Many people, you know, often find themselves wrestling with tech issues that make them feel a bit unsure about their online safety. Perhaps you have seen messages pop up saying a connection is "untrusted," or maybe your computer warns that it is "at risk" because of missed updates, that kind of thing. These moments, actually, show just how much we need reliable and safe ways for our devices to talk to each other, especially when we are dealing with things like securely connecting remote IoT for P2P downloads. It is a big deal to make sure our smart gadgets can share information without opening doors to trouble.
Think about the little frustrations, too, like when a file saves as a "crdownload" and does not appear in the right format, or when legitimate emails get blocked by Outlook, which is pretty annoying. These small hiccups, you see, reflect a larger need for systems that just work, and work safely. When we talk about remote IoT devices, which are often out in the wild, far from our direct control, that need for safety and smooth operation becomes even more important, very much so.
This article will explore how to securely connect remote IoT devices for P2P downloads. We will look at the challenges involved and, you know, some practical ways to keep your data and gadgets safe. We will discuss methods to help prevent those "untrusted connection" warnings from ever showing up for your smart devices, and make sure your IoT network is, well, pretty solid. Let us get into how to make sure your remote IoT P2P downloads are safe and sound, basically.
- Jake Plummer Net Worth
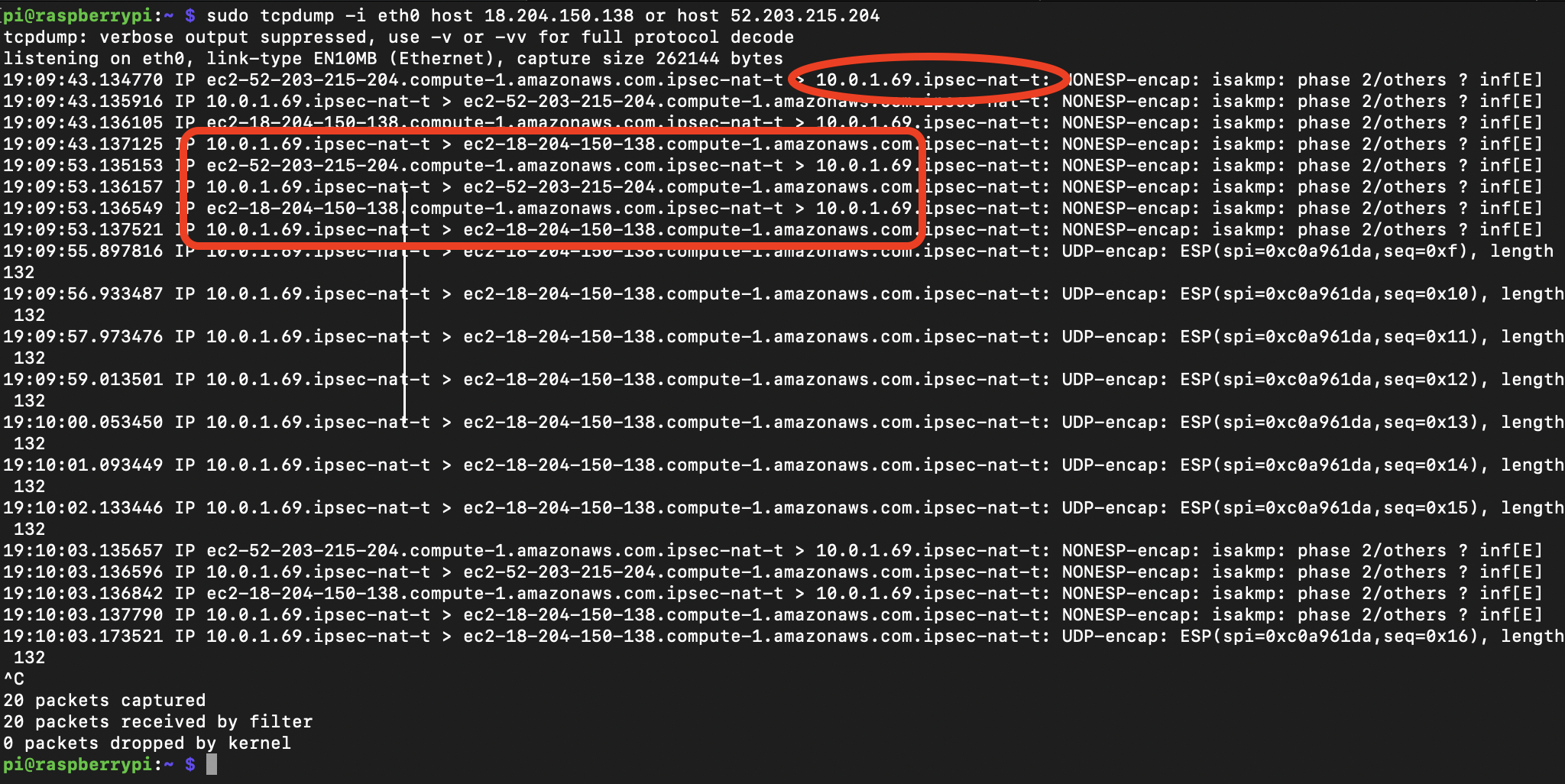
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Free
- Venus In 8th House Synastry
- Rebecca Gormley Onlyfans Leak
- Jude Bellingham Religion
Table of Contents
- The Growing Need for Secure IoT Connections
- What Makes P2P Connections for IoT Risky?
