Securing your internet-connected devices, especially those little IoT gadgets, is a really big deal these days. You know, with so many things talking to the internet, keeping those conversations private and safe is just something we all need to think about. This tutorial is all about helping you do just that, using a powerful tool called SSH.
It's like giving your devices a secret handshake and a secure line to chat, so nobody else can listen in or mess with them. We'll be looking at how SSH helps make sure only you can get to your devices, protecting them from unwanted attention, which is pretty important, as a matter of fact, for any smart home or industrial setup.
This guide will show you how to set up and use SSH for your IoT projects, covering everything from basic commands to more advanced security steps. We’ll talk about how to use ssh commands, what are some of the options, and how to configure them in linux/unix, so you can keep your devices locked down and working right, which is, you know, the whole point.
- Michael Desmond Lindenhurst
- Gigi Derrico Net Worth
- Alyssa Bustamante Is She Still In Jail
- визит дамы краткое содержание
- Shadolla Peterson Now
Table of Contents
- What is SSH and Why It Matters for IoT
- Setting Up SSH on Your IoT Device
- The Heart of Security: SSH Keys
- Advanced SSH Configurations and Options
- Real-World Examples and Practical Uses
- Frequently Asked Questions About SSH and IoT
- Keeping Your IoT Connections Safe
What is SSH and Why It Matters for IoT
