It's a big world out there, and our gadgets, often called IoT devices, are everywhere. From smart home sensors to industrial equipment, these little helpers make our lives, well, just a little bit easier. Yet, as we bring more things online, the question of how to keep them safe, especially when you need to check on them from afar, becomes a really important one. It's kind of like that feeling you get when your computer warns, "Your device is at risk because it's out of date and missing important security and quality updates," except now, it's about all your connected devices.
You see, getting to your remote IoT devices, like that weather station in your garden or a security camera at a distant property, can sometimes feel like a tricky puzzle. You might worry about who else could be looking in, or if your connection is truly private. This concern is very much like encountering a message saying, "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." Nobody wants that kind of uncertainty, especially when it comes to the things running our homes or businesses.
That's where a smart solution comes in, one that lets you talk directly and safely to your IoT gadgets using just your Android phone. We're talking about Peer-to-Peer (P2P) SSH, which is a bit like creating a secret, protected pathway straight from your phone to your device. It’s a pretty neat way, actually, to make sure your commands and data stay private, giving you peace of mind and, you know, control. So, let's explore how you can make this happen, starting right now.
- Nick Hogan Net Worth
- Allen Covert Net Worth
- Urbabydollxo Onlyfans Leaked
- Jade Love 123 Nude
- Jackson Yearby
Table of Contents
- Why Secure Remote Access for IoT is a Big Deal
- What is P2P SSH and Why It's Your IoT's Best Friend
- Getting Started: Preparing Your IoT Device for SSH
- Your Android Phone as a Command Center: Tools for P2P SSH
- Step-by-Step Guide: Connecting Securely from Android
- Best Practices for Keeping Your IoT Connections Safe
- Common Challenges and Quick Fixes
- Frequently Asked Questions About Secure IoT P2P SSH on Android
- Conclusion: Taking Control of Your Remote IoT
Why Secure Remote Access for IoT is a Big Deal
Having a way to reach your IoT devices from anywhere is, you know, pretty convenient. Whether you're checking on your home's temperature while away or adjusting settings on a smart garden watering system, remote access offers a lot of flexibility. However, this convenience does come with its own set of concerns, very much like how a computer that's "out of date and missing important security and quality updates" might feel vulnerable. You really want to make sure that only you, or people you trust, can get to these devices.
The digital landscape, it's fair to say, is always changing, and with more devices getting connected, the need for robust security measures grows too. If you've ever had the frustration of an "update that keeps trying to reinstall and fails," you understand how important it is for systems to work correctly and safely. For IoT, an unsecured connection is a bit like leaving your front door wide open, which is, well, not ideal for anyone.
The Pitfalls of Open Connections
When an IoT device is connected to the internet without proper security, it can, in a way, become a target. Unprotected connections are, quite frankly, a playground for those with less-than-good intentions. This can lead to all sorts of problems, from someone messing with your device's settings to, even worse, gaining access to your personal information or using your device as a stepping stone to other parts of your network. It's a bit like having "a problem connecting securely to this website," but on a much wider scale, affecting physical gadgets.
- Raspberry Pi Remoteiot App Download
- Alice Rosenblum Leaks
- Trent Richardson Net Worth
- Toby Dorr Ex Husband
- Tequan Richmond Net Worth
Data breaches are a serious concern, too. Many IoT devices collect information, whether it's about your energy usage, daily routines, or even sensitive health data. If this information isn't sent over a secure pathway, it could be intercepted. This is why, you know, we often see warnings like "This connection is untrusted you have asked firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure." You really want to avoid that kind of risk for your personal devices, or even for your organization's systems, like when you're "assisting creating transport rules to lock down my organizations o365 tenant."
What is P2P SSH and Why It's Your IoT's Best Friend
So, let's talk about P2P SSH. P2P, or Peer-to-Peer, simply means your Android phone connects directly to your IoT device, more or less bypassing central servers that could, you know, be another point of vulnerability. It's a bit like two friends talking directly, without a middleman. SSH, on the other hand, stands for Secure Shell. It's a protocol, or a set of rules, that provides a really strong, encrypted connection between two devices. Think of it as a super-secret, armored tunnel for your data.