- Key Ways to Securely Connect Remote IoT P2P Download
- Tools and Approaches for Safer IoT P2P
- Best Practices for Setting Up Secure IoT P2P
- Frequently Asked Questions (FAQ)
- Conclusion
The Growing Need for Secure IoT Connections
More and more, our homes and businesses are filled with smart devices, from security cameras to thermostats, all needing to talk to each other and to us, too. These Internet of Things (IoT) gadgets often sit far from our main computers, sometimes in different buildings or even cities. This distance, actually, means they need to connect remotely, and often they do this by sharing files or data directly with each other, which is what we call P2P, or peer-to-peer. It is a convenient way to move information around, very much so.
However, this convenience brings its own set of concerns, as many people have learned the hard way. For instance, just like when someone sees a message that their browser is "managed by an organization" when it should not be, or when a device is "out of date and missing important security" patches, IoT devices face similar, if not greater, risks. An insecure connection for a remote IoT device could mean anyone might get access to your data, or even control your device, you know, which is pretty serious.
The core idea of securely connecting remote IoT for P2P downloads is to make sure that when these devices share information, they do so in a way that keeps out unwanted visitors and protects the data itself. It is about building a trusted path for your smart gadgets, so you do not have to worry about "untrusted connection" warnings popping up, or worse, someone messing with your system. This is, in a way, about giving you peace of mind, basically.
- Kevin Hunter Jr Net Worth
- Jeffrey Katzenberg Net Worth
- Bhad Bhabie Of Leaks
- Margarett Qualley Nudes
- Doug Clifford
What Makes P2P Connections for IoT Risky?
When IoT devices connect directly, peer-to-peer, they bypass central servers that often add a layer of safety. This direct link, while efficient, can be a bit like leaving your front door unlocked if you are not careful. Think about the times people get those "This connection is untrusted" messages, like when trying to reach a mail server or a website. That same kind of vulnerability can exist, actually, for IoT devices trying to talk to each other, very much so.
One big risk is that if one device on the P2P network is not secure, it can become a weak point. An attacker might get into that single device and then, you know, use it to access all the other devices it connects with. This is similar to how a computer that is "out of date and missing important security and quality updates" can put your whole system at risk. An old, unpatched IoT device can be a real problem, pretty much.
Another concern comes from the data itself. If your IoT devices are downloading updates or sharing sensitive information P2P, and that connection is not protected, the data could be intercepted or changed. Imagine trying to save a file from Microsoft Edge only for it to turn into a "crdownload" file, not in the correct format. Now, think about that happening with a critical firmware update for your smart home; that could be, well, a disaster. So, it is clear that safety is a must.
Key Ways to Securely Connect Remote IoT P2P Download
Making sure your remote IoT P2P downloads are safe involves several important steps. It is not just one thing, but rather a combination of methods that work together, you know, to build a strong shield. Each part plays a role in keeping your devices and your data safe from harm, very much so.
Strong Encryption for Data Privacy
Encryption is, in a way, like putting your data into a secret code that only the right devices can read. When your IoT devices send information to each other over a P2P link, this data needs to be scrambled. If someone were to intercept it, all they would see is gibberish, which is pretty good. This helps keep your private information private, you know, so it does not fall into the wrong hands.
Without proper encryption, any data shared during a P2P download could be exposed. This is similar to the worry people have when they see "This connection is untrusted" messages; it means the data traveling over that link might not be safe. For IoT, strong encryption means that even if someone manages to tap into the connection, they cannot understand what is being sent, which is actually a big relief.
Device Identity and Authentication
Before any two IoT devices start sharing data P2P, they need to make sure they are talking to the right partner. This is called authentication, and it is about verifying each device's identity. It is like checking an ID card before letting someone into a secure area, you know, to prevent imposters. Each device should have a unique digital fingerprint, so to speak, that proves it is who it says it is, basically.
If devices cannot properly authenticate each other, a malicious device could pretend to be a legitimate one. This could lead to unauthorized downloads or uploads, similar to how "legitimate email is being blocked by Outlook" can cause problems, but in this case, it is about allowing bad data in. Proper authentication ensures that only trusted devices are part of your P2P network, which is, well, pretty important.
