Getting your Internet of Things (IoT) devices to talk to you from anywhere can feel a bit like magic, can't it? It’s a wonderful thing, actually, being able to check on a sensor in your garden or restart a tiny computer in another room without needing to be right there. This kind of remote interaction is not just convenient; it is pretty much a must-have for many projects these days. So, you know, knowing how to set this up properly makes a big difference.
A big part of making these connections happen involves a tool called SSH, or Secure Shell. Think of it as a really private, locked-down telephone line for your devices. It helps you send commands and get information back, all while keeping things safe from prying eyes. This guide will walk you through setting up SSH for your remote IoT gadgets, giving you the control you need, which is quite important, you see, especially with all the data floating around.
You might have experienced something similar when trying to manage other digital parts of your life, like how you sign into YouTube to get to your subscriptions and watch history, or when you deal with installing software like Microsoft Office. Just like those situations need proper accounts and setup, your IoT devices also need a clear, secure way for you to reach them. This tutorial, as a matter of fact, aims to make that process straightforward and safe for your remote IoT setups, giving you peace of mind.
- Sam Neill And Bruce Greenwood
- Tall Lizzy Biography
- Mckinley Richardson Leak
- Who Is Touring With Nate Bargatze 2025
- Hannah Jo Leaked
Table of Contents
- What is SSH and Why It Matters for IoT?
- Getting Ready: Your Prerequisites
- Generating Your SSH Keys: The Secure Way
- Setting Up SSH on Your IoT Device
- Connecting to Your IoT Device from Your Computer
- Keeping Things Safe: Security Tips for Remote IoT SSH
- When Things Go Wrong: Troubleshooting Common SSH Issues
- Frequently Asked Questions About Remote IoT SSH
- Wrapping Up Your Remote IoT SSH Adventure
What is SSH and Why It Matters for IoT?
SSH, which stands for Secure Shell, provides a method for connecting to a computer over an unsecured network. It is a cryptographic network protocol, you know, that lets you operate network services securely over an unsecure network. For IoT devices, this means you can send commands, transfer files, and even run programs on your little gadget from a distance, all without worrying too much about someone listening in. This is pretty much essential for any device that is, say, out in the field or in a tricky spot to get to physically, so it's a very helpful thing.
Think about it like this: if you have a smart home system or a weather station running on a small computer, you need a way to update its software or check its status. SSH gives you that ability. It helps keep your data private and your device safe from unauthorized access, which, honestly, is a big deal in today's connected world. So, it's actually a very good idea to get familiar with it.
Getting Ready: Your Prerequisites
Before we jump into the setup, there are a few things you will need to have ready. First, you will need an IoT device, like a Raspberry Pi or a similar single-board computer, that can run a Linux-based operating system. This is pretty standard for many projects, you see. You will also need a computer to connect from, which could be your desktop or laptop, more or less.
- Adult Movie In Movierulz
- Did Celine Dions Son Get Married Recently
- Alice Rosenblum Only Fans Leak
- Eric Weinstein Net Worth
- Texas Renaissance Festival Lawsuit
You will also need to have an operating system installed on your IoT device, and it should be connected to your local network. You might need to access it locally first, perhaps with a monitor and keyboard, to get its network address. You will also need a way to open a terminal or command prompt on your main computer, which is where you will type your SSH commands. This is, you know, just the basic setup to get things going.
Generating Your SSH Keys: The Secure Way
Using SSH keys is a much safer way to log in than using passwords, which can sometimes be guessed or stolen. A key pair consists of a private key, which stays on your computer, and a public key, which goes on your IoT device. They work together like a lock and a special key, so, you know, it is pretty clever. This method makes it very hard for someone to get into your device without your specific private key.
On Linux or macOS
Open your terminal application. You will use a command called `ssh-keygen` to create your keys. Just type `ssh-keygen -t rsa -b 4096` and press Enter. The `-t rsa` specifies the type of key, and `-b 4096` makes it a very strong key, which is a good thing, actually. You will be asked where to save the key; the default location is usually fine. You can also set a passphrase for your private key, which is a very good idea for extra security, like a second lock on your special key, you know.
After that, you will have two files in your `~/.ssh/` directory: `id_rsa` (your private key) and `id_rsa.pub` (your public key). Remember, keep your private key absolutely secret, like your most important personal documents. You wouldn't want anyone else getting their hands on it, would you? So, treat it with care, basically.
On Windows
If you are using Windows, you can use a tool like PuTTYgen to create your SSH keys. You can download PuTTYgen as part of the PuTTY suite. Open PuTTYgen, select "RSA" as the type of key, and set the number of bits to 4096. Then, click "Generate" and move your mouse around the blank area to create randomness, which is kind of cool, you know, how it uses your movements.
