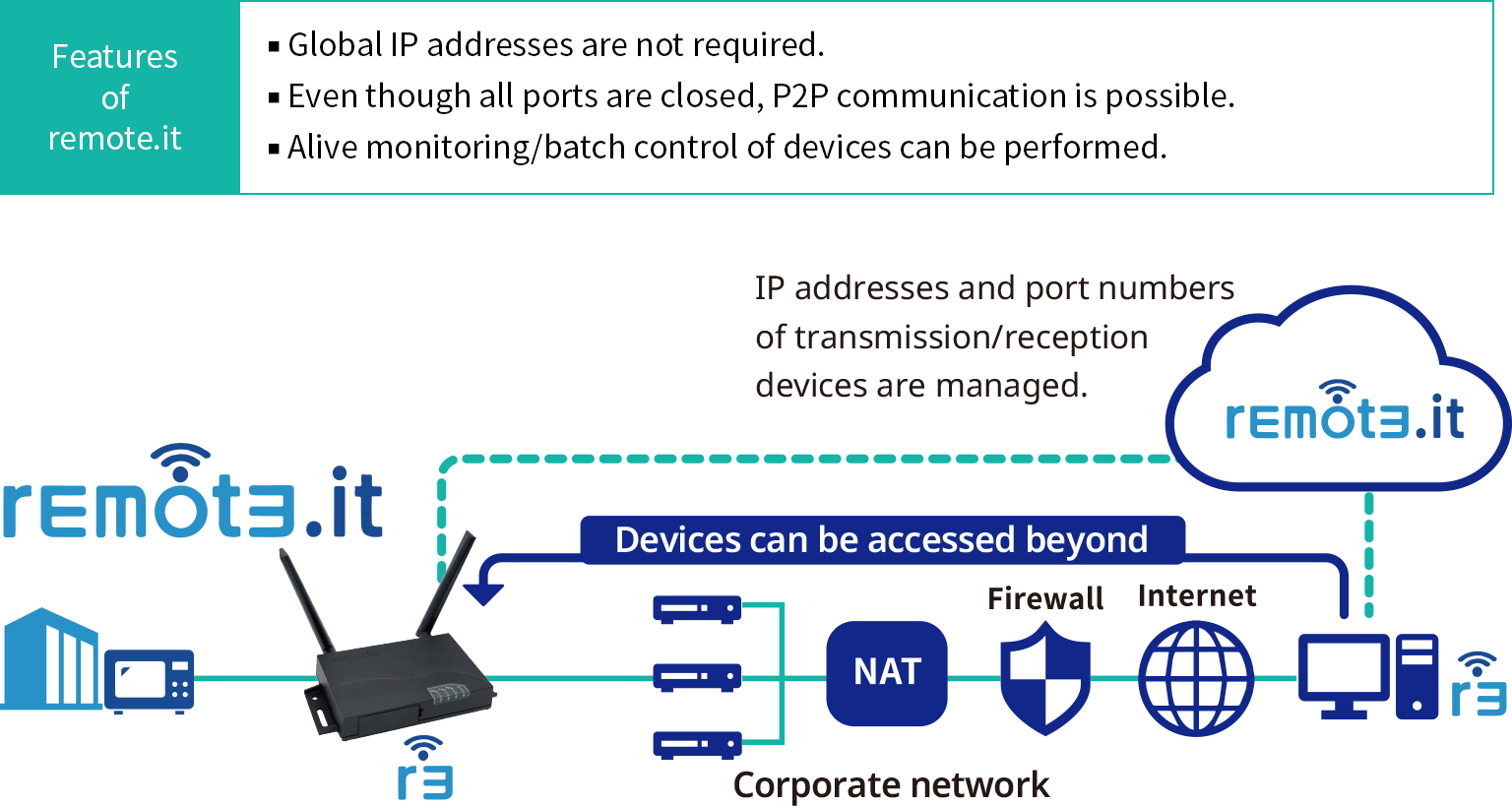
For most folks, using a cloud-based IoT platform is the easiest and most common way to use remote IoT behind a router without needing to mess with MAC addresses or port forwarding. These platforms are basically services that act as a middleman, helping your devices talk to you from anywhere, which is rather convenient.
How They Work
Think of it like this: your IoT device, instead of waiting for you to directly contact it, makes an outgoing connection to a cloud server on the internet. This connection is typically initiated by the device itself, so it goes right past your router's usual protections, because it's going *out* not *in*. When you want to control your device, you simply use an app on your phone or a web interface, which then talks to that same cloud server, and the server relays your commands to your device, which is pretty clever, you know.
This method works because most routers allow outgoing connections by default, which is very common. The device "phones home" to the cloud, and you "phone home" to the cloud, and the cloud connects you both. It is a bit like leaving a message with a central operator who then passes it along, so, arguably, it makes things much simpler.
Popular Examples
Many popular smart home brands already use this model. Devices from companies like Google Nest, Amazon Alexa-enabled gadgets, Philips Hue lighting, and even many smart plugs or cameras rely on their own cloud services. When you set up these devices, you typically link them to an account with the manufacturer, and that account is what handles the remote access, which is usually quite straightforward.
