Getting your little Raspberry Pi gadgets to chat safely with a big cloud server, like one over on AWS, can feel a bit like making sure a secret message gets from one friend to another without anyone else peeking. It's a tricky puzzle, you know, because you really want your important information to travel right. As the internet of things, or IoT, keeps growing so fast, making sure your remote devices are hooked up securely through a virtual private cloud, or VPC, on AWS is becoming, well, pretty essential for lots of folks.
You might have seen messages pop up, something like "This connection is untrusted" or "There is a problem connecting securely to this website." Those warnings are a big deal, actually, and they show us just how important it is to get our connections right. When you're talking about tiny computers like a Raspberry Pi sending information to a huge cloud setup, like an AWS VPC, you absolutely want to avoid those kinds of scary alerts. You want to send that information to a place like AWS, where it can be stored and used, but you also want to make sure it's done right, you know, very securely.
This guide is all about helping you sort out that puzzle. We'll walk through how to securely connect your remote IoT Raspberry Pi to an AWS server using a VPC. It's a comprehensive look, sort of, at making sure your data stays private and your devices are safe. By following these steps and best practices, you'll be well on your way to building a really reliable and safe IoT system, which is pretty cool, if you ask me.
- Yasmeen Ghauri Net Worth
- Omar Benson Miller Wife
- Jasmine Monjack
- Wwxxcom Reviews 2024
- Alex Honnold Autismo
Table of Contents
- Why Security Matters for Your IoT Projects
- Getting Your Raspberry Pi Ready
- AWS VPC: Your Private Cloud Sanctuary
- Connecting Your Pi to the VPC
- Best Practices for Ongoing Security
- Frequently Asked Questions (FAQs)
- Conclusion
Why Security Matters for Your IoT Projects
You know, in today's interconnected world, securely connecting remote IoT devices to a VPC Raspberry Pi AWS server is pretty much crucial. It helps make sure your data stays private, everything is safe, and things run efficiently. Just like you wouldn't want someone listening in on a private chat, you really don't want unauthorized people getting into your device data. It's about protecting what's important, actually.
The Risks of Open Connections
Think about it: if your Raspberry Pi is just sending data out into the open internet, it's a bit like shouting your secrets in a crowded room. Anyone could potentially hear them. This could lead to all sorts of bad stuff, like someone messing with your device, stealing your information, or even using your Pi for things you never intended. I mean, you've probably heard about devices being compromised because of weak security, right? It's a real worry, so, in some respects, we need to be careful.
When connections are untrusted, or you're seeing those warnings about not being able to confirm a secure connection, that's a red flag. It means there's a problem, and your data might be exposed. For IoT devices, where you're often collecting sensitive environmental data or controlling physical things, these risks are even higher. You really want to avoid any situation where your device is at risk because it's out of date or missing important security updates, which is a common issue, actually.
Why a VPC Makes a Difference
A Virtual Private Cloud, or VPC, is kind of like having your own special, walled-off section within the big AWS cloud. It's a private network just for your stuff, which is pretty neat. This means your Raspberry Pi, when it connects to your AWS server through this VPC, isn't just floating out on the public internet. Instead, it's communicating within a more controlled and isolated space. This significantly cuts down on the chances of unwanted visitors, you know, trying to peek in.
Using a VPC gives you a lot more control over who and what can talk to your devices and your AWS resources. You can set up specific rules, almost like bouncers at a club, to decide exactly what traffic is allowed in and out. This isolation and control are absolutely key for keeping your IoT setup safe. It's a fundamental step towards making sure your connection is secure, not untrusted, which is what we're aiming for.
Getting Your Raspberry Pi Ready
Before we even think about AWS, your Raspberry Pi itself needs to be in good shape, security-wise. It's like preparing your car for a long trip; you want to make sure everything is tuned up and ready to go. This initial setup is, honestly, very important for the overall safety of your remote IoT system.
