Are you feeling that familiar pang of worry about your remote devices, wondering if they are truly safe out there? So many folks, myself included, have run into those frustrating messages, like when your browser says, "This connection is untrusted," or when your computer warns, "Your device is at risk because it's out of date." It's a real headache, isn't it, especially when you're trying to keep everything running smoothly.
It's like when an update keeps trying to reinstall and just fails, even though it seems like it was already put on there. You just want it to stop, you know? This kind of thing makes you think about how we connect to our gadgets, especially those far-off Internet of Things (IoT) items. We need ways to get to them that feel solid and dependable, not something that leaves us feeling exposed or guessing.
That's where the idea of a free download for securely connecting remote IoT devices using P2P SSH really starts to shine. It's a way, in some respects, to bring a bit more peace of mind to your digital world. We're talking about making sure your connections are not just working, but are truly locked down, keeping unwanted eyes away from your precious data and operations. This is about making things work better, so your devices can run more securely, and you can worry less, you know?
Table of Contents
- The Big Picture: Why IoT Security Matters
- What is P2P SSH and How Does It Help?
- Getting Started with Your Free Download
- Common Connection Problems and How P2P SSH Helps
- Keeping Your IoT Connections Safe: Tips and Tricks
- Frequently Asked Questions About Secure IoT Connections
- Looking Ahead: The Future of Secure IoT Access
The Big Picture: Why IoT Security Matters
Think about all the smart things around us these days, from sensors in a field to cameras watching your home, or even industrial controls. They are, in a way, everywhere. These IoT devices, as we call them, gather so much information and often control important functions. But, you know, just like any computer, they can be a target if they're not protected well. It's a bit like leaving your front door unlocked; you're just asking for trouble, more or less.
Many people have faced issues that make them think hard about security. For instance, I've heard about folks trying to set up mail rules to lock down their email, only to find themselves constantly dealing with security alerts. Or, very commonly, you get those scary messages saying your connection isn't secure, even when you're just trying to check your mail, like when Firefox tells you it can't confirm your connection to a site. These things happen a lot, actually.
When your devices are out there, sometimes in places far away, connecting to them becomes a real concern. You need to know that when you send a command or pull data, nobody else is listening in or messing with things. That's why having a way to securely connect remote IoT devices is so important, and why a solution like P2P SSH, especially a free download option, really catches people's attention. It's about building trust in those digital pathways, you know?
- Somali Hub Telegram Vip
