Connecting your smart devices from afar, you know, when you're not actually home, can feel a bit like trying to talk through a thick wall. That wall, for most of us, is our network firewall. It's there to keep things safe inside, which is great for security but, in a way, makes accessing your Internet of Things (IoT) gadgets a real head-scratcher. Many folks find themselves wondering how to use remote IoT behind firewall using mac server example, looking for a reliable way to get their smart lights, cameras, or thermostats to listen to commands even when they're miles away.
The challenge really comes down to this: your firewall, quite properly, blocks incoming connections from the outside world. This protection keeps unwanted visitors out, which is something we all want, but it also means your smart home devices, which often rely on these incoming connections for remote control, can't be reached. So, you might want to switch off the lights after you've left, or check on your pet camera, but your network's defenses are doing their job a little too well, in some respects.
This is where a Mac server, or even an older Mac you've repurposed, can actually come to the rescue. By setting up your Mac to act as a bridge, you can create a secure pathway through that firewall, allowing you to connect to your IoT devices from anywhere. It's about making good use of your existing Apple hardware to solve a common, yet rather annoying, smart home problem, so we'll explore how to get this done.
- How Tall Is Marcus King Singer
- Debbie Rowe Age
- Dr Yunus Net Worth
- Wwxxcom Reviews 2024
- Woah Vicky Onlyfans Leaked
Table of Contents
- Understanding the Challenge
- The Mac Server Advantage
- Methods for Remote IoT Access
- Security Considerations
- Troubleshooting Common Issues
- Frequently Asked Questions
Understanding the Challenge
Before we jump into solutions, it's pretty important to get a handle on what we're up against. Remote access to devices behind a firewall is a common hurdle, especially with the way smart home gadgets work. It's not always as simple as just plugging something in and expecting it to connect from anywhere, you know?
What is a Firewall, really?
Think of your firewall as a security guard for your home network, basically. It checks every bit of information trying to come in or go out. Its main job is to block things that look suspicious or that haven't been explicitly allowed, which is that. This is a very good thing for keeping your computers and personal data safe from bad actors on the internet.
Most home routers have a built-in firewall, and your Mac itself also has one. These defenses are there to make sure only authorized traffic gets through, which is a great use for them. They're designed to protect you, and that's why we need to be thoughtful about how we ask them to let our IoT devices communicate.
Why IoT Devices Need Special Care
IoT devices, like smart bulbs or doorbells, are a bit different from your computer or phone. They often have simpler operating systems and, sometimes, fewer built-in security features. They need to connect to the internet to receive commands or send data, and this is where the firewall can get in the way.
Some IoT devices use cloud services, where they connect out to a server on the internet and then you connect to that same server to control them. This works around the firewall without much fuss, which is kind of convenient. However, many other devices need a direct path into your home network to function remotely, and that's where we have to use some clever techniques to make it happen securely, you know.
The Mac Server Advantage
Using a Mac as a server might seem a little unusual to some, but it's actually a pretty solid choice for this particular task. Macs are reliable, and with macOS, you have access to powerful Unix-based tools that are very capable for network management.
Why a Mac for This Job?
A Mac, especially an older one you might have lying around, makes a great server for a few reasons. They're typically quite energy-efficient, meaning they won't cost a fortune to run all the time, which is nice. macOS is also quite user-friendly, even for server tasks, and it offers a stable environment for running services like VPNs or reverse proxies. It's about putting something you already own to a particular purpose, rather than buying new hardware, you know.
The security features built into macOS are also a big plus. You're starting with a secure foundation, which is quite important when you're opening up paths through your firewall. This means you can focus more on configuring your remote access and less on basic system security, which is good.
