Building connected devices, especially with something as versatile as a Raspberry Pi, opens up a world of possibilities, yet it also brings a serious need for strong security. It’s a bit like building a house; you want to make sure the doors and windows are locked up tight, don't you? Many folks, like those who might see an "untrusted connection" warning pop up on their screen, or find their system stuck in an update loop, really understand the headache that comes from things not being quite right. This article is all about making sure your remote IoT projects, especially those using a Raspberry Pi and AWS, are not just working, but working safely and soundly.
You see, when you put a Raspberry Pi out there, maybe gathering data from a garden or monitoring equipment far away, it's essentially a door into your system. If that door isn't properly guarded, it can leave your whole setup open to problems, perhaps even like those frustrating moments when a device is "at risk because it's out of date and missing important security updates." We want to avoid that feeling of vulnerability, and that, is what we will explore together.
This guide will show you how to truly protect your devices and their information. We'll look at how to set up a private, protected space using an AWS Virtual Private Cloud (VPC), how to get your Raspberry Pi talking to it safely, and how to keep everything updated and secure. You'll get practical advice, so you can feel good about your remote IoT setup, knowing it's built on a solid foundation, which is quite important, actually.
- Teyana Taylor Ethnicity
- Jameliz Benitez Onlyfans Leaked
- Dick Van Dyke
- Thandie Newton Worth
- Ben Soffer Birthday
Table of Contents
- The Big Picture: Why Secure IoT Connections Matter
- Understanding Your Tools: Raspberry Pi, AWS, and VPC
- Setting Up Your Secure Foundation: AWS VPC Basics
- Connecting Your Raspberry Pi to the VPC
- Securing Your IoT Data with AWS IoT Core
- Implementing Robust Device Security on Your Raspberry Pi
- Keeping Things Safe: Ongoing Security Practices
- Common Questions About Secure IoT Connections
The Big Picture: Why Secure IoT Connections Matter
Imagine you have a small computer, a Raspberry Pi, doing something really helpful far away from you. It might be checking the temperature in a greenhouse or keeping an eye on water levels. For this little device to send its information back to you, it needs to connect to the internet, and that, is where things can get a bit tricky. Just like how you might get a warning that "This connection is untrusted" when trying to visit a website, an insecure IoT connection can leave your data exposed, or even let unwanted people control your device. It's a real concern for many, you know.
We've all seen or heard about devices that, apparently, get stuck in loops or just stop working right after an update. Sometimes, it's because the system itself wasn't quite ready for the change, or perhaps the update process wasn't secure. For IoT, this means not only a loss of data but also the potential for someone to take over your device. That could be used for all sorts of mischief, or even to cause bigger problems, which is something nobody wants, really.
Think about the times you've had a device tell you it's "at risk because it's out of date and missing important security and quality updates." That message, it’s a clear signal that protection is needed. For IoT, this is even more critical because these devices often operate without much direct oversight. Ensuring a secure connection from the start helps prevent these headaches and keeps your project running smoothly, which is a pretty good goal, don't you think?
Understanding Your Tools: Raspberry Pi, AWS, and VPC
Before we get into the "how-to," let's just quickly go over the main players here. First, there's the Raspberry Pi. It's a small, affordable computer that's really popular for all sorts of projects, from learning to code to building smart home gadgets. It's powerful enough to run many tasks and, arguably, quite flexible for remote work.
Then we have Amazon Web Services, or AWS. This is a huge collection of cloud computing services. It lets you store data, run applications, and manage your devices over the internet, without needing to own all the big, expensive hardware yourself. It's a very robust platform, offering many tools that, in a way, help manage remote operations.
Finally, there's the Virtual Private Cloud, or VPC. You can think of a VPC as your own private, isolated section within the AWS cloud. It's like having your own dedicated, locked-off room in a very large building. You get to decide who comes in and out, and what goes on inside. This is where your Raspberry Pi will connect, creating a secure space for its operations, which is quite handy, actually.
Why use a VPC for IoT?
Using a VPC for your IoT devices, especially a Raspberry Pi, offers a significant layer of security. It helps you control network access, which is something many people want when they are trying to "lock down" their systems, perhaps like those who want to restrict email access to certain IPs. Without a VPC, your Raspberry Pi might be directly exposed to the wider internet, which is a bit like leaving your front door wide open, you know.
