Imagine controlling your smart devices, checking on sensors, or even running small programs on your Raspberry Pi, all while you are away from home. This kind of freedom, you know, makes a huge difference for anyone with IoT projects. Getting your Raspberry Pi to talk to you from across town, or even another country, really opens up a world of possibilities for your smart home or personal projects.
For many folks, the idea of managing their Raspberry Pi-powered gadgets remotely sounds like a big task. There are often worries about security, or maybe thinking it will cost too much money. But, actually, there is a way to do this that is both safe and, very importantly, free. It means you can keep an eye on things, or make changes, without being right there next to your device.
This guide will show you how to set up secure remote access for your Raspberry Pi IoT projects using SSH. We will look at how this method keeps your connections private and how you can get it working, basically, from anywhere. We will cover the steps to get you connected and, really, feeling good about your setup, so you can manage your little computers with peace of mind.
- Tana Mongeau Leaked
- Shanin Blake Onlyfans Leaked
- Marc Mezvinsky Net Worth
- Bryce Adams Onlyfans Leaks
- Alice Rosenblum Leaks
Table of Contents
- What is SSH and Why it Matters for IoT?
- Getting Your Raspberry Pi Ready for Remote Access
- Connecting to Your Raspberry Pi from Anywhere
- Securing Your Remote IoT Connection
- Troubleshooting Common SSH Issues
- Frequently Asked Questions
- Take Control of Your IoT Projects
What is SSH and Why it Matters for IoT?
When we talk about controlling devices from afar, security is, like, a big deal. You wouldn't want just anyone to mess with your smart home gadgets, would you? That is where SSH comes into the picture, providing a safe way to connect to your Raspberry Pi, no matter where you are.
The Basics of SSH
SSH stands for Secure Shell, and it is a way to get into a computer over an unsecured network, but in a very secure way. It means you can send commands, move files, and even run programs on your Raspberry Pi as if you were sitting right in front of it, just using your keyboard. You can, for instance, use various ssh commands, with special values for different options, to get exactly what you need done. This tool, you know, makes remote work possible for many.
It is a client-server type of thing, where your computer (the client) talks to your Raspberry Pi (the server). The connection between them is encrypted, so nobody can snoop on what you are doing. This encryption is, actually, a key part of why it is so trusted for sensitive tasks.
- Cheryl Tiegs Net Worth
- Remoteiot Device Connect Software Download
- Moroccan Cutie
- Daniel Powter Net Worth
- Matthew Koma Net Worth
SSH's Roots and Security
The original free version of SSH was created by Tatu Ylonen, and then the OpenBSD project further developed it. This history means it has a solid foundation, built by people who really care about making things secure. SSH is, basically, a leading defensive cybersecurity tool that keeps communications safe between people, computer systems, and networks.
It specializes in something called zero trust privileged access controls, which is a fancy way of saying it is very strict about who gets to do what. According to Miikka Sainio, who is the CTO at SSH, organizations really need to get ready for attacks that mix technical cleverness with psychological tricks. SSH helps protect against those kinds of threats. Eduardo Giancristofaro, a channel development manager (OT) at SSH Communications Security, explains that several key topics are covered, including access control, which is, obviously, super important.
Why Raspberry Pi and IoT Need SSH
Raspberry Pis are often used for IoT projects, like smart thermostats, security cameras, or weather stations. These devices, you know, might be tucked away in places where it is not easy to connect a monitor and keyboard. So, having a way to manage them remotely is pretty much essential. SSH gives you that ability, letting you update software, check sensor readings, or restart a service without having to physically touch the Pi.
Without SSH, managing your IoT devices would be, frankly, a lot harder and less secure. You might have to use less protected methods, or always be near the device, which defeats the purpose of "Internet of Things." SSH, in a way, brings the internet to your things securely.
Getting Your Raspberry Pi Ready for Remote Access
Before you can connect to your Raspberry Pi from anywhere, you need to get it set up correctly. This involves a few steps to make sure SSH is enabled and your Pi is ready to accept connections. It is not too hard, honestly, and makes all the difference.
