Getting your Internet of Things (IoT) gadgets to talk to you when you are away from home can feel a bit like trying to shout through a closed door, especially when a router is standing in the way. Many folks want to check on their smart home gear, a Raspberry Pi project, or other connected devices from a Mac, no matter where they happen to be. This article is all about helping you make those connections work, giving you control over your devices even when they are tucked away behind your home network’s defenses.
The idea of having your IoT devices accessible from anywhere, like when you are at work or on a trip, is quite appealing, isn't it? It means you can adjust your smart thermostat, check on a security camera, or perhaps restart a little home server without needing to be physically present. This kind of access, as a matter of fact, lets you put your devices into service for your specific needs, making them truly useful tools.
This guide will walk you through some really good ways to achieve that remote access, focusing on options that won't cost you anything and work well with your Mac computer. We'll look at various techniques that help you get past the usual hurdles that home routers present, so you can control your IoT devices with ease, so you know, even if they are not directly visible to the wider internet.
Table of Contents
- Why Remote IoT Access Matters for You
- Understanding the Home Network Barrier: Routers and NAT
- Common Ways to Connect to Your IoT Devices
- SSH for Command-Line Control
- VNC for a Visual Desktop Experience
- RDP for Windows-Based IoT Devices
- Free Solutions for Mac Users to Get Remote Access
- Virtual Private Networks (VPNs): Your Own Secure Lane
- Reverse SSH Tunneling: A Clever Way to Connect
- Cloud-Based IoT Platforms: Letting Others Handle the Connection
- Ngrok and Similar Services: Quick Temporary Access
- Step-by-Step Guide: Setting Up Remote Access with Reverse SSH
- What You'll Need to Get Started
- Preparing Your IoT Device for Remote Access
- Setting Up Your Mac to Receive the Connection
- Creating the Reverse SSH Tunnel
- Connecting Remotely to Your Device
- Keeping Your Remote Access Secure
- Dealing with Common Connection Problems
- Your Next Steps for Remote IoT Access
Why Remote IoT Access Matters for You
Having the ability to reach your IoT devices from afar offers a lot of comfort and convenience, you know. Think about being able to adjust your home's temperature before you get there, or checking on a pet camera while you are on vacation. It really lets you put your smart home tech to its full purpose, making it work for you even when you're not physically present. This kind of control can save you time, give you peace of mind, and just generally make life a bit smoother, which is pretty nice.