- 50th Birthday Invitation Wording
- Jameliz Benitez Onlyfans Leaked
- Music Masters Meaning
- Sun Conjunct Pluto
What is P2P SSH and How Does It Help?
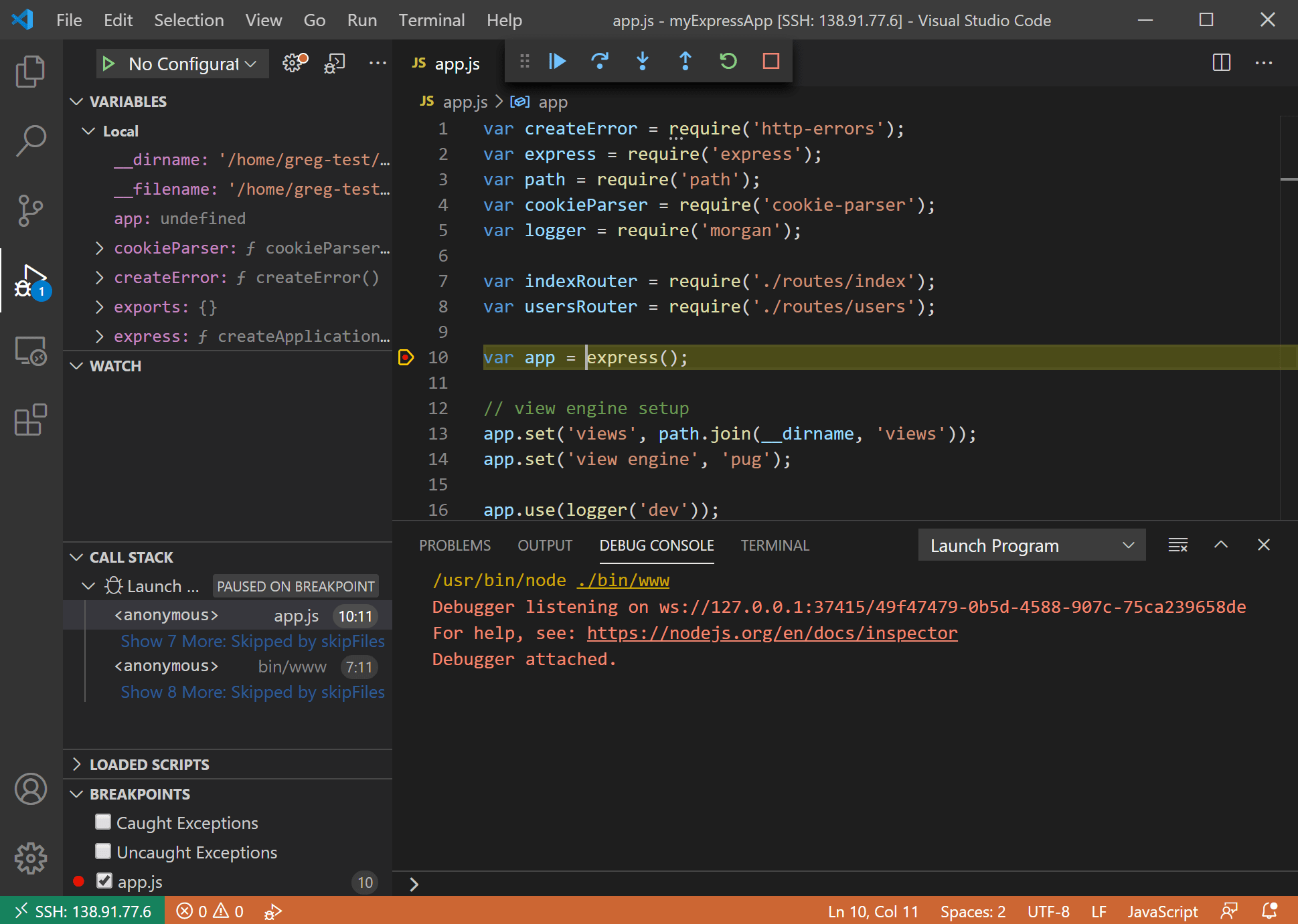
So, what exactly is P2P SSH, and why is it such a helpful thing for your IoT devices? Well, P2P stands for "peer-to-peer," and SSH means "Secure Shell." Put those together, and you get a way for two devices to talk directly and safely, almost like they're whispering secrets only to each other. This is different from older ways of connecting, which often involved a middleman server, which can be a bit more complicated, you know?
This direct connection is, in some respects, a game-changer for remote IoT. It means you don't always need to set up tricky network configurations or rely on a central server that might become a weak spot. It's about making things simpler while still keeping them very, very safe. People are looking for solutions that are both easy to use and incredibly secure, and P2P SSH really aims for that sweet spot, I mean.
When you hear about a "free download" for this kind of technology, it really opens up possibilities. It means more people can access these strong security features without a big cost barrier. This helps a lot with getting more devices connected safely, which is a good thing for everyone, actually. It's about giving you the tools to protect your own digital space, right?
Traditional SSH vs. P2P SSH
Let's think about how SSH usually works. Typically, when you use SSH to connect to a remote server, your computer talks to that server directly over a network. This works great if your server has a public IP address and is easy to find on the internet. But what about your IoT device that might be behind a router, or maybe it only has a private IP address? That's where things get a little tricky, you know.
With traditional SSH, you'd often need to set up "port forwarding" on your router, or use a VPN, or perhaps a cloud service to bounce your connection through. These methods can be a bit of a hassle to set up, and they might even introduce new security considerations. For someone who's just trying to stop an update from reinstalling, adding more network configuration steps is probably the last thing they want to do, I mean.
P2P SSH, however, finds a way around these hurdles. It allows devices to establish a direct, encrypted connection even if they are behind different firewalls or routers, without needing manual port forwarding. It uses clever techniques to "punch through" those network barriers, making it much simpler to reach your remote IoT device. This means less configuration pain and, in some respects, a more direct path to your device, which is very helpful.
The Benefits of P2P SSH for IoT
The advantages of using P2P SSH for your IoT devices are, arguably, pretty clear. First off, there's the security aspect. SSH itself creates a very strong, encrypted tunnel for your data. This means that anything you send or receive from your IoT device is protected from prying eyes. It's a big step up from unsecured connections that might leave your data exposed, you know?
