Connecting a tiny computer, like your Raspberry Pi, to the big, wide internet for an Internet of Things (IoT) project feels pretty exciting, doesn't it? You get to control things from far away, gather information, and make cool stuff happen. But, you know, it's almost like leaving your front door wide open if you don't think about how you're doing it. We really need to talk about how to securely connect remote IoT Raspberry Pi to VPC, especially when it comes to getting files onto your device.
Many folks, you know, they just want their little Pi to do its job without any fuss. They might not realize the risks involved when that connection isn't as tight as it could be. Think about all the things that go wrong when you're trying to do something online and a connection feels, well, a bit off. There's often a worry about who else might be peeking in or even messing with your devices. This is why making sure your Raspberry Pi has a safe pathway to its virtual private cloud (VPC) is very, very important.
This whole idea of a "download" when we talk about securely connecting your remote IoT Raspberry Pi to a VPC, it's more than just grabbing a file. It includes updates, new instructions, or even just checking if everything is running right. As a matter of fact, making sure these bits of information travel safely means your whole project stays sound. We're going to walk through how to keep things locked down, so your Pi can work its magic without any unwelcome surprises, truly.
Table of Contents
- What is Remote IoT and VPC for Raspberry Pi?
- Why Security Matters for Your Pi
- Common Connection Worries
- Understanding the "Download" Aspect
- Firmware and OS Updates
- Configuration Files and Scripts
- Secure Transfer Methods
- Steps to Secure VPC Connection
- Setting Up Your AWS VPC
- Configuring Your Raspberry Pi
- VPN or Direct Connect?
- Implementing Identity and Access Management (IAM)
- Best Practices for Ongoing Security
- Regular Updates and Patches
- Strong Authentication
- Monitoring and Logging
- Troubleshooting Common Issues
- Connection Drops
- "Untrusted Connection" Messages
- Update Failures
- Frequently Asked Questions
What is Remote IoT and VPC for Raspberry Pi?
When we talk about "Remote IoT," we mean devices, like your Raspberry Pi, that are out there, doing their thing, but you're not right next to them. They're gathering information, maybe controlling some lights, or perhaps keeping an eye on temperatures in a greenhouse. You need to reach them, give them new instructions, or get their data, all from a distance. That, is that, pretty much what remote IoT is about, you know?
Now, a "VPC," or Virtual Private Cloud, is like having your own little section of a big cloud computing service, such as Amazon Web Services (AWS). It's a place where you can set up your servers and services in a way that feels like your own private network, even though it's part of a much larger system. This private space helps keep your things separate from everyone else's. So, when your Raspberry Pi connects to this VPC, it's almost like it's joining your private office network, but online, which is pretty neat.
Why Security Matters for Your Pi
A Raspberry Pi, for all its small size and cleverness, can be a doorway. If someone gets in, they could mess with your project, steal your data, or even use your Pi to cause trouble elsewhere. Honestly, the thought of someone taking over your little device is a bit unsettling. It's not just about your project, either; it could affect other parts of your home network or even your online accounts if things aren't locked down. We really want to avoid those kinds of headaches, you know?
- Is Jack Pratt Disabled
- Holly Sonders Age
- Bongonaari Porn Video
- Taylor Fritz Nude
- Jenny Mccarthy Net Worth
Imagine, for instance, your device is at risk because it's out of date and missing important security updates. That's a real worry, isn't it? We want to get you back on track so your Raspberry Pi can run more securely, doing its job without being a target. Keeping things safe means your hard work stays protected, and you can trust what your Pi is doing. It's like putting a strong lock on your digital front door, basically.
Common Connection Worries
People often run into issues when trying to get their remote devices to talk to their cloud setups. Sometimes, it's just a matter of things not connecting at all. Other times, you might see messages like "This connection is untrusted" when trying to reach a service, which is a clear sign something isn't right. It's a bit like trying to call someone and getting a weird message saying you can't confirm the line is safe, you know?
There can be a problem connecting securely to a website, or in this case, your cloud service. These kinds of warnings are really important. They tell you that the path your data is taking isn't as secure as it should be, and that's a big deal for IoT projects. We want to avoid that feeling of confusion, like when you're not supposed to have your browser managed by an organization, but it is, and you're just wondering why. We want clear, trustworthy connections, truly.