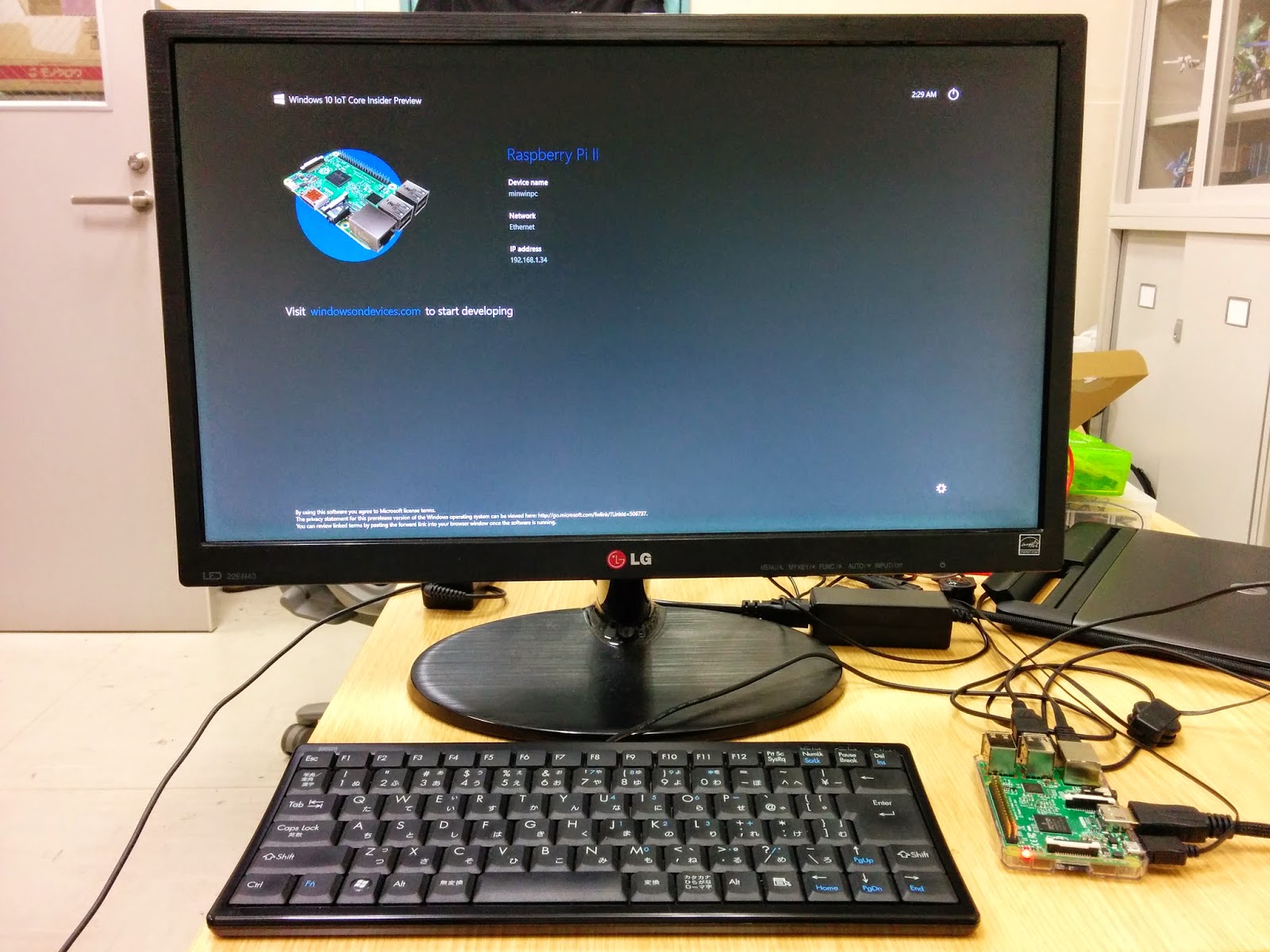
Initial Raspberry Pi Setup
First things first, you need to have your Raspberry Pi running with an operating system like Raspberry Pi OS. Make sure it is connected to your local network, either with an Ethernet cable or Wi-Fi. It is a good idea to update your system's software, too, just to make sure everything is current. You can do this with a couple of commands in the terminal: sudo apt update and then sudo apt full-upgrade. This, you know, gets you started on the right foot.