For those who enjoy tinkering with small computers, like a Raspberry Pi, remote access is pretty much a must-have. It means you can work on projects, deploy updates, or even restart a service without needing to physically connect a keyboard and monitor to the device. This freedom, in a way, allows for a lot more experimentation and continuous development, making your creative endeavors much simpler to manage.
Understanding the Home Network Barrier: Routers and NAT
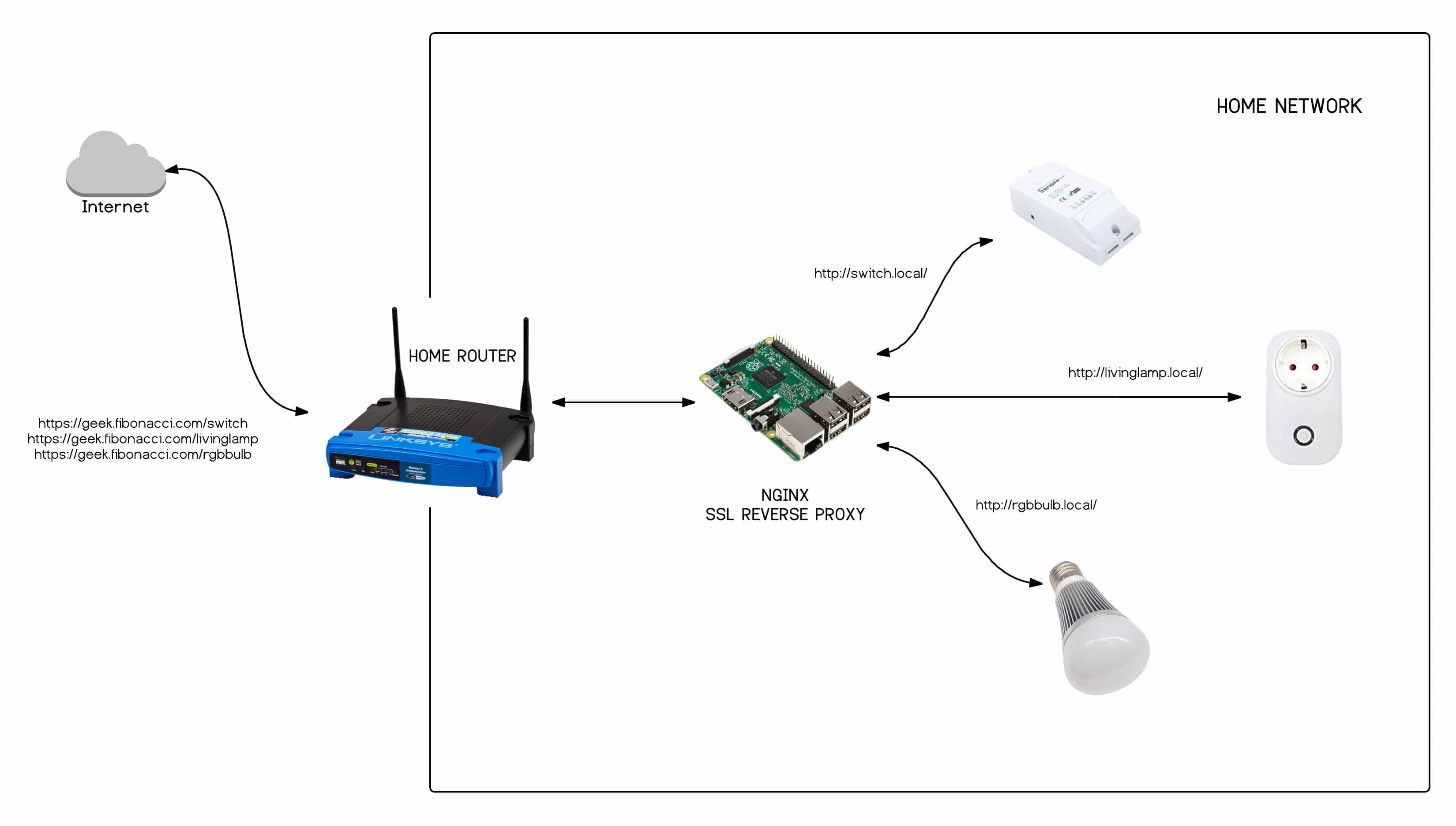
Routers are, basically, the gatekeepers of your home network, and they do a good job of protecting your devices from the outside world. They use something called Network Address Translation, or NAT, which helps multiple devices share one public internet address. While this is great for security, it also means that devices on your home network aren't directly visible to the internet, so it's a bit like trying to find a specific apartment in a large building without knowing the apartment number.
- Anna Wrossetti
- Corinna Kopf Onlyfans Leaked
- Rebecca Gormley Onlyfans Leak
- Shubhasree Sahu Leaked Mms
- табита кинг
This protection, while beneficial, makes it tricky when you want to connect to an IoT device from outside your home. Your router, you see, doesn't automatically know which internal device you want to reach when a request comes in from the internet. This is the core problem we're looking to solve, finding clever ways to bypass this protective layer without compromising your network's overall safety, which is really important.
Common Ways to Connect to Your IoT Devices
When you want to put your IoT device into service from afar, there are a few standard methods people often employ. These methods help you send commands or even see a graphical desktop, depending on what you need to do. Each has its own way of working, and knowing about them helps you choose the right tool for your particular purpose, you know.
SSH for Command-Line Control
SSH, which stands for Secure Shell, is a very common way to access devices remotely, especially those running Linux, like a Raspberry Pi. It gives you a command-line interface, which means you type commands directly to the device. It's incredibly powerful for managing files, running programs, or checking system status, and it's generally quite secure, so that's a plus.
