Connecting to your IoT devices from a distance, especially those connected to the cloud, is a pretty big deal for many projects today. This means you can keep an eye on things and even make changes no matter where you are. Our focus here is on the remoteiot ssh aws example, showing you how to set up secure connections for your internet-connected gadgets using Amazon Web Services. It’s about making sure your devices are safe and always reachable, which, you know, is really quite handy.
You might be wondering just how to get started with this kind of setup, and that's fair enough. This whole process is your ticket to securely accessing and managing your IoT devices from anywhere in the world using Amazon Web Services (AWS), which is a big deal, as I was saying. We will explore how to use SSH (Secure Shell) on AWS (Amazon Web Services) to manage IoT devices securely, giving you practical insights and actionable advice. This guide aims to provide a comprehensive overview of how to utilize remoteiot VPC SSH for Raspberry Pi on AWS, ensuring a smooth and efficient remote management experience.
Whether you are just beginning with IoT or have some experience, this setup offers a reliable way to keep your devices running as they should. The remoteiot SSH AWS example acts as your compass, guiding you through the intricacies of establishing and maintaining secure SSH connections on AWS for your IoT gadgets. We will walk through everything you need to know about remotely SSHing into an IoT device using AWS, complete with practical examples and actionable steps, so you can feel pretty confident about it all.
- When Does Anna Faris Leave Mom
- सरवततम रमट मनटरग रसपबर पई
- Is Gigi Derrico Still Alive
- Abby Phillips
- Mydesinetcom
Table of Contents
- Understanding Remote IoT SSH and AWS
- Why Secure Remote Access Matters for IoT
- Getting Ready: Your Prerequisites for Remote IoT SSH AWS
- Setting Up Your Raspberry Pi for AWS IoT
- Establishing Secure Connections with AWS IoT
- Practical Examples and Use Cases
- Frequently Asked Questions About Remote IoT SSH AWS
- Taking the Next Steps with Your IoT Projects
Understanding Remote IoT SSH and AWS
IoT SSH control AWS refers to the use of Secure Shell (SSH) protocols to remotely access and manage IoT devices hosted on Amazon Web Services. This is, you know, a pretty fundamental part of keeping your connected things working well. SSH provides a secure channel over an unsecured network by using strong encryption, which is rather important for keeping your data safe. It allows you to run commands, transfer files, and manage your IoT devices as if you were right there with them, even when you are miles away, so that's a good thing.
When you combine SSH with AWS IoT, you get a really powerful combination for device management. AWS IoT Core is a managed cloud service that lets connected devices interact with cloud applications and other devices securely. This integration, you see, means that your devices can send data to AWS, and you can also send commands back to them, all through a secure link. It is like having a direct, private line to each of your devices, which is actually quite useful for maintaining control.
This setup, with the integration of AWS IoT, Virtual Private Cloud (VPC), and Secure Shell (SSH), allows users to securely access and manage their IoT devices from anywhere in the world. By leveraging SSH, developers can establish encrypted connections between IoT devices and AWS resources, ensuring data integrity and confidentiality. Remote IoT SSH AWS example demonstrates how to use SSH (Secure Shell) on AWS (Amazon Web Services) to manage IoT devices securely, which is, you know, the whole point.
- Sherri Papini Psych Evaluation
- May Mailman Husband
- Where Is Ovidio Guzman Now
- Abigail Lust Interview
- How To Use Remoteiot Behind Router Mac Free
Why Secure Remote Access Matters for IoT
Having secure remote access for your IoT devices is really important for a bunch of reasons. For one, it means you can troubleshoot problems without having to physically visit each device, which saves a lot of time and effort, especially if your devices are spread out. Imagine having sensors in different buildings or even different cities; you can, in a way, fix things from your desk, which is pretty neat.
Then there is the security aspect, which is, you know, a very big deal. IoT devices can sometimes be targets for bad actors, so making sure your connections are encrypted is a must. SSH provides that layer of protection, keeping your data private and preventing unauthorized access to your devices. This means your smart garden or your industrial sensors are not just connected, but they are also, actually, protected, which is a big relief.