Basic Pi Setup and OS Hardening
First off, when you get a new Raspberry Pi, don't just leave the default username and password. Change them immediately! That's like leaving your front door unlocked, you know? Use a strong, unique password. Also, always keep your Raspberry Pi's operating system, usually Raspberry Pi OS, up to date. You can do this by running `sudo apt update` and then `sudo apt upgrade` in the terminal. These updates often include important security fixes, so, really, don't skip them.
Consider disabling services you don't actually need running on your Pi. Every running service is potentially another door for someone to try and get in. For example, if you're not using a desktop environment, you might run your Pi in "headless" mode. Also, setting up a firewall on your Pi, like UFW (Uncomplicated Firewall), can help control what network traffic is allowed to reach your device. It's about closing off unnecessary entry points, pretty much.
Essential Software and Tools
To get your Pi talking to AWS securely, you'll need a few pieces of software. For starters, you'll likely use SSH (Secure Shell) to connect to your Pi remotely. Make sure you're using key-based authentication for SSH, not just passwords. Keys are much, much more secure. You'll also need tools for managing certificates, which are a big part of secure communication, as well as any specific AWS SDKs or client software for IoT services.
Depending on your chosen connection method, you might install VPN client software like OpenVPN. We'll get into that a bit later. For your Raspberry Pi to securely connect remote IoT VPC Raspberry Pi AWS server, you'll also want to make sure you have the necessary libraries for whatever programming language you're using, like Python, to interact with AWS services. It's about having all your tools ready, so you can build things properly.
AWS VPC: Your Private Cloud Sanctuary
Now, let's talk about the AWS side of things. Setting up your VPC correctly is, in a way, the cornerstone of this whole secure connection business. It's where you build that private, walled-off space we mentioned earlier, which is really cool.
Setting Up Your VPC
When you create a VPC in AWS, you're essentially defining your own private IP address range within AWS. This range is called a CIDR block. You pick a range that won't clash with your existing home or office networks. Then, you'll choose an AWS Region where your VPC will live. It's important to pick a region that's geographically close to your Raspberry Pi devices if possible, to help with performance, you know, and reduce latency.
AWS has a "VPC Wizard" that can help you get started with a basic setup, which is pretty handy. It can create a VPC with public and private subnets, an internet gateway, and route tables for you. This is often a good starting point, especially if you're somewhat new to VPCs. You can always customize it later, of course, but it gives you a solid foundation to build upon, which is very helpful.
Subnets, Route Tables, and Internet Gateways
Inside your VPC, you'll have subnets. Think of subnets as smaller sections of your private network. You might have public subnets for resources that need to talk to the internet, like an internet gateway, and private subnets for resources that should only be accessible from within your VPC, like your backend servers or databases. Your IoT devices, arguably, will likely connect into a private part of this network.
Route tables tell your network traffic where to go. They contain rules that dictate how packets are routed within your VPC and to destinations outside your VPC. An internet gateway, on the other hand, is a component that allows communication between your VPC and the public internet. For a secure IoT setup, you'll be very careful about what traffic actually goes through that internet gateway, as a matter of fact.
Security Groups and Network ACLs
These are your network's bouncers, remember? Security groups act like virtual firewalls for your instances (like EC2 servers) within your VPC. They control inbound and outbound traffic at the instance level. You define rules that say, "Allow traffic on port 22 (SSH) from this specific IP address" or "Allow all outbound traffic." It's very granular control, actually.
Network Access Control Lists, or Network ACLs, work at the subnet level. They are stateless, meaning they don't remember previous connections, and they apply to all instances within a subnet. Network ACLs give you another layer of security, acting as a broad filter for traffic entering or leaving a subnet. Using both security groups and Network ACLs gives you a really robust defense, so, you know, it's a good idea to set them up carefully.
Connecting Your Pi to the VPC
This is where the magic happens – getting your Raspberry Pi to actually talk to your AWS server securely inside that private VPC. There are a few good ways to do this, and the best choice might depend on your specific project needs, you know, and how your system is set up.
