It can feel pretty frustrating, can't it, when you're trying to get your remote IoT devices talking to your AWS VPC, and nothing seems to work quite right? You've got your devices, you've got your cloud, and yet, that crucial, secure connection just isn't happening. It's a common snag, you know, a bit like those times when a browser keeps telling you a connection is untrusted, or when a file just won't save in the right format. We've all been there, scratching our heads, wondering why something that should be straightforward turns into a puzzle.
Getting your internet-connected gadgets to chat safely with your private cloud network in AWS is, in some respects, a really big deal for any modern setup. This isn't just about getting data from point A to point B; it's about making sure that data travels with strong protection, away from prying eyes or unwelcome interference. When that secure link breaks down, or, very, never quite forms, it can put your whole system in a tough spot, maybe even leaving your device feeling a little bit at risk, as it were.
This article aims to help you figure out what might be going wrong when your secure remote IoT connections to an AWS VPC aren't quite clicking. We'll go over some of the typical reasons for these kinds of problems, give you some practical steps to sort things out, and talk about how to set things up correctly from the start, so you can avoid these headaches down the line. We'll look at things like certificates, network rules, and how AWS services fit together, actually, to help you get back on track.
- Progressed Moon In 10th House
- Fio Fap
- Okxx
- Does Patty Mayo Have A Daughter
- Brigitte Macron Wedding Dress
Table of Contents
- Understanding the Challenge: Why Secure IoT VPC Connections Matter
- Common Roadblocks When Connecting Remote IoT to AWS VPC
- Network Configuration Hurdles
- Certificate and Authentication Snags
- AWS IoT Core Policy and Rules Glitches
- VPC Endpoint Misunderstandings
- Step-by-Step Troubleshooting for Connection Issues
- Checking Your Network Path
- Validating Certificates and Keys
- Reviewing AWS IoT Core Policies
- Inspecting VPC Endpoint Setup
- Best Practices for a Solid Secure IoT Connection
- Implementing Strong Authentication
- Crafting Precise AWS IoT Policies
- Designing Your VPC for IoT
- Frequently Asked Questions About Secure IoT-VPC Connections
Understanding the Challenge: Why Secure IoT VPC Connections Matter
Connecting remote IoT devices to a private network segment in AWS, what we call a VPC, is a pretty important piece of the puzzle for many businesses today. It's not just about getting data flowing; it's about making sure that data is safe, that it's protected from anyone who shouldn't see it, and that your devices are communicating in a way that can't be easily messed with. Think of it like a secure tunnel, so to speak, where your device's messages can travel without worry.
When this secure connection isn't working, it can feel a lot like when you're trying to send an important email, but Outlook just keeps blocking it, even from your junk folder. The message is legitimate, it needs to get through, but something in the system is stopping it. For IoT, this can mean your sensors aren't reporting, your actuators aren't responding, or, in some respects, your whole operation could just grind to a halt. It's a problem that needs to be fixed quickly, naturally.
The goal is to build a setup where your devices, perhaps a fleet of smart sensors out in the field, can talk directly and privately to your applications running inside your AWS VPC. This bypasses the public internet for the most sensitive parts of the communication, giving you a much tighter grip on security. It's about creating a trustworthy link, you know, one that you can rely on day in and day out, without having to constantly worry about outside threats.
- Jack Benny Lynn
- Remote Iot Vpc Price
- Raspberry Pi Remoteiot App Download
- Gosford Park Plot Explained Who Is The Killer
- Mackenzie Mauzy
Common Roadblocks When Connecting Remote IoT to AWS VPC
When your remote IoT devices are having trouble linking up securely with your AWS VPC, there are, actually, a few usual suspects that tend to pop up. It's often not one big thing, but a combination of smaller details that need to be just right. We've seen similar issues with general connectivity, like when a browser keeps telling you "this connection is untrusted" for a perfectly normal website. The underlying cause is often a mismatch or a missing piece in the security chain, as it were.