Also, secure remote access allows for regular updates and maintenance. You can push out software patches, update configurations, or even install new features on your devices without any fuss. This helps keep your IoT ecosystem running smoothly and securely over time. It is like giving your devices a regular check-up, you know, but without the need for a physical visit, so that's a good thing for sure.
Getting Ready: Your Prerequisites for Remote IoT SSH AWS
Before you can start connecting to your IoT devices using SSH on AWS, there are a few things you need to have in place. The prerequisites for running the tutorial can vary depending on whether you use the manual or quick setup methods for opening a tunnel and accessing the remote device. This means you will want to make sure your AWS account is set up correctly and that you have the necessary permissions, which is, you know, pretty standard for any AWS work.
You will need an IoT device, like a Raspberry Pi, ready to go. This device should have an operating system installed and be connected to the internet. Remoteiot platform SSH Raspberry Pi download a client application, which is a part of the setup, will also be something you will want to have. This client helps in establishing the secure tunnel to your device, so it is a pretty key piece of the puzzle.
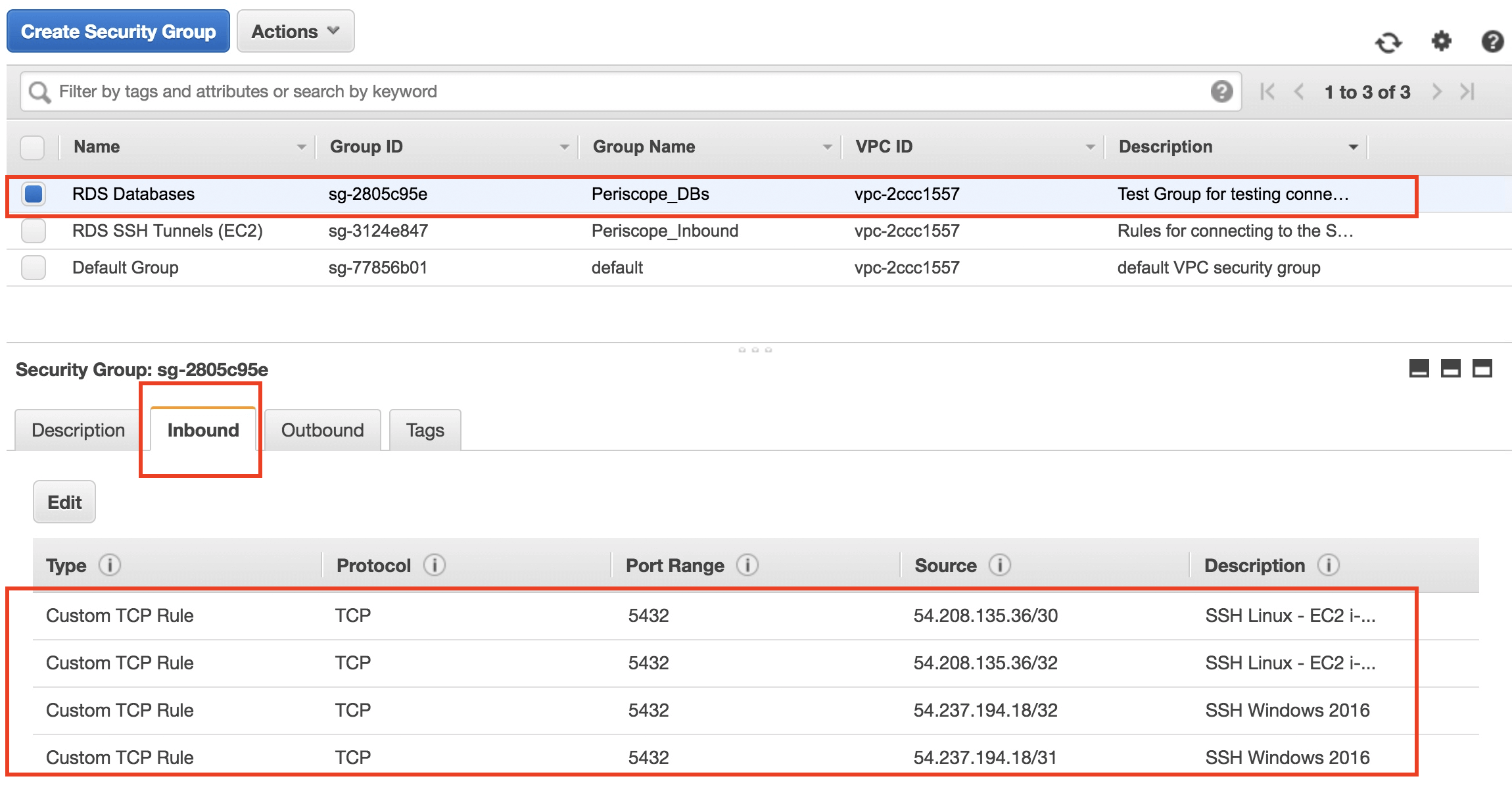
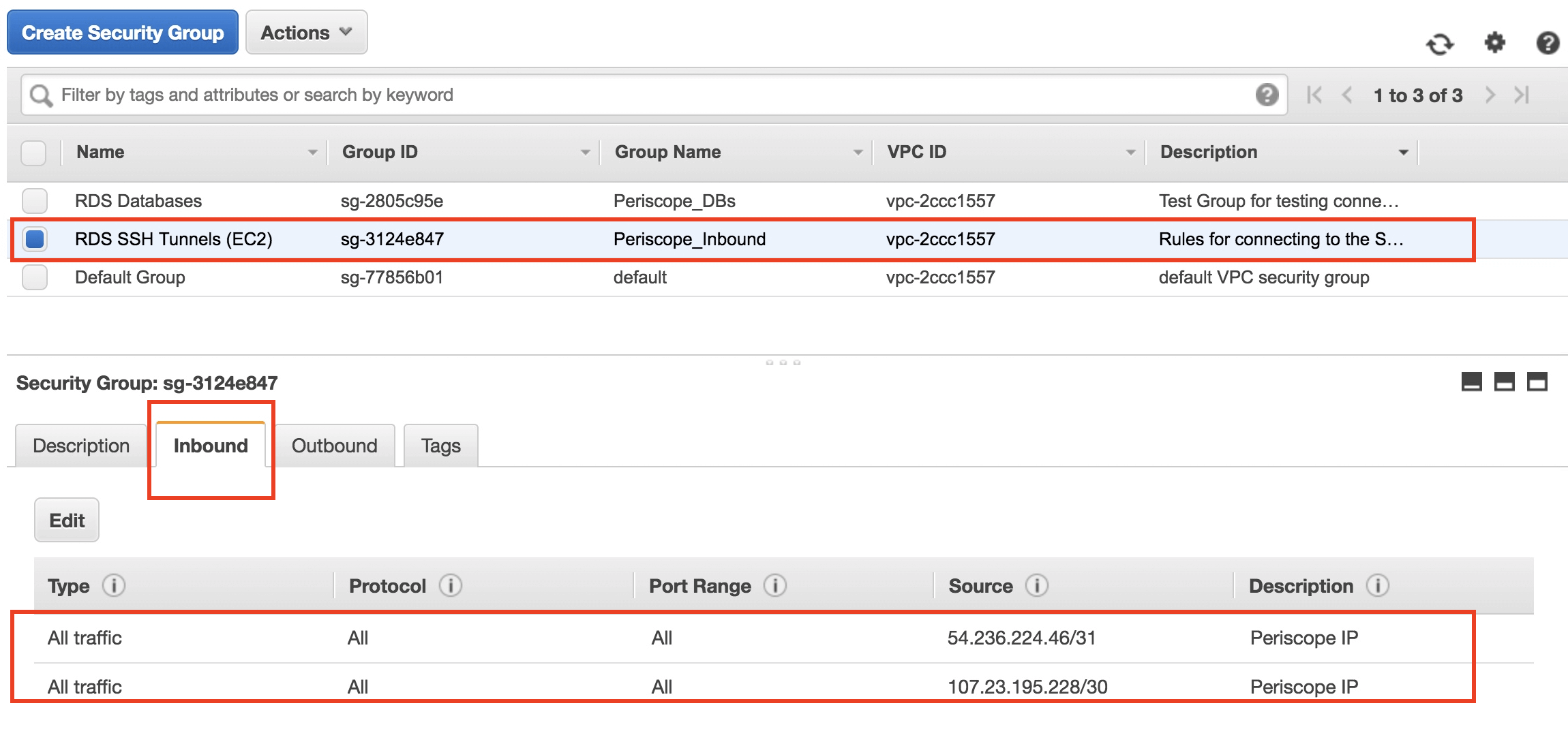
On the AWS side, you will need to configure AWS IoT Core to recognize your device. This involves creating a "thing" in AWS IoT, attaching policies, and generating certificates. These certificates are used for secure authentication between your device and AWS, making sure only authorized devices can connect. It is a bit like giving your device an ID card and a secret handshake, which is, you know, very important for security.