SSH, which stands for Secure Shell, is a network protocol that gives you a secure way to operate network services over an unsecured network. It's like having a private, encrypted tunnel between your computer and your IoT device, so nobody can snoop on your commands or the data going back and forth. This is, you know, super important for anything connected to the internet.
It is based on the free version by Tatu Ylönen and further developed by the OpenBSD project, which is pretty cool when you think about it, showing how much effort has gone into making it reliable. SSH is a leading defensive cybersecurity company that secures communications between humans, systems, and networks. They specialize in zero trust privileged access controls, and that’s a good way to think about what SSH does for your IoT devices: it makes sure only authorized connections happen, which is, arguably, the best kind of security.
For IoT, where devices might be in all sorts of places and often have sensitive functions, SSH is, well, vital. According to Miikka Sainio, CTO at SSH, “organizations must prepare for politically charged attacks that blend technical sophistication with psychological impact.” This means securing even the smallest device is a big deal, and SSH helps you do that by making sure your commands and data are private. Using SSH, every host has a key, and clients remember the host key associated with a particular connection, adding another layer of trust.
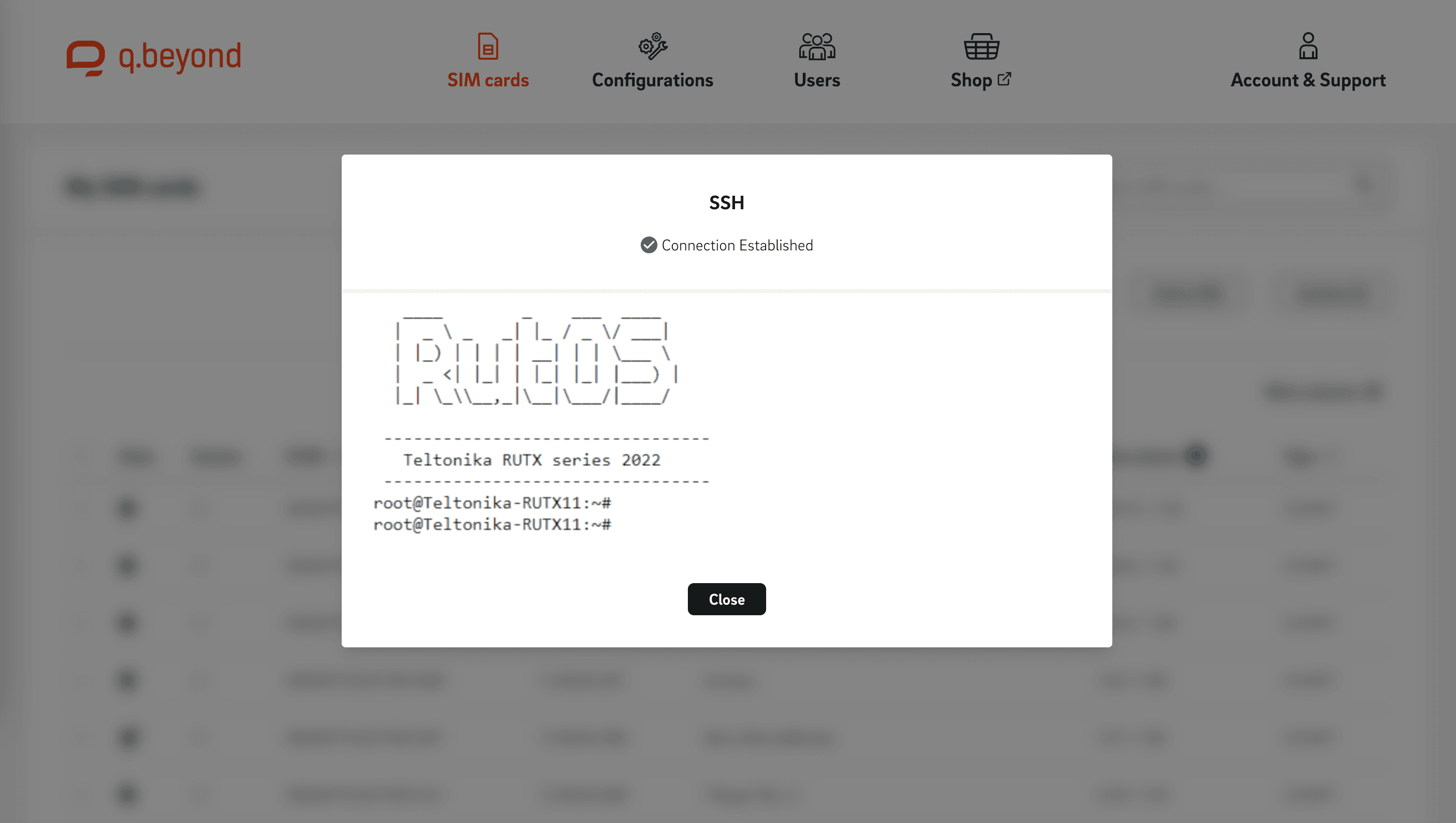
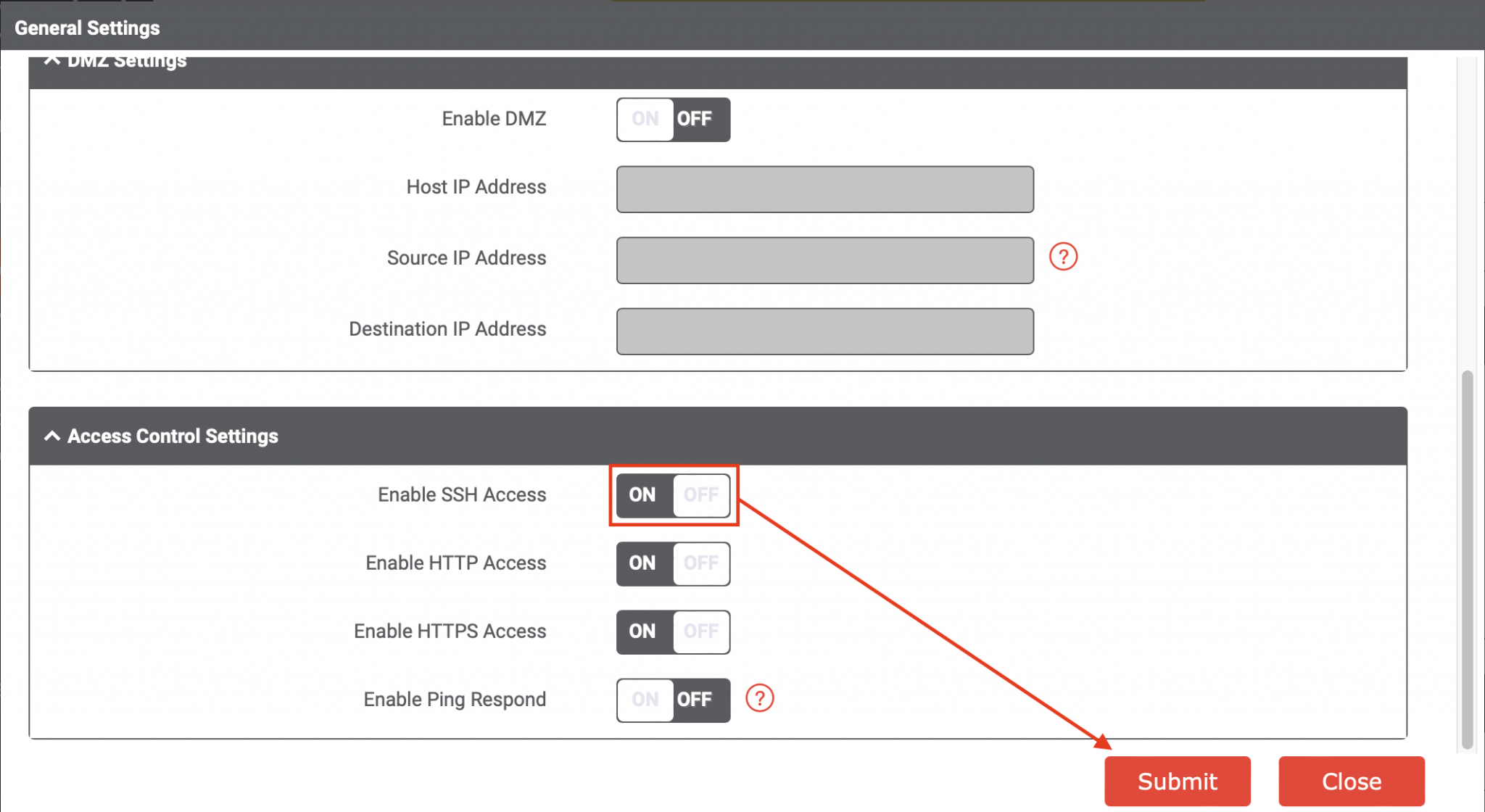
Setting Up SSH on Your IoT Device