VPN Options: OpenVPN or AWS Client VPN
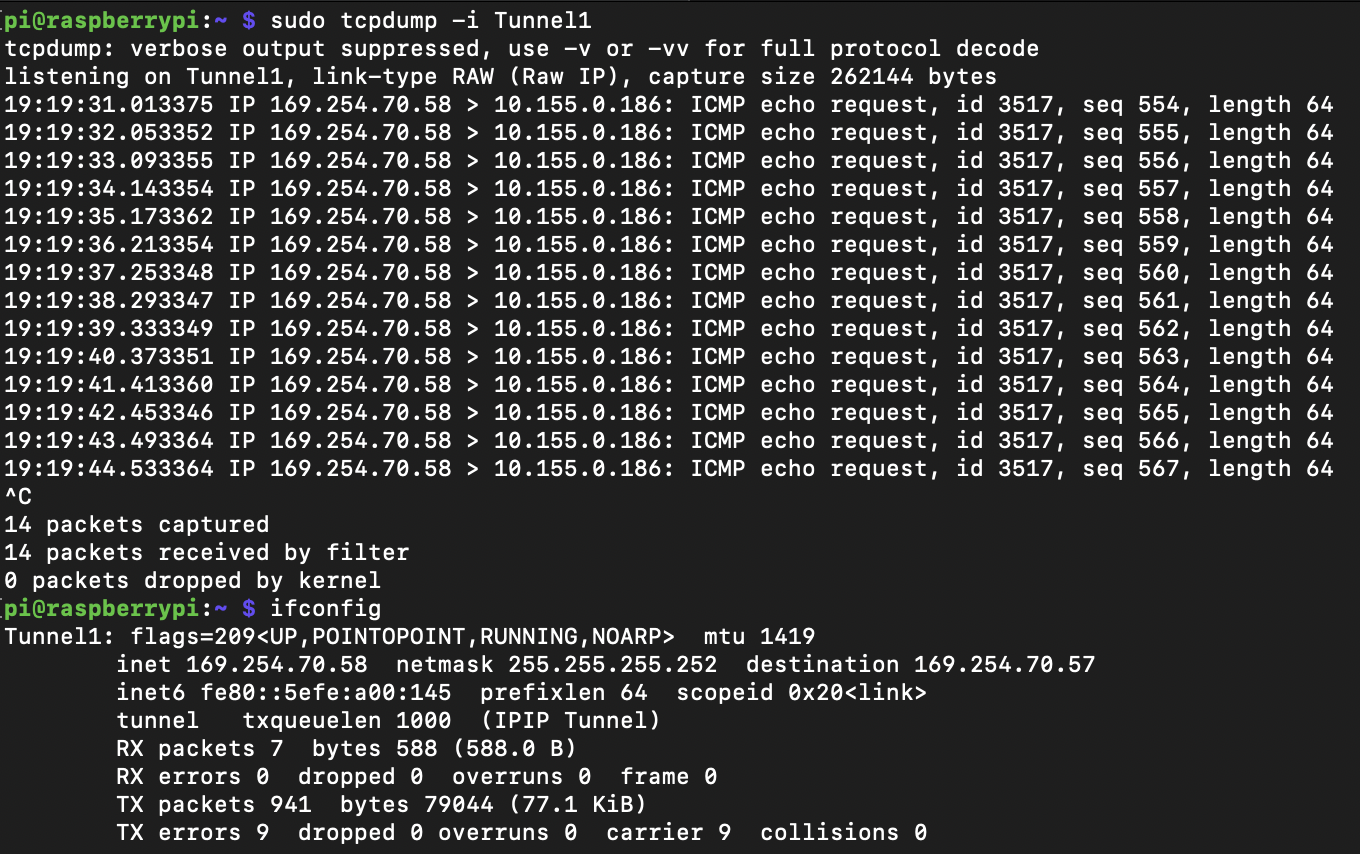
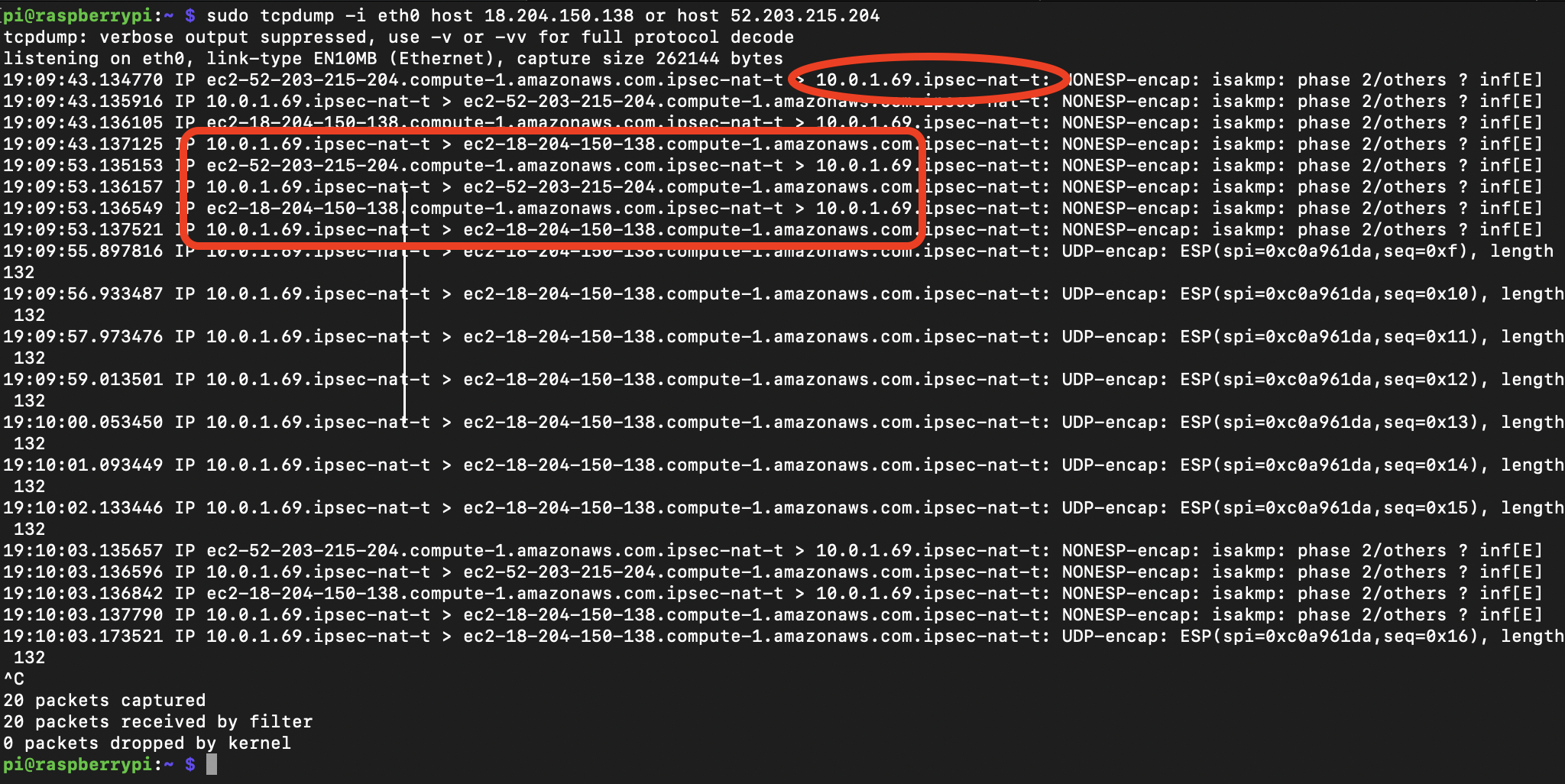
One common way to connect a remote device like a Raspberry Pi to a VPC is by using a Virtual Private Network, or VPN. A VPN creates an encrypted tunnel over the public internet, making it feel like your Pi is directly on your VPC network. You could set up an OpenVPN server inside your VPC, perhaps on an EC2 instance, and then install the OpenVPN client on your Raspberry Pi. This creates a secure, private link.