Network Configuration Hurdles
One of the first places to look when things aren't connecting is your network setup. This involves things like firewalls, routing tables, and security groups. If your device can't even find the path to your AWS VPC endpoint, then, obviously, no secure connection can be made. It's like trying to mail a letter without the correct address or postage; it's just not going to get there. You need to make sure the network traffic from your IoT device is allowed to reach the specific AWS IoT Core VPC endpoint.
For instance, your security groups in AWS might be too restrictive, blocking incoming connections on the necessary ports (usually 8883 for MQTT over TLS). Or, perhaps your network ACLs (Access Control Lists) are stopping the traffic. On the device side, its local firewall might be preventing it from initiating the connection. These are, basically, the digital gatekeepers, and if they're not set to open the right gates, then, well, nothing gets through, you know.
Certificate and Authentication Snags
A really common reason for secure connection failures comes down to certificates and how devices prove who they are. IoT devices use X.509 certificates to establish a secure, encrypted link (TLS) with AWS IoT Core. If these certificates are expired, incorrectly formatted, or not properly registered with AWS IoT, the connection will, pretty much, fail every single time. It's a bit like trying to get into a secure building with an old, invalid ID card.
I mean, remember those "this connection is untrusted" messages in Firefox or Edge? That's often because the browser can't verify the website's certificate. It's very similar here. Your IoT device needs to trust the AWS IoT Core endpoint's certificate, and AWS IoT Core needs to trust your device's certificate. Any mismatch, any missing piece in that chain of trust, and the connection will be, you know, immediately rejected. This also includes making sure the private key on your device matches its certificate, and that it's kept super secret.
AWS IoT Core Policy and Rules Glitches
Even if your device can reach AWS IoT Core and authenticate itself, its actions are still governed by policies. An AWS IoT policy defines what your device is allowed to do: publish messages to certain topics, subscribe to others, or receive messages. If your device tries to do something that isn't explicitly permitted by its attached policy, AWS IoT will, in some respects, simply block that action. It's like having a valid ticket to a concert but then trying to go backstage when your ticket only allows you into the general seating area.