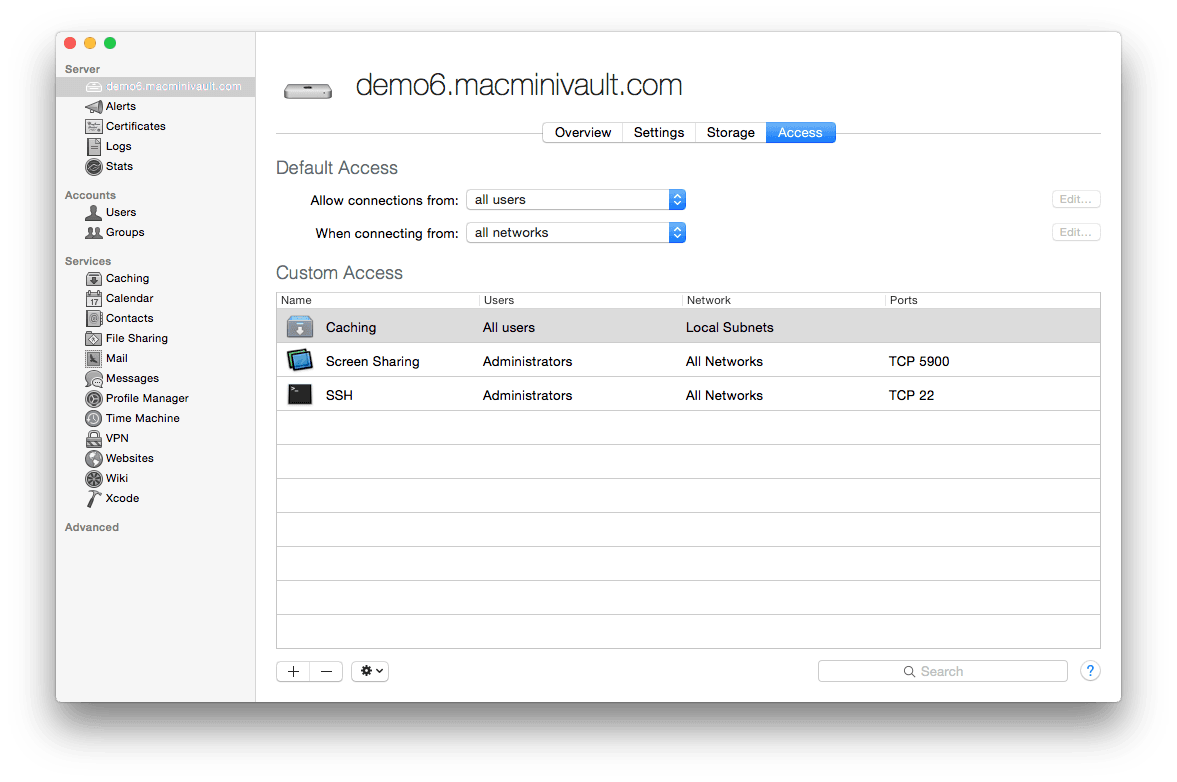
Essential Mac Server Preparations
Before you turn your Mac into an IoT access point, there are a few things you'll want to take care of. First, make sure your Mac's operating system is up to date. This ensures you have the latest security patches and features, which is very important. You'll also want to give your Mac a static IP address on your local network, so it always has the same address, which makes it easier for other devices to find it.
To do this, go to System Settings > Network, select your active connection (Wi-Fi or Ethernet), and manually set an IP address that's outside your router's DHCP range. You'll also want to disable any sleep settings, so your Mac stays awake and available all the time. It's about making sure your server is always ready to use, basically.
Methods for Remote IoT Access
There are a few main ways to achieve remote access to your IoT devices through a firewall, each with its own benefits and considerations. We'll look at three common methods, explaining how you can use your Mac server for each, you know.
Method 1: VPN (Virtual Private Network)
A VPN is often the most secure and recommended way to access your home network remotely. When you use a VPN, you create a secure, encrypted tunnel from your remote device (like your phone or laptop) to your Mac server at home. Once connected, your remote device essentially becomes part of your home network, allowing you to access all your local devices, including your IoT gadgets, as if you were sitting right there, which is pretty neat.
This approach lets us use the VPN connection to securely bypass the firewall. The firewall sees only one incoming connection to your Mac, and once that connection is established and authenticated, everything else happens securely within that tunnel. It's a very effective way to make your network available, but only to those you allow.
Setting Up a VPN Server on macOS
macOS used to have a built-in VPN server, but that's not the case anymore, sadly. However, you can still set one up using third-party software. OpenVPN is a popular and very secure choice, and it's free to use. You'll need to install it on your Mac server, which involves a few steps, including installing Homebrew first if you don't have it already.
After installing OpenVPN, you'll need to generate certificates and configuration files. This process creates the digital "keys" that allow your remote devices to securely connect. You'll also need to configure your router to forward a specific port (usually UDP 1194 for OpenVPN) to your Mac server's static IP address. This is a very important step to allow the initial VPN connection to reach your Mac.
Connecting Your IoT Devices
Once your OpenVPN server is running on your Mac, and you've connected your remote device (phone, laptop) to it, you can then access your IoT devices using their local IP addresses. For example, if your smart camera is at 192.168.1.105, you'd just type that into your browser or app while connected to the VPN. It's like you're home, so you just use their regular local addresses, which is actually quite simple.