Within a VPC, you can set up strict rules about what kind of traffic can reach your Raspberry Pi and what it can connect to. This means you can greatly reduce the chances of unwanted access or attacks. It also lets your devices communicate with other AWS services in a private way, without their data ever having to travel across the public internet, which is a pretty big deal for security, too.
This private network setup helps prevent many common security problems. It makes it much harder for malicious actors to even find your device, let alone try to get into it. It's a foundational step for building a truly secure remote IoT system, and that, is something we should all aim for, really.
Setting Up Your Secure Foundation: AWS VPC Basics
Getting your VPC ready is the first major step to securely connect remote iot vpc raspberry pi aws. It's about drawing the boundaries for your private network. You'll start by creating the VPC itself, which defines the range of IP addresses your network will use. This is a bit like deciding the street number range for your new neighborhood, so to speak.
Within your VPC, you'll set up subnets. These are smaller divisions of your network. It's usually a good idea to have both public and private subnets. Public subnets can reach the internet, while private subnets are isolated, which is rather important for keeping your IoT devices safe. Your Raspberry Pi will typically reside in a private subnet, which is a good practice, in a way.
You'll also need an Internet Gateway for your public subnets to talk to the internet, and a NAT Gateway in a public subnet for your private subnets to get out to the internet for updates, without being directly exposed. This setup helps ensure that while your Raspberry Pi can fetch updates, it doesn't just sit out there for anyone to find. It's a key part of the puzzle, actually.
Configuring Network Access Control Lists (NACLs) and Security Groups
NACLs and Security Groups are like the bouncers and security guards for your VPC. NACLs operate at the subnet level, deciding what traffic can enter or leave an entire subnet. They are stateless, meaning they don't remember previous connections, so you need rules for both incoming and outgoing traffic. This offers a broad layer of protection, you know.
Security Groups, on the other hand, act at the instance level, meaning they protect individual Raspberry Pi devices or other AWS resources. They are stateful, so if you allow traffic in, the response traffic is automatically allowed out. This is a more granular way to control who can talk to your Pi. You'll want to set these up very carefully, only allowing the necessary connections, which is pretty much like only giving keys to trusted people, really.
When setting up your Security Groups for your Raspberry Pi, think about what it absolutely needs to communicate with. Does it need to send data to AWS IoT Core? Yes. Does it need to accept incoming connections from anywhere on the internet? Probably not. Being strict with these rules helps keep your device safe, much like how you might want to "password protect a file" rather than leaving it open for anyone to see, which is quite sensible, apparently.