Once the key is generated, save your private key by clicking "Save private key" and choose a secure location. Make sure to save it as a `.ppk` file for PuTTY. Copy the public key text from the top window, as you will need this for your IoT device. It's really important, you see, to keep track of both parts of the key.
Setting Up SSH on Your IoT Device
Now that you have your keys, it is time to get your IoT device ready to accept SSH connections. Most Linux-based IoT devices, like a Raspberry Pi, come with an SSH server already installed or can have it added quite easily. This is, you know, pretty convenient for folks like us.
For Raspberry Pi and Similar Linux-Based Devices
If you are setting up a new Raspberry Pi, you can enable SSH during the initial setup using the Raspberry Pi Imager. There is an option in the advanced settings to enable SSH. If your device is already running, you can enable SSH by opening a terminal on the device itself and typing `sudo systemctl enable ssh` and then `sudo systemctl start ssh`. This tells the device to run the SSH server and start it up, which is really what you need.
You can also use `sudo raspi-config`, go to "Interface Options," and then "SSH" to enable it. This is a pretty common way to do it, you know, for Raspberry Pi users. Make sure your device has a network connection and you know its IP address, which you can find with `hostname -I` or `ip a` in the terminal, so you can connect to it later.
Adding Your Public Key to the IoT Device
This is where your public key comes into play. You need to put your public key on the IoT device so it knows to trust your computer. First, connect to your IoT device using SSH with your password (just this one time, hopefully). For example, `ssh pi@your_device_ip_address`. Then, once logged in, you need to create a special directory and file. This is, you know, a pretty standard procedure.
Type these commands:
mkdir -p ~/.ssh chmod 700 ~/.ssh touch ~/.ssh/authorized_keys chmod 600 ~/.ssh/authorized_keys These commands create the `.ssh` directory if it doesn't exist, set the correct permissions (which is very important for security, actually), and create the `authorized_keys` file. Now, you need to add your public key to this `authorized_keys` file. You can do this by copying and pasting the content of your `id_rsa.pub` file (from your computer) into the `authorized_keys` file on the IoT device. You can use a text editor like `nano` on the device: `nano ~/.ssh/authorized_keys`. Paste your public key and save the file. This is where, you know, the magic really happens for key-based authentication.
Alternatively, from your computer, you can use `ssh-copy-id` if it is available: `ssh-copy-id pi@your_device_ip_address`. This tool, actually, automates the whole process of putting your public key on the remote device, which is quite handy. It is a much easier way, honestly, to get your key onto the device.
Connecting to Your IoT Device from Your Computer
With your public key on the IoT device, you should now be able to connect without a password. Open your terminal or command prompt on your computer. Type `ssh pi@your_device_ip_address` (replace `pi` with your device's username and `your_device_ip_address` with the actual IP address). If you set a passphrase for your private key, you will be prompted for that. Otherwise, you should connect directly, which is very cool, you know, when it just works.
For Windows users using PuTTY, open PuTTY, enter the IP address of your IoT device in the "Host Name (or IP address)" field. Then, go to "Connection > SSH > Auth" in the left-hand menu. Click "Browse" and select your private key file (`.ppk`). Then, click "Open" to connect. It should connect, and if you used a passphrase, it will ask for it, which is pretty straightforward, actually.
Once connected, you will see a command prompt for your IoT device. You can now run commands, check sensor readings, or update software from a distance. This gives you, you know, a lot of freedom and control over your devices, which is really what remote access is all about. It is a powerful capability to have at your fingertips, basically.
Keeping Things Safe: Security Tips for Remote IoT SSH
Security is a very big deal when it comes to remote access, especially for IoT devices that might be exposed to the internet. Just like how you need to protect your YouTube account from unauthorized access, or how you would want to make sure your Office software installation is legitimate and secure, your IoT devices need similar care. So, you know, it's really important to take these steps seriously.
- Disable Password Authentication: Once you have key-based authentication working, edit the `sshd_config` file on your IoT device (`sudo nano /etc/ssh/sshd_config`). Find the line `PasswordAuthentication yes` and change it to `PasswordAuthentication no`. Restart the SSH service (`sudo systemctl restart ssh`). This makes it so only people with the correct SSH key can get in, which is a lot safer, really.
- Change Default SSH Port: The default SSH port is 22. Attackers often scan for this port. Changing it to something else (e.g., 2222) can make your device less of an obvious target. Find `Port 22` in `sshd_config` and change it. Remember to specify the new port when connecting (`ssh -p 2222 pi@your_device_ip_address`), so, you know, that's a small but effective change.
- Keep Software Updated: Regularly update the operating system and software on your IoT device. This helps patch any security weaknesses. `sudo apt update && sudo apt upgrade` is a command you should run often, honestly.
- Use Strong Passphrases: If you use a passphrase for your private key, make it long and complex. This is another layer of protection, kind of like a very strong password for your special key.