These policies are, actually, very specific. They use JSON documents to spell out permissions. If a policy is too restrictive, or if it has a typo, or if the device isn't even attached to the right policy, then you'll run into problems. It's a bit like those times when legitimate emails get blocked because of an overly strict spam filter; the intention is good, but the execution might be too broad or too narrow, so to speak.
VPC Endpoint Misunderstandings
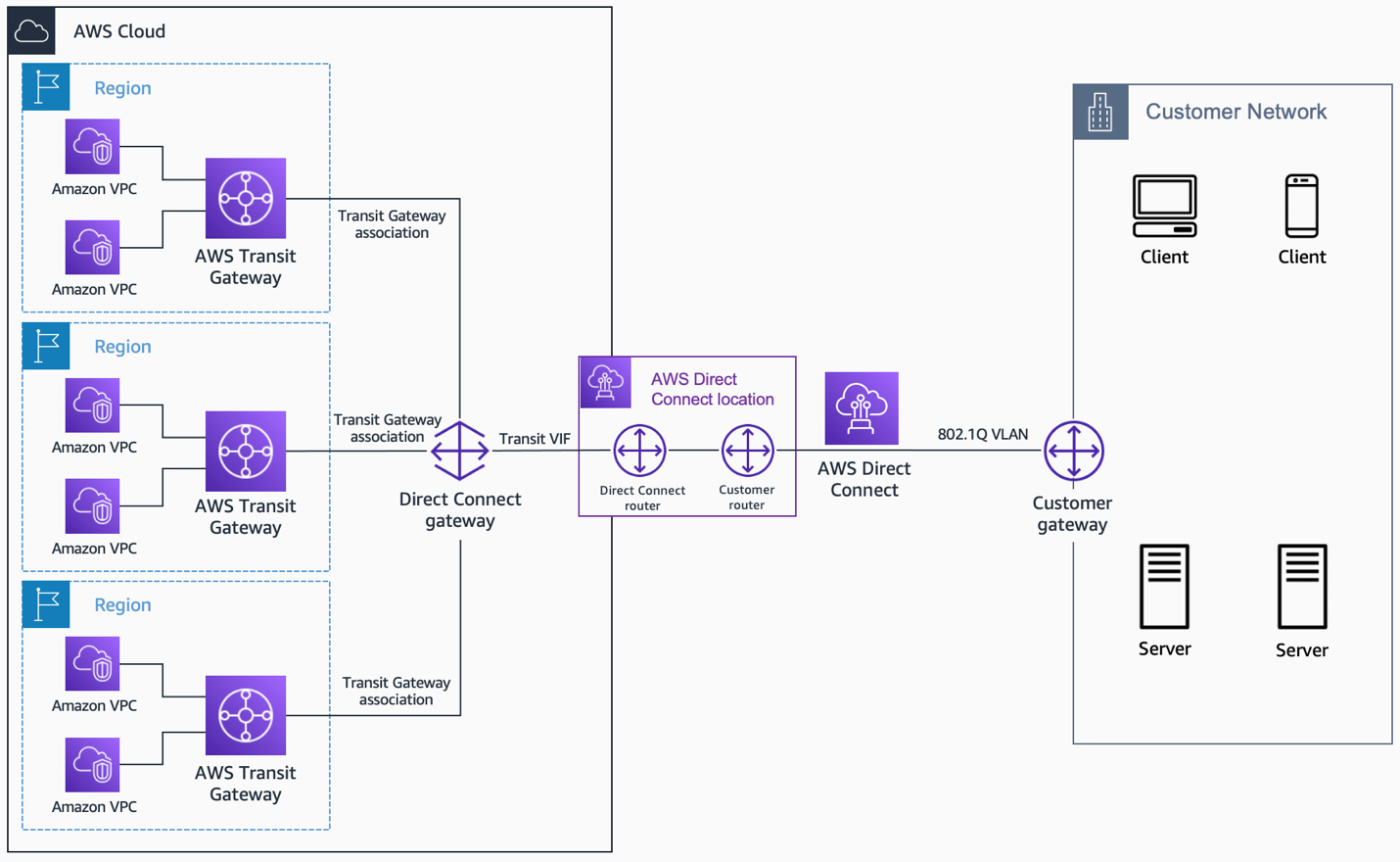
For remote IoT devices connecting to a VPC, you're likely using a VPC endpoint for AWS IoT Core. This allows your devices to connect to IoT Core privately, without going over the public internet. However, setting this up incorrectly can cause major headaches. Issues could include the endpoint not being in the correct subnets, its security groups not allowing traffic from your devices, or your device not being configured to use the endpoint's specific DNS name or IP addresses. It's, well, a pretty specific path that needs to be followed precisely.
You need to make sure that the DNS resolution for your IoT endpoint is pointing to the private VPC endpoint, rather than the public one. If your device is still trying to hit the public endpoint but you've set up your networking to force private access, then, obviously, that's going to cause a connection failure. It's a common point of confusion, actually, and needs careful checking.
Step-by-Step Troubleshooting for Connection Issues
When you're trying to figure out why your secure remote IoT connection to an AWS VPC isn't working, a structured approach is, you know, super helpful. It's a lot like fixing a computer that's stuck in an automatic repair loop; you need to go through specific steps to pinpoint the problem rather than just guessing. Let's walk through some practical steps to get things sorted.
Checking Your Network Path
First things first, you need to confirm that your IoT device can even reach the AWS IoT Core endpoint. This involves looking at the network path from your device to AWS. Are your device's local firewalls allowing outbound traffic on port 8883 (for MQTT over TLS)? If you're using a VPN or a direct connect, is that connection stable and correctly routed? You can, in some respects, use tools like `ping` or `traceroute` (if your device supports them and the endpoint responds) to check basic network reachability, though secure endpoints often don't respond to ping for security reasons.
Inside AWS, check the security groups attached to your VPC endpoint for IoT Core. Do they allow inbound traffic on port 8883 from the IP addresses or CIDR blocks where your IoT devices are located? Also, look at the network ACLs for the subnets where your VPC endpoint resides; these need to permit both inbound and outbound traffic on port 8883. It's a bit like making sure all the doors along a hallway are unlocked, you know, for the message to get through.