Then there's the ease of access. As we just talked about, P2P helps you bypass those tricky network setups. This means you can get to your devices from almost anywhere, without needing to be a network wizard. For someone who's had trouble connecting securely to a website in the past, or who doesn't have "any other option when this comes on my," this simplicity is a huge plus, actually.
Another great thing is the directness of the connection. Because it's peer-to-peer, you're often reducing the number of hops your data has to make. This can lead to faster response times and a more reliable connection overall. Plus, with a free download option, it's accessible to a wider range of users, making strong IoT security something everyone can consider, which is pretty neat.
Getting Started with Your Free Download
So, you're thinking about trying out this secure connection for your IoT devices, and you're looking for that free download. That's a great step! The idea is to make this process as straightforward as possible, so you can get your devices talking securely without too much fuss. It's about empowering you to take control of your device's safety, you know?
When you're searching for a solution, you'll find a few options out there. It's good to look for ones that are well-regarded by others and have clear instructions. The goal is to get something that works, that's easy to understand, and that truly offers that secure P2P SSH connection. This isn't about adding more problems, like when you're stuck in an automatic repair loop after an update; it's about solving them, actually.
Remember, the whole point is to make your remote IoT connections feel safe and dependable. A free download means you can try it out, see how it works for your specific setup, and decide if it's the right fit. It's a low-risk way to explore a powerful security tool, which is pretty cool.
Finding a Reliable Solution
When you're looking for a free download to securely connect remote IoT P2P SSH, it's very important to pick something trustworthy. Just like you wouldn't click on an untrusted link, you shouldn't download software from just any old place. Look for projects that are open-source, or solutions from reputable companies that offer a free tier. These often have communities around them that can help if you get stuck, you know.
Check for reviews and see what other users are saying. Does the solution actually deliver on its promise of easy, secure P2P SSH? Does it seem to work well for various IoT devices? You want something that's been tested and proven, not something that's going to add to your list of "problems connecting securely to this website" type issues. A little research here goes a long way, truly.
Also, think about how well the solution is maintained. Are there regular updates? Good software gets better over time, with fixes and new features. This shows that the developers are committed to keeping it secure and functional, which is something you definitely want for your IoT connections, I mean. Learn more about secure connections on our site for related tips.
Basic Setup Steps
Once you've found your chosen free download for P2P SSH, getting it set up for your IoT devices usually follows a few simple steps. First, you'll typically install a client application on your local computer, the one you're using to connect from. This is, you know, your control center.
Next, you'll need to get a small agent or client onto your remote IoT device itself. This is the piece that allows your device to "listen" for your secure connection requests. Often, this involves running a few commands in the terminal of your IoT device, which might seem a little scary at first, but it's usually quite straightforward, honestly.
Finally, you'll typically generate some security keys. These keys are what make your SSH connection so strong; they're like digital fingerprints that prove you are who you say you are. You'll put one part of the key on your local machine and the other on your IoT device. Then, you can initiate your secure P2P SSH connection. It sounds like a lot, but many free solutions have very clear guides to walk you through it, which is good, you know?
Common Connection Problems and How P2P SSH Helps
We've all been there, haven't we? That moment when you try to connect to something, and it just doesn't work. It's like when your computer gets stuck in an automatic repair loop after installing updates, or when you can't seem to find the option to password protect a file in SharePoint. These kinds of frustrations are, very common, actually, and they often come down to connection or security issues.
For IoT devices, these problems can be even trickier because the devices might be far away, or in places where you can't easily get to them. Traditional network setups often cause headaches with firewalls blocking connections, or dynamic IP addresses making it hard to find your device. You might try multiple platforms – MS Edge, Firefox, Chrome – and still, to no avail, just like some folks have experienced with untrusted connection warnings, you know.
P2P SSH really steps in here to smooth things over. Because it's designed to punch through those network barriers, it often solves the problem of "I can't reach my device." It creates that direct, secure channel, making it much less likely that a firewall or a tricky router setting will stand in your way. This means fewer moments of head-scratching and more reliable access to your remote gadgets, which is pretty helpful, I mean.
Keeping Your IoT Connections Safe: Tips and Tricks
Even with a great tool like P2P SSH, there are still things you can do to make your IoT connections even safer. Think of it as adding extra locks to your very secure door. One big tip is to always use strong, unique passwords for your devices. This might seem obvious, but it's a step that people sometimes overlook, which is a bit risky.