The beauty of this method is that your IoT devices don't need any special configuration. They just sit on your local network as usual. Your remote device does all the work of connecting through the VPN, making it a pretty straightforward way to manage your smart home from anywhere, you know.
Method 2: Reverse Proxy
A reverse proxy is another powerful tool you can use with your Mac server. Instead of connecting directly to each IoT device, you connect to your Mac server, and the Mac then fetches the information or sends commands to the correct IoT device on your behalf. It acts as an intermediary, basically.
This method is particularly good if you want to expose only specific web-based IoT interfaces, like a smart home hub's web portal, without giving full network access. It adds an extra layer of security because the outside world only ever "sees" your Mac server, not your individual IoT devices, which is quite reassuring.
What's a Reverse Proxy?
Imagine you have a private library, and people want to borrow books. Instead of letting everyone wander through your shelves, you have a librarian (the reverse proxy) who takes requests, goes into the library, gets the book, and brings it back to the person. The person never enters the library itself, which is a good analogy. In our case, the librarian is your Mac server, and the books are your IoT device interfaces.
The reverse proxy listens for incoming requests on a specific port, say port 80 or 443 (for secure web traffic). When a request comes in, it looks at the request's details (like the domain name or path) and then forwards it to the correct internal IoT device. This way, you can use a single public IP address and port on your Mac to access multiple internal devices, which is very efficient.
Configuring Nginx on macOS
Nginx (pronounced "engine-x") is a very popular and powerful web server that can also function as an excellent reverse proxy. You can install Nginx on your Mac server using Homebrew, which makes the process fairly simple. Once installed, you'll edit its configuration file to set up your proxy rules.
In the Nginx configuration, you'll define "server blocks" for each IoT device you want to expose. For example, you might set up a rule that says: "If a request comes in for smartcamera.yourdomain.com, send it to 192.168.1.105:8080 on the local network." You'll also need to configure your router to forward ports 80 and/or 443 to your Mac server's static IP. This setup allows you to use your own domain name for easier access, which is quite handy.
Securing Your Proxy
When you use a reverse proxy, security is absolutely key. You'll want to use HTTPS (SSL/TLS encryption) for all external connections to your Nginx proxy. This means getting an SSL certificate, which you can obtain for free from services like Let's Encrypt. Nginx can be configured to automatically renew these certificates, which is a very convenient feature.
Additionally, you can add authentication to your Nginx configuration, requiring a username and password before anyone can even reach your IoT device interfaces. This adds another layer of protection, making sure only authorized people can access your smart home controls. It's about being careful with what you expose to the internet, you know.
Method 3: Port Forwarding (with Caution)
Port forwarding is perhaps the simplest method to understand, but it's also the one that requires the most caution. It involves telling your router to send specific incoming requests directly to a particular device on your local network. While it can work, it's generally less secure than a VPN or reverse proxy, and for that reason, we suggest using it very carefully, if at all, for IoT devices.
This method doesn't use your Mac server as an intermediary in the same way the others do. Instead, your Mac server might just be the device you're forwarding to, or it might be the device you use to manage the router settings. It's about making a direct path, which is where the risk comes in.
The Basics of Port Forwarding
Port forwarding is like putting a sign on your front door that says, "Deliver all packages for apartment 3B to the back door." You're directing specific types of traffic (packages) to a specific internal address (apartment 3B). For IoT, you'd tell your router: "Any incoming request on public port X should go to the smart camera at 192.168.1.105 on local port Y."
The problem here is that you're opening a direct path from the internet to your IoT device. If that device has any security vulnerabilities, it could be exploited by someone on the outside. That's why we emphasize caution when you use this method, you know.
Steps on Your Router and Mac
To set up port forwarding, you'll log into your router's administration interface. Look for a section called "Port Forwarding," "NAT," or "Virtual Servers." Here, you'll create a new rule specifying the external port, the internal IP address of your IoT device, and the internal port. For example, if your smart thermostat uses port 8000, you might forward external port 8000 to 192.168.1.110:8000.
Your Mac server isn't directly involved in the forwarding itself, but you'd use it to access your router's settings. You also need to make sure your IoT device has a static IP address, just like your Mac server, so the forwarded traffic always goes to the right place. This is a very important detail to get right.
Why Be Careful?
The main reason to be careful with port forwarding is security. Many IoT devices are not designed with strong internet-facing security. If you open a port directly to one of these devices, it becomes a potential target for malicious activity. If the device has a weak password, or a known software flaw, it could be compromised, and that's a serious risk.
If you absolutely must use port forwarding, ensure your IoT device has strong, unique passwords, and keep its firmware updated. Only forward the exact ports necessary, and consider using a very high, non-standard external port to make it less obvious. It's about weighing the convenience against the potential risks, you know.