After updating, it is a good habit to reboot your Pi. Just type sudo reboot and wait for it to come back online. This ensures all updates are applied properly, and, really, gives you a fresh start for the next steps.
Enabling SSH on Your Pi
By default, SSH might not be turned on with some Raspberry Pi OS versions. You can enable it in a few ways. The easiest way is using the Raspberry Pi Configuration tool, which you can find in the graphical interface under "Preferences." Go to the "Interfaces" tab and make sure "SSH" is set to "Enabled."
If you are using a headless setup (without a screen), you can enable SSH by creating an empty file named ssh (no file extension) in the boot partition of your SD card. When the Pi starts up, it will see this file and turn on SSH automatically. This method is, actually, quite handy for initial setup.
Another way to enable it from the command line is to type sudo systemctl enable ssh and then sudo systemctl start ssh. This gets the SSH service running right away. You can check its status with sudo systemctl status ssh to make sure it is active, and, really, ready to go.
Basic Network Configuration
For remote access, it is helpful to know your Raspberry Pi's IP address. You can find this by typing hostname -I in the terminal on your Pi. It will show you a number like `192.168.1.100`. This address is what you will use to connect to your Pi from within your home network.
It is often a good idea to set a static IP address for your Raspberry Pi. This means its IP address won't change every time it restarts, which can make remote connections much more reliable. You can usually do this in your router's settings, or, alternatively, by editing network configuration files on the Pi itself. This, in some respects, simplifies things a lot.
Make sure your Pi is on the same network as the computer you are trying to connect from, at least for the initial setup. This local connection is, basically, your first test to ensure SSH is working correctly before trying to connect from further away.
Connecting to Your Raspberry Pi from Anywhere
Connecting from your local network is one thing, but reaching your Raspberry Pi from anywhere in the world is where the real magic happens. This involves a few more steps, as home networks are usually set up to keep outside connections out.
Understanding Network Challenges
Most home internet connections use something called NAT (Network Address Translation). This means your router has one public IP address, but all your devices inside your home have private IP addresses. Your router, in a way, acts as a bouncer, letting traffic out but not letting unsolicited traffic in.
To connect to your Raspberry Pi from outside your home network, you need a way to tell your router to forward specific incoming connections to your Pi. This is often done with port forwarding, but that has some security considerations. There are, however, other methods that avoid directly opening ports on your router, which is, generally, a safer approach.
Methods for Remote Access
There are several ways to connect to your Raspberry Pi from anywhere. One common method is port forwarding, where you configure your router to send incoming SSH requests (usually on port 22) to your Raspberry Pi's internal IP address. This works, but it does expose your SSH port to the internet, which means you need to be extra careful with security settings.
A more secure option is using a VPN (Virtual Private Network). You can set up a VPN server on your home network (even on your Raspberry Pi itself!) and then connect to that VPN from your remote location. Once connected to the VPN, your remote device is, basically, part of your home network, allowing you to SSH into your Pi as if you were home. This, you know, adds a nice layer of protection.
Another clever method is a reverse SSH tunnel. This is where your Raspberry Pi initiates an outgoing connection to a publicly accessible server (a "jump host") and keeps it open. Then, when you want to connect to your Pi, you SSH into the jump host, which then tunnels you back to your Pi through the already-established connection. This means your home router doesn't need any incoming ports open, which is, honestly, a very secure way to do it. You could, for example, use a free tier of a cloud provider for your jump host, making it quite cost-effective.
Setting Up SSH Keys for Better Security
Using passwords for SSH connections is okay, but SSH keys are much, much better for security. An SSH key is, basically, an access credential in the SSH protocol. It is a pair of cryptographic keys: a public key and a private key. You put the public key on your Raspberry Pi, and you keep the private key safe on your computer.
When you try to connect, your computer uses the private key to prove its identity to the Raspberry Pi. The Pi then uses the public key to verify that you are who you say you are. SSH keys authenticate users and hosts in SSH, which means no one can guess your password, because there isn't one to guess! This method is, arguably, the gold standard for secure remote access. To be honest, it is something everyone should set up.