Understanding the "Download" Aspect
When we talk about "downloading" in the context of your remote IoT Raspberry Pi and a secure VPC connection, it's not just about getting a new picture or a song. For these little computers, "download" can mean a whole bunch of really important things that keep them running right and safely. It's almost like giving your Pi new instructions or a fresh set of tools, you know?
This "download" idea is very broad here. It covers everything from making sure the core software is up-to-date to sending specific commands that tell your Pi what to do next. All these actions need to happen over a secure connection, because if they don't, someone could slip in something bad or change your instructions. That, is that, a big risk we want to avoid, honestly.
Firmware and OS Updates
Just like your phone or your home computer, your Raspberry Pi needs regular updates. These updates often fix security holes, make things run better, or add new features. This is the "firmware" and "operating system (OS)" stuff. When your device is out there, perhaps in a remote spot, getting these updates safely is really important. It's like getting your car serviced; you want to make sure the mechanic is trustworthy, right?
If these updates don't come through a secure path, there's a chance someone could give your Pi a fake update, or even one that breaks things. You know, like when an update keeps trying to reinstall and fails, or it looks like it was already installed, but you're still trying to stop it from reinstalling again. That kind of frustration is bad enough, but imagine if it was a malicious update! So, a secure connection for these updates is pretty much non-negotiable, honestly.
Configuration Files and Scripts
Your Raspberry Pi runs based on a bunch of settings and small programs called "scripts." These tell it how to connect to Wi-Fi, what sensors to read, or how to send data to your VPC. When you make changes to your project, you often need to send new configuration files or update these scripts to your remote Pi. This is another type of "download" that needs to be super secure, you know.
Imagine you want to password protect a file, but you can't seem to find the option anymore. Or you only want to protect a specific file, not the entire folder. This applies to your Pi's configuration files too. You need to make sure that when you send a new setting, only your Pi gets it, and no one else can read or change it along the way. Otherwise, someone could trick your Pi into doing something it shouldn't, which is a big worry, really.
Secure Transfer Methods
To get these updates and files to your Pi safely, you can't just send them over any old connection. You need secure ways to move them. Things like Secure Shell (SSH) for remote access and file transfer, or using secure protocols like HTTPS for web-based downloads, are pretty standard. But even then, how your Pi connects to the internet and then to your VPC is the first layer of protection. This is where the VPC connection really shines.
Using a secure tunnel, perhaps a VPN, means that all the data, including your downloads, gets encrypted before it leaves your Pi and stays encrypted until it reaches your private cloud. It's like putting your important documents in a locked box and then sending that box through a private, guarded tunnel. This way, even if someone intercepts the data, they can't make sense of it, which is very, very reassuring, truly. Learn more about secure connections on our site, and link to this page here for more details on secure file handling.
Steps to Secure VPC Connection
Getting your Raspberry Pi to talk to your VPC in a safe way involves a few steps. It's not overly complicated, but each part is important for building a strong, protected pathway. We're going to walk through the main bits, so you can set things up with confidence. It's almost like building a little fortress for your data, you know?
This process is about creating a dedicated, private space for your Pi's communications within a larger cloud environment. It helps prevent unauthorized access and keeps your IoT data separate from public traffic. So, let's get into how you can make this happen, honestly.
Setting Up Your AWS VPC
First off, you need to set up your Virtual Private Cloud in AWS. This means defining its size, its network ranges, and creating subnets within it. Think of it like drawing the blueprint for your private digital neighborhood. You'll also set up security groups and network access control lists (ACLs) which act like firewalls, deciding what traffic can come in and go out. These are very, very important for keeping things locked down, you know.
You'll want to make sure your VPC is configured with private subnets for your Raspberry Pi, meaning these parts of your network aren't directly exposed to the internet. This is a pretty fundamental step for security. You can find excellent guides on the AWS website itself for this, which is a great external reference. For example, you can check out the AWS VPC documentation for detailed instructions. This initial setup is, frankly, crucial.
