Getting your remote IoT devices to talk to each other, especially for peer-to-peer (P2P) downloads on a Windows 10 system, can feel like a bit of a tightrope walk. You want that convenience, that direct data exchange, but you absolutely need to know your information is safe. It's a common worry, you know, when your device flashes warnings like "Your device is at risk because it's out of date and missing important security and quality updates." That message alone can make anyone pause and think about how truly secure their connections are, and it's a very real concern for IoT setups.
Imagine you have a sensor out in the field, collecting vital information, and you need to pull large data files directly to your Windows 10 machine, or maybe even distribute updates to other IoT units. Relying on traditional server-based methods can be slow or just plain inefficient for big data transfers, so P2P sounds great, doesn't it? But, there's often a problem connecting securely to this kind of setup, and that's where the real challenge comes in. It's not just about getting the connection to work; it's about making sure that connection is trusted and protected from potential threats, a bit like when your browser tells you, "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure."
This article is here to help you get a clearer picture of how to securely connect remote IoT devices for P2P downloads using Windows 10. We'll look at why this is so important, what kinds of issues you might run into, and some practical steps you can take to keep everything safe. We'll talk about making sure your Windows 10 system is ready, picking the right P2P tools, and putting strong security measures in place. Basically, we want to help you run Windows more securely, especially when it comes to your valuable IoT data.
- Incredible Amy Bradley Update
- Edi Words
- Japanese Lesbian Massage
- Greek Word For Flower
- Krystal Ann Mother
Table of Contents
- Understanding the Need for Secure IoT P2P Connections on Windows 10
- Why P2P for IoT?
- The Security Stakes
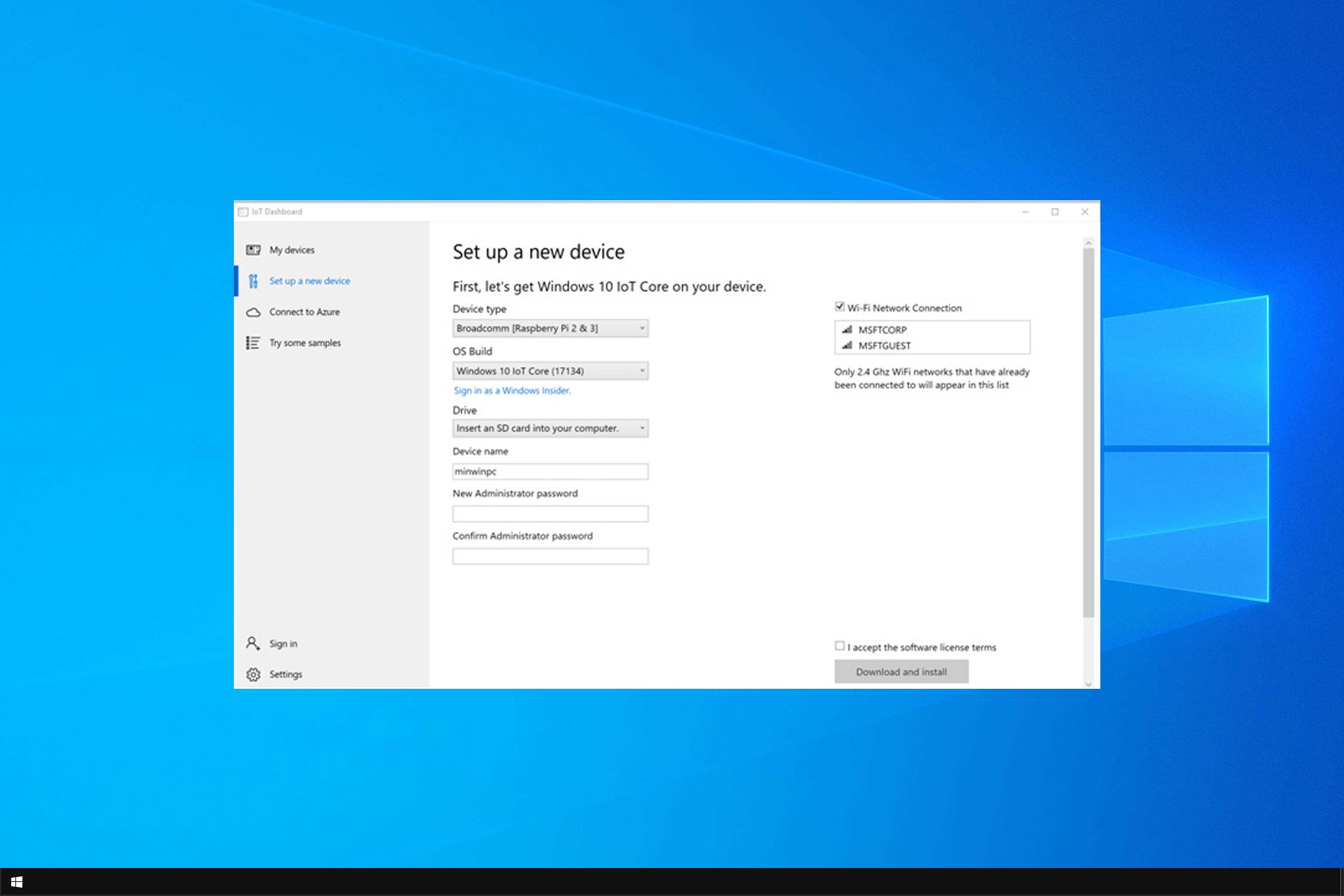
- Setting Up Your Windows 10 Environment for Secure IoT P2P
- Keeping Windows 10 Updated
- Firewall and Network Configuration
- User Account Control (UAC) and Permissions
- Choosing the Right P2P Technologies for IoT
- VPNs: Your Private Tunnel
- Secure File Transfer Protocols
- Blockchain-Based P2P Solutions
- Implementing Strong Security Measures
- Encryption is Key
- Authentication and Authorization
- Monitoring and Logging
- Device Management and Policy
- Troubleshooting Common Secure Connection Issues
- Dealing with Untrusted Connections
- Update Troubles
- Browser Management Concerns
- Best Practices for Ongoing IoT P2P Security
- Frequently Asked Questions (FAQs)
Understanding the Need for Secure IoT P2P Connections on Windows 10
Connecting remote IoT devices directly for P2P downloads on Windows 10 might sound a bit niche, but it's actually becoming pretty important for a lot of folks. Think about it: you have sensors, cameras, or even industrial equipment scattered across different locations, and they're generating tons of data. Getting that data back to a central point, or distributing updates to those devices, needs a reliable and efficient method. P2P can be really good for this, as a matter of fact, because it often cuts out the middleman, making transfers quicker and sometimes more robust.