When you put P2P and SSH together, you get a direct, highly protected way to manage your remote IoT devices. This method helps to make sure that whatever you send or receive from your device is kept private and safe from prying eyes. It's a very effective way, actually, to avoid those "untrusted connection" warnings you might get with less secure methods. This approach gives you, the user, a lot more confidence in your remote interactions.
How P2P SSH Makes a Difference
The main thing P2P SSH does is create a direct, encrypted link. This means that all the information traveling between your Android phone and your IoT device is scrambled, making it, you know, unreadable to anyone who might try to intercept it. It's a bit like sending a coded message that only the intended recipient has the key to decipher. This encryption is a really big deal for security, as it protects your commands, data, and device status.
Another benefit is strong authentication. SSH doesn't just rely on passwords; it can use something called key-based authentication. This is where you have a unique digital key on your Android phone and a matching lock on your IoT device. Only if the keys match can a connection be made. This is, arguably, much more secure than just a password, which could, you know, be guessed or stolen. It's a proactive step to prevent unauthorized access, ensuring that only you can control your devices, which is pretty important.
Getting Started: Preparing Your IoT Device for SSH
Before you can start connecting from your Android phone, your IoT device needs a little bit of preparation. Most modern IoT devices, especially those running Linux-based operating systems like Raspberry Pis or certain smart hubs, usually have SSH capabilities built in, or they can be added. The first step is typically to make sure SSH is actually enabled on your device. This might involve going into its settings or configuration files, which is, you know, sometimes a bit of a process.
Once SSH is enabled, you'll want to set up proper user accounts. It's a good idea to create a dedicated user for remote access, rather than using a default "admin" account. And, very importantly, make sure this user has a strong, unique password. We've all, you know, heard about the risks of weak passwords, and for IoT, it's no different. This initial setup is crucial for laying a secure foundation, so take your time with it.
Essential IoT Device Setup Steps
Beyond enabling SSH and setting up user accounts, there are a few other things to consider. First, always make sure your IoT device's firmware and software are up to date. Just like when you encounter an "update that keeps trying to reinstall and fails" on your computer, outdated software on an IoT device can leave it open to known vulnerabilities. Keeping things current is, you know, a basic but very effective security measure.
Next, think about network configuration. Your IoT device needs to be accessible on your local network, and you might need to configure your router to allow incoming SSH connections if you're connecting from outside your home network. This often involves setting up port forwarding, but for true P2P, some solutions might use clever tricks to bypass direct port forwarding. It's a bit like making sure all the roads to your house are clear, but also that only authorized vehicles can use them, which is, you know, a good way to think about it.
Your Android Phone as a Command Center: Tools for P2P SSH
Your Android phone, in a way, becomes your portable control panel for your IoT devices. To make this happen, you'll need a good SSH client app. The Google Play Store offers quite a few options, each with its own set of features and user interface. Choosing the right one can make a big difference in how easy and pleasant your remote management experience is, so, you know, it's worth looking around a bit.
When picking an app, look for features like support for key-based authentication, which is, as we talked about, much more secure than just passwords. Also, consider apps that allow you to save connection profiles, so you don't have to type in all the details every time. A clean, easy-to-use interface is also, you know, a definite plus, especially if you're going to be using it often. Some apps even offer extra features like built-in SFTP for file transfers, which can be very handy.
Top Android SSH Client Apps to Consider
There are several well-regarded SSH client apps available for Android. For example, Termius is a very popular choice, offering a clean interface, support for key-based authentication, and even cloud synchronization of your connections across devices. JuiceSSH is another strong contender, known for its extensive feature set and customization options. ConnectBot, too, is a long-standing open-source option that many people find reliable. Each of these, in their own way, provides a solid foundation for secure remote access.