Choosing Your Setup Method
When it comes to actually setting up the connection, you usually have a couple of options: a manual approach or a quicker, more automated one. The manual way gives you a lot of control over each step, which some people really like for, you know, really understanding what is going on. This might involve setting up SSH tunnels and configurations by hand, which can be a bit more involved but very informative.
The quick setup, on the other hand, often streamlines the process, sometimes using scripts or tools that automate much of the work. This can be a real time-saver, especially if you are looking to get things running fast. For an example tutorial, see open a tunnel and start SSH session to remote device. When you create a tunnel from the thing details page of the AWS IoT console, you can also specify some settings, which makes it, you know, pretty straightforward.
Which method you pick really depends on your comfort level and how much you want to customize things. Both methods, actually, lead to the same result: a secure SSH connection to your IoT device. So, it is more about how you prefer to get there, which is, you know, a personal choice, really. Just make sure you follow the steps for your chosen method carefully.
Setting Up Your Raspberry Pi for AWS IoT
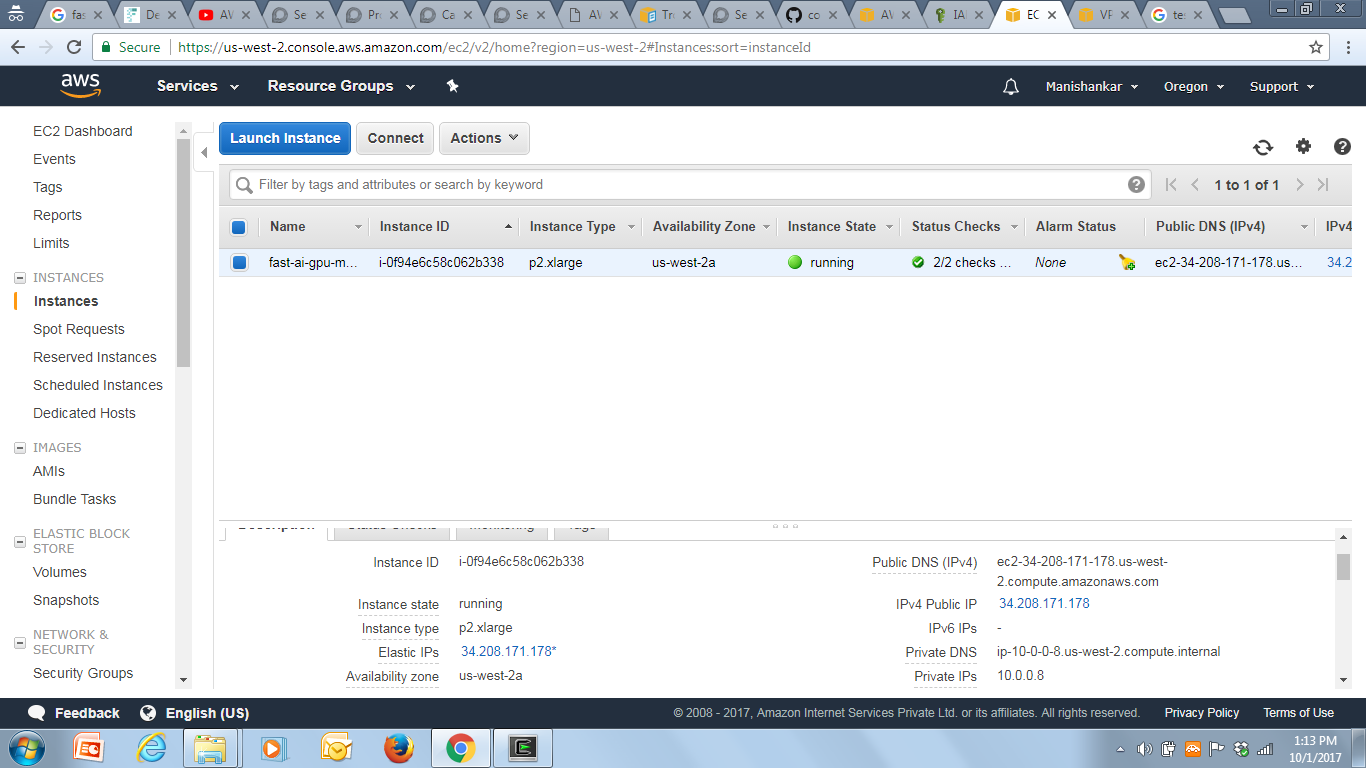
Getting your Raspberry Pi ready for AWS IoT is a key step in this whole process. First off, you need to make sure your Raspberry Pi has a working operating system, usually Raspberry Pi OS, and is connected to the internet. This is, you know, the basic foundation for everything else. You will also want to make sure SSH is enabled on your Raspberry Pi, as that is how you will eventually connect to it remotely.
Next, you will install the AWS IoT Device SDK on your Raspberry Pi. This SDK provides the tools and libraries your device needs to communicate with AWS IoT Core. It handles things like authentication and message publishing, making it easier for your Pi to talk to the cloud. You can find instructions for this on the AWS documentation, which is, you know, a good place to look for such things.