Validating Certificates and Keys
This is, arguably, one of the most frequent culprits. Make sure the X.509 certificate on your IoT device is still valid and hasn't expired. Also, confirm that the private key on the device correctly matches the certificate. Any mismatch here will, basically, stop the secure handshake dead in its tracks. You can use OpenSSL commands to inspect your certificates and keys if you have access to the device's file system or a way to extract them.
Next, check the status of your device's certificate in AWS IoT Core. Is it "ACTIVE"? If it's "INACTIVE" or "REVOKED," it won't work. Also, make sure your device is using the correct root CA certificate for AWS IoT. If your device is complaining about an "untrusted connection," it's often a sign that it doesn't trust the server's certificate, which usually means the root CA is missing or wrong. You need to make sure you have the right Amazon Root CA installed on your device, actually.
Reviewing AWS IoT Core Policies
Even with perfect network and certificate setups, a restrictive or incorrect policy will, very, prevent your device from doing anything useful. Go into the AWS IoT Core console, find your device's certificate, and look at the policies attached to it. Does the policy explicitly allow the actions your device is trying to perform (e.g., `iot:Publish` to specific topics, `iot:Subscribe` to others)?
Make sure the resource ARN (Amazon Resource Name) in the policy matches the actual topics your device is interacting with. For example, if your device publishes to `my/sensor/data`, the policy needs to allow `iot:Publish` on `arn:aws:iot:REGION:ACCOUNT_ID:topic/my/sensor/data`. A common mistake is to have a policy that's too broad or too narrow, so to speak. It's like having a permission slip that says "go to school" but not "go to the library," when your device needs to access the library.
Inspecting VPC Endpoint Setup
If you're using a VPC endpoint for private connectivity, verify its configuration. Is the endpoint in the correct subnets? Are its security groups allowing traffic from your IoT devices on port 8883? Crucially, is your IoT device configured to use the private DNS name or IP addresses of the VPC endpoint? If your device is still trying to resolve the public AWS IoT Core endpoint, but your network setup is routing traffic privately, then, well, that's going to be a problem.
You might need to adjust your device's DNS settings or its connection string to explicitly point to the VPC endpoint's private DNS name. Sometimes, you know, devices might have cached DNS entries, so clearing those can help. It's about making sure your device is looking for the right door, and that the right door is actually there and open.
Best Practices for a Solid Secure IoT Connection
Getting your remote IoT devices to connect securely to your AWS VPC isn't just about fixing problems when they pop up; it's also about setting things up right from the start. This approach can save you a lot of future headaches, very much like making sure your computer updates are installed correctly the first time, rather than dealing with constant reinstall failures. It's about building a strong foundation, you know.
Implementing Strong Authentication
Always use X.509 client certificates for device authentication. Make sure each device has its own unique certificate and private key. These should be provisioned securely onto the device and never shared. Rotate your certificates regularly, especially if a device is decommissioned or if there's any suspicion of compromise. It's, basically, your device's ID card, and you want that ID card to be as secure and up-to-date as possible.
Consider using AWS IoT Just-in-Time Provisioning (JITP) or Just-in-Time Registration (JITR) to automatically register devices and attach policies when they first connect. This helps automate the process and reduces manual errors. Also, for extra protection, think about using Certificate Authority (CA) certificates that are registered with AWS IoT, which allows AWS to verify the authenticity of your device certificates, in some respects, even more strictly.
Crafting Precise AWS IoT Policies
When you create your AWS IoT policies, remember the principle of least privilege. This means giving your devices only the permissions they absolutely need to do their job, and nothing more. If a device only needs to publish to `my/sensor/data`, then its policy should only allow `iot:Publish` to `arn:aws:iot:REGION:ACCOUNT_ID:topic/my/sensor/data`, and not to `arn:aws:iot:REGION:ACCOUNT_ID:topic/#` (which would allow publishing to *any* topic). It's a bit like giving someone a key to their own office, but not the key to the entire building.
Regularly review your IoT policies to make sure they are still appropriate for your devices' functions. As your system evolves, you might need to update these policies, but always with security in mind. Overly broad policies are, well, a common security weak point, so be careful there, you know.