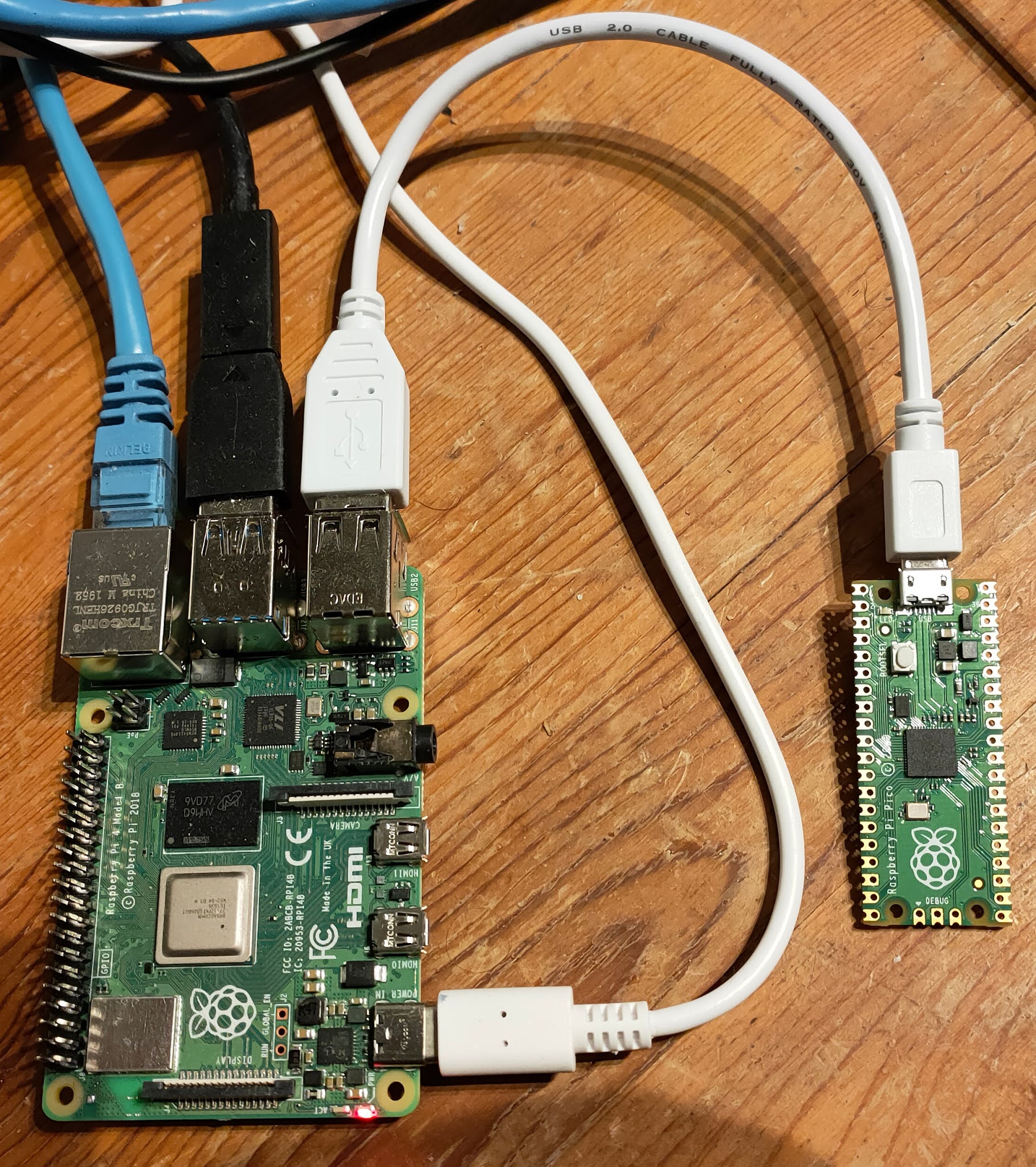
Configuring Your Raspberry Pi
Once your VPC is ready, your Raspberry Pi needs to know how to connect to it. This usually involves installing specific software on your Pi, such as a VPN client. This client will create a secure tunnel between your Pi and a VPN server that you've set up within your VPC. It's like giving your Pi a special key and a secret map to your private network, you know.
You'll also need to make sure your Pi's operating system is up-to-date and that you've changed default passwords. Honestly, leaving default passwords is like leaving your actual house key under the doormat. We want to avoid that, you know? The configuration files for the VPN client need to be set up correctly, pointing to your VPN server's details in the VPC. This step is, in some respects, where the magic happens for the secure connection.