For those who like to build their own IoT projects, platforms like Adafruit IO, Particle.io, or even services like AWS IoT Core or Google Cloud IoT Core offer similar functionality. They provide the infrastructure for your custom devices to connect and be controlled remotely, allowing you to utilize your creations from anywhere, which is very cool for makers.
Advantages and Things to Think About
The biggest plus here is how simple it is; you usually do not have to touch your router settings at all, which is a huge relief for many. These services also often handle security, updates, and reliability for you, which is great. However, you are relying on a third-party service, so privacy and data handling are things to consider, and you should always check their policies, as a matter of fact.
Sometimes, if the internet connection to the cloud service goes down, your remote control might stop working, which can be a bit annoying. But for general ease of use and getting around router limitations, this approach is often the best way to employ your remote IoT devices, especially if you just want things to work without a lot of fuss.
Using VPN Services for a Secure Connection
Another powerful way to use remote IoT behind a router without direct MAC address or port forwarding adjustments is to set up a Virtual Private Network (VPN). A VPN creates a secure, encrypted tunnel between your remote device (like your phone or laptop) and your home network, making it seem as if you are actually inside your home, which is pretty neat.
Setting Up a VPN Server at Home
Some advanced routers actually have a built-in VPN server feature. If your router has this, you can turn it on and then connect to it from anywhere using a VPN client on your phone or computer. Once connected, you are virtually part of your home network, and you can then access your IoT devices as if you were sitting right there, which is a very secure way to operate.
If your router does not offer a VPN server, you could employ a dedicated device, like a Raspberry Pi, to act as a VPN server on your home network. Software like OpenVPN or WireGuard can be set up on these small computers. This usually requires a bit more technical know-how to configure, but it gives you a lot of control and security, so it is a good option for those who like to tinker a little.
The main challenge with a home VPN server is that you still need a way for your remote device to find your home network's public IP address, especially if it changes. Dynamic DNS (DDNS) services can help here, by giving your changing home IP a consistent name, which is something you might want to look into. Even with DDNS, you might still need to forward a single port for the VPN server, but it's just one port, not many for each IoT device, which is a slight difference.
Using a Commercial VPN with IoT
This approach is a bit different. While commercial VPNs are great for protecting your privacy and security when you are browsing the internet, they typically do not help you directly access your home IoT devices from outside. This is because a commercial VPN connects you to *their* servers, not directly to your home network, so, in a way, it is not quite the same thing.
However, if your IoT device itself supports connecting to a VPN (which is rare for most consumer gadgets), or if you have a router that can run a VPN client and route all your home traffic through it, then your IoT devices would appear to be coming from the VPN server's location. This is generally used for privacy or bypassing geo-restrictions for the IoT device itself, not for remote access *to* the device, which is a key distinction.
Reverse Proxies and Tunneling: More Advanced, Yet Effective
For those who are a bit more comfortable with technical setups, reverse proxies and tunneling services offer another way to use remote IoT behind a router without direct MAC address fiddling. These methods create a pathway through your router, much like the cloud services, but they give you more control, which is often preferred by developers or advanced users.
Ngrok and Similar Services
Services like Ngrok, or alternatives like Cloudflare Tunnel (formerly Argo Tunnel), are pretty clever. You install a small client application on a computer or a Raspberry Pi within your home network. This client then creates a secure, outgoing tunnel to the service's servers. The service then gives you a public URL that points to this tunnel, so, basically, anyone on the internet can use that URL to access your device or service running at home, which is quite powerful.
This means your router sees only an outgoing connection from your local computer to the Ngrok server, which is usually allowed. When someone accesses the public URL, Ngrok routes that request through the tunnel back to your local computer, and then to your IoT device. It is a fantastic way to expose a local web server or an IoT device's interface to the internet without any port forwarding, which is very useful for testing or specific applications.
These services often come with free tiers that are good for basic use, and paid tiers for more features like custom domains or increased bandwidth. They are excellent for temporary access or for projects where you need to showcase something running on your local network, which is often the case for developers, you know.
SSH Tunnels for Specific Needs
If you have a computer on your home network that you can access via SSH (Secure Shell), you can set up what is called an SSH reverse tunnel. This is a bit more manual and typically requires a publicly accessible server somewhere else (a cheap VPS, for instance) to act as a go-between. The computer at home initiates an SSH connection to the public server and "tunnels" a local port to a port on the public server, which is a rather technical way to put it.
Then, when you are away, you can connect to that public server, and through the SSH tunnel, you can access your home IoT device. This method is very secure and gives you a lot of control, but it does require a good grasp of command-line interfaces and server administration. It is probably not for the casual user, but for those with specific needs or a desire for deep control, it is a robust solution to employ.
IoT Gateways and Hubs: A Centralized Approach
Many smart home ecosystems use a central hub or gateway device. These devices are specifically designed to manage all your various IoT gadgets locally and then provide a single point of remote access, which is quite convenient. Brands like SmartThings, Hubitat, or Home Assistant (when running on a dedicated device) are examples of this.