Alternatively, AWS offers a service called AWS Client VPN. This is a managed service, which means AWS handles a lot of the server setup for you. You configure the Client VPN endpoint in your VPC, and then your Raspberry Pi uses a Client VPN application to connect. This can be a simpler option, especially if you want to avoid managing a VPN server yourself. Both methods provide that crucial encrypted connection, preventing those "untrusted connection" warnings, which is what we want, pretty much.
Using AWS IoT Core with VPC Endpoints
For your Raspberry Pi to securely connect remote IoT VPC Raspberry Pi AWS server, consider using a VPC endpoint for AWS IoT Core. This is a really elegant solution, actually. AWS IoT Core is a service that lets your IoT devices easily and securely connect to AWS. Normally, devices connect to IoT Core over the public internet.
However, by using a VPC endpoint, your Raspberry Pi can connect to IoT Core directly through your VPC, entirely bypassing the public internet. This means your data never leaves the AWS network, which is a huge boost for security. It's like having a private, dedicated road for your IoT data, rather than sending it on the main highway. This approach offers a very high level of security and privacy for your IoT communications, which is really quite good.
IAM Roles and Policies for IoT Devices
Even with a secure connection, you need to control what your Raspberry Pi is allowed to do once it's connected to AWS. This is where AWS Identity and Access Management, or IAM, comes in. You should create specific IAM roles and policies for your IoT devices. These policies define exactly which AWS resources your Pi can access and what actions it can perform.
For example, a policy might allow your Pi to publish data to a specific AWS IoT topic but not to delete anything or access other services. This is called the principle of least privilege – giving your device only the permissions it absolutely needs to do its job, and nothing more. It's a fundamental security practice that helps limit potential damage if a device were ever compromised, so, you know, it's very important to get this right.
Best Practices for Ongoing Security
Setting up your secure connection is a big first step, but security is an ongoing effort, really. You can't just set it and forget it. To keep your remote IoT Raspberry Pi and AWS server safe over time, you need to follow some consistent practices, which is something people often overlook, actually.
Regular Updates and Patching
Just like we talked about updating your Pi's operating system, you need to keep everything else updated too. This includes any software running on your Pi, client applications for VPNs, and even the firmware on your Raspberry Pi itself. On the AWS side, while AWS manages a lot of the underlying infrastructure, you're responsible for keeping your EC2 instances (if you're using them) and application code updated.
Security vulnerabilities are discovered all the time, and software updates usually contain fixes for these issues. Neglecting updates is a common reason why devices become vulnerable, which can lead to problems like "Your device is at risk because it's out of date and missing important security and quality updates." You want to avoid that, so, regularly checking for and applying updates is, arguably, a pretty essential habit.
Monitoring and Logging
Knowing what's happening with your devices and your AWS environment is crucial for security. Set up monitoring for your Raspberry Pi devices to track their activity, resource usage, and network connections. On AWS, services like CloudWatch and CloudTrail can help you monitor your VPC, IoT Core, and other AWS resources. CloudTrail, for instance, logs API calls, so you can see who did what, when, and from where.
If something unusual happens, like a sudden spike in data transmission from a Pi or an unauthorized access attempt, your monitoring systems should alert you. This allows you to react quickly to potential security incidents. It's like having a security camera system for your digital assets, which is pretty useful, you know, for peace of mind.
Least Privilege Principle
We touched on this with IAM roles, but it applies more broadly. Always give your devices, users, and applications only the minimum permissions they need to perform their tasks. If a Raspberry Pi only needs to send data, don't give it permission to delete resources. If a user only needs to view logs, don't give them administrative access.