VPN or Direct Connect?
When connecting your Raspberry Pi to your VPC, you typically have a couple of main options. A Virtual Private Network (VPN) is a common choice for remote IoT devices. It creates an encrypted tunnel over the public internet, making your connection private and secure. This is usually the most practical and cost-effective method for individual Raspberry Pis, honestly.
Another option, for larger or more critical deployments, is AWS Direct Connect. This provides a dedicated, private network connection from your premises to AWS. While incredibly secure and reliable, it's generally overkill and much more expensive for a single Raspberry Pi. For most remote IoT projects, a well-configured VPN connection is usually the way to go, offering a great balance of security and practicality, you know. It tends to be a pretty solid choice for many people.
Implementing Identity and Access Management (IAM)
AWS Identity and Access Management (IAM) is how you control who can do what within your AWS account. For your Raspberry Pi, you'll want to create an IAM role or user with very specific, limited permissions. This role would only allow your Pi to access the exact AWS services it needs, and nothing more. It's like giving someone a guest pass that only lets them into the specific rooms they need to visit, not the whole building, you know?
This "least privilege" principle is incredibly important for security. If your Pi's credentials were ever compromised, the damage would be contained because it couldn't access anything beyond its designated tasks. This prevents a situation where, for instance, your browser is managed by an organization without your permission, but for your Pi, you are in full control of its permissions. Setting up IAM properly is, honestly, a key piece of the puzzle.
Best Practices for Ongoing Security
Setting up a secure connection is a fantastic start, but keeping it secure is an ongoing effort. It's not a one-and-done kind of deal, you know? Just like you keep your home secure by locking doors and checking things regularly, your remote IoT Raspberry Pi needs constant care. We want to make sure your system stays safe and sound, truly.
These practices are about maintaining that strong defense over time. They help you stay ahead of potential problems and keep your Pi working as it should, without any worries. So, let's look at how to keep things tight, honestly.
Regular Updates and Patches
We've talked about this a bit, but it really can't be stressed enough: keep your Raspberry Pi's operating system and all its software updated. Software developers constantly find and fix security vulnerabilities. If you don't apply these updates, your Pi remains exposed to known weaknesses. It's like leaving a window open after a new, stronger lock has been invented, you know?
Automate updates where possible, or set a regular schedule to check for and apply them. This also includes updating any firmware on the Pi itself. Remember, your device is at risk if it's out of date. We want to make sure windows, or rather, your Pi's system, can run more securely. This is, in some respects, one of the easiest yet most overlooked security steps, frankly.
Strong Authentication
Accessing your Raspberry Pi, whether directly or through your VPC, should always require strong authentication. This means using complex passwords, or even better, SSH keys instead of passwords for remote access. SSH keys are much harder to guess or crack than even the longest password. It's like having a very unique, uncopyable fingerprint for access, you know?
Also, consider implementing two-factor authentication (2FA) for any management interfaces or cloud accounts related to your Pi. This adds an extra layer of security, requiring a second piece of information (like a code from your phone) in addition to your password. This makes it significantly harder for unauthorized people to get in, which is very, very good, truly.