The hub itself often uses a cloud-based connection (similar to what we discussed earlier) to allow you to control your devices remotely. So, instead of each individual smart bulb or sensor needing its own remote access method, the hub handles all of that. You simply connect to the hub's cloud service, and it then relays your commands to the devices connected to it within your home, which is a very efficient way to operate.
This approach simplifies things greatly because you only have one device (the hub) that needs to establish remote connectivity. It often means better local control and sometimes even allows for local automation to continue working even if your internet goes down, which is a big plus. If you are building a comprehensive smart home, a good hub is almost always a part of the setup you will want to use.
Security Considerations for Remote IoT
No matter which method you choose to use to access your remote IoT devices, security should always be a top priority, very much so. Opening up your home network, even indirectly, always comes with some risks. Here are a few things to keep in mind, as a matter of fact.
Strong Passwords: This might seem obvious, but it is incredibly important. Use long, complex, unique passwords for all your IoT devices, cloud accounts, and router access. Frankly, a password manager can really help with this.
Two-Factor Authentication (2FA): Wherever it is available, enable 2FA on your cloud accounts for IoT services. This adds an extra layer of protection, usually requiring a code from your phone in addition to your password, which is a very good idea.
Keep Software Updated: Make sure your IoT devices, hubs, routers, and any software you use for remote access are always up to date. Updates often include critical security fixes, which is why they are so important.
Network Segmentation: If you are feeling a bit more advanced, consider putting your IoT devices on a separate network (a "guest" network or a dedicated VLAN) if your router supports it. This way, if an IoT device were to be compromised, it would be harder for attackers to reach your main computers and personal data, which is a smart move.
Use Secure Connections: Always make sure you are using encrypted connections (HTTPS, VPNs, SSH tunnels) when accessing your devices remotely. Avoid any methods that transmit data in plain text, which is a huge security risk, really.
Limit Access: Only give remote access to what you absolutely need. If a device does not require remote access, do not enable it. Less exposure means less risk, which is a simple truth.
For more general tips on keeping your smart home secure, you might want to learn more about IoT security best practices on our site, which is a good resource. It is really about being mindful and taking reasonable steps to protect your digital home, because, you know, your privacy and security are worth it.
Frequently Asked Questions About Remote IoT Access
How can I access my IoT devices remotely without opening ports?
You can use cloud-based IoT platforms, which allow your devices to connect outwards to a server, then you connect to that same server. Services like Ngrok or Cloudflare Tunnel also create secure outgoing tunnels. These methods typically bypass the need for port forwarding entirely, which is very helpful for many people.
What are the most secure ways to connect to IoT devices from outside my home network?
Using a VPN server set up on your home router or a dedicated device like a Raspberry Pi is arguably one of the most secure ways. Cloud-based platforms from reputable manufacturers also offer good security, as they handle encryption and authentication. Always use strong passwords and two-factor authentication, too, for any method you employ.
Do I need a static IP address to control my smart home gadgets when I'm away?
Not necessarily. While a static IP makes some direct connection methods easier, many solutions, like cloud-based platforms and tunneling services, work perfectly fine with dynamic IP addresses. If you set up your own home VPN server, a Dynamic DNS (DDNS) service can help you use a consistent name even if your IP address changes, which is a very common solution.
Getting Your IoT Devices Connected From Anywhere
Connecting your IoT devices remotely without the fuss of MAC address configurations or extensive router changes is very much within reach for almost anyone. Whether you opt for the simplicity of cloud-based platforms, the robust security of a VPN, or the flexibility of tunneling services, there is a method that will suit your comfort level and technical skills, which is really good news.
The key is to understand how these different approaches work and to pick the one that best fits your specific needs and devices. Remember to always prioritize security, no matter which path you choose, because, you know, keeping your digital home safe is just as important as making it smart. By employing these strategies, you can truly use your smart home to its full potential, enjoying the convenience and control it offers from wherever you are, which is the whole point, really. You can also find more information about general IoT security guidance from government resources, which is a good external reference.
And for more tips on setting up your smart home, be sure to link to this page here.
- Bryce Dickey Elko Nv
- Shaira Diaz Parents
- Kirsten Dunst Nude Pictures
- Isnotmena Of Leaks
- Queenpussybossv Only Fans

Detail Author:
- Name : Terrance Legros
- Username : hassan34
- Email : cchamplin@gmail.com
- Birthdate : 2004-05-13
- Address : 65402 Selina Spur Abigaleland, TX 80900
- Phone : 1-716-459-3936
- Company : Crooks Inc
- Job : Production Planning
- Bio : Voluptates quia libero perferendis culpa hic accusantium in. Eveniet doloribus tenetur et est.
Socials
linkedin:
- url : https://linkedin.com/in/rafael_xx
- username : rafael_xx
- bio : Minus sed et similique hic.
- followers : 5157
- following : 1030
instagram:
- url : https://instagram.com/feeney2001
- username : feeney2001
- bio : Quia consequatur magni quod. Nihil nihil a excepturi.
- followers : 520
- following : 2206