Regularly review your IAM policies and security group rules to make sure they are still appropriate. As your project grows or changes, permissions might need to be adjusted, but always default to the least privilege. This practice significantly reduces the "blast radius" if a component is ever compromised. It's a very simple but incredibly effective security concept, actually, and something you should always keep in mind.
Learn more about secure connections on our site, and link to this page for AWS IoT Core best practices.
Frequently Asked Questions (FAQs)
Here are some common questions people ask about connecting IoT devices securely:
How can I secure my Raspberry Pi IoT device?
You can secure your Raspberry Pi by changing default credentials, keeping its operating system and software updated, using strong passwords or SSH keys, and enabling a firewall. Also, only install software you really need, which is a pretty good idea, actually.
What is the best way to connect a Raspberry Pi to AWS?
The best way often involves using a Virtual Private Cloud (VPC) for isolation, combined with either a VPN connection (like OpenVPN or AWS Client VPN) or, even better, using AWS IoT Core with a VPC endpoint. These methods ensure your data travels over a private, encrypted path, so, you know, it's very safe.
Do I need a VPC for my IoT devices on AWS?
While not strictly mandatory for every single IoT project, using a VPC is very, very strongly recommended for most production IoT deployments. It provides a private, isolated network environment that significantly boosts security, control, and compliance for your devices and data, which is pretty important, at the end of the day.
Conclusion
Connecting remote IoT devices, like a little Raspberry Pi, to a big cloud setup, like an AWS virtual private cloud (VPC), can feel like a tricky puzzle, but it's absolutely doable with the right steps. We've gone through how to set up your Pi, create a private network on AWS, and establish those secure links. From hardening your Raspberry Pi to using VPC endpoints for AWS IoT Core, you've got a solid framework now.
Remember, the goal is to make sure your important data gets from one place to another without any "untrusted connection" warnings. By putting these practices into action, you're not just connecting devices; you're building a reliable, secure foundation for your IoT projects. It’s about getting you back on track so your windows, or rather, your connections, can run more securely, which is a pretty good feeling, you know.
- Pisces Leo Rising
- Who Is Axl Roses Partner Now
- Was Miranda Actually Pregnant In Satc
- Kenny Wayne Shepherd Net Worth
- Does Jeff Bridges Have Dentures

Detail Author:
- Name : Prof. Adella Oberbrunner DVM
- Username : sonya.kuhic
- Email : ewalsh@schaden.org
- Birthdate : 1996-04-08
- Address : 3416 Sanford Hill Lake Eldora, IL 15310
- Phone : +1-484-769-6848
- Company : Hane, Ondricka and Ebert
- Job : Septic Tank Servicer
- Bio : Occaecati est saepe alias. Qui nobis repudiandae voluptatibus et mollitia in. Rerum consequatur ea laboriosam qui. In occaecati nihil aut architecto.
Socials
linkedin:
- url : https://linkedin.com/in/remington7832
- username : remington7832
- bio : Dolorem voluptatem nulla aut repudiandae.
- followers : 4093
- following : 2310
tiktok:
- url : https://tiktok.com/@remingtonconroy
- username : remingtonconroy
- bio : Et voluptates et et fugit omnis harum.
- followers : 1536
- following : 360
instagram:
- url : https://instagram.com/conroy2016
- username : conroy2016
- bio : Sit sequi est sed et recusandae dolores non. Non accusantium quis non pariatur asperiores at.
- followers : 6437
- following : 1235
twitter:
- url : https://twitter.com/conroyr
- username : conroyr
- bio : Fugiat ut omnis eum doloribus et officiis repellendus. Incidunt ea nemo debitis. Nobis ad temporibus illum eveniet. Ad est officiis quas quas autem aliquid et.
- followers : 5665
- following : 1551
facebook:
- url : https://facebook.com/remington_real
- username : remington_real
- bio : Nostrum corporis a dolorem soluta esse omnis.
- followers : 1171
- following : 2433