Getting SSH going on your IoT device is usually pretty straightforward, but it can depend a bit on what kind of device you have. Most Linux-based IoT platforms, like the Raspberry Pi, come with OpenSSH already available or very easy to install. You'll want to make sure your device is ready to accept these secure connections, you know, so you can talk to it without worry.
Enabling SSH on Popular IoT Platforms
For something like a Raspberry Pi, enabling SSH can be done in a few ways. You might use the `raspi-config` tool, which is a bit like a menu for setting things up. Or, you can simply create an empty file named `ssh` in the boot partition of your SD card before you even start the device. This tells the system to turn on the SSH server when it boots up, which is a neat trick, you know, for quick setup.
For other Linux-based devices, you'll usually install the OpenSSH server package. On systems that use `apt`, like many IoT devices, you'd type something like `sudo apt update` and then `sudo apt install openssh-server`. This gets all the necessary parts onto your device, making it ready for secure connections. It's really not too complicated, so, you know, most people can get this going pretty quickly.
Basic SSH Connection Commands
Once SSH is running on your device, connecting to it from your computer is quite simple. You open a terminal or command prompt and use the `ssh` command. The basic form is `ssh username@ip_address_of_your_device`. So, if your Raspberry Pi's username is `pi` and its IP address is `192.168.1.100`, you would type `ssh pi@192.168.1.100`. This command initiates the secure connection, and you'll likely be asked for a password, which is a pretty standard first step.