After installing the SDK, you will provision your Raspberry Pi as an IoT "thing" in the AWS IoT console. This involves registering the device, creating certificates, and attaching policies that define what your device can do within AWS IoT. These steps are pretty important for establishing trust and security, so, you know, take your time with them. Once that is done, your Raspberry Pi is, actually, ready to securely interact with AWS.
Establishing Secure Connections with AWS IoT
Once your Raspberry Pi is set up and registered with AWS IoT, the next big step is establishing those secure SSH connections. This part involves creating a secure tunnel between your local machine and your remote IoT device, all managed through AWS. It is, you know, pretty clever how it all works together to keep things safe.
This guide will explain how to harness the SSH protocol to securely access your IoT devices, with a special focus on practical examples leveraging Amazon Web Services (AWS). You will be using AWS IoT Device Management to create and manage these tunnels, which makes the whole process, actually, a lot smoother than trying to do it all manually from scratch. It is about making sure that every connection is encrypted and authorized.
The beauty of this system is that you do not need to expose your IoT device directly to the public internet, which is a big security advantage. Instead, the connection goes through AWS, which acts as a secure intermediary. This means your devices are less vulnerable to external threats, which is, you know, a pretty good thing for any IoT setup.
Creating an SSH Tunnel
Creating an SSH tunnel is a bit like digging a private, secure passageway from your computer to your IoT device. You initiate this process from your local machine, telling AWS IoT Device Management that you want to open a tunnel to a specific device. This is, you know, a crucial step for getting that remote access.
AWS IoT then helps set up the secure connection, often using AWS IoT Secure Tunneling. This service creates a secure channel that your SSH traffic can flow through. It handles the authentication and encryption, so you do not have to worry about those details yourself. It is, actually, quite convenient, making the process much simpler.