Connecting Your Raspberry Pi to the VPC
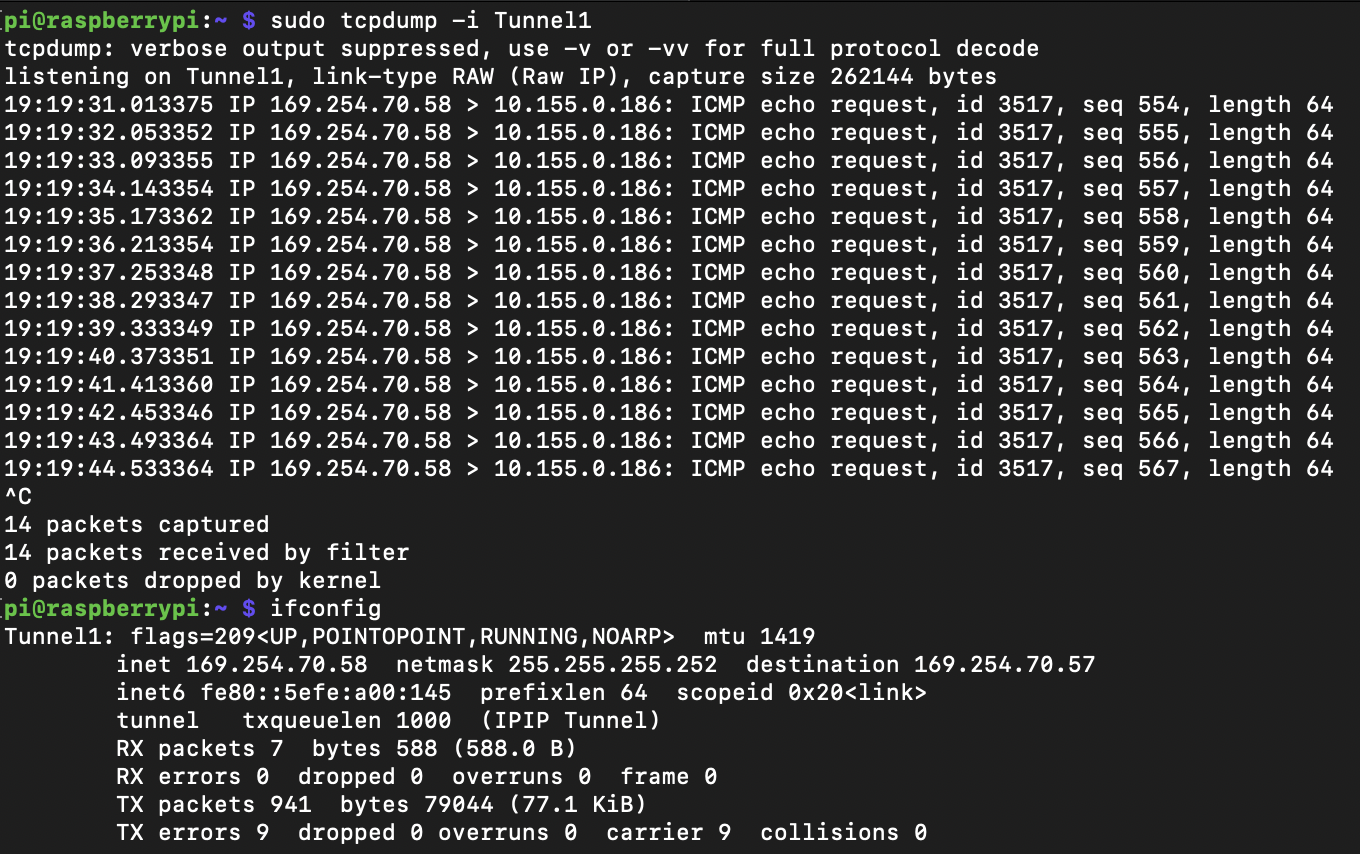
Getting your Raspberry Pi into your private AWS VPC is a crucial step for securely connect remote iot vpc raspberry pi aws. There are a few ways to do this, but a common and very secure method involves using a VPN connection. This creates a secure tunnel from your Raspberry Pi to your VPC, so all its communication is encrypted and protected, which is a big plus, too.
You can set up a client-side VPN on your Raspberry Pi that connects to a VPN server you run within your VPC. This server could be an EC2 instance running OpenVPN or a similar solution. This way, your Pi appears as if it's directly inside your private network, even if it's physically located somewhere else. It's a pretty neat trick, in a way.
Another approach, especially for larger deployments, might involve AWS IoT Greengrass, which extends AWS capabilities to your edge devices. However, for a single Raspberry Pi, a direct VPN connection is often simpler and very effective for establishing that secure link. You'll want to make sure the VPN client on your Pi is configured correctly, and that, is a key part of making it all work, you know.
Setting up a VPN Client on Raspberry Pi
To get your Raspberry Pi connected via VPN, you'll need to install VPN client software on it. OpenVPN is a popular choice and, arguably, quite reliable. First, make sure your Raspberry Pi's operating system is up-to-date, which helps prevent those "device is at risk" messages. You can do this with simple commands in the terminal, like `sudo apt update` and `sudo apt upgrade`, which is a good habit to get into, actually.
Next, you'll install the OpenVPN client. Once installed, you'll need the configuration files from your VPN server in your AWS VPC. These files tell your Raspberry Pi how to connect to the server securely, including the server's address and any necessary certificates or keys. It's a bit like giving your Pi the secret handshake to get into your private club, so to speak.
Once the configuration is in place, you can start the OpenVPN service on your Raspberry Pi. After a successful connection, your Pi will have an IP address within your VPC's private range, and all its traffic will flow through the secure VPN tunnel. This means your data is protected from eavesdropping and tampering, which is a very important aspect of security, don't you think?
Securing Your IoT Data with AWS IoT Core
Even with your Raspberry Pi in a VPC, you'll likely want it to communicate with other AWS services, especially AWS IoT Core, which is designed for managing IoT devices and their data. AWS IoT Core provides a secure, two-way communication channel between your devices and the AWS cloud. It's a very powerful tool for collecting, processing, and acting on data from your IoT fleet, and that, is quite useful, you know.