To generate SSH keys on your computer, you usually type ssh-keygen in your terminal. It will ask you where to save the keys and if you want a passphrase (which is a good idea!). Then, you copy the public key to your Raspberry Pi using a command like ssh-copy-id pi@your_pi_ip_address. This makes the setup, you know, pretty straightforward.
Securing Your Remote IoT Connection
Even with SSH, there are extra steps you can take to make your Raspberry Pi IoT projects even safer. Security is not a one-time thing; it is an ongoing process. We, like your, want to make sure your devices are well-protected.
Beyond Passwords: Key-Based Authentication
As mentioned, SSH keys are far superior to passwords. Once you have set up key-based authentication, you should, actually, disable password login for SSH on your Raspberry Pi. This removes the risk of someone trying to guess your password. You can do this by editing the SSH server configuration file (/etc/ssh/sshd_config) and setting PasswordAuthentication no. Remember to restart the SSH service after making changes with sudo systemctl restart ssh.
This simple change, basically, makes your Pi much harder to break into. It means only someone with your specific private key can connect, and that key is, very, very hard to copy or fake.
Firewall Rules and Best Practices
Even if you are using SSH keys, having a firewall on your Raspberry Pi adds another layer of defense. A firewall controls what network traffic is allowed in and out of your device. You can use a tool like ufw (Uncomplicated Firewall) to set up rules. For example, you might only allow SSH connections from specific IP addresses, or only allow SSH on a non-standard port.
Changing the default SSH port (port 22) to a different, higher-numbered port (like 2222 or 22022) is a common practice. This does not make your connection inherently more secure, but it does make it less likely to be targeted by automated scanning tools that just look for port 22. It is, like, a simple way to fly under the radar a bit. Also, regularly checking your router's logs can help you spot unusual activity, which is, generally, a good habit.
Regular Updates and Monitoring
Keeping your Raspberry Pi's operating system and software up to date is, honestly, one of the most important security practices. Software updates often include fixes for security vulnerabilities. If you don't update, you could be leaving your device open to known attacks. Make it a habit to run sudo apt update && sudo apt full-upgrade regularly, perhaps once a month or whenever you notice new updates are available.
Monitoring your Pi for unusual activity can also help. Tools like fail2ban can automatically block IP addresses that try to log into your SSH server too many times unsuccessfully. This prevents brute-force attacks and, really, keeps your system safer. You can also set up email alerts for certain system events, which is, actually, pretty neat for staying informed.
Troubleshooting Common SSH Issues
Sometimes things do not go perfectly the first time, and that is okay. Here are some common problems you might run into when setting up SSH and how to fix them. It is, basically, part of the learning process.
Connection Refused?
If you get a "Connection refused" error, it usually means the SSH server on your Raspberry Pi is not running, or a firewall is blocking the connection. First, check if SSH is enabled and running on your Pi using sudo systemctl status ssh. If it is not active, try starting it with sudo systemctl start ssh.
Also, check your firewall settings on the Pi and your router. Make sure port 22 (or whatever port you are using for SSH) is open and forwarded correctly, if you are using port forwarding. Sometimes, too, it's almost a simple typo in the IP address, so double-check that as well.
Authentication Problems
Getting "Permission denied" errors usually points to an issue with your username or authentication method. Make sure you are using the correct username for your Raspberry Pi (usually pi). If you are using SSH keys, verify that your public key is correctly installed on the Pi in the ~/.ssh/authorized_keys file and that the permissions on that file are correct (chmod 600 ~/.ssh/authorized_keys).
If you have disabled password authentication, you absolutely must use SSH keys. If you forgot your private key's passphrase, you will need to regenerate your keys. This can be a bit of a hassle, so keep those passphrases safe, you know.
Slow Connections
A slow SSH connection can be frustrating. This might be due to network latency, especially if you are connecting over a long distance or a poor Wi-Fi signal. Try connecting from a different network or closer to your router to see if the speed improves. Sometimes, a slow DNS lookup can also cause delays. You can try adding UseDNS no to your sshd_config file on the Pi, but be aware of what that does.