Many folks use SSH to put their devices into action for tasks that don't need a visual screen. You can, for instance, install software, adjust settings, or restart services all from your Mac's terminal. It's a fundamental tool for anyone working with IoT devices that run an operating system, and it's something you'll likely utilize a lot.
VNC for a Visual Desktop Experience
If you prefer to see a graphical desktop of your IoT device, much like you would if you were sitting right in front of it, VNC (Virtual Network Computing) is a great choice. This method sends the device's screen display to your Mac, letting you use a mouse and keyboard as if they were directly connected. It's really handy for tasks that require a visual interface, like setting up a new application with a graphical installer or just seeing what's happening on the device's screen, so it's almost like being there.
VNC lets you, in a way, have a full desktop experience for your remote device. This is particularly useful for Raspberry Pi users who might be running a graphical operating system and need to interact with it visually. It's about putting the device's visual capabilities into service from a distance, which is pretty cool.
RDP for Windows-Based IoT Devices
For those IoT devices that happen to run a version of Windows, like some industrial controllers or specialized mini-PCs, Remote Desktop Protocol (RDP) is the standard method. RDP works similarly to VNC, giving you a full graphical interface to the remote Windows device. It's what Windows systems typically use for their own remote access, so it's a familiar sight for many.
If your IoT setup includes devices that are Windows-based, RDP is the tool you'll most likely employ to control them remotely. It allows you to use the device as if you were sitting right there, making it simple to put its features into service, which is quite convenient.
Free Solutions for Mac Users to Get Remote Access
Now, let's talk about the good stuff: getting your IoT devices to connect to your Mac without spending any money. There are several clever methods available that help you bypass the router's natural barriers, giving you control over your devices from anywhere. These options let you put your Mac and IoT devices into service together, freely and effectively.
Virtual Private Networks (VPNs): Your Own Secure Lane
A VPN, or Virtual Private Network, can create a secure, private connection over a public network. If you have a VPN server set up at your home, either on your router (if it supports it) or on a dedicated device like a Raspberry Pi, you can connect to it from your Mac. Once connected, your Mac essentially becomes part of your home network, making all your IoT devices directly accessible as if you were physically home, so that's a pretty neat trick.
Setting up a home VPN server can take a little bit of effort, but once it's working, it's a very secure and reliable way to access everything on your home network. It truly lets you use your home network's resources as if you were present, which is quite powerful.
Reverse SSH Tunneling: A Clever Way to Connect
Reverse SSH tunneling is a particularly smart way to get around router restrictions without needing to open ports. Instead of your Mac trying to connect *into* your home network, your IoT device *initiates* a connection *out* to a publicly accessible server (which could be another Mac, a cloud server, or even a free tier server). This creates a "tunnel" that your Mac can then use to connect back to your IoT device through the server. It's a bit like having your IoT device call you, and then you talk back through that same call, which is very clever.
This method is excellent because it doesn't require any special router settings, making it very user-friendly for those who don't want to mess with port forwarding. You are essentially using a public server as a meeting point, allowing your Mac to put your IoT device into service remotely, which is very handy for, say, a Raspberry Pi.
Cloud-Based IoT Platforms: Letting Others Handle the Connection
Some IoT devices and platforms offer their own cloud services that handle the remote access for you. These services often have a free tier that allows a certain number of devices or a certain amount of data transfer. Your IoT device connects to the cloud platform, and then your Mac connects to the same platform to send commands or receive data. This means the cloud service takes care of the router issues, which is quite convenient.
While these platforms might have limits on their free versions, they can be a simple way to get started, especially if you're just looking to control a few specific devices. They put the heavy lifting of network connections into service for you, making remote access straightforward, you know, for basic needs.
Ngrok and Similar Services: Quick Temporary Access
Tools like Ngrok create secure tunnels from your local machine to the internet, making your local services publicly available. You run a small program on your IoT device (or a computer on the same network), and it gives you a unique public URL that points directly to your device. This is great for temporary access or testing, as it's very quick to set up, so it's almost instant access.