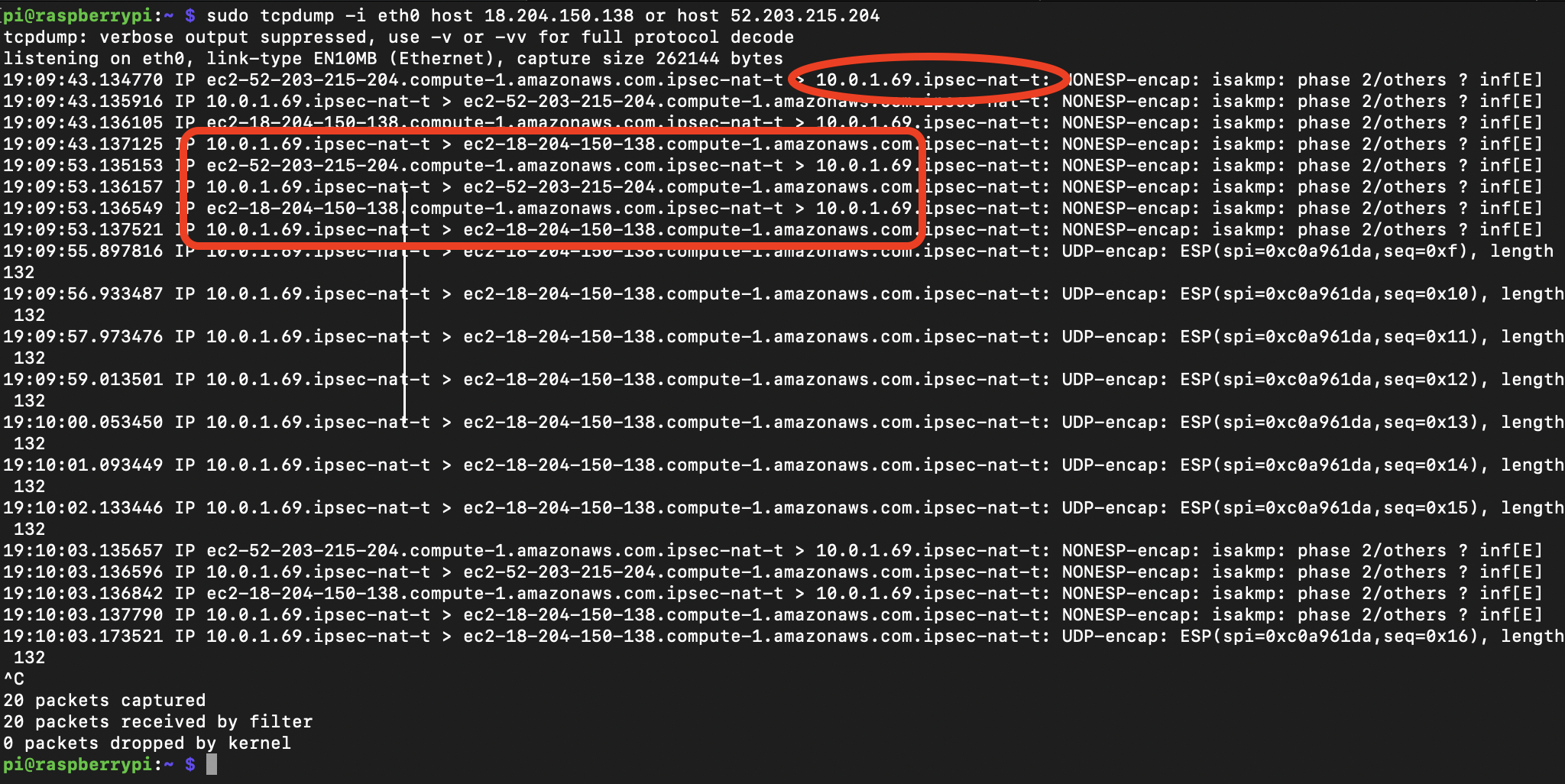
Monitoring and Logging
Knowing what's happening on your Raspberry Pi and within your VPC is pretty important. Set up logging to record events, like who accessed the Pi, when, and what they did. Then, regularly review these logs for anything unusual. It's like having a security camera and reviewing the footage; you can spot problems early, you know?
AWS provides tools like CloudWatch for monitoring your VPC and the services within it. You can set up alerts to notify you if certain thresholds are met, or if suspicious activity is detected. This helps you catch issues quickly, like if legitimate email is being blocked by Outlook, but in this case, it's about spotting unauthorized access attempts or strange network traffic. Being proactive is, frankly, a big part of staying secure.
Troubleshooting Common Issues
Even with the best planning, things can sometimes go a bit sideways. It's almost inevitable, you know? When you're trying to securely connect remote IoT Raspberry Pi to VPC, you might hit a few bumps in the road. Don't worry, many of these issues have pretty straightforward solutions. We want to get you back on track quickly, truly.
It's like when you're working on something and a problem pops up, and you're just confused. We're going to look at some common snags and how to untangle them, honestly. This way, you can keep your Pi running smoothly and securely.
Connection Drops
If your Raspberry Pi keeps losing its connection to the VPC, that's a real pain. This could be due to a few things. Sometimes, it's a weak Wi-Fi signal at the Pi's location, or maybe an issue with the internet service provider. Other times, it could be related to your VPN client configuration on the Pi, or even network settings within your VPC that are accidentally blocking traffic. It's a bit like a phone call that keeps cutting out, you know?