- Firewall Rules: Configure your network's firewall to only allow SSH connections from trusted IP addresses. This is a very good way to limit who can even try to connect, so, you know, it's a smart move.
- Regularly Review Logs: Check SSH logs on your IoT device for any suspicious activity. This can help you spot problems early, which is, you know, pretty helpful for keeping things secure.
When Things Go Wrong: Troubleshooting Common SSH Issues
Sometimes, things do not work perfectly the first time, and that is okay. Even with things like trying to install Microsoft Office, you can sometimes run into errors, or find that a website for activation does not exist, as some people have found. These kinds of problems can be frustrating, but they often have solutions. Similarly, with SSH, there are common issues that pop up, and you know, usually they are fixable.
- Connection Refused: This usually means the SSH server is not running on your IoT device, or a firewall is blocking the connection. Double-check that SSH is enabled and started on your device. Also, verify any firewall settings on your router or the device itself. This is a pretty common thing, actually.
- Permission Denied (publickey): This means your SSH key is not being accepted. Make sure your public key is correctly placed in `~/.ssh/authorized_keys` on the IoT device, and that the permissions for `~/.ssh` (700) and `~/.ssh/authorized_keys` (600) are correct. Sometimes, you know, it's just a small permission error.
- Host Key Verification Failed: This happens if the host key of your IoT device changes, perhaps after reinstalling the OS. Your computer remembers the old key and gets confused. You can remove the old entry from your `~/.ssh/known_hosts` file (just open it with a text editor and delete the line for your device's IP address) and try again. It will ask you to confirm the new key, which is pretty normal.
- Incorrect IP Address or Port: Double-check the IP address of your IoT device. Make sure you are using the correct port if you changed it from the default 22. A simple typo can cause a lot of headaches, so, you know, a quick check can save time.
- Network Issues: Ensure both your computer and the IoT device are on the same network or can reach each other. Ping the IoT device's IP address from your computer to confirm network connectivity. If you cannot ping it, the problem is with the network itself, which is, you know, a different kind of issue.
Frequently Asked Questions About Remote IoT SSH
People often have questions when setting up remote access for their IoT devices, which is totally fair, you know. Here are a few common ones that come up.
Can I access my IoT device via SSH from outside my home network?
Yes, you can, but it requires a bit more setup. You will typically need to configure port forwarding on your home router to direct incoming SSH connections from the internet to your IoT device's local IP address. This is a very common way to do it, actually. Be very careful with this, as it exposes your device to the internet, so make sure your SSH security (key-based auth, strong passphrase, changed port) is absolutely top-notch. For more secure options, consider using a VPN or a service like a reverse SSH tunnel, which can be a bit more involved, you know, but offer greater safety.