When you download one of these apps, you're essentially getting the software that will allow your phone to "speak" SSH to your IoT devices. It's a bit like downloading a new browser when "I have tried multiple platforms (ms edge, firefox, chrome etc) and to no avail" with a particular website. You're trying a different tool to get the job done, and in this case, a secure one. Make sure to download from the official Google Play Store to avoid any, you know, unwanted surprises or security risks.
Step-by-Step Guide: Connecting Securely from Android
Alright, so you've got your IoT device ready and your SSH client app installed on your Android phone. Now for the fun part: making that secure connection. The exact steps might vary a little depending on the app you chose, but the general process is pretty much the same. First, you'll open your SSH client app and look for an option to add a new connection or host. This is where you'll put in the details of your IoT device.
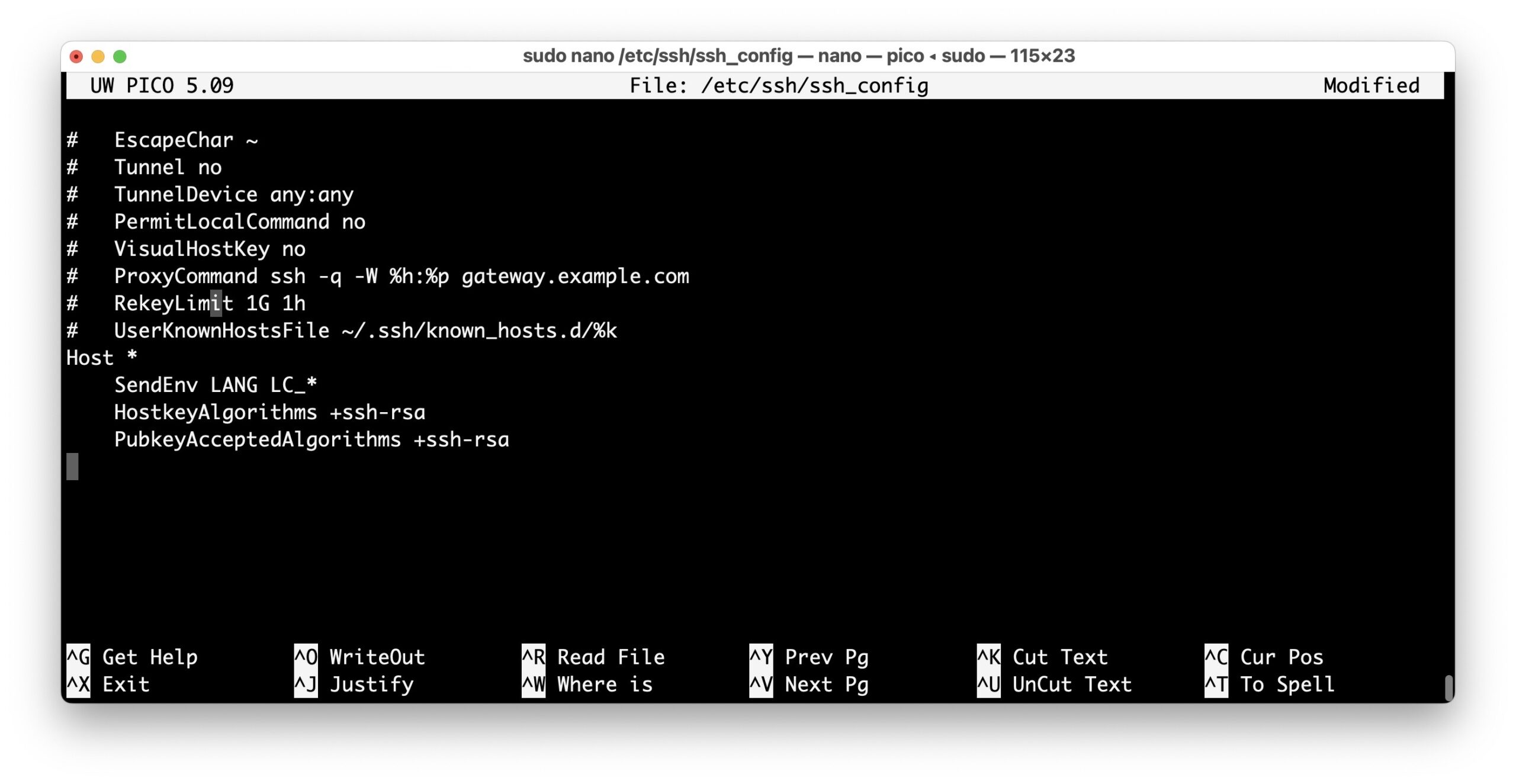
You'll need the IP address of your IoT device on your network, the SSH port (usually 22, but it's often a good idea to change it for better security), and the username you set up earlier. Then, you'll configure the authentication method. This is where you can choose to use a password or, even better, set up key-based authentication. If you go with keys, you'll generate a key pair (a public key for your IoT device and a private key for your phone) and import them into the app. This is, you know, a really important step for strong security.