Another good practice is to regularly update your IoT device's software and the P2P SSH client you're using. Remember those frustrating messages about devices being "out of date and missing important security and quality updates"? Keeping things current helps close any newly discovered security holes. It's like getting a fresh coat of paint on your house; it keeps things looking good and protected, you know?
Also, only allow access to your IoT devices from trusted computers. Don't just connect from any machine. This limits the potential points of entry for anyone who shouldn't be there. And, perhaps, consider using multi-factor authentication if your P2P SSH solution offers it. That adds another layer of protection, making it much harder for unauthorized people to get in, which is very important.
For more insights on safeguarding your digital presence, you can also check this page for advanced security practices. It's about being proactive, you know?
Frequently Asked Questions About Secure IoT Connections
People often have a few common questions when they start thinking about securely connecting their remote IoT devices. These are, you know, the things that come up again and again.
Is a free download for P2P SSH truly secure?
Yes, many free P2P SSH solutions can be very secure. The "free" part often refers to the software being open-source or having a free tier, not that it compromises on the core security features of SSH itself. SSH uses strong encryption methods, so the connection itself is, in some respects, very solid. You just need to pick a reputable option, you know?
Do I need special hardware for P2P SSH with IoT devices?
Generally, no, you don't need special hardware. P2P SSH solutions typically run as software on your existing IoT devices, like a Raspberry Pi or an industrial controller, and on your computer. Your devices just need to be able to run the client software and connect to the internet, which is pretty standard these days, I mean.
Can P2P SSH help with untrusted connection warnings like those in browsers?
While P2P SSH itself doesn't directly fix browser warnings about untrusted websites, it addresses a similar underlying problem: ensuring a secure, verified connection. For your IoT devices, P2P SSH means the connection *to* the device is trusted and encrypted, preventing the kind of "we can't confirm that your connection is secure" messages you might get when talking to your gadgets directly. It's about building trust from the ground up, you know?
Looking Ahead: The Future of Secure IoT Access
The world of IoT is always changing, and so are the ways we keep it safe. The need for securely connecting remote IoT devices will only grow, especially as more and more things get smart. Solutions like P2P SSH, particularly those available as a free download, are making strong security more accessible to everyone, which is really important.
We'll likely see even more user-friendly interfaces and simpler setup processes in the future. The goal is to make it so easy that anyone can protect their remote devices without needing to be a security expert. It's about taking away those frustrations of failed updates and untrusted connections, and replacing them with dependable, safe access. This kind of progress is, you know, what keeps us moving forward.
Keeping an eye on new developments and staying informed about the best practices will always be a good idea. The digital landscape is always shifting, and being prepared means your IoT devices can continue to serve you well, safely and reliably, for a long time to come. It's about having that peace of mind, truly.
- 100 Words About Baseball
- Sophie Rain Onlyfans Naked
- Erime
- Lea Michele Net Worth
- Jameliz Benitez Smith Onlyfans

Detail Author:
- Name : Prof. Caitlyn Lindgren IV
- Username : dietrich.brown
- Email : rylan.runte@yahoo.com
- Birthdate : 1998-05-07
- Address : 8574 Ruthie Islands Noemyburgh, GA 31502
- Phone : 743-286-9233
- Company : Lehner, Little and Skiles
- Job : Tree Trimmer
- Bio : Qui aut blanditiis a qui unde consectetur excepturi. A tempora delectus eum qui. Cumque vitae in illum ex quisquam adipisci doloremque.
Socials
tiktok:
- url : https://tiktok.com/@mariane_hudson
- username : mariane_hudson
- bio : Dolor ut commodi minima. Aspernatur et vel laborum libero fugit.
- followers : 2455
- following : 87
facebook:
- url : https://facebook.com/hudsonm
- username : hudsonm
- bio : Inventore assumenda perferendis ab sit non est in.
- followers : 2120
- following : 2075
linkedin:
- url : https://linkedin.com/in/mhudson
- username : mhudson
- bio : Porro perferendis quis dicta minima et atque et.
- followers : 5639
- following : 2556
twitter:
- url : https://twitter.com/mariane_official
- username : mariane_official
- bio : Deserunt omnis consectetur veniam ab quos sint. Debitis repellat molestiae qui delectus qui temporibus totam. Et nulla nostrum quae recusandae assumenda qui.
- followers : 1347
- following : 829
instagram:
- url : https://instagram.com/mhudson
- username : mhudson
- bio : Quae aut in et explicabo quis. Sit iusto id magnam optio sequi quis.
- followers : 3692
- following : 2457