What if my IoT device doesn't have a screen or keyboard for initial setup?
Many IoT devices, especially those designed for headless operation like some Raspberry Pi models, can be set up without a screen or keyboard. You can flash the operating system image onto an SD card and enable SSH during that process. For example, with the Raspberry Pi Imager, you can pre-configure SSH and even Wi-Fi settings before you ever boot the device. This is, you know, a pretty convenient feature for these kinds of devices.
Is SSH the only way to remotely access an IoT device?
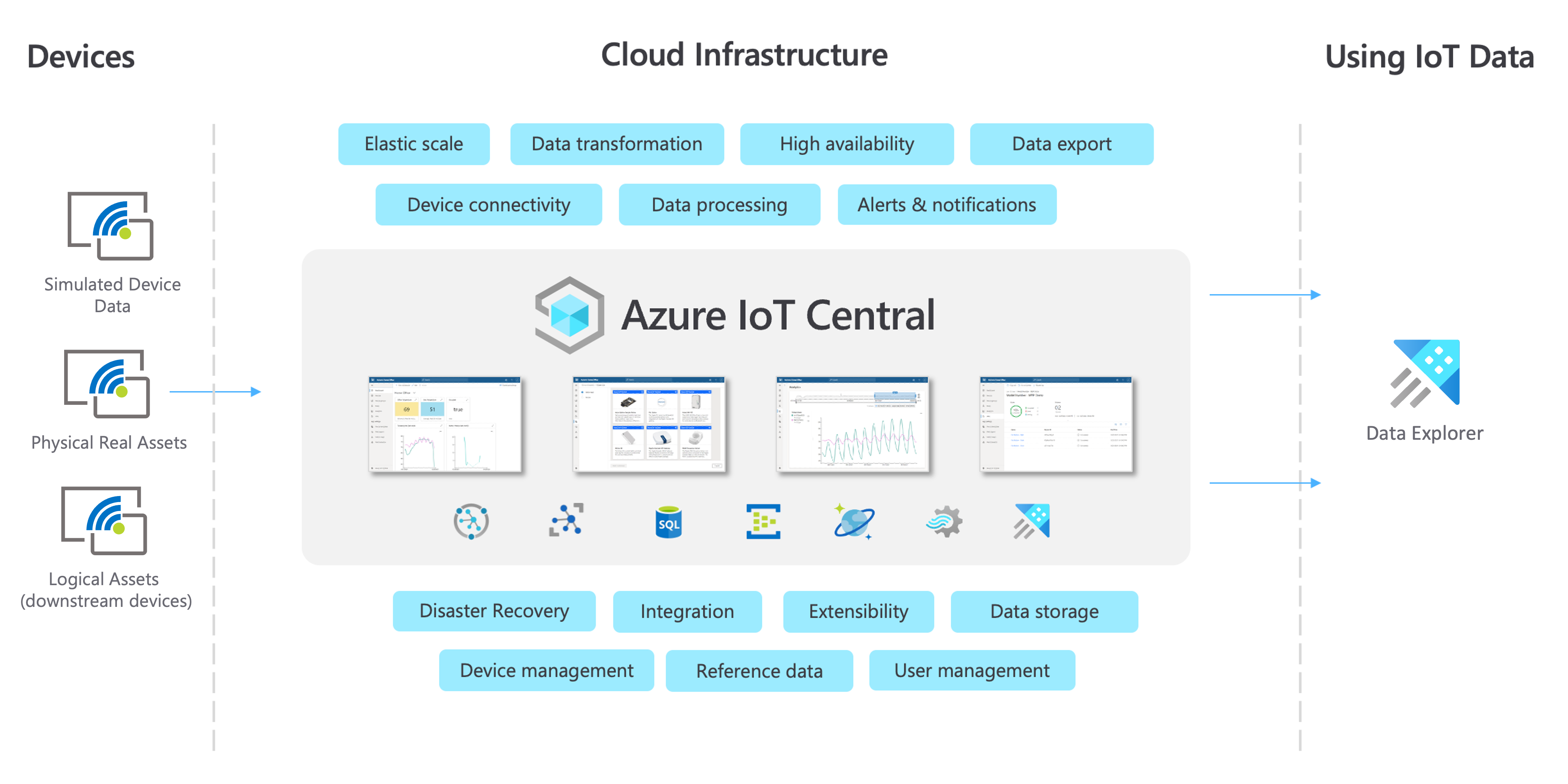
No, SSH is certainly not the only way, though it is a very popular and secure method for command-line access. There are other protocols and services, like VNC for graphical desktop access, or various cloud-based IoT platforms that offer remote management dashboards. Some devices might also support remote APIs or web interfaces. SSH is just one powerful tool in your toolkit, you see, but it is a very good one for direct system control.
Wrapping Up Your Remote IoT SSH Adventure
Setting up SSH for your remote IoT devices is a really valuable skill, honestly. It gives you the ability to manage and control your projects from anywhere, which is incredibly useful for all sorts of applications, from smart home gadgets to environmental sensors. By following these steps, you have given your devices a secure and reliable way to communicate with you, which is pretty cool. Just remember to keep security at the front of your mind, you know, as you continue to build and expand your connected world. It's truly a rewarding experience to have this kind of control, so keep exploring!
Learn more about secure remote access on our site, and link to this page IoT security best practices for further reading.
For more detailed information on SSH, you might want to check out resources like the official documentation for OpenSSH, which provides a lot of technical specifics. It is a very comprehensive source, actually, for those who want to go deeper.
- Gustavo Fring Actor
- Sienna West Onlyfans
- Richard Boone Net Worth
- Joe C Wen Net Worth
- Isnotmena Onlyfans

Detail Author:
- Name : Joan Smitham
- Username : zander74
- Email : talon.labadie@hotmail.com
- Birthdate : 1992-05-16
- Address : 1645 Zulauf Fields Apt. 871 Maximusbury, DE 66990-4342
- Phone : +1.334.915.9021
- Company : Donnelly Inc
- Job : Central Office Operator
- Bio : Qui beatae at in voluptas. Pariatur veritatis odio ad consequatur vel aliquid dolor. Consequuntur deleniti dolorem ut rerum inventore tempora velit.
Socials
tiktok:
- url : https://tiktok.com/@charity.lynch
- username : charity.lynch
- bio : Ut quibusdam quia aut architecto. Ut sunt qui voluptatem soluta voluptatem.
- followers : 5333
- following : 2134
facebook:
- url : https://facebook.com/charity4874
- username : charity4874
- bio : Pariatur dolor sunt eveniet ipsa iusto aliquid est.
- followers : 3604
- following : 2651
twitter:
- url : https://twitter.com/charity4993
- username : charity4993
- bio : Dolore temporibus ut et quae asperiores quas. Sed rerum sit et tenetur recusandae eum. Ducimus distinctio molestiae et.
- followers : 2130
- following : 794