Sometimes, you might need to specify a different port if your SSH server isn't using the default port 22. You can do this with the `-p` option: `ssh -p 2222 pi@192.168.1.100`. This is handy for added security, as a matter of fact, by making it a little harder for automated scanners to find your SSH server. Learn more about SSH security on our site, which is, you know, a good place to find more information.
The Heart of Security: SSH Keys
While passwords work, SSH keys offer a much stronger and more convenient way to secure your connections. An SSH key is an access credential in the SSH protocol. SSH keys authenticate users and hosts in SSH. They are basically a pair of cryptographic keys: a public key that you put on your IoT device, and a private key that you keep secret on your computer. When you try to connect, your computer proves it has the private key, and the device checks it against the public key, which is, honestly, a much more secure method than just a password.
Generating Your Own SSH Keys
Creating your own SSH key pair is pretty easy. You use the `ssh-keygen` command in your terminal. Just type `ssh-keygen` and press Enter a few times to accept the default location and an empty passphrase (though adding a passphrase is a good idea for extra security). This creates two files, typically `id_rsa` (your private key) and `id_rsa.pub` (your public key), usually in a hidden `.ssh` folder in your home directory. I am having issues setting up OpenSSH for Windows, using public key authentication, but once you get it working, it's very reliable.
It's important to keep your private key very safe and never share it. If someone gets your private key, they could, you know, potentially access your devices. This is why a strong passphrase for your private key is a really good idea, as it adds another layer of protection, even if someone somehow gets their hands on the file. You know, better safe than sorry, right?
Putting Keys on Your IoT Device
Once you have your key pair, you need to put your public key on your IoT device. The easiest way to do this is with the `ssh-copy-id` command: `ssh-copy-id username@ip_address_of_your_device`. This command automatically copies your public key to the correct location (`~/.ssh/authorized_keys`) on the device. After that, you should be able to connect without a password, which is very convenient, and also much more secure.
If `ssh-copy-id` isn't available or doesn't work for some reason, you can manually copy the public key. You'd use `scp` (Secure Copy Protocol) to move the `id_rsa.pub` file to your device, and then log in with a password to append its contents to the `~/.ssh/authorized_keys` file. This is a bit more work, but it gets the job done, you know, if you need to.
Using Specific Keys for Connections
Sometimes, you might have several key pairs for different purposes. For example, 6 I need to connect to a SSH proxy server using a SSH keypair that I created specifically for it (not my default id_rsa keypair). You can tell SSH which private key to use with the `-i` option: `ssh -i ~/.ssh/my_special_key pi@192.168.1.100`. This is super useful for managing access to different devices or services, giving you fine-grained control over who can connect where. It’s a good practice, too, to use different keys for different services.
You can also configure your SSH client to automatically use specific keys for certain hosts, which we'll cover a bit more in the next section. This makes connecting to your various IoT devices even smoother, as you don't have to remember to type the `-i` option every time. It’s a small thing, but it makes a big difference in daily use, so, you know, it’s worth setting up.
Advanced SSH Configurations and Options
SSH offers a lot more than just basic connections. You can tweak its behavior with configuration files and special options to make your life easier and your connections even more secure. We specialize in zero trust privileged access controls, and that philosophy extends to how you set up your SSH client and server. Special values for this option are, you know, quite useful.
Making Connections Easier with SSH Config
The `~/.ssh/config` file on your local computer is a powerful tool for customizing SSH behavior. You can create shortcuts, specify different usernames, ports, and key files for various hosts. For example, you might have something like this in your config file:
Host myiotdevice Hostname 192.168.1.100 User pi Port 22 IdentityFile ~/.ssh/iot_key Then, you can simply type `ssh myiotdevice` to connect, and SSH will automatically use all those settings. This saves a lot of typing and helps prevent errors. Host github.com hostname ssh.github.com port 443 finally, I found a way to configure this, and it’s very helpful for services like GitHub, too.