Why P2P for IoT?
So, why would you even consider P2P for your IoT setup? Well, for one, it can be incredibly efficient. When devices talk directly to each other, you reduce latency and reliance on a single central server that could become a bottleneck. This is especially true for large file transfers, like firmware updates or big data logs from an IoT sensor. It's like, instead of everyone sending their mail through one post office, they just hand it directly to the person next door. That's faster, right? Also, in some remote locations, a direct P2P link might be more resilient than trying to maintain a constant, stable connection to a distant server, which is a big plus.
The Security Stakes
Now, while P2P offers some clear advantages, the security stakes are very, very high. When devices connect directly, you're essentially opening up a potential pathway for all sorts of unwanted access. If you've ever seen a message like, "This connection is untrusted you have asked firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure," you know that feeling of unease. That same feeling applies tenfold to your IoT network. Without proper security, those direct connections can become easy targets for data breaches, malware, or unauthorized control. It's almost like leaving your front door unlocked, isn't it? You need to make sure every entry point is solid.
- What Happened To Holly Sonders
- Jules Ari Leak
- John Sculley Net Worth
- Is Ann Bessette Freeman Still Alive
- Is Dax Riggs Married
Setting Up Your Windows 10 Environment for Secure IoT P2P
Getting your Windows 10 system ready for secure IoT P2P connections is a bit like preparing your home before guests arrive; you want everything tidy and protected. This involves making sure your operating system is in tip-top shape and that its built-in security features are doing their job. A lot of the issues people run into, like an update that keeps trying to reinstall and fails, can actually leave your system vulnerable, so addressing these basics is really important.
Keeping Windows 10 Updated
This might seem obvious, but keeping your Windows 10 system fully updated is arguably the single most important step for security. You know those messages, "Your device is at risk because it's out of date and missing important security and quality updates"? They're not just nagging; they're critical warnings. Updates often patch security vulnerabilities that attackers could exploit. If you're having an issue with an update that keeps trying to reinstall and fails, it's worth digging into that problem. Sometimes, it looks like it was already installed, but Windows still tries to push it. You might need to troubleshoot why it's reinstalling again. Making sure your system is current means you're running with the latest defenses, which is basically your first line of protection.