Ngrok has a free tier that's perfect for occasional use or for demonstrating projects. It's a really quick way to put your device's services into action for a short period without any complex setup. You can, for instance, quickly share a web interface running on your Raspberry Pi with someone outside your network.
Step-by-Step Guide: Setting Up Remote Access with Reverse SSH
Let's walk through how to set up remote access using reverse SSH tunneling, a truly effective and free method for Mac users. This approach, you see, is particularly good because it avoids the need for port forwarding on your home router. We'll focus on a Raspberry Pi as our IoT device example, but the principles apply to other Linux-based devices as well. This will help you put your devices into service from afar.
What You'll Need to Get Started
Before we begin, gather these items:
- An IoT device, like a Raspberry Pi, running a Linux operating system.
- Your Mac computer.
- A publicly accessible server. This could be a cheap VPS (Virtual Private Server) from a cloud provider (many offer free tiers or very low-cost options for small instances), or even another Mac at a different location with a public IP address. This server will act as the "meeting point."
- SSH access already set up on your IoT device and the public server.
Having these ready will make the whole process a lot smoother, you know, and help you get things working without too much fuss.
Preparing Your IoT Device for Remote Access
First, we need to get your IoT device ready. This involves making sure it can connect to the public server and stay connected. You'll need to use SSH to connect to your IoT device locally first.
- Update your device: It's always a good idea to make sure your device's software is up to date. Open a terminal on your Mac and SSH into your IoT device (e.g., `ssh pi@your_iot_ip_address`). Then run:
sudo apt update && sudo apt upgrade -yThis ensures you are using the latest versions, which is good for security and stability, you know.
- Install `autossh` (optional but recommended): `autossh` is a program that helps maintain SSH tunnels. If your connection drops, `autossh` tries to re-establish it automatically. Install it on your IoT device:
sudo apt install autossh -yThis little tool really helps keep your connection alive, so it's a very good thing to have.
- Generate SSH keys for your IoT device: This allows your IoT device to connect to the public server without needing a password every time, which is much more secure and convenient.
ssh-keygen -t rsa -b 4096Press Enter for all prompts to save to the default location and without a passphrase (unless you want to add one for extra security, but remember it will need to be entered automatically if using `autossh`).
- Copy the public key to your public server: This tells your public server to trust connections from your IoT device.
ssh-copy-id -i ~/.ssh/id_rsa.pub user@your_public_server_ipReplace `user` with your username on the public server and `your_public_server_ip` with the public server's IP address. You'll be asked for your public server's password one last time, so that's something to remember.
After these steps, your IoT device is, you know, pretty much ready to initiate the tunnel. It's about putting the device in a position to serve your remote access needs.
Setting Up Your Mac to Receive the Connection
Your Mac needs to be ready to connect to the public server, and then through that server to your IoT device. Make sure you have SSH installed, which it usually is by default on macOS. You'll also want to make sure your Mac can connect to the public server without a password for ease of use.
- Generate SSH keys on your Mac: If you haven't already, create SSH keys on your Mac.
ssh-keygen -t rsa -b 4096Again, press Enter for defaults.
- Copy your Mac's public key to the public server: This lets your Mac connect to the public server without a password.
ssh-copy-id -i ~/.ssh/id_rsa.pub user@your_public_server_ipUse your public server's username and IP. This is really about making your connection to the public server as smooth as possible, you know.
With these steps, your Mac is now set up to easily connect to the public server, which is a key part of this whole process. It helps you, in a way, establish the first leg of your remote access journey.
Creating the Reverse SSH Tunnel
This is where the magic happens. Your IoT device will now connect *out* to the public server, creating a tunnel. We'll use `autossh` for reliability.
On your IoT device (via local SSH or directly if you have a screen):
autossh -M 0 -N -R 2222:localhost:22 user@your_public_server_ip -i ~/.ssh/id_rsa -o "ExitOnForwardFailure yes" -o "ServerAliveInterval 60" -o "ServerAliveCountMax 3" &
- `autossh -M 0`: Tells `autossh` not to use a monitoring port (we're relying on SSH's own keepalives).