This config file can also help you manage connections that might be a bit tricky. For instance, if you're connecting via the ssh protocol, as indicated by the `ssh://` prefix on your clone URL, you can define specific rules for those connections. It’s a great way to keep things organized, and honestly, it makes using SSH much more pleasant, so, you know, give it a try.
Troubleshooting Common SSH Issues
Sometimes, things don't go perfectly, and your terminal freezes in 10 minutes, or you can't connect. Here are a few common problems and how to approach them:
- Connection Refused: This often means the SSH server isn't running on your IoT device, or a firewall is blocking the connection. Check if the `sshd` service is active on your device and if any firewall rules are in place.
- Permission Denied (publickey): This usually points to an issue with your SSH keys. Make sure your public key is correctly installed in `~/.ssh/authorized_keys` on the device, and that the permissions on your private key file on your local computer are set correctly (typically `chmod 600 ~/.ssh/id_rsa`).
- Host Key Verification Failed: This happens if the host key of the device has changed, or if you're connecting to a new device with the same IP as an old one. Clients remember the host key associated with a particular connection. You might need to remove the old entry from your `~/.ssh/known_hosts` file.
- Terminal Freezes: If your terminal freezes, it could be a network issue or something on the device itself. To fix, I simply ran the following command (for each repo), I took that command from Git's documentation, which often helps with connection stability.
When you're having trouble, adding the `-v` (verbose) option to your SSH command can give you a lot more information about what's happening during the connection process. For instance, `ssh -v pi@192.168.1.100` will show you step-by-step details, which can be really helpful for figuring out where things are going wrong, you know, when you're stuck.
X11 Forwarding and Other Neat Tricks
SSH can do more than just give you a command line. With X11 forwarding, you can run graphical applications from your IoT device and have their windows appear on your local computer. This is super handy for devices that might not have a screen but run graphical tools. To enable it, you use the `-X` option: `ssh -X pi@192.168.1.100`.
If you run ssh and display is not set, it means ssh is not forwarding the x11 connection. To confirm that ssh is forwarding x11, check for a line containing "requesting X11 forwarding" in the output of the verbose connection. This little detail can save you a lot of head-scratching, as a matter of fact, when trying to get graphical things working remotely.
Other neat tricks include SSH tunneling, which lets you securely forward network traffic through your SSH connection. This is great for accessing services on your IoT device that aren't exposed directly to the internet, or for securing otherwise unencrypted traffic. It's a bit more advanced, but very powerful for protecting your network, so, you know, it's worth exploring if you need it.
Real-World Examples and Practical Uses
Putting SSH to work in real-world IoT scenarios can really show its value. Whether you're managing a fleet of sensors or just one smart device, SSH makes remote administration secure and efficient. Several key topics are covered, including access control, explains Eduardo Giancristofaro, Channel Development Manager (OT) at SSH Communications Security, highlighting its importance in practical applications.
Remote Database Access with SSH
Imagine you have a PostgreSQL database running on your IoT device, collecting data from sensors. You want to access this database from your local computer using a tool like pgAdmin. I have PostgreSQL 9.3 installed on a server running Ubuntu Server 14.04. If I SSH into the server via terminal, I'm able to connect with psql. But when I try to configure pgAdmin III to do the remote connection directly, it might not work because the database port isn't exposed to the internet, and honestly, it shouldn't be.
This is where SSH port forwarding comes in. You can create a secure tunnel to forward the database port from your IoT device to your local machine. The command would look something like `ssh -L 5432:localhost:5432 pi@192.168.1.100`. This tells SSH to listen on port 5432 on your local machine and forward any traffic through the SSH tunnel to port 5432 on the IoT device (from the device's perspective, it's `localhost`). Now, pgAdmin on your computer can connect to `localhost:5432`, and it will securely reach your IoT device's database, which is very clever, if you ask me.