Firewall and Network Configuration
Your Windows Firewall is a really powerful tool for controlling what comes in and out of your system. For secure IoT P2P, you'll need to configure it carefully. You don't want to just open up every port, of course. Instead, you'll want to create specific rules that only allow traffic from your trusted IoT devices on the ports they need. This is a bit like having a bouncer at a club, letting in only the people on the guest list. You might also need to adjust network settings, especially if your IoT devices are on a separate subnet or require specific IP configurations. Making sure these settings are just right helps prevent unwanted network access, which is quite important.
User Account Control (UAC) and Permissions
User Account Control (UAC) on Windows 10 is there to prevent unauthorized changes to your system. While it can sometimes feel a little annoying with its constant prompts, it's actually a vital security layer. For IoT P2P, ensure that any applications or services handling the P2P connections are running with the minimum necessary permissions. Giving an application more privileges than it needs is a security risk. It's a bit like giving a house key to someone who only needs to water your plants; you want to limit access to just what's required. Regularly reviewing user and application permissions can help keep your system secure, which is a good habit to get into.
Choosing the Right P2P Technologies for IoT
When you're looking to securely connect remote IoT devices for P2P downloads on Windows 10, picking the right technology is pretty essential. It's not just about getting data to move; it's about making sure it moves safely and efficiently. There are a few different approaches you can take, and each has its own strengths, so you need to pick what fits your situation best, you know?
VPNs: Your Private Tunnel
Using a Virtual Private Network (VPN) is arguably one of the most straightforward ways to add a layer of security to your P2P IoT connections. A VPN creates an encrypted tunnel between your Windows 10 machine and your remote IoT devices, or even between the IoT devices themselves. This means all the data traveling through that tunnel is scrambled, making it very difficult for anyone to snoop on your traffic. It's like sending your data through a private, armored car instead of an open truck. You could set up a VPN server on your Windows 10 machine or use a dedicated VPN service that supports IoT devices. This method basically solves a lot of the "untrusted connection" problems we often see, providing a secure foundation for any P2P activity.
Secure File Transfer Protocols
Beyond the network layer, you also need to think about the actual protocols you're using for file transfers. Just because you're doing P2P doesn't mean you should skip secure protocols. For instance, instead of basic HTTP, you should always use HTTPS for any web-based interfaces or API calls involved in your P2P setup. For direct file transfers, protocols like SFTP (SSH File Transfer Protocol) or FTPS (FTP Secure) offer encryption and authentication, which is really important. Even if you're building a custom P2P application, incorporating strong encryption libraries and authenticated sessions is crucial. It's about making sure the "handshake" between devices is legitimate and that the data itself is protected during its journey, which is actually a big deal.
Blockchain-Based P2P Solutions
This might sound a bit advanced, but blockchain technology is starting to offer some interesting possibilities for secure IoT P2P. Imagine a decentralized network where each IoT device is a node, and transactions (like data transfers or updates) are recorded on an immutable ledger. This can provide a very high level of trust and integrity, as every participant can verify the authenticity of the data and the devices involved. While setting this up can be more complex than a simple VPN, it offers a robust solution for ensuring data integrity and device identity in a P2P network. It's a bit like having a public, unchangeable record of every interaction, making it very hard for anyone to tamper with things. This approach, you know, could really change how we think about IoT security in the future.
Implementing Strong Security Measures
Once you've got your Windows 10 environment set up and chosen your P2P technologies, the next big step is putting in place strong security measures. It's not enough to just hope for the best; you need active defenses. This is where you address the core of "securely connect remote iot p2p download windows 10" head-on, making sure every part of your system is locked down, which is really important.
Encryption is Key
Any data moving between your remote IoT devices and your Windows 10 system for P2P downloads absolutely needs to be encrypted. This means transforming your data into a coded format that only authorized parties can read. Whether you're using a VPN, secure file transfer protocols, or building a custom application, encryption should be baked in. Think of it like putting your sensitive documents in a locked safe before sending them. Even if someone intercepts the safe, they can't open it without the key. This prevents eavesdropping and ensures the privacy of your data, which is actually a fundamental aspect of security.