Another reason could be that your Raspberry Pi is under heavy load, running many processes. Check its resource usage with commands like top or htop. Reducing the workload on your Pi can often speed up SSH connections, and, really, improve its overall performance.
Frequently Asked Questions
Here are some common questions people ask about SSH and Raspberry Pi IoT.
How can I connect to my Raspberry Pi if I don't know its IP address?
If you are on the same local network, you can often use its hostname, like ssh pi@raspberrypi.local. Tools like network scanners can also help find devices on your network. For remote access, you might need a dynamic DNS service if your public IP changes, or use a method like a reverse SSH tunnel which doesn't rely on knowing your public IP directly, which is, generally, easier for many.
Is it safe to port forward SSH to my Raspberry Pi?
It can be safe if you take strong security measures. This means using very strong SSH keys, disabling password authentication, changing the default SSH port, and potentially restricting access to specific IP addresses with a firewall. Without these steps, it is, honestly, quite risky. Many people prefer VPNs or reverse SSH tunnels for better security.
Can I use SSH to control other IoT devices, not just Raspberry Pi?
Yes, if your IoT device runs a Linux-based operating system and has an SSH server installed and enabled, you can often use SSH to control it. Many single-board computers and some smart home hubs fit this description. However, simpler IoT devices might not have SSH capabilities, and, really, rely on other protocols for control.
Take Control of Your IoT Projects
Getting your Raspberry Pi IoT projects accessible from anywhere using SSH is, basically, a game-changer. It gives you the freedom to manage your devices, collect data, and keep things running smoothly, no matter where you are. By understanding the basics of SSH, setting up your Pi correctly, and focusing on strong security practices, you can build a truly connected and reliable system.
Remember that the core of SSH, as developed by Tatu Ylonen and OpenBSD, is about secure communication. Using SSH keys and keeping your system updated are, you know, your best defenses. Start exploring the possibilities of remote access for your Raspberry Pi today, and, really, see how much more you can do. Learn more about SSH on our site, and link to this page here for more Raspberry Pi tips.
You can find more detailed information on SSH commands and configurations on the official OpenSSH documentation, which is, typically, a great resource for learning about options and settings.
- Max Amini Muslim
- Science Words With K
- Femboy Threesome
- Queenpussybossv Leaked Onlyfans
- Sabeer Bhatia Net Worth


Detail Author:
- Name : Prof. Adella Oberbrunner DVM
- Username : sonya.kuhic
- Email : ewalsh@schaden.org
- Birthdate : 1996-04-08
- Address : 3416 Sanford Hill Lake Eldora, IL 15310
- Phone : +1-484-769-6848
- Company : Hane, Ondricka and Ebert
- Job : Septic Tank Servicer
- Bio : Occaecati est saepe alias. Qui nobis repudiandae voluptatibus et mollitia in. Rerum consequatur ea laboriosam qui. In occaecati nihil aut architecto.
Socials
linkedin:
- url : https://linkedin.com/in/remington7832
- username : remington7832
- bio : Dolorem voluptatem nulla aut repudiandae.
- followers : 4093
- following : 2310
tiktok:
- url : https://tiktok.com/@remingtonconroy
- username : remingtonconroy
- bio : Et voluptates et et fugit omnis harum.
- followers : 1536
- following : 360
instagram:
- url : https://instagram.com/conroy2016
- username : conroy2016
- bio : Sit sequi est sed et recusandae dolores non. Non accusantium quis non pariatur asperiores at.
- followers : 6437
- following : 1235
twitter:
- url : https://twitter.com/conroyr
- username : conroyr
- bio : Fugiat ut omnis eum doloribus et officiis repellendus. Incidunt ea nemo debitis. Nobis ad temporibus illum eveniet. Ad est officiis quas quas autem aliquid et.
- followers : 5665
- following : 1551
facebook:
- url : https://facebook.com/remington_real
- username : remington_real
- bio : Nostrum corporis a dolorem soluta esse omnis.
- followers : 1171
- following : 2433