- `-N`: No command will be executed on the remote server; we just want the tunnel.
- `-R 2222:localhost:22`: This is the reverse tunnel. It says: "On the public server, open port 2222. Any connection to port 2222 on the public server should be forwarded to port 22 (SSH) on *this* IoT device (localhost)."
- `user@your_public_server_ip`: The username and IP of your public server.
- `-i ~/.ssh/id_rsa`: Specifies the private key to use for authentication (the one you generated on the IoT device).
- `-o "ExitOnForwardFailure yes"`: Makes the tunnel exit if the port forwarding fails.
- `-o "ServerAliveInterval 60" -o "ServerAliveCountMax 3"`: These options tell SSH to send keepalive messages, helping to prevent the connection from dropping due to inactivity.
- `&`: Runs the command in the background, so you can close your local terminal session without stopping the tunnel.
This command, you know, basically sets up a persistent link. Your IoT device is now putting a connection into service, waiting for you to use it from your Mac.
To make this tunnel start automatically every time your IoT device boots up, you can add this command to your device's startup script, like `/etc/rc.local` (before `exit 0`) or by creating a systemd service. This way, your remote access is always ready, which is pretty convenient.
Connecting Remotely to Your Device
Now that the tunnel is active, you can connect from your Mac to your IoT device through the public server. You'll SSH into the public server, but instead of connecting to the public server itself, you'll connect to the *port* that the IoT device opened on the public server.
On your Mac's terminal:
ssh -p 2222 user@your_public_server_ip
- `-p 2222`: Specifies that you want to connect to port 2222 on the public server.
- `user@your_public_server_ip`: The username and IP of your public server.
When you run this, you are actually connecting to your IoT device! The public server simply acts as a relay. You will then be prompted for the *IoT device's* username and password (or use its SSH key if you set that up). This means you are now controlling your IoT device from anywhere, so that's really cool.
You can use this same tunnel for other services too. For instance, if your IoT device runs a web server on port 80, you could add another `-R` option to the `autossh` command on your IoT device: `-R 8080:localhost:80`. Then, from your Mac, you could access the web server by going to `http://your_public_server_ip:8080` in your browser. This truly lets you put many of your device's functions into service remotely.
Keeping Your Remote Access Secure
While gaining remote access is great, keeping it secure is, you know, incredibly important. You're opening a path to your home network, so you want to make sure only you can use it. Here are some key things to remember:
- Use strong passwords or SSH keys: Always use very strong, unique passwords for all your devices and the public server. Better yet, use SSH key authentication and disable password login where possible. This is a much more secure way to connect.
- Limit user permissions: On your IoT device, create a user account specifically for remote access and give it only the permissions it needs. Don't use the `root` user for daily remote tasks. This is, you know, a basic security practice.
- Keep software updated: Regularly update the operating system and all software on your IoT device, your Mac, and especially your public server. Updates often include security fixes that protect against known vulnerabilities.
- Monitor logs: Occasionally check the logs on your public server and IoT device for any unusual activity. This can help you spot potential unauthorized access attempts.
- Use a dedicated public server: If you can, use a public server that is only
- Gigi Derrico Net Worth
- Progressed Moon In 10th House
- Erin Murphy Muscatelli
- Sone 786 Video
- Beemedix Bee Venom Cream

Detail Author:
- Name : Terrance Legros
- Username : hassan34
- Email : cchamplin@gmail.com
- Birthdate : 2004-05-13
- Address : 65402 Selina Spur Abigaleland, TX 80900
- Phone : 1-716-459-3936
- Company : Crooks Inc
- Job : Production Planning
- Bio : Voluptates quia libero perferendis culpa hic accusantium in. Eveniet doloribus tenetur et est.
Socials
linkedin:
- url : https://linkedin.com/in/rafael_xx
- username : rafael_xx
- bio : Minus sed et similique hic.
- followers : 5157
- following : 1030
instagram:
- url : https://instagram.com/feeney2001
- username : feeney2001
- bio : Quia consequatur magni quod. Nihil nihil a excepturi.
- followers : 520
- following : 2206