Access Control and Authorization
Even after a device is authenticated, it should not automatically have permission to do everything. Access control means deciding what each device is allowed to do, or what data it can access. For example, a smart light bulb might only need to receive commands to turn on or off, not download sensitive files from a security camera. This is about giving devices just enough permission to do their job, and no more, you know.
This idea is a bit like when someone wants to "password protect a file in SharePoint" but not the entire folder. You want to control access at a very specific level. For remote IoT P2P downloads, authorization makes sure that a device only downloads what it is supposed to, and from sources it is allowed to. This helps prevent accidental data leaks or unauthorized data transfers, which is actually a good thing.
Firmware Integrity and Secure Boot
The "firmware" is like the basic operating system of an IoT device. If this firmware is tampered with, the whole device becomes untrustworthy. Secure boot is a process that checks the firmware every time the device starts up, making sure it has not been altered. If it finds any changes, it will not let the device start, you know, which is a pretty good safety measure.
This helps protect against situations where a device might be "at risk" because its core software has been compromised. If a P2P download involves updating a device's firmware, it is very important that the new firmware is also verified as legitimate and untampered. This ensures that even the updates themselves are safe, preventing malicious code from being introduced, which is, well, pretty crucial.
Network Separation and Firewalls
Keeping your IoT devices on their own separate network, or at least using firewalls to control their traffic, adds another layer of protection. This means that if one IoT device gets compromised, it is harder for the problem to spread to your other devices or your main home network. It is about creating boundaries, basically, so problems stay contained.
Think of it like having different rooms in a house, with fire doors between them. If a fire starts in one room, it does not immediately spread to the others. For remote IoT P2P, firewalls can help control which devices can connect to each other and what kind of data they can exchange, you know, preventing unauthorized connections that might otherwise lead to "untrusted" situations. This is a practical step, very much so.
Keeping Devices Up-to-Date
Just like your computer needs "important security and quality updates" to run securely, IoT devices need regular updates too. These updates often fix security holes that attackers could use to get in. An outdated device is, well, a tempting target. Making sure your remote IoT devices can receive and install these updates securely, perhaps even through P2P, is very important, actually.
Many people have issues with updates, like an "update that keeps trying to reinstall and fails," or a computer getting "stuck in this automatic repair loop" after updates. For IoT, a failed or insecure update can be even worse, potentially rendering a device useless or, you know, opening it up to attacks. A secure P2P download system for updates helps ensure that the correct, verified updates reach the devices reliably, which is a good thing.
Tools and Approaches for Safer IoT P2P
To really securely connect remote IoT for P2P downloads, we often rely on specific tools and ways of doing things. These methods help put the key security principles into action, making the whole process much safer, you know, for everyone involved. It is about choosing the right ingredients for a safe system, basically.
Using Secure Communication Protocols
When devices talk to each other, they use "protocols," which are like rules for communication. For secure P2P, protocols such as TLS (Transport Layer Security) or DTLS (Datagram Transport Layer Security) are very helpful. These protocols include encryption and authentication as part of their design, so, you know, the connection is protected from the start. They help prevent those "untrusted connection" warnings by building trust right into the communication itself, very much so.
Using these protocols means that data exchanged during a P2P download is automatically scrambled and verified. It is a foundational layer of safety that makes sure the messages sent between your IoT devices are both private and authentic. This is, in a way, a standard practice for keeping online interactions safe, and it applies just as much to your smart gadgets, actually.
Virtual Private Networks (VPNs)
A VPN creates a secure, encrypted "tunnel" over a public network. You can use VPNs to connect your remote IoT devices to each other or to a central server in a very safe way. Even if the underlying internet connection is not secure, the data inside the VPN tunnel remains protected. This is a bit like sending a private message inside a locked box, you know, where only the sender and receiver have the key.
For securely connecting remote IoT for P2P downloads, a VPN can provide an extra layer of privacy and integrity. It helps hide the actual IP addresses of your devices, making it harder for outsiders to find and target them. This can be especially useful for devices that are physically far apart and need to communicate over potentially insecure public Wi-Fi networks, which is, well, pretty common.
Decentralized Trust Systems
Some newer approaches use decentralized systems, sometimes involving blockchain-like technologies, to manage trust among IoT devices. Instead of relying on one central authority to say which devices are trustworthy, the trust is distributed across the network. Each device can verify the identity and permissions of others without needing a single point of control. This can be, you know, a very resilient way to manage security.
This kind of system helps prevent a single point of failure. If one part of the system goes down or is compromised, the rest of the network can still function securely. It offers a fresh perspective on how devices can authenticate each other and ensure the integrity of P2P downloads, making the overall system stronger against various types of attacks, which is actually pretty clever.