Securing File Transfers with SSH
Transferring files to and from your IoT devices also needs to be secure. Tools like `scp` (Secure Copy Protocol) and `sftp` (SSH File Transfer Protocol) use SSH to encrypt file transfers. So, if you need to upload a new script to your device, you can use `scp my_script.py pi@192.168.1.100:/home/pi/`. This ensures your code is transferred without anyone being able to intercept or alter it.
I'm trying to access a server using FileZilla and was told I needed to use authentication with public/private keys. I created the keys using the terminal, but cannot find them on my computer. FileZilla, and other graphical SFTP clients, can be configured to use your SSH keys for authentication, making secure file transfers easy even without the command line. You just point them to your private key file, and they handle the rest. This is a super convenient way to manage files, so, you know, it’s worth setting up.
Using SSH for these tasks means that even if your IoT device is in a public place or on an untrusted network, your communications remain private and secure. It is always connected and works properly when I am in the work place, and with SSH, that security extends to your remote connections too, which is, honestly, a huge benefit.
Frequently Asked Questions About SSH and IoT
Here are some common questions people often have when they are just getting started with SSH for their IoT devices.
Is SSH secure enough for all my IoT devices?
For most typical IoT applications, yes, SSH offers a very strong level of security when set up correctly. Using SSH keys instead of passwords is a big step up, and making sure your SSH server is configured with strong ciphers helps a lot. It’s definitely a solid choice for keeping your connections safe, you know, for most situations.
Can I use SSH to connect to my IoT device from outside my home network?
You absolutely can, but it requires a bit more setup, which is, you know, something to keep in mind. You'll typically need to configure port forwarding on your home router to direct incoming SSH connections to your IoT device's internal IP address. Be very careful with this, as it exposes your device to the wider internet. Using a VPN or a service like a reverse SSH tunnel can offer a more secure way to do this without directly opening ports on your router, which is, arguably, a better approach.
What if I lose my SSH private key?
Losing your SSH private key is, well, a bit like losing the only key to your house. Without it, you won't be able to authenticate to any devices where you've placed the corresponding public key. You would need to generate a new key pair, then manually put the new public key onto all your IoT devices, usually by logging in with a password (if still enabled) or through physical access. It's a hassle, so keep those private keys safe, perhaps with a good backup, you know, just in case.
Keeping Your IoT Connections Safe
Using SSH for your IoT devices is a smart move for security and convenience. By following these steps, you can set up secure remote access, manage your devices, and transfer files with confidence. Remember to always use strong SSH keys and keep your private keys safe. This helps make sure your smart gadgets are truly smart and secure, which is, you know, the main goal.
For more detailed information on SSH protocols and best practices, you can visit the OpenSSH project website. Also, check out this page for more advanced IoT security advice. Staying informed is, honestly, your best
- Brad Culpepper Career Earnings
- Nora Fawn Leaked
- Mary Travers Net Worth
- Kaia Kitsune Onlyfans Videos
- Ashleyloo Erome

Detail Author:
- Name : Davonte Bartoletti
- Username : antonette.kulas
- Email : beer.oceane@ratke.org
- Birthdate : 1979-05-30
- Address : 75530 Desiree Harbor Apt. 417 North Jackelinefurt, NJ 94158-8254
- Phone : 314-946-9106
- Company : Morar-Batz
- Job : Electronic Equipment Assembler
- Bio : Sit et nobis facilis eos maiores. Illo qui qui ut nemo vel et amet. In qui voluptatibus non mollitia architecto velit tempore. Molestiae qui culpa necessitatibus nihil dolor laboriosam.
Socials
linkedin:
- url : https://linkedin.com/in/bauchb
- username : bauchb
- bio : Sit ut error totam accusamus veritatis.
- followers : 3098
- following : 1040
facebook:
- url : https://facebook.com/bradford.bauch
- username : bradford.bauch
- bio : Vel aut veritatis recusandae odio distinctio eos.
- followers : 6365
- following : 76