The Initial Connection: What to Expect
When you try to connect for the very first time, your SSH client app will likely ask you to verify the host's fingerprint. This is a unique identifier for your IoT device, and it's a critical security check. It's very much like when you see a warning that "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." With SSH, you get a chance to confirm that you're truly connecting to your device and not, you know, some imposter.
Once you confirm the fingerprint, and if your authentication details are correct, you should see a command prompt from your IoT device. Congratulations! You're now securely connected. If you run into issues, like "I seem to be having the same problem" with connection failures, double-check your IP address, port number, username, and especially your authentication keys or password. Sometimes, a small typo can, you know, really mess things up. It's all about getting those details just right.
Best Practices for Keeping Your IoT Connections Safe
Setting up a secure P2P SSH connection is a fantastic start, but keeping it safe is an ongoing effort. Just like how you might need to "lock down my organizations o365 tenant to only allow mail from our third party email threat protection platform's ip's," your IoT devices also benefit from continuous vigilance. Regular updates for both your IoT devices and your Android SSH client app are, you know, incredibly important. These updates often include security patches that fix newly discovered vulnerabilities.
Always use strong, unique passwords for your IoT device accounts, even if you're primarily using key-based authentication. Think of them as a backup layer of security. If your device supports two-factor authentication (2FA) for SSH, absolutely enable it. This adds another layer of protection, usually requiring a code from a separate device in addition to your password or key. Limiting access, too, is a smart move. Only give SSH access to the specific users who truly need it, and remove access when it's no longer required. It's all about minimizing potential entry points.
Staying Ahead of Potential Risks
Monitoring your IoT device's logs can also be very helpful. Most devices keep a record of who has tried to connect and when. Regularly checking these logs can alert you to any unusual activity, which is, you know, a good early warning system. Consider network segmentation as well, if your home network allows it. This means putting your IoT devices on a separate network segment from your main computers and phones. If one IoT device were to be compromised, it would be harder for an attacker to reach your more sensitive devices, which is, you know, a rather smart way to contain potential problems.
Finally, always be cautious about where you download software, whether it's for your IoT device or your Android SSH client. Stick to official app stores and trusted developers. This helps to prevent installing malicious software that could, you know, compromise your security from the get-go. Staying informed about general IoT security news can also help you anticipate and address new threats before they become a problem, which is, you know, just being prepared.
Common Challenges and Quick Fixes
Even with the best preparation, you might, you know, run into a snag or two when trying to connect. It's a bit like when your computer gets "stuck in this automatic repair loop" after an update; sometimes things just don't go as smoothly as you'd hope. Connection failures are pretty common. This could be due to a simple typo in the IP address or port number, or perhaps your IoT device isn't actually online or reachable on the network. Always double-check these basic details first, as they're often the culprits.