The core of AWS IoT Core security lies in its use of X.509 certificates and policies. Each Raspberry Pi device should have its own unique certificate, which it uses to authenticate itself to AWS IoT Core. This is a much stronger form of identification than a simple username and password, helping to prevent unauthorized devices from connecting, which is a common problem, apparently.
AWS IoT policies define what actions a device is allowed to perform. For instance, a policy might say your Raspberry Pi can publish data to a specific topic but cannot subscribe to others, or it can only update its own "device shadow." Being very specific with these policies helps limit the damage if a device ever gets compromised, which is a sensible precaution, really.
Registering Your Raspberry Pi with AWS IoT Core
To get started, you'll need to register your Raspberry Pi as a "thing" in AWS IoT Core. This involves creating a unique name for your device. Then, you'll generate a set of device certificates and keys. These are critical for the secure connection, so you'll need to handle them with great care, much like you'd protect sensitive documents, actually.
You'll download these certificates and keys and securely transfer them to your Raspberry Pi. It's very important that these files are never exposed or shared publicly. Think of them as the unique credentials that prove your Raspberry Pi is who it says it is. Losing them, or having them stolen, could lead to serious security problems, which is something nobody wants, you know.
Finally, you'll attach an AWS IoT policy to your device's certificate. This policy, as mentioned, specifies what your Raspberry Pi is permitted to do within AWS IoT Core. By carefully crafting these policies, you ensure your device has just enough access to do its job, and no more, which is a fundamental principle of good security, and that, is quite important, you know.
Implementing Robust Device Security on Your Raspberry Pi
While the VPC and AWS IoT Core provide strong network and cloud security, the Raspberry Pi itself needs to be hardened. Just like how you might get a message saying "Your device is at risk because it's out of date," an unsecure Pi can be a weak link. This means paying attention to the operating system, user accounts, and local software, which is pretty important, actually.
Always change the default password for the `pi` user, or better yet, create a new user account and disable the `pi` user entirely. Using strong, unique passwords for any accounts on the device is a must. Consider using SSH keys for remote access instead of passwords, as they offer a much stronger form of authentication. This is a very basic but effective step, so to speak.
Keep the Raspberry Pi's operating system and all installed software up-to-date. Regular updates often include security patches that fix newly discovered vulnerabilities. This helps prevent situations where your system gets stuck or fails due to outdated components, which can be a real headache, you know. Automating these updates where possible can save you a lot of trouble, too.
Securing the Operating System and Software
Beyond basic updates, there are other steps you can take to secure your Raspberry Pi's operating system. Disable any services you don't need running on the device. Every open port or running service is a potential entry point for someone trying to get in. If your Pi is only sending data, it probably doesn't need a web server running, for example, which is quite sensible, apparently.
Consider using a read-only file system for your Raspberry Pi, especially if it's deployed in a very remote or critical environment. This prevents unauthorized changes to the system files and makes it harder for malicious software to persist. While it adds some complexity for updates, it greatly enhances security. It's a bit like putting a permanent lock on your important documents, so to speak.
Implement logging and monitoring on your Raspberry Pi. Knowing what's happening on your device, what processes are running, and what connections are being made can help you detect unusual activity early. Sending these logs to a central logging service in AWS can give you a better overview of your entire IoT fleet, which is a good practice, really.
Keeping Things Safe: Ongoing Security Practices
Setting up a secure connection for your Raspberry Pi in an AWS VPC is a fantastic start, but security isn't a one-time task. It's an ongoing process, much like how you might continually update your antivirus software or check for "missing important security and quality updates" on your computer. Regular attention helps keep your IoT project protected over time, and that, is quite important, you know.
Regularly review your AWS Security Groups and NACL rules. Are they still as restrictive as they need to be? Have new services been added that require different access? Periodically checking these settings helps ensure that no unnecessary doors are left open. It's a good habit to get into, actually.
Keep an eye on the latest security news and advisories for Raspberry Pi and AWS. New vulnerabilities are discovered all the time, and staying informed allows you to take proactive steps to protect your devices. This proactive approach helps avoid those frustrating moments when your "computer getting stuck in this automatic repair loop" after an update, because you're already prepared, you see.