Once the tunnel is open, you will receive credentials that allow your local SSH client to connect through this tunnel to your Raspberry Pi. This involves specifying the correct port and using the provided token to authenticate. This whole process is designed to be as secure as possible, ensuring that only authorized users can connect to your devices, which is, you know, a top priority.
Accessing Your Device Remotely
With the SSH tunnel established, accessing your remote device is pretty much like accessing any local machine via SSH. You will use your standard SSH client on your computer, but instead of connecting directly to your device's IP address, you will connect through the tunnel that AWS has set up for you. This is, you know, the final step to getting control.
You will typically use a command that looks something like `ssh -i /path/to/your/key.pem pi@localhost -p [local_port]`. The `[local_port]` here is the port your tunnel is listening on, and `pi` is the default username for a Raspberry Pi. This command tells your computer to connect to your Pi through the secure tunnel, which is, actually, quite straightforward once it is all set up.
Once connected, you can run commands, manage files, and do pretty much anything you would do if you were physically connected to your Raspberry Pi. This gives you a lot of flexibility for managing your IoT projects from anywhere. It is, you know, a really powerful capability for anyone working with remote devices, allowing you to stay productive no matter where you are.
Practical Examples and Use Cases
Now, let's look at some real-world ways you can put this remote IoT SSH AWS example setup to good use. Setting up a remoteiot VPC SSH Raspberry Pi AWS environment opens up endless possibilities for IoT projects. This section will present case studies and examples of how people are actually using this technology, so you can see, you know, what is possible.
One common use is for monitoring and controlling environmental sensors in remote locations. Imagine having sensors in a forest or a distant farm, collecting data on temperature, humidity, or soil moisture. With remote SSH access, you can check on these sensors, adjust their settings, or even update their software without having to travel to those locations, which is, actually, a huge benefit.
Another great use case involves smart home or smart building applications. You might have a Raspberry Pi controlling lights, thermostats, or security cameras in your home. If you are away and something goes wrong, or you just want to tweak a setting, you can SSH into your Pi from your phone or laptop and make the necessary changes. This gives you, you know, peace of mind and control, even when you are not there.
Building a Smart Garden with Remote IoT VPC SSH
Let’s take a look at a practical example: building a smart garden using remoteiot VPC SSH. Imagine you have a garden, maybe even on a rooftop or in a community plot, and you want to make sure your plants are getting enough water. You could set up a Raspberry Pi with moisture sensors to keep track of the soil conditions, which is, you know, a pretty smart idea.
By connecting moisture sensors to your Raspberry Pi and storing the data in AWS, you can monitor your garden's health from anywhere. If you notice the soil is too dry, you can SSH into your Raspberry Pi and, perhaps, activate a small pump to water your plants. This kind of remote control is, actually, incredibly useful for maintaining a healthy garden without constant physical presence.
This setup also allows you to, you know, fine-tune your watering schedule or even integrate other sensors, like light or temperature sensors, over time. You can update the code on your Raspberry Pi remotely to add new features or adjust existing ones, which gives you a lot of flexibility. It is a clear demonstration of how powerful remote management can be for everyday projects.
Monitoring Remote Sensors
Monitoring remote sensors is another very common application for remote IoT SSH on AWS. Consider, for instance, a situation where you need to keep an eye on air quality in different parts of a city. You could deploy several Raspberry Pis, each equipped with air quality sensors, in various locations. This is, you know, a pretty effective way to gather distributed data.
With SSH access through AWS, you can connect to each of these sensor nodes individually. This allows you to check their status, collect data logs, or even calibrate the sensors if needed. If a sensor starts acting up, you can diagnose the problem remotely, which saves a lot of travel time and effort. It is, actually, a very efficient way to manage a network of devices.
This setup also helps with data integrity. You can securely transfer sensor data from the Raspberry Pi to AWS for storage and analysis, ensuring that the information is protected during transit. Mastering remoteiot SSH example for secure device management this guide will walk you through the fundamentals of SSH, its integration with AWS services, and practical applications, so you can feel pretty confident about managing your sensors.