Designing Your VPC for IoT
When setting up your AWS VPC, design it with IoT traffic in mind. Use private subnets for your AWS IoT Core VPC endpoint and any backend services that your IoT devices will interact with. Ensure that routing tables correctly direct traffic from your devices to the VPC endpoint. Use security groups and network ACLs to strictly control what traffic can enter and leave your VPC endpoint.
Consider using AWS PrivateLink for other AWS services that your IoT devices or backend applications might need to access within the VPC, like S3 for data storage or Lambda for processing. This keeps all traffic within the AWS network, further reducing exposure to the public internet. It's about creating a very controlled and private environment for your IoT ecosystem, actually, where everything has its proper place and pathway.
Learn more about secure IoT connections on our site, and for more specific guidance on setting up your AWS environment, link to this page AWS IoT Setup Guide.
Frequently Asked Questions About Secure IoT-VPC Connections
How do I connect IoT devices to a private VPC in AWS?
Connecting IoT devices to a private VPC in AWS typically involves setting up an AWS IoT Core VPC endpoint. This endpoint allows your devices to communicate with AWS IoT Core over a private connection, rather than the public internet. You'll need to configure your device to use the private DNS name or IP addresses associated with this VPC endpoint, and make sure your network settings (like security groups and routing tables) permit this private traffic. It's, basically, creating a dedicated, secure pathway, you know.
What are common reasons for AWS IoT Core VPC connection failures?
There are several common reasons why AWS IoT Core VPC connections might fail. These often include incorrect network configurations (like overly restrictive security groups or network ACLs), invalid or expired device certificates, mismatched private keys, or AWS IoT policies that don't grant the necessary permissions. Also, devices might be trying to connect to the public IoT endpoint instead of the private VPC endpoint, or, well, the VPC endpoint itself might be improperly configured. It's often a puzzle with several pieces that need to fit just right, actually.
How can I secure my remote IoT device connections to AWS?
To secure your remote IoT device connections to AWS, you should always use X.509 client certificates for authentication, ensuring each device has a unique certificate and private key. Implement strict AWS IoT policies based on the principle of least privilege, allowing devices only the actions they truly need. Use AWS IoT Core VPC endpoints to keep traffic private within the AWS network. Additionally, keep device firmware and security libraries up-to-date, and regularly review your security configurations. It's about layers of protection, so to speak, to keep everything safe and sound.
- Bhad Bhabie Leaked
- Split Face Diving Incident 2009
- Chelsie Deville Leaks
- Lesia Farner
- Kirk Cameron Net Worth


Detail Author:
- Name : Dr. Antonio Shanahan
- Username : jonathan.ledner
- Email : rmaggio@hotmail.com
- Birthdate : 2002-02-14
- Address : 819 Parisian Freeway Suite 367 Dickiland, OK 66986
- Phone : 702-285-0370
- Company : Kuvalis-Turcotte
- Job : Tool Set-Up Operator
- Bio : Odit qui qui sit hic. Ut fugit sit sunt fugiat ipsam consequatur maxime. Occaecati repellendus officiis enim minus quam corrupti commodi.
Socials
tiktok:
- url : https://tiktok.com/@little1976
- username : little1976
- bio : Ex maiores occaecati quibusdam voluptatibus voluptatem.
- followers : 3095
- following : 564
instagram:
- url : https://instagram.com/roxanelittle
- username : roxanelittle
- bio : Et beatae ea dolor harum voluptatem. Est voluptatibus sit sed tenetur. Ducimus ut quam debitis.
- followers : 1184
- following : 1992
facebook:
- url : https://facebook.com/roxane.little
- username : roxane.little
- bio : Quia cupiditate necessitatibus saepe ut rerum.
- followers : 3957
- following : 81
twitter:
- url : https://twitter.com/roxanelittle
- username : roxanelittle
- bio : Ad qui odio a voluptas tempore eaque. Minima facere facere quis distinctio. Sed tenetur aut iste tempore adipisci rerum dignissimos.
- followers : 2433
- following : 915