Best Practices for Setting Up Secure IoT P2P
Beyond the technical tools, there are some everyday good habits that help keep your remote IoT P2P downloads safe. These are practical steps you can take to make sure your system is as secure as possible, you know, minimizing potential risks. It is about being smart and careful with your connected gadgets, basically.
Change Default Passwords: This might seem obvious, but many IoT devices come with easy-to-guess default passwords. Always change these to strong, unique passwords right away. An easy password is, well, an open invitation for trouble.
Regularly Check for Updates: Make it a habit to look for firmware updates for all your IoT devices. Install them as soon as they are available. This helps fix security holes before they can be exploited, which is, you know, a very important part of staying safe.
Limit Device Access: Configure your devices so they only have access to what they absolutely need. If a smart light bulb does not need internet access, do not give it any. This reduces the ways an attacker could get in, actually.
Monitor Network Activity: Keep an eye on the traffic going to and from your IoT devices. Unusual activity could signal a problem. There are tools that can help you do this, giving you a heads-up if something seems off, which is, well, pretty useful.
Buy from Trusted Brands: Stick to reputable manufacturers for your IoT devices. These companies are generally more likely to prioritize security and provide regular updates. Choosing wisely at the start can save a lot of headaches later, you know.
Understand Your Device Settings: Take the time to learn about the security settings on your IoT devices. Many devices have options you can adjust to make them more secure, but you have to know they are there, basically. This helps you gain more control, very much so.
Frequently Asked Questions (FAQ)
What makes P2P connections for IoT risky?
P2P connections for IoT can be risky because they often bypass central security measures, making individual devices more exposed. If one device is not secure, it can become a way for unauthorized people to access the entire network, you know, like a weak link in a chain. Also, data shared without proper protection can be intercepted or changed, which is, well, pretty concerning.
How can I protect my IoT devices during P2P downloads?
You can protect your IoT devices during P2P downloads by using strong encryption for all data, making sure devices properly identify each other through authentication, and setting clear rules for what each device can do with authorization. Also, keeping device firmware safe with secure boot and regularly applying updates are very important steps, you know, to keep things safe.
Are there specific protocols for secure IoT P2P data transfer?
Yes, there are specific protocols that help make IoT P2P data transfer secure. Protocols like TLS (Transport Layer Security) and DTLS (Datagram Transport Layer Security) include built-in encryption and authentication features. Using these helps ensure that the data exchanged between devices is both private and verified, preventing those "untrusted connection" warnings from ever appearing, which is, well, pretty good. Learn more about IoT security on our site.
Conclusion
Making sure your remote IoT P2P downloads are safe is a very important part of using smart devices today. It means taking steps like encrypting your data, making sure devices prove who they are, and giving them only the access they need. Just like dealing with "untrusted connections" or "out of date" warnings on your computer, your IoT devices need constant care and attention to their safety, you know, for everything to work right.
By following these methods and using the right tools, you can create a much safer environment for your connected gadgets. This helps prevent many of the common security headaches people face with technology. It is about being proactive and thoughtful about how your devices communicate, which is, well, pretty smart in the long run. For more insights on keeping your smart home safe, you can also check out this IoT security guidance.
So, take a moment to review the security of your own IoT setup. Are your devices updated? Are they using strong passwords? Thinking about these things now can save you a lot of trouble later, ensuring your remote IoT P2P downloads happen securely and reliably, every time. You can find more helpful information about device safety on this page.
- Is Jen Mueller Still Married
- Itsbbykota Leak
- Jules Ari Onlyfans Leak
- Raspberry Pi Remote Iot Free
- Jasonliv


Detail Author:
- Name : Dr. Joseph Johnston
- Username : glowe
- Email : dante.keeling@franecki.org
- Birthdate : 2004-11-24
- Address : 82644 Barbara Hills West Reubenland, NY 65607-4141
- Phone : +1-458-815-2195
- Company : Feest-Ortiz
- Job : Audiologist
- Bio : Distinctio non debitis ut tempore quisquam. Facere omnis facere soluta dolores vero nostrum. Qui incidunt ullam praesentium perferendis. Ad sit ut est labore.
Socials
tiktok:
- url : https://tiktok.com/@hallie795
- username : hallie795
- bio : Beatae quam saepe labore natus.
- followers : 2696
- following : 1076
linkedin:
- url : https://linkedin.com/in/hallie.marquardt
- username : hallie.marquardt
- bio : Dignissimos odit dolorum voluptate quae ab.
- followers : 353
- following : 479
instagram:
- url : https://instagram.com/marquardt2005
- username : marquardt2005
- bio : Eum consectetur quis quae ea sint ipsum. Officia unde et facere iste. Et commodi harum explicabo.
- followers : 178
- following : 2445
facebook:
- url : https://facebook.com/hallie_marquardt
- username : hallie_marquardt
- bio : Repellat et accusamus impedit et sit eos et.
- followers : 406
- following : 2540