Frequently Asked Questions About Remote IoT SSH AWS
People often have questions about getting their IoT devices connected securely with AWS. Here are some common ones that might pop up, you know, when you are getting started.
How do I remotely access an IoT device on AWS?
You access an IoT device remotely on AWS by setting up an SSH tunnel through AWS IoT Device Management. This involves registering your device as an AWS IoT "thing," configuring certificates, and then initiating a secure tunnel from your local machine to the device. The tunnel acts as a secure pathway for your SSH connection, which is, you know, pretty much how it works.
What is AWS IoT SSH?
AWS IoT SSH refers to using the Secure Shell (SSH) protocol to securely connect to and manage IoT devices that are integrated with AWS IoT. It allows you to run commands, transfer files, and perform maintenance on your remote devices, all while benefiting from the security features of AWS. It is, actually, a way to keep your devices reachable and safe.
Can I use Raspberry Pi with AWS IoT SSH?
Yes, absolutely! Raspberry Pi devices are a very popular choice for use with AWS IoT SSH. They are quite versatile and can be easily configured to connect to AWS IoT Core, making them ideal for various remote monitoring and control projects. This guide, you know, focuses quite a bit on using Raspberry Pi for these kinds of setups.
Taking the Next Steps with Your IoT Projects
So, there you have it, folks—a comprehensive guide to remoteiot SSH AWS example. By following the steps we’ve outlined, you can establish and maintain secure SSH connections for your IoT devices on AWS. Whether you are a seasoned IoT developer or just starting out, this setup offers a reliable and secure way to manage your connected gadgets, which is, you know, really quite beneficial.
Setting up a remoteiot VPC SSH Raspberry Pi AWS environment opens up endless possibilities for IoT projects. You can now confidently deploy devices in various locations, knowing you can access and manage them securely from anywhere. This capability means you can keep your projects running smoothly, troubleshoot issues quickly, and even push updates without physical intervention, which is, actually, a huge advantage in today's world.
We encourage you to experiment with these setups and explore the many ways secure remote access can benefit your specific IoT applications. The ability to control and monitor your devices from a distance truly changes how you can approach your projects. You can find more details about AWS IoT Secure Tunneling on the official AWS documentation. Learn more about this topic on our site, and find more helpful guides on this page to continue your learning journey.
- Imani Tillery
- Is Chris Kyle A Fraud
- Sean Carroll Oconnor Net Worth
- Ari Kytsya Movie
- John Sculley Net Worth
Detail Author:
- Name : Prof. Adella Oberbrunner DVM
- Username : sonya.kuhic
- Email : ewalsh@schaden.org
- Birthdate : 1996-04-08
- Address : 3416 Sanford Hill Lake Eldora, IL 15310
- Phone : +1-484-769-6848
- Company : Hane, Ondricka and Ebert
- Job : Septic Tank Servicer
- Bio : Occaecati est saepe alias. Qui nobis repudiandae voluptatibus et mollitia in. Rerum consequatur ea laboriosam qui. In occaecati nihil aut architecto.
Socials
linkedin:
- url : https://linkedin.com/in/remington7832
- username : remington7832
- bio : Dolorem voluptatem nulla aut repudiandae.
- followers : 4093
- following : 2310
tiktok:
- url : https://tiktok.com/@remingtonconroy
- username : remingtonconroy
- bio : Et voluptates et et fugit omnis harum.
- followers : 1536
- following : 360
instagram:
- url : https://instagram.com/conroy2016
- username : conroy2016
- bio : Sit sequi est sed et recusandae dolores non. Non accusantium quis non pariatur asperiores at.
- followers : 6437
- following : 1235
twitter:
- url : https://twitter.com/conroyr
- username : conroyr
- bio : Fugiat ut omnis eum doloribus et officiis repellendus. Incidunt ea nemo debitis. Nobis ad temporibus illum eveniet. Ad est officiis quas quas autem aliquid et.
- followers : 5665
- following : 1551
facebook:
- url : https://facebook.com/remington_real
- username : remington_real
- bio : Nostrum corporis a dolorem soluta esse omnis.
- followers : 1171
- following : 2433