Authentication issues are another frequent hurdle. Maybe your password is wrong, or your SSH keys aren't set up correctly. If you're using key-based authentication, make sure the public key is correctly installed on your IoT device and the private key is properly loaded into your Android SSH client. Sometimes, the permissions on the key files on your IoT device can be incorrect, preventing the SSH server from reading them. It's a bit like when "Legitimate email is being blocked by outlook (meaning not delivered even to junk email folder)"; sometimes the system just needs a little adjustment to let the right things through.
When Things Don't Go as Planned
If you're facing persistent connection problems, it can feel, you know, a bit frustrating, very much like when "I do not have any other option when this comes on my" screen. Start by checking your network settings on both your Android phone and your IoT device. Is your IoT device connected to the internet or your local network? Can you ping its IP address from another device on the same network? Sometimes, a simple restart of the IoT device or your router can resolve temporary network glitches.
For authentication problems, try logging in with a password if you've set one up, just to confirm that the username is correct. If that works, then you know the issue lies with your SSH keys. Review the steps for generating and installing SSH keys very carefully. It's a process that needs precision, and even a small mistake can, you know, prevent a successful connection. There are many online guides for troubleshooting SSH, so don't hesitate to look up specific error messages you might be seeing.
Frequently Asked Questions About Secure IoT P2P SSH on Android
1. Can I use P2P SSH to connect to any IoT device?
Not every IoT device supports SSH directly. Devices running operating systems like Linux (e.g., Raspberry Pi, certain smart hubs) typically do. Simpler, more closed-system devices (like some smart plugs or light bulbs) might not. You'll need to check your specific device's documentation to see if SSH access is, you know, an available feature.
2. Is P2P SSH truly secure?
Yes, SSH is considered a very secure protocol when implemented correctly. It uses strong encryption and authentication methods. The "P2P" aspect means you're often creating a direct, encrypted tunnel, which can reduce reliance on third-party servers. However, its security also depends on you using strong passwords, key-based authentication, and keeping your software updated, which is, you know, pretty important.
3. Do I need a static IP address for my IoT device to use P2P SSH?
A static IP address for your IoT device can make direct connections easier, especially if you're setting up port forwarding on your router. However, there are also dynamic DNS services that can help you reach devices with changing IP addresses. For true P2P solutions, some services can help establish connections without needing a fixed IP or complex router setup, which is, you know, quite convenient.
Conclusion: Taking Control of Your Remote IoT
Being able to securely connect to your remote IoT devices from your Android phone using P2P SSH is, you know, a real game-changer for control and peace of mind. We've talked about why secure access matters, much like avoiding those "untrusted connection" warnings on your browser. We've also covered what P2P SSH is and how it creates a private, encrypted pathway, helping you manage your gadgets without unnecessary risks. From preparing your IoT device with updates and strong credentials to choosing the right Android app and following best practices, you now have a solid roadmap.
Remember, the digital world, it's fair to say, keeps moving forward, and keeping your devices safe is an ongoing task. By taking these steps, you're not just connecting; you're connecting responsibly and securely. Learn more about secure remote access on our site, and link to this page for more IoT security tips. So, why not start exploring these options today and take full control of your remote IoT world?


Detail Author:
- Name : Davonte Bartoletti
- Username : antonette.kulas
- Email : beer.oceane@ratke.org
- Birthdate : 1979-05-30
- Address : 75530 Desiree Harbor Apt. 417 North Jackelinefurt, NJ 94158-8254
- Phone : 314-946-9106
- Company : Morar-Batz
- Job : Electronic Equipment Assembler
- Bio : Sit et nobis facilis eos maiores. Illo qui qui ut nemo vel et amet. In qui voluptatibus non mollitia architecto velit tempore. Molestiae qui culpa necessitatibus nihil dolor laboriosam.
Socials
linkedin:
- url : https://linkedin.com/in/bauchb
- username : bauchb
- bio : Sit ut error totam accusamus veritatis.
- followers : 3098
- following : 1040
facebook:
- url : https://facebook.com/bradford.bauch
- username : bradford.bauch
- bio : Vel aut veritatis recusandae odio distinctio eos.
- followers : 6365
- following : 76