Authentication and Authorization
Knowing who or what is connecting to your system is pretty vital. Authentication verifies the identity of a device or user, while authorization determines what they're allowed to do. For IoT P2P, this means ensuring that only your legitimate IoT devices can connect and that they only have access to the data and functions they need. Using strong passwords, multi-factor authentication (MFA) where possible, and digital certificates for device identity are all good practices. It's a bit like having a strict ID check at the door and then giving different guests different levels of access to your home. This helps prevent unauthorized access and keeps your network secure, which is a major concern for many.
Monitoring and Logging
You can't protect what you don't know about, right? Implementing robust monitoring and logging for your IoT P2P connections is crucial. This means keeping a record of who connected, when they connected, what data was transferred, and any unusual activity. If something goes wrong, like an attempted breach or a connection that seems suspicious, these logs will be your first clue. It's like having a security camera system and a detailed visitor log for your network. Regularly reviewing these logs can help you spot potential threats early and respond quickly, which is very helpful for maintaining security.
Device Management and Policy
Managing your IoT devices, especially their security policies, is another big piece of the puzzle. This includes things like regularly auditing device configurations, ensuring firmware is up-to-date, and enforcing strict access controls. You might even find your browser is managed by an organization, even when you're not supposed to be, going to edge://policy, and seeing that two policies are in place. This shows how policies can impact even seemingly personal devices. For IoT, having clear policies about how devices connect, what data they can access, and how they receive updates is key. This centralized management helps maintain a consistent security posture across your entire IoT fleet, which is quite important for preventing vulnerabilities.
Troubleshooting Common Secure Connection Issues
Even with the best planning, you might still run into a few bumps when trying to securely connect remote IoT devices for P2P downloads on Windows 10. It's honestly pretty common, and a lot of these issues are things people deal with regularly in other areas of their tech lives, too. Knowing how to handle them can save you a lot of headaches, you know?
Dealing with Untrusted Connections
One of the most frequent messages that pops up, and one that causes a lot of worry, is "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." Or maybe it's "There is a probler connecting securely to this website." These messages basically mean your system can't verify the identity of the server or device it's trying to talk to, or that the encryption isn't working right. For IoT P2P, this often points to issues with SSL/TLS certificates. Make sure your IoT devices have valid, up-to-date certificates, and that your Windows 10 system trusts the Certificate Authority (CA) that issued them. Sometimes, it's a simple time sync issue between devices, which can invalidate certificates. Checking these things can often clear up those pesky warnings, which is a good first step.
Update Troubles
You might be having an issue with an update that keeps trying to reinstall and fails, even though it looks like it was already installed. This kind of problem can actually prevent your Windows 10 system from getting crucial security patches, leaving it vulnerable. If you're trying to stop it from reinstalling again, you might need to use Windows Update troubleshooter, or even manually download and install the update. Sometimes, corrupted system files or conflicting software can cause these loops. Ensuring your operating system is fully patched is really vital for secure connections, because those updates often fix security flaws that could be exploited in a P2P setup. It's about keeping your foundation strong, you know?
Browser Management Concerns
It might seem a bit odd, but sometimes issues like "I'm confused on why my browser is managed by an organization, when i'm not supposed to be" can hint at broader policy or network configuration problems that affect IoT. If you go to edge://policy and it tells you that two policies are active, this could mean something is enforcing network rules that interfere with your P2P connections or security settings. While this specifically relates to browsers, the underlying issue might be a Group Policy Object (GPO) or a network device pushing configurations that affect all network traffic, including your IoT P2P. Investigating these policies, even if they seem unrelated at first glance, can sometimes uncover why your secure IoT connections aren't behaving as expected, which is pretty insightful.
Best Practices for Ongoing IoT P2P Security
Keeping your remote IoT P2P downloads on Windows 10 secure isn't a one-time setup; it's an ongoing effort. Think of it like maintaining a garden; you can't just plant seeds and walk away. You need to keep tending to it, you know? Regular care and attention will help ensure your system stays protected against new threats and vulnerabilities, which is pretty much always a concern.
One really important practice is to regularly review and audit your security configurations. This means checking your firewall rules, VPN settings, and access controls to make sure they're still appropriate and haven't been inadvertently changed. As a matter of fact, it's easy for settings to drift over time, especially if multiple people are managing the system. A periodic check can catch potential weaknesses before they become a problem, which is a good habit to get into.
Another thing is to stay informed about the latest security threats and best practices for both Windows 10 and IoT devices. Security is a constantly evolving field, and what was secure last year might not be secure today. Following reputable cybersecurity news sources and industry blogs can help you stay ahead of the curve. For example, learning about new types of malware or common attack vectors can help you proactively strengthen your defenses. It's like, being aware of the weather forecast helps you prepare for a storm, right? Staying current is absolutely vital.