Start by checking the basics: Is the Pi's internet connection stable? Look at the logs on your Pi and your VPN server for any error messages. Make sure your VPC security groups and network ACLs aren't too restrictive, accidentally blocking your Pi's traffic. Sometimes, a simple restart of the VPN service on the Pi can fix it, honestly. Persistence is key here, basically.
"Untrusted Connection" Messages
You know that feeling when you ask Firefox to connect securely to a website, but it says "we can't confirm that your connection is secure"? That kind of message, when connecting your Pi to a service or even your VPC, is a huge red flag. It means the security certificate isn't valid, or there's something else making the connection untrustworthy. This is, in some respects, a very serious warning.
For your Raspberry Pi, this often points to issues with SSL/TLS certificates. Make sure your Pi's system clock is accurate, as incorrect time can cause certificate validation failures. Also, verify that the certificates used by your VPN server or any other services your Pi connects to are correctly installed and up-to-date. If you're seeing this, stop immediately and investigate; don't just click through, you know? Your security depends on it, truly.
Update Failures
Having an issue with an update that keeps trying to reinstall and fails, or it looks like it was already installed, but you're trying to stop it from reinstalling again – that's a common frustration, even with Raspberry Pis. Update failures can leave your Pi vulnerable or even break its functionality. It's like your computer getting stuck in an automatic repair loop after installing Windows updates, you know, showing the logo with "preparing" but never quite finishing.
When updates fail, check your Pi's disk space first; a full disk can prevent updates from installing. Also, look at the update logs for specific error messages. Network issues during the download can also cause failures, so ensure your secure VPC connection is stable. Sometimes, clearing the package cache or manually forcing an update can resolve these problems. It's often a process of elimination to figure out what's going on, honestly.
Frequently Asked Questions
How do I connect my Raspberry Pi to AWS VPC?
You typically connect your Raspberry Pi to an AWS VPC by setting up a VPN (Virtual Private Network) tunnel. This involves configuring a VPN server within your VPC, then installing and configuring a VPN client on your Raspberry Pi. The client creates a secure, encrypted link to your VPC, making your Pi a part of your private cloud network. This is, in some respects, the most common approach for securely connecting remote IoT Raspberry Pi to VPC, truly.
What's the most secure way to access a remote Raspberry Pi?
The most secure way to access a remote Raspberry Pi involves several layers. Using SSH (Secure Shell) with key-based authentication (not passwords) is a must. Connecting through a VPN tunnel to a private network, like an AWS VPC, adds a significant layer of security by encrypting all traffic. Additionally, keeping your Pi's software updated, using strong, unique credentials, and limiting its network exposure are all very, very important steps. It's about building a robust defense, you know?
Do I need a VPN for IoT devices?
While not strictly required for *all* IoT devices in *every* scenario, using a VPN for your Raspberry Pi and other IoT devices is highly recommended for security. It encrypts your device's communications, protects it from direct exposure to the public internet, and helps ensure data integrity. For devices handling sensitive data or performing critical tasks, a VPN, especially when connecting to a VPC, is honestly a very good idea. It helps prevent many of the common connection worries people face, you know.
Detail Author:
- Name : Prof. Lafayette Leannon
- Username : tyrique64
- Email : gloria.mertz@hotmail.com
- Birthdate : 1987-03-17
- Address : 785 Cristian Extension New Craigview, AK 76645
- Phone : (629) 606-0116
- Company : Lindgren Inc
- Job : Public Relations Specialist
- Bio : Laudantium delectus deserunt dolorem excepturi nihil ut. Culpa velit qui aut ducimus. Dolorem voluptates quis et error et quia ut. Quo delectus quos sit fugiat.
Socials
linkedin:
- url : https://linkedin.com/in/cwyman
- username : cwyman
- bio : Aut magnam quisquam amet porro.
- followers : 3508
- following : 2381
tiktok:
- url : https://tiktok.com/@crystal.wyman
- username : crystal.wyman
- bio : Veniam consequatur maiores quaerat natus sunt quos. Eaque sed voluptas et ab.
- followers : 2468
- following : 24
facebook:
- url : https://facebook.com/crystal_wyman
- username : crystal_wyman
- bio : Qui cum est ex minima repudiandae recusandae.
- followers : 3471
- following : 805