Security Considerations
No matter which method you choose to use for remote IoT access, security should always be at the forefront of your mind. Opening up your network, even a little bit, means you're taking on some responsibility to keep things safe. It's not just about getting access; it's about getting secure access, too.
Keeping Things Safe
First and foremost, always use strong, unique passwords for everything: your Mac server, your router, your IoT devices, and any VPN or proxy accounts. Avoid default passwords at all costs. You should also enable two-factor authentication (2FA) wherever it's available, which adds an extra layer of protection, which is very helpful.
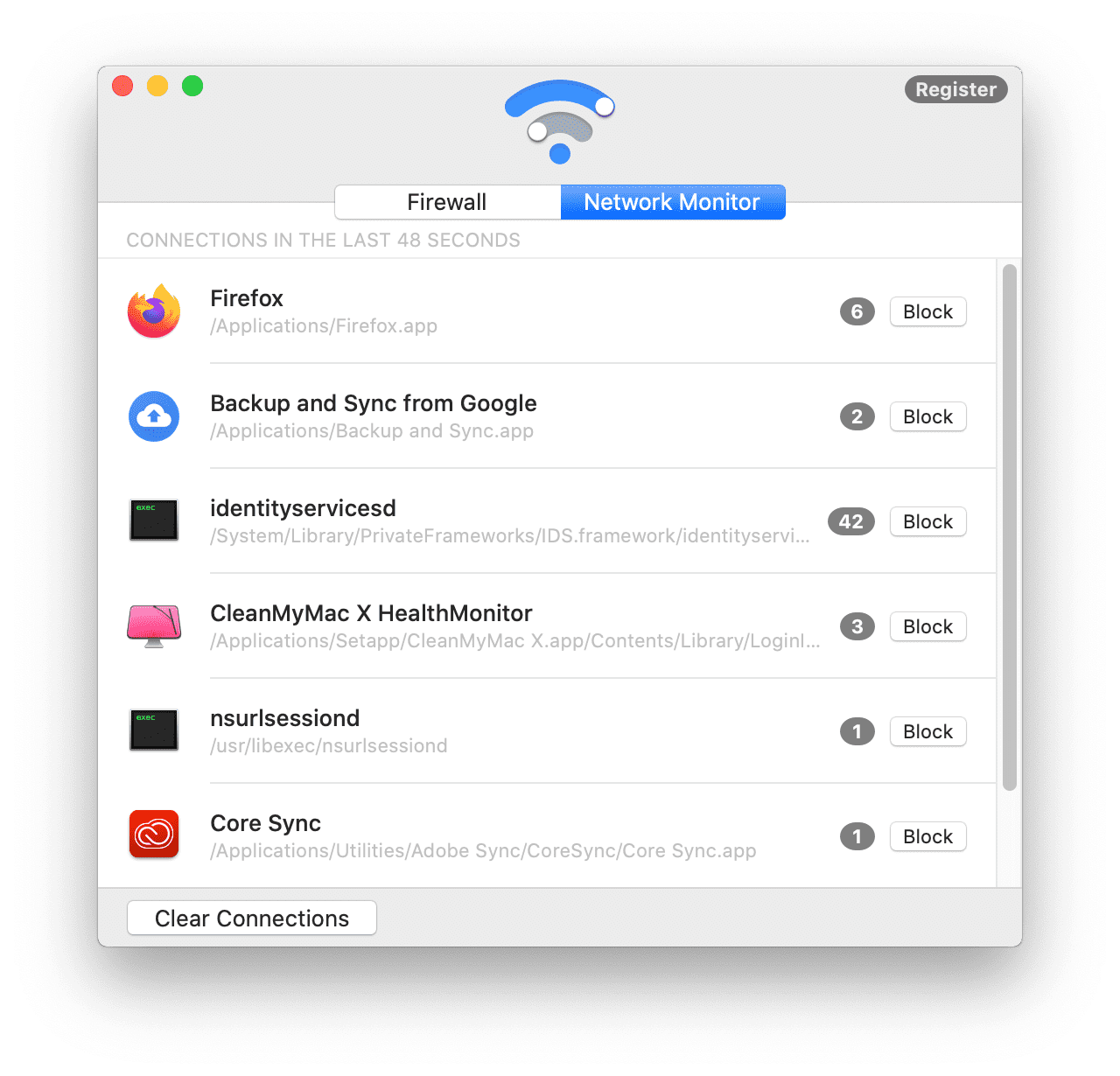
Keep your Mac server's firewall enabled and configured to only allow the specific traffic needed for your chosen remote access method. Don't open ports or services you don't absolutely need. It's about being very intentional with your network's defenses, basically.