Also, make sure you have a clear incident response plan in place. Even with the best security, things can sometimes go wrong. Knowing exactly what to do if a security breach occurs – how to isolate the affected devices, how to recover data, and how to report the incident – can significantly minimize damage. This includes regular backups of critical data, too. It's a bit like having a fire escape plan; you hope you never need it, but you're glad it's there if you do. Being prepared can make a huge difference, you know, when time is of the essence.
Finally, consider segmenting your network. If possible, put your IoT devices on a separate network segment from your main corporate or home network. This means that even if an IoT device is compromised, the attacker won't have immediate access to your more sensitive systems. It's a bit like having different rooms in a house; a problem in one room doesn't necessarily spread to all the others. This adds an extra layer of defense and limits the potential impact of a security incident, which is actually a very smart strategy for any IoT deployment.
Frequently Asked Questions (FAQs)
1. How can I fix an "untrusted connection" error when connecting to my IoT device?
If you're seeing messages like "This connection is untrusted," it often means there's a problem with the SSL/TLS certificate used by your IoT device or the way your Windows 10 system is verifying it. You should first check that the date and time on both your Windows 10 machine and the IoT device are correct. Incorrect time can invalidate certificates, you know. Then, make sure the IoT device's certificate is valid and hasn't expired. You might need to update the certificate on the device or ensure that your Windows 10 system trusts the Certificate Authority (CA) that issued it. Sometimes, adding the device's certificate to your Windows trust store can help, which is a pretty common fix.
2. My Windows 10 update keeps failing, how does this affect IoT security?
An update that keeps trying to reinstall and fails, even if it looks like it was already installed, can leave your Windows 10 system vulnerable. These updates often contain critical security patches that fix known weaknesses. If your system isn't getting these updates, it means potential entry points for attackers remain open, which is a big deal. For secure IoT P2P, an unpatched Windows 10 machine could be a weak link, allowing an attacker to compromise your system and potentially gain access to your IoT network or data. You should troubleshoot the update issue immediately, perhaps by using the Windows Update troubleshooter or manually installing the update, to make sure your system is fully protected.
3. Can network policies from an organization affect my personal IoT connections?
Yes, absolutely. If your Windows 10 machine is, for example, managed by an organization, even if you're not supposed to be, the policies enforced by that organization can definitely impact your IoT connections. If you go to edge://policy and see active policies, these might include network restrictions, firewall rules, or even certificate requirements that could interfere with how your IoT devices connect. Legitimate email being blocked by Outlook, for instance, shows how network rules can sometimes have unintended consequences. These policies could block ports needed for P2P, prevent the installation of necessary drivers, or interfere with VPN connections. You might need to check with your IT administrator or investigate the specific policies to understand their impact on your IoT setup, which is quite important for getting things working right.
Learn more about secure connections on our site, and link to this page for more on IoT device management.
- Jon Skoog Wife
- Whitney Cummings Age
- John Giarrusso Court
- April Kirkwood Husband
- Howard Stern Net Worth


Detail Author:
- Name : Joan Smitham
- Username : zander74
- Email : talon.labadie@hotmail.com
- Birthdate : 1992-05-16
- Address : 1645 Zulauf Fields Apt. 871 Maximusbury, DE 66990-4342
- Phone : +1.334.915.9021
- Company : Donnelly Inc
- Job : Central Office Operator
- Bio : Qui beatae at in voluptas. Pariatur veritatis odio ad consequatur vel aliquid dolor. Consequuntur deleniti dolorem ut rerum inventore tempora velit.
Socials
tiktok:
- url : https://tiktok.com/@charity.lynch
- username : charity.lynch
- bio : Ut quibusdam quia aut architecto. Ut sunt qui voluptatem soluta voluptatem.
- followers : 5333
- following : 2134
facebook:
- url : https://facebook.com/charity4874
- username : charity4874
- bio : Pariatur dolor sunt eveniet ipsa iusto aliquid est.
- followers : 3604
- following : 2651
twitter:
- url : https://twitter.com/charity4993
- username : charity4993
- bio : Dolore temporibus ut et quae asperiores quas. Sed rerum sit et tenetur recusandae eum. Ducimus distinctio molestiae et.
- followers : 2130
- following : 794