Automating Updates and Monitoring
Manually updating every remote Raspberry Pi can be a huge task, so automating the update process is often a very good idea. You can use tools like AWS IoT Greengrass for over-the-air updates, or even simple scripts that check for and install updates regularly. This ensures your devices always have the latest security patches, which is a crucial part of keeping them safe, too.
Monitoring your devices for unusual activity is also key. AWS CloudWatch can collect logs and metrics from your VPC and IoT Core, allowing you to set up alarms for suspicious events. For example, if a Raspberry Pi suddenly tries to connect to an unusual IP address, you could get an alert. This helps you react quickly to potential threats, which is pretty much like having a watchful eye over your system, really.
Consider implementing a robust backup strategy for your Raspberry Pi's configuration and data. In the event of a security incident or device failure, having a recent backup means you can quickly restore your device to a known good state. This helps minimize downtime and data loss, which is a very sensible precaution, don't you think? Learn more about secure IoT practices on our site, and link to this page here for more details on AWS IoT security.
Common Questions About Secure IoT Connections
How do I connect my Raspberry Pi to AWS IoT securely?
To connect your Raspberry Pi to AWS IoT securely, you'll typically use X.509 certificates and unique device policies. Each Pi gets its own certificate and private key, which it uses to authenticate with AWS IoT Core. This ensures only authorized devices can communicate. All communications are then encrypted using TLS, which keeps your data private and protected, which is quite important, you know. You also want to make sure your Pi is in a secure network, perhaps like a VPC, to add another layer of protection.
What are the best practices for securing IoT devices in a VPC?
Securing IoT devices in a VPC involves several key steps. First, place your devices in private subnets, behind NAT Gateways, to prevent direct internet exposure. Use strict Security Groups and Network Access Control Lists (NACLs) to control all incoming and outgoing traffic, only allowing what's absolutely necessary. Implement a VPN for remote access to your Pi, ensuring all communication is encrypted. Keep your device's operating system and software updated, and use strong authentication methods, such as SSH keys, for access. This comprehensive approach helps create a very protected environment, which is a good idea, actually.
Can I use a Raspberry Pi for commercial IoT applications with AWS?
Yes, a Raspberry Pi can certainly be used for commercial IoT applications with AWS, provided you implement robust security and reliability measures. Its low cost and flexibility make it a popular choice for prototyping and even production deployments. However, for commercial use, you must ensure the device is securely provisioned, regularly updated, and integrated into a resilient cloud architecture like an AWS VPC with AWS IoT Core. This helps address concerns about scalability, security, and device management, which are very important for any business application, you know. It's all about building it right from the start, which is pretty much what we've been talking about, really.
For more detailed insights into general security practices, you might find this NIST Cybersecurity Framework quite helpful, as it outlines principles for managing cybersecurity risks.
- Cnbc Anchors Salaries
- Margarett Qualley Nudes
- Astarbabyxo Sex
- Alicia Vikander Net Worth 2025
- Olivia Brown Net Worth


Detail Author:
- Name : Dr. Antonio Shanahan
- Username : jonathan.ledner
- Email : rmaggio@hotmail.com
- Birthdate : 2002-02-14
- Address : 819 Parisian Freeway Suite 367 Dickiland, OK 66986
- Phone : 702-285-0370
- Company : Kuvalis-Turcotte
- Job : Tool Set-Up Operator
- Bio : Odit qui qui sit hic. Ut fugit sit sunt fugiat ipsam consequatur maxime. Occaecati repellendus officiis enim minus quam corrupti commodi.
Socials
tiktok:
- url : https://tiktok.com/@little1976
- username : little1976
- bio : Ex maiores occaecati quibusdam voluptatibus voluptatem.
- followers : 3095
- following : 564
instagram:
- url : https://instagram.com/roxanelittle
- username : roxanelittle
- bio : Et beatae ea dolor harum voluptatem. Est voluptatibus sit sed tenetur. Ducimus ut quam debitis.
- followers : 1184
- following : 1992
facebook:
- url : https://facebook.com/roxane.little
- username : roxane.little
- bio : Quia cupiditate necessitatibus saepe ut rerum.
- followers : 3957
- following : 81
twitter:
- url : https://twitter.com/roxanelittle
- username : roxanelittle
- bio : Ad qui odio a voluptas tempore eaque. Minima facere facere quis distinctio. Sed tenetur aut iste tempore adipisci rerum dignissimos.
- followers : 2433
- following : 915