Updates and Monitoring
Regularly update macOS and any server software you're running (like OpenVPN or Nginx). Software updates often include security fixes that patch vulnerabilities. Keeping everything current is a very simple yet effective way to maintain security, you know.
Consider setting up some basic monitoring for your Mac server. This could be as simple as checking logs periodically for unusual activity or using a tool to notify you if the server goes offline. Staying aware of your server's status can help you catch problems early, which is pretty important.
Troubleshooting Common Issues
Even with the best planning, things can sometimes go wrong. When you're trying to use remote IoT behind firewall using mac server example, you might run into a few common problems. Don't worry, many of these issues have straightforward solutions, which is good.
Connectivity Glitches
If you can't connect remotely, the first thing to check is your internet connection at home. Is your Mac server online? Is your router working correctly? A simple reboot of your router and Mac server can often clear up temporary network hiccups, which is a very common fix.
Next, verify your port forwarding settings on your router. Make sure the external port, internal IP address, and internal port are all correct and pointing to your Mac server or IoT device. A common mistake is using the wrong internal IP address, or forgetting that your Mac's IP address changed if you didn't set it to be static, you know.
Access Problems
If you can connect to your VPN or proxy, but still can't reach your IoT devices, check the firewall settings on your Mac server. macOS has its own firewall, and it might be blocking traffic to your IoT devices even after the remote connection is established. You might need to add specific rules to allow this traffic, which is a detail often overlooked.
Also, double-check the IP addresses of your IoT devices. They might have changed if they're not set to static IPs. It's a good idea to assign static IP addresses to all your critical IoT devices as well, making them much easier to locate consistently, which is quite helpful. Learn more about network configuration on our site, and link to this page here for more specific Mac server tips.
Frequently Asked Questions
People often have similar questions when setting up remote access for their smart devices, so here are a few common ones, you know.
1. Is it safe to expose IoT devices to the internet?
It can be, but you need to be very careful. Direct exposure through simple port forwarding is generally not recommended due to potential security weaknesses in many IoT devices. Using a VPN or a well-configured reverse proxy with strong security measures, like HTTPS and authentication, makes it much safer. It's about managing the risk, basically.
2. How do I access my home network from outside using a Mac?
The most secure way to access your entire home network from outside using a Mac server is by setting up a VPN server on your Mac. Once your remote device connects to this VPN, it acts as if it's part of your home network, letting you reach all your local devices, which is quite convenient. This method allows you to use your Mac to establish a secure connection, you know.
3. What is the best way to secure remote access to IoT devices?
The best way involves a combination of methods. A VPN offers the most comprehensive security by encrypting all traffic and making your remote device appear local. For web-based interfaces, a reverse proxy with HTTPS and authentication adds excellent security. Always use strong passwords, keep all software updated, and only open necessary ports. It's about layering your defenses, basically.
- Jessie Godderz Net Worth
- Billy Boyd Net Worth
- Howard Hughes Net Worth Adjusted For Inflation
- Sam Elliott Salary Per Episode
- 9xmoviesrent

Detail Author:
- Name : Aliza O'Conner I
- Username : gloria.bahringer
- Email : diana87@pollich.info
- Birthdate : 2002-12-08
- Address : 3986 Catharine Vista South Lylamouth, ME 99971
- Phone : +15416983728
- Company : Strosin-Brakus
- Job : Job Printer
- Bio : Accusantium mollitia sed aliquam aut repudiandae. Est consequatur porro quia eum explicabo voluptas. Esse doloribus aspernatur expedita itaque.
Socials
instagram:
- url : https://instagram.com/antwanfeeney
- username : antwanfeeney
- bio : Adipisci esse minima minus. Tempore maxime sed magni dolor. Quas exercitationem tempore aspernatur.
- followers : 1765
- following : 2760
facebook:
- url : https://facebook.com/antwanfeeney
- username : antwanfeeney
- bio : Qui qui qui pariatur debitis.
- followers : 928
- following : 833
tiktok:
- url : https://tiktok.com/@feeney2020
- username : feeney2020
- bio : Et consequatur itaque aliquam dolores. Laudantium et corrupti sit id.
- followers : 1162
- following : 1703
linkedin:
- url : https://linkedin.com/in/antwan.feeney
- username : antwan.feeney
- bio : Dolorum est et nihil nam reprehenderit.
